攻防世界 reverse xx
xx
程序开始验证输入长度为19位。
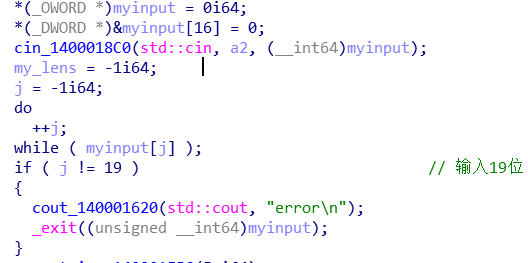
取前4位(作为后面加密的key),验证这4位都在‘qwertyuiopasdfghjklzxcvbnm1234567890‘中。

将key用0填充为16位

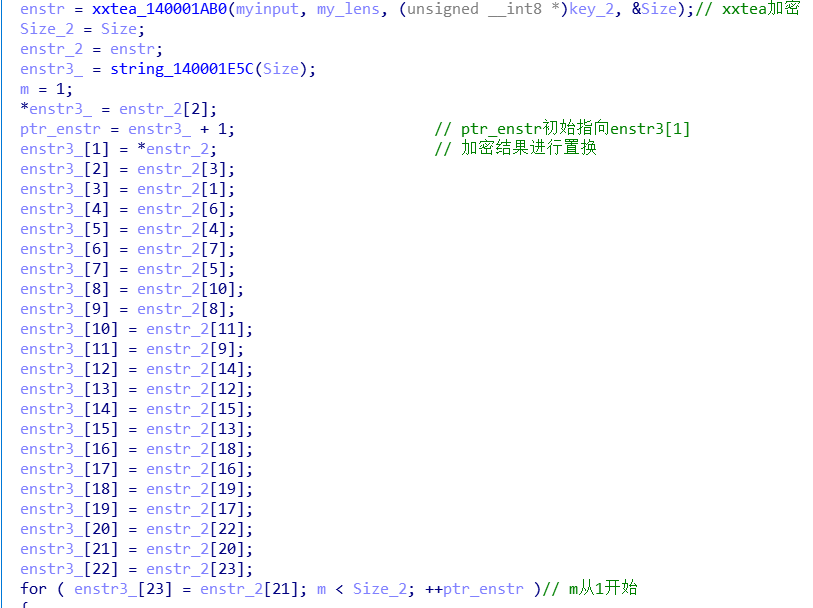
调用xxtea进行加密,加密结果再进行置换。
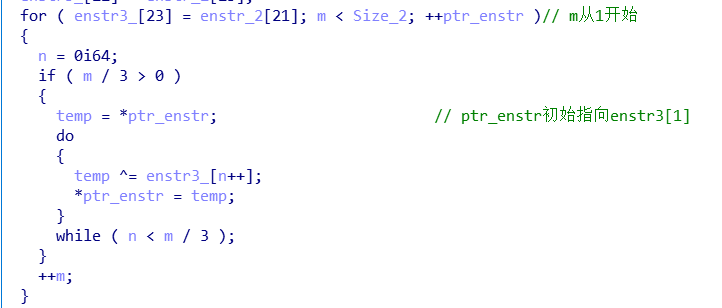
再进行异或操作
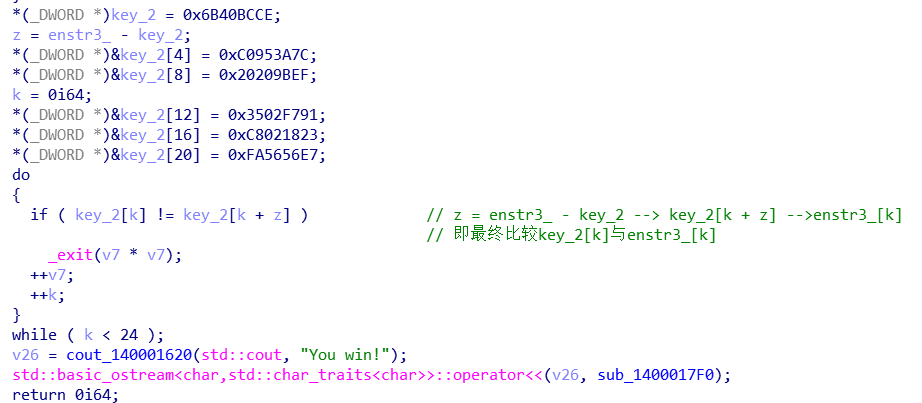
最终比较
wp
import struct _DELTA = 0x9E3779B9 def _long2str(v, w):
n = (len(v) - 1) << 2
if w:
m = v[-1]
if (m < n - 3) or (m > n): return ''
n = m
s = struct.pack('<%iL' % len(v), *v)
return s[0:n] if w else s def _str2long(s, w):
n = len(s)
m = (4 - (n & 3) & 3) + n
s = s.ljust(m, b"\0")
v = list(struct.unpack('<%iL' % (m >> 2), s))
if w: v.append(n)
return v def encrypt(str, key):
if str == '': return str
v = _str2long(str, True)
k = _str2long(key.ljust(16, b"\0"), False)
n = len(v) - 1
z = v[n]
y = v[0]
sum = 0
q = 6 + 52 // (n + 1)
while q > 0:
sum = (sum + _DELTA) & 0xffffffff
e = sum >> 2 & 3
for p in range(n):
y = v[p + 1]
v[p] = (v[p] + ((z >> 5 ^ y << 2) + (y >> 3 ^ z << 4) ^ (sum ^ y) + (k[p & 3 ^ e] ^ z))) & 0xffffffff
z = v[p]
y = v[0]
v[n] = (v[n] + ((z >> 5 ^ y << 2) + (y >> 3 ^ z << 4) ^ (sum ^ y) + (k[n & 3 ^ e] ^ z))) & 0xffffffff
z = v[n]
q -= 1
return _long2str(v, False) def decrypt(str, key):
if str == '': return str
v = _str2long(str, False)
k = _str2long(key.ljust(16, b"\0"), False)
n = len(v) - 1
z = v[n]
