wifi IP address scanner on macOS
wifi IP address scanner on macOS
Nmap Network Scanning

https://nmap.org/book/inst-macosx.html
https://nmap.org/download.html#macosx
test
$ nmap -T4 -A -v 192.168.1.1-255

Nmap 命令
https://svn.nmap.org/nmap/docs/nmap.usage.txt
Nmap 7.80SVN ( https://nmap.org )
Usage: nmap [Scan Type(s)] [Options] {target specification}
TARGET SPECIFICATION:
Can pass hostnames, IP addresses, networks, etc.
Ex: scanme.nmap.org, microsoft.com/24, 192.168.0.1; 10.0.0-255.1-254
-iL <inputfilename>: Input from list of hosts/networks
-iR <num hosts>: Choose random targets
--exclude <host1[,host2][,host3],...>: Exclude hosts/networks
--excludefile <exclude_file>: Exclude list from file
HOST DISCOVERY:
-sL: List Scan - simply list targets to scan
-sn: Ping Scan - disable port scan
-Pn: Treat all hosts as online -- skip host discovery
-PS/PA/PU/PY[portlist]: TCP SYN/ACK, UDP or SCTP discovery to given ports
-PE/PP/PM: ICMP echo, timestamp, and netmask request discovery probes
-PO[protocol list]: IP Protocol Ping
-n/-R: Never do DNS resolution/Always resolve [default: sometimes]
--dns-servers <serv1[,serv2],...>: Specify custom DNS servers
--system-dns: Use OS's DNS resolver
--traceroute: Trace hop path to each host
SCAN TECHNIQUES:
-sS/sT/sA/sW/sM: TCP SYN/Connect()/ACK/Window/Maimon scans
-sU: UDP Scan
-sN/sF/sX: TCP Null, FIN, and Xmas scans
--scanflags <flags>: Customize TCP scan flags
-sI <zombie host[:probeport]>: Idle scan
-sY/sZ: SCTP INIT/COOKIE-ECHO scans
-sO: IP protocol scan
-b <FTP relay host>: FTP bounce scan
PORT SPECIFICATION AND SCAN ORDER:
-p <port ranges>: Only scan specified ports
Ex: -p22; -p1-65535; -p U:53,111,137,T:21-25,80,139,8080,S:9
--exclude-ports <port ranges>: Exclude the specified ports from scanning
-F: Fast mode - Scan fewer ports than the default scan
-r: Scan ports consecutively - don't randomize
--top-ports <number>: Scan <number> most common ports
--port-ratio <ratio>: Scan ports more common than <ratio>
SERVICE/VERSION DETECTION:
-sV: Probe open ports to determine service/version info
--version-intensity <level>: Set from 0 (light) to 9 (try all probes)
--version-light: Limit to most likely probes (intensity 2)
--version-all: Try every single probe (intensity 9)
--version-trace: Show detailed version scan activity (for debugging)
SCRIPT SCAN:
-sC: equivalent to --script=default
--script=<Lua scripts>: <Lua scripts> is a comma separated list of
directories, script-files or script-categories
--script-args=<n1=v1,[n2=v2,...]>: provide arguments to scripts
--script-args-file=filename: provide NSE script args in a file
--script-trace: Show all data sent and received
--script-updatedb: Update the script database.
--script-help=<Lua scripts>: Show help about scripts.
<Lua scripts> is a comma-separated list of script-files or
script-categories.
OS DETECTION:
-O: Enable OS detection
--osscan-limit: Limit OS detection to promising targets
--osscan-guess: Guess OS more aggressively
TIMING AND PERFORMANCE:
Options which take <time> are in seconds, or append 'ms' (milliseconds),
's' (seconds), 'm' (minutes), or 'h' (hours) to the value (e.g. 30m).
-T<0-5>: Set timing template (higher is faster)
--min-hostgroup/max-hostgroup <size>: Parallel host scan group sizes
--min-parallelism/max-parallelism <numprobes>: Probe parallelization
--min-rtt-timeout/max-rtt-timeout/initial-rtt-timeout <time>: Specifies
probe round trip time.
--max-retries <tries>: Caps number of port scan probe retransmissions.
