Ethical Hacking - NETWORK PENETRATION TESTING(1)
Pre--Connection-Attacks that can be done before connecting to the network.
Gaining Access - How to break Wi-Fi keys(WEP/WPA/WPA2)
Post-Connection-Attacks can be done after connecting to the network.
Detection&Security - detect and prevent the above attacks
Sniffing Basics - MAC Address
Each network card has a physical static address assigned by the card manufacturer called MAC address(Media Access Control)
This address is used between devices to identify each other and to transfer packets to the right place.
Each packet has a source MAC and a destination MAC.
We can change your MAC address value that is stored in the memory using a program called macchanger like so:
ifconfig [INTERFACE] down
macchanger -m [MAC] [INTERFACE]
ifconfig [INTERFACE] up
[INFTERFACE] = your wifi card name
[MAC] = the mac address you want to use
Install TP-Link TL-WDN5200 Driver on Kali Linux:
1. Check system information and network setting.
root@kali:~# uname -a
Linux kali 5.2.-kali2-amd64 # SMP Debian 5.2.-2kali1 (--) x86_64 GNU/Linux
root@kali:~# cat /etc/issue
Kali GNU/Linux Rolling \n \l root@kali:~# lsusb
Bus Device : ID 0bda:c811 Realtek Semiconductor Corp. .11ac NIC
Bus Device : ID 1d6b: Linux Foundation 2.0 root hub
Bus Device : ID 0e0f: VMware, Inc. Virtual USB Hub
Bus Device : ID 0e0f: VMware, Inc. Virtual Mouse
Bus Device : ID 1d6b: Linux Foundation 1.1 root hub
root@kali:~# lsusb -t
/: Bus .Port : Dev , Class=root_hub, Driver=uhci_hcd/2p, 12M
|__ Port : Dev , If , Class=Human Interface Device, Driver=usbhid, 12M
|__ Port : Dev , If , Class=Hub, Driver=hub/7p, 12M
/: Bus .Port : Dev , Class=root_hub, Driver=ehci-pci/6p, 480M
|__ Port : Dev , If , Class=Vendor Specific Class, Driver=, 480M
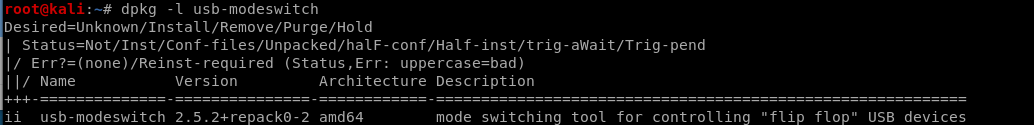
2. Check the usb-modeswitch installation status.
dpkg -l usb-modeswitch
3. Down load the driver code.
https://github.com/chenhaiq/mt7610u_wifi_sta_v3002_dpo_20130916
4.
I will continue after receive the ALFA AWUS1900 WiFi adapter.
Ethical Hacking - NETWORK PENETRATION TESTING(1)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- beego register db `default`, sql: unknown driver "mysql" (forgotten import?)
首先先去你的目录下找找这个文件里有没有东西,或者有没有这个文件 如果没有 执行下面两个命令: 下载:go get github.com/Go-SQL-Driver/MySQL 安装:go instal ...
- PHP丨PHP基础知识之流程控制WHILE循环「理论篇」
昨天讲完FOR循环今天来讲讲他的兄弟WHILE循环!进入正题: while是计算机的一种基本循环模式.当满足条件时进入循环,进入循环后,当条件不满足时,跳出循环.while语句的一般表达式为:whil ...
- 如何在VMware虚拟机中安装CentOS6.7系统(下篇)
上一篇文章讲到了CentOS6.7的安装教程,安装步骤到时区选择这块了,这篇文章接上篇文章,继续讲述CentOS6.7的安装教程,直至安装完成. 17.设置root的登录密码,日后登录虚拟机,用户名就 ...
- 成为python程序员,对疫情过后的毕业生来说,真是一个不错的方向吗?
Python最近几年,一直被炒得很火,这其中有商业因素,但更重要的是即将到来的人工智能时代,而python就恰好是最适合的编程语言. 所以无论是在职的人,还是在校的学生,都想着跟上这一趋势,但,在今年 ...
- Beta冲刺--项目测试
这个作业属于哪个课程 软件工程 (福州大学至诚学院 - 计算机工程系) 这个作业要求在哪里 Beta 冲刺 这个作业的目标 Beta冲刺--项目测试 作业正文 如下 其他参考文献 ... Beta冲刺 ...
- VulnHub CengBox2靶机渗透
本文首发于微信公众号:VulnHub CengBox2靶机渗透,未经授权,禁止转载. 难度评级:☆☆☆☆官网地址:https://download.vulnhub.com/cengbox/CengB ...
- 入门大数据---Elasticsearch搭建与应用
项目版本 构建需要: JDK1.7 Elasticsearch2.2.1 junit4.10 log4j1.2.17 spring-context3.2.0.RELEASE spring-core3. ...
- ceph bluestore与 filestore 数据存放的区别
一. filestore 对象所在的PG以文件方式放在xfs文件中 1 查看所有的osd硬盘,跟其他linux其他硬盘一样,被挂载一个目录中. [root@hz-storage1 ~]# df -h ...
- .NET Core WEB API接口参数模型绑定
.NET Core WEB API 模型绑定方式有以下表格中的几种: 特性 绑定源 [FromHeader] 请求标头 [FromQuery] 请求查询字符串参数 [FromForm] 请求正文中的表 ...
- 使用 Nginx 部署静态页面
Nginx 介绍 Nginx 是俄罗斯人编写的十分轻量级的 HTTP 服务器, Nginx,它的发音为「engine X」,是一个高性能的 HTTP 和反向代理服务器,同时也是一个 IMAP/ POP ...