y = v[0]
q = 6 + 52 // (n + 1)
sum = (q * _DELTA) & 0xffffffff
while (sum != 0):
e = sum >> 2 & 3
for p in range(n, 0, -1):
z = v[p - 1]
v[p] = (v[p] - ((z >> 5 ^ y << 2) + (y >> 3 ^ z << 4) ^ (sum ^ y) + (k[p & 3 ^ e] ^ z))) & 0xffffffff
y = v[p]
z = v[n]
v[0] = (v[0] - ((z >> 5 ^ y << 2) + (y >> 3 ^ z << 4) ^ (sum ^ y) + (k[0 & 3 ^ e] ^ z))) & 0xffffffff
y = v[0]
sum = (sum - _DELTA) & 0xffffffff
return _long2str(v, True)
tg=[0xCE, 0xBC, 0x40, 0x6B, 0x7C, 0x3A, 0x95, 0xC0, 0xEF, 0x9B, 0x20, 0x20, 0x91, 0xF7, 0x02, 0x35,
0x23, 0x18, 0x02, 0xC8, 0xE7, 0x56, 0x56, 0xFA ]
order=[2,0,3,1,6,4,7,5,10,8,11,9,14,12,15,13,18,16,19,17,22,20,23,21]
flag=[0]*24
for i in range(23,-1,-1):
for j in range(i//3):
tg[i]^=tg[j]
print('逆异或操作后:'+' '.join(map(hex,tg)))
for i in range(24):
flag[order[i]]=tg[i]
print('逆加密字符串替换后:'+' '.join(map(hex,flag)))
x=decrypt(bytes(flag),'flag'.encode())
print(x)
逆异或操作后:0xce 0xbc 0x40 0xa5 0xb2 0xf4 0xe7 0xb2 0x9d 0xa9 0x12 0x12 0xc8 0xae 0x5b 0x10 0x6 0x3d 0x1d 0xd7 0xf8 0xdc 0xdc 0x70
逆加密字符串替换后:0xbc 0xa5 0xce 0x40 0xf4 0xb2 0xb2 0xe7 0xa9 0x12 0x9d 0x12 0xae 0x10 0xc8 0x5b 0x3d 0xd7 0x6 0x1d 0xdc 0x70 0xf8 0xdc
b'flag{CXX_and_++tea}'
xxtea算法参考:
XXTEA for Python
攻防世界 reverse xx的更多相关文章
- 攻防世界 reverse 进阶 10 Reverse Box
攻防世界中此题信息未给全,题目来源为[TWCTF-2016:Reverse] Reverse Box 网上有很多wp是使用gdb脚本,这里找到一个本地还原关键算法,然后再爆破的 https://www ...
