Kubernets二进制安装(7)之部署主控节点服务--apiserver二进制安装
kube-apiserver集群规划
| 主机名 | 角色 | IP地址 |
|---|---|---|
| mfyxw30.mfxyw.com | kube-apiserver主 | 192.168.80.30 |
| mfyxw40.mfyxw.com | kube-apiserver从 | 192.168.80.40 |
温馨提示:这里部署文档以mfyxw30.mfyxw.com主机为例,另外两台主机安装部署方法类似
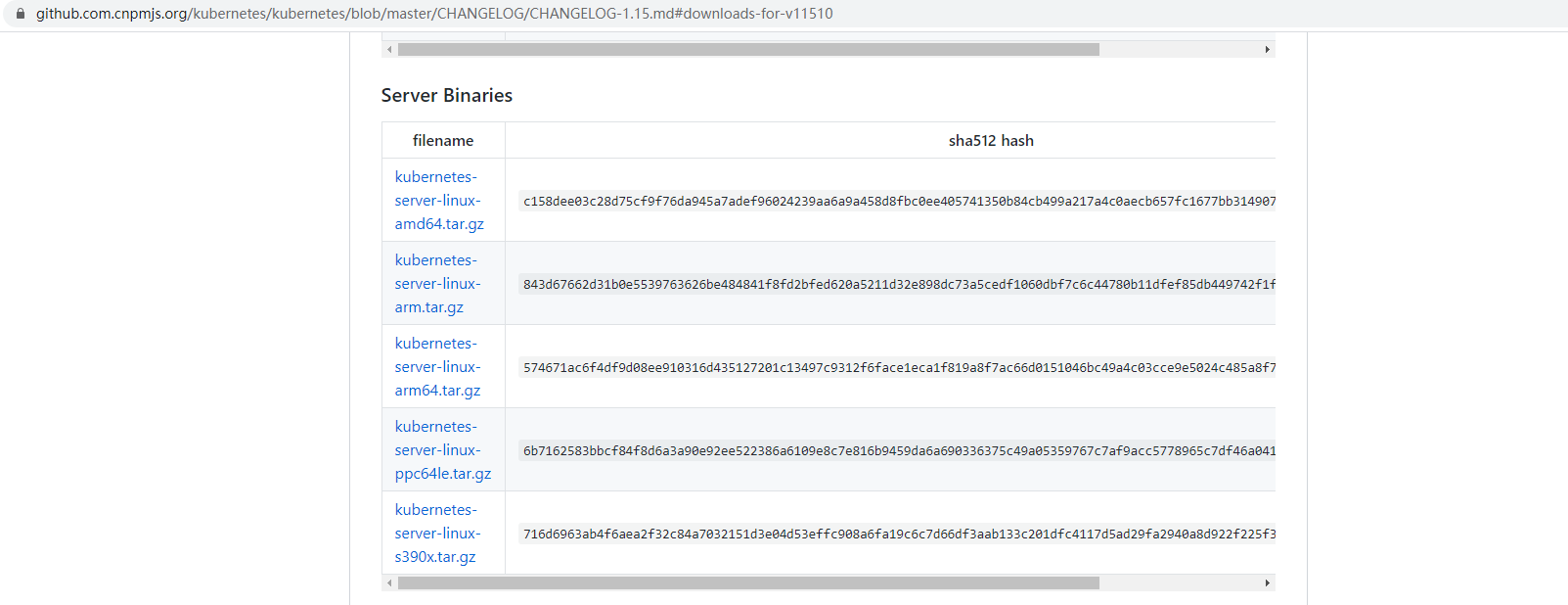
1.下载kubernetes软件
kubernetes的github链接:https://github.com/kubernetes
kubernetes-v1.15.10链接地址:https://dl.k8s.io/v1.15.10/kubernetes-server-linux-amd64.tar.gz
可以登录mfyxw30服务器下载
wget https://dl.k8s.io/v1.15.10/kubernetes-server-linux-amd64.tar.gz
#发现国内没有办法下载。只能自己想办法了。我下载好的kubernetes-v1.15.10上传到网盘
k8s-v1.15.10网盘地址
链接:https://pan.baidu.com/s/1qL_su3YppyyBGz-loKSHfg
提取码:3kfx
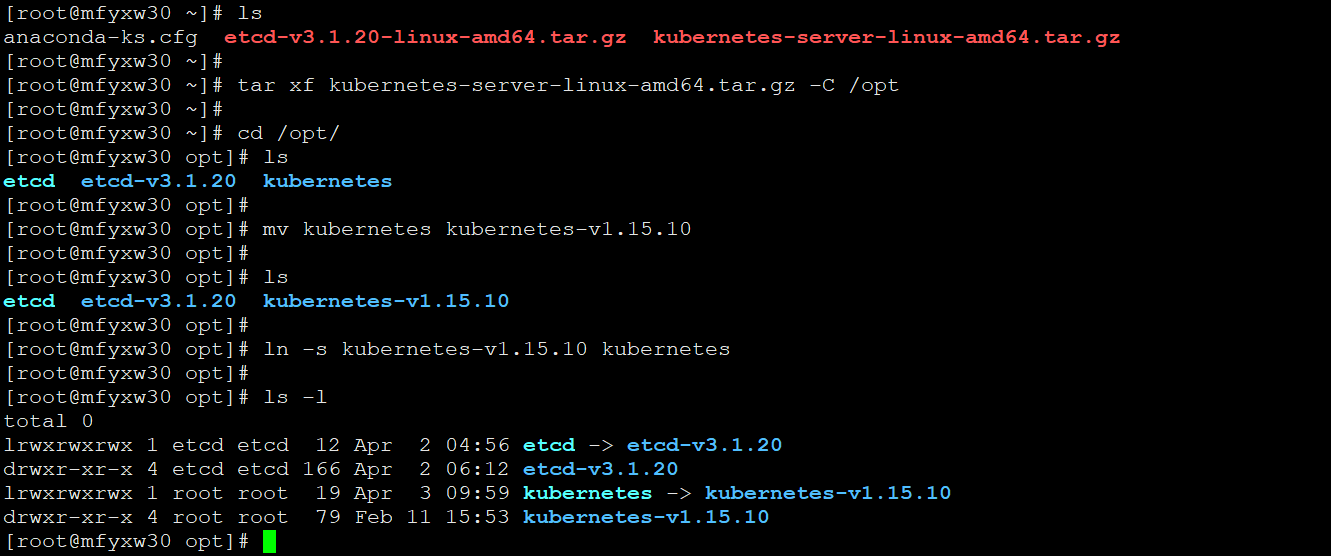
2.把kubernetes上传服务器,解压,软连接
#mfyxw30和mfyxw40都需要执行此操作,以mfyxw30为例
[root@mfyxw30 ~]#tar xf kubernetes-server-linux-amd64.tar.gz -C /opt