--host-timeout <time>: Give up on target after this long
--scan-delay/--max-scan-delay <time>: Adjust delay between probes
--min-rate <number>: Send packets no slower than <number> per second
--max-rate <number>: Send packets no faster than <number> per second
FIREWALL/IDS EVASION AND SPOOFING:
-f; --mtu <val>: fragment packets (optionally w/given MTU)
-D <decoy1,decoy2[,ME],...>: Cloak a scan with decoys
-S <IP_Address>: Spoof source address
-e <iface>: Use specified interface
-g/--source-port <portnum>: Use given port number
--proxies <url1,[url2],...>: Relay connections through HTTP/SOCKS4 proxies
--data <hex string>: Append a custom payload to sent packets
--data-string <string>: Append a custom ASCII string to sent packets
--data-length <num>: Append random data to sent packets
--ip-options <options>: Send packets with specified ip options
--ttl <val>: Set IP time-to-live field
--spoof-mac <mac address/prefix/vendor name>: Spoof your MAC address
--badsum: Send packets with a bogus TCP/UDP/SCTP checksum
OUTPUT:
-oN/-oX/-oS/-oG <file>: Output scan in normal, XML, s|<rIpt kIddi3,
and Grepable format, respectively, to the given filename.
-oA <basename>: Output in the three major formats at once
-v: Increase verbosity level (use -vv or more for greater effect)
-d: Increase debugging level (use -dd or more for greater effect)
--reason: Display the reason a port is in a particular state
--open: Only show open (or possibly open) ports
--packet-trace: Show all packets sent and received
--iflist: Print host interfaces and routes (for debugging)
--append-output: Append to rather than clobber specified output files
--resume <filename>: Resume an aborted scan
--stylesheet <path/URL>: XSL stylesheet to transform XML output to HTML
--webxml: Reference stylesheet from Nmap.Org for more portable XML
--no-stylesheet: Prevent associating of XSL stylesheet w/XML output
MISC:
-6: Enable IPv6 scanning
-A: Enable OS detection, version detection, script scanning, and traceroute
--datadir <dirname>: Specify custom Nmap data file location