- 攻防世界 reverse evil
这是2017 ddctf的一道逆向题, 挑战:<恶意软件分析> 赛题背景: 员工小A收到了一封邮件,带一个文档附件,小A随手打开了附件.随后IT部门发现小A的电脑发出了异常网络访问请求,进 ...
- 攻防世界 reverse tt3441810
tt3441810 tinyctf-2014 附件给了一堆数据,将十六进制数据部分提取出来, flag应该隐藏在里面,(这算啥子re,) 保留可显示字符,然后去除填充字符(找规律 0.0) 处理脚本: ...
- 攻防世界 reverse 进阶 APK-逆向2
APK-逆向2 Hack-you-2014 (看名以为是安卓逆向呢0.0,搞错了吧) 程序是.net写的,直接祭出神器dnSpy 1 using System; 2 using System.Diag ...
- 攻防世界 reverse Windows_Reverse2
Windows_Reverse2 2019_DDCTF 查壳: 寻找oep-->dump-->iat修复 便可成功脱壳 int __cdecl main(int argc, con ...
- 攻防世界 reverse BabyXor
BabyXor 2019_UNCTF 查壳 脱壳 dump 脱壳后 IDA静态分析 int main_0() { void *v0; // eax int v1; // ST5C_4 char ...
- 攻防世界 reverse parallel-comparator-200
parallel-comparator-200 school-ctf-winter-2015 https://github.com/ctfs/write-ups-2015/tree/master/sc ...
- 攻防世界 reverse 进阶 8-The_Maya_Society Hack.lu-2017
8.The_Maya_Society Hack.lu-2017 在linux下将时间调整为2012-12-21,运行即可得到flag. 下面进行分析 1 signed __int64 __fastca ...
- 攻防世界 reverse easy_Maze
easy_Maze 从题目可得知是简单的迷宫问题 int __cdecl main(int argc, const char **argv, const char **envp) { __int64 ...
随机推荐
- Emacs和Vim:神的编辑器和编辑器之神, 到底哪个更好?
Emacs和Vim:神的编辑器和编辑器之神, 到底哪个更好? 在这个蔚蓝色的星球上,流传着两大神器的传说:据说Emacs是神的编辑器,而Vim是编辑器之神. 一些人勇敢地拾起了Vim或Emacs,却发 ...
- vscode & javascript & react & "editor.foldingStrategy": "indentation"
vscode & javascript & react & "editor.foldingStrategy": "indentation" ...
- js jsonParse
mdn const rx_one = /^[\],:{}\s]*$/; const rx_two = /\\(?:["\\\/bfnrt]|u[0-9a-fA-F]{4})/g; // 匹配 ...
- Flutter 真机调试
先把手机开启开发者模式,并打开USB调试功能(每种机型开启方法可能不一样) flutter devices 查看是否连接 flutter run
- 「NGK每日快讯」2021.2.7日NGK公链第96期官方快讯!
- Mosquitto
mosquitto可连接远程服务器及本地服务器. mosquitto可在一个节点内建立一个连接用于收发,也可在一个节点内建立多个连接用于收发.建立一个连接用于收发时,会有初始部分帧的延迟.(可能由于内 ...
- 开启算法之路,还原题目,用debug调试搞懂每一道题
文章简述 大家好,本篇是个人的第 3 篇文章. 承接第一篇文章<手写单链表基础之增,删,查!附赠一道链表题>,在第一篇文章中提过,在刷算法题之前先将基础知识过一遍,这样对后面的做算法题是很 ...
- 类关系与uml图示表示
1. 关联(Association).聚合(Aggregation).组合(Composition)区别 association: 两者之间存在某种关联即可,很弱的关系,如student and co ...
- Prism -- 简介
Prism是一个开源框架,用于在WPF.Xamarin Forms.Uno/Win UI等应用中创建松耦合.可维护.可测试的XAML应用程序.Prism提供了一组设计模式的实现,这些设计模式有助于编写 ...
- python中yield的用法详解——最简单,最清晰的解释
转载自https://blog.csdn.net/mieleizhi0522 首先我要吐槽一下,看程序的过程中遇见了yield这个关键字,然后百度的时候,发现没有一个能简单的让我懂的,讲起来真TM的都 ...