--send-eth/--send-ip: Send using raw ethernet frames or IP packets
--privileged: Assume that the user is fully privileged
--unprivileged: Assume the user lacks raw socket privileges
-V: Print version number
-h: Print this help summary page.
EXAMPLES:
nmap -v -A scanme.nmap.org
nmap -v -sn 192.168.0.0/16 10.0.0.0/8
nmap -v -iR 10000 -Pn -p 80
SEE THE MAN PAGE (https://nmap.org/book/man.html) FOR MORE OPTIONS AND EXAMPLES
Nmap 使用教程
https://nmap.org/man/zh/man-briefoptions.html
https://nmap.org/book/man.html
nmap [ <Scan Type> ...] [ <Options> ] { <target specification> }
https://nmap.org/book/man-examples.html
nmap -v scanme.nmap.org
nmap -sS -O scanme.nmap.org/24
nmap -sV -p 22,53,110,143,4564 198.116.0-255.1-127
nmap -v -iR 100000 -Pn -p 80
nmap -Pn -p80 -oX logs/pb-port80scan.xml -oG logs/pb-port80scan.gnmap 216.163.128.20/20
https://www.cnblogs.com/xgqfrms/tag/NMAP/
Nmap 命令
Nmap 语法格式: nmap [空格] [选项/多选项/协议] [空格] [目标]
# 1-255 对一个 ip 范围进行全面扫描
# -A 全面扫描. 综合扫描. 是一种完整扫描目标信息的扫描方式
# -T 时序选项, -T0-T5. 用于IDS逃逸, 0=>非常慢,1=>缓慢的,2=>文雅的,3=>普通的,4=>快速的,5=>急速
# -v 版本探测 ,通过相应的端口探测对应的服务,根据服务的指纹识别出相应的版本
$ nmap -T4 -A -v 192.168.1.1-255
https://www.cnblogs.com/php09/p/10530057.html
Security Scanner
refs
https://www.jianshu.com/p/705d6aa95a37
MacPorts
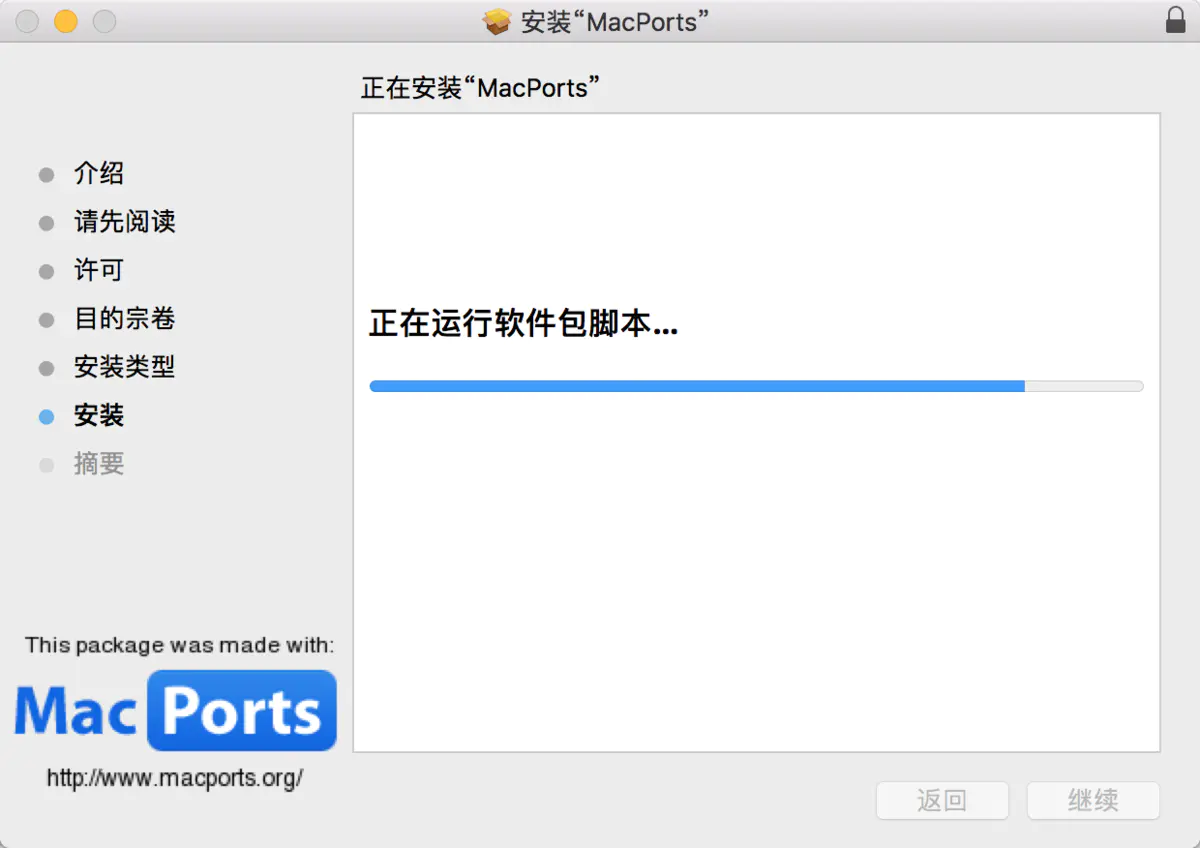
macOS 除了可以用 dmg、pkg 来安装软件外,比较方便的还有用MacPorts来帮助你安装其他应用程序;
跟 BSD 中的 ports 道理一样。MacPorts 就像 apt-get、yum 一样,可以快速安装些软件;
https://kapeli.com/cheat_sheets/MacPorts.docset/Contents/Resources/Documents/index
# Search directory for ports
$ port search [--name] [--regex] '<searchtext>'
# Get information about a port
$ port info <portname>
# List installed ports
# For just a list of the ports you have explicitly installed
$ port echo requested
# For a list of everything installed by MacPorts, including all dependencies
$ port installed
xgqfrms 2012-2020
www.cnblogs.com 发布文章使用:只允许注册用户才可以访问!
wifi IP address scanner on macOS的更多相关文章
- AndroidStudio ADB WIFI :adb wifi scan ip address
笔记本使用Android studio的adb wifi插件时,AS 最下方报 adb wifi scan ip address.一直无法使用. 解决办法: ----在Terminal窗口中输入: a ...
- macOS & wifi & ip
macOS & wifi & ip mac show wifi ip # wireless ipconfig getifaddr en1 # ethernet ipconfig get ...
- Linux Force DHCP Client (dhclient) to Renew IP Address
http://www.cyberciti.biz/faq/howto-linux-renew-dhcp-client-ip-address/‘m using Ubuntu Linux. How to ...
- TOJ4413: IP address
传送门:http://acm.tzc.edu.cn/acmhome/problemdetail.do?&method=showdetail&id=4413 时间限制(普通/Java): ...
- poj 2105 IP Address(水题)
一.Description Suppose you are reading byte streams from any device, representing IP addresses. Your ...
- ERROR 2003 (HY000): Can't connect to MySQL server on 'ip address' (111)的处理办法
远程连接mysql数据库时可以使用以下指令 mysql -h 192.168.1.104 -u root -p 如果是初次安装mysql,需要将所有/etc/mysql/内的所有配置文件的bind-a ...
- oracle 11g RAC安装节点二执行结果错误CRS-5005: IP Address: 192.168.1.24 is already in use in the network
[root@testdb11b ~]# /u01/app/oraInventory/orainstRoot.sh Changing permissions of /u01/app/oraInvento ...
- Assign an Elastic IP Address to Your Instance
By default, an instance in a nondefault VPC is not assigned a public IP address, and is private.You ...
- Ubuntu setup Static IP Address
Change Ubuntu Server from DHCP to a Static IP Address If the Ubuntu Server installer has set your se ...
随机推荐
- calc, support, media各自的含义及用法?
@support主要是用于检测浏览器是否支持CSS的某个属性,其实就是条件判断,如果支持某个属性,你可以写一套样式,如果不支持某个属性,你也可以提供另外一套样式作为替补. calc() 函数用于动态计 ...
- loj10006数列分段
题目描述 对于给定的一个长度为 N 的正整数数列 A,现要将其分成连续的若干段,并且每段和不超过 M(可以等于 M),问最少能将其分成多少段使得满足要求. 输入格式 第一行包含两个正整数 N,M表示了 ...
- power network 电网——POJ1459
Power Network Time Limit: 2000MS Memory Limit: 32768K Total Submissions: 27282 Accepted: 14179 D ...
- RocketMQ 常用消息类型
文章首发于公众号<程序员果果> 地址 : https://mp.weixin.qq.com/s/dYqGd9zi2mNelsNNLIribg 消息发送示例 导入依赖: <depend ...
- Jenkins安装部署项目
Jenkins安装部署项目 配置JDK git maven 部署到服务器 一.新建任务 二.配置jenkins 三.添加构建信息 四.应用.保存 五.踩坑填坑记录 5.1没有jar包的情况 5.2无法 ...
- python --装饰器通俗讲解
装饰器 什么是装饰器?:在不修改源代码和调用方式的基础上给其增加新的功能,多个装饰器可以装饰在同一个函数上 Python中的装饰器是你进入Python大门的一道坎; 装饰器特点: 不改变原函数原代码: ...
- Mysql:好好的索引,为什么要下推?
前段时间有读者提议讲讲索引下推,这期就把这事儿安排上.多余的前言就不赘述了,我们直接开始. 列位坐好! 图注:思维导图 回表操作 对于数据库来说,只要涉及到索引,必然绕不过去回表操作.当然这也是我们今 ...
- 织梦(DedeCms)的安全问题解决办法
网上大家也看到DEDECMS这套程序,虽然便捷草根站长的快速建站,但安全问题也是非常多的.DEDE官方也在很久之前就已经不再对这套系统进行什么版本升级了,最多就是一些补丁修复: 好,废话不多说,下面整 ...
- Flink 在又拍云日志批处理中的实践
日前,由又拍云举办的大数据与 AI 技术实践|Open Talk 杭州站沙龙在杭州西溪科创园顺利举办.本次活动邀请了有赞.个推.方得智能.又拍云等公司核心技术开发者,现场分享各自领域的大数据技术经验和 ...
- Maven多模块的2种依赖管理策略
在Maven多模块的时候,管理依赖关系是非常重要的,各种依赖包冲突,查询问题起来非常复杂,于是就用到了<dependencyManagement>, 示例说明, 在父模块中: <de ...