[root@mfyxw30 ~]#cd /opt
[root@mfyxw30 opt]#mv kubernetes kubernetes-v1.15.10
[root@mfyxw30 opt]#ln -s kubernetes-v1.15.10 kubernetes
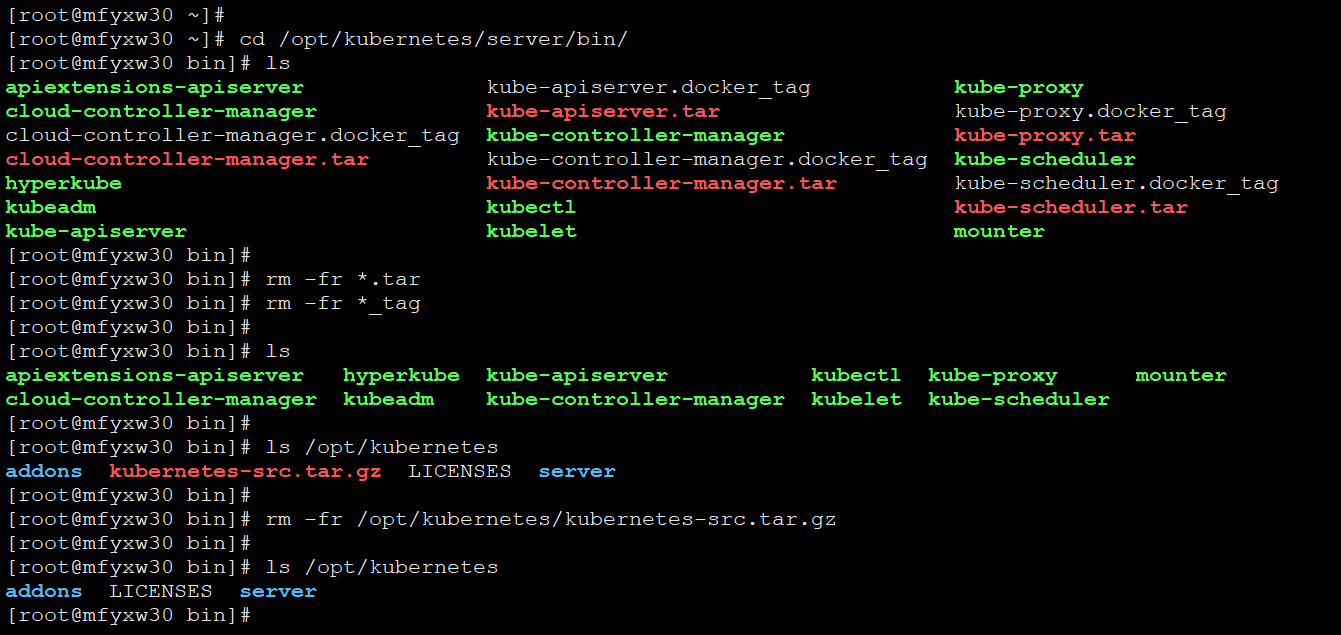
3.删除kuberneters包不需要的文件
在mfyxw30主机上删除kubernetes包不需要的文件
[root@mfyxw30 ~]#cd /opt/kubernetes/server/bin
#tar后缀的是容器镜像包,不是采用kubeadm来安装,故可以删除
[root@mfyxw30 bin]#rm -fr *.tar
[root@mfyxw30 bin]#rm -fr *_tag
#kubernetes-src.tar.gz是kubernetes的go语言写的源码包,在此用不到
[root@mfyxw30 bin]#rm -fr /opt/kubernetes/kubernetes-src.tar.gz
在mfyxw40主机上删除kubernetes包不需要的文件
[root@mfyxw40 ~]#cd /opt/kubernetes/server/bin
#tar后缀的是容器镜像包,不是采用kubeadm来安装,故可以删除
[root@mfyxw40 bin]#rm -fr *.tar
[root@mfyxw40 bin]#rm -fr *_tag
#kubernetes-src.tar.gz是kubernetes的go语言写的源码包,在此用不到
[root@mfyxw40 bin]#rm /opt/kubernetes/kubernetes-src.tar.gz
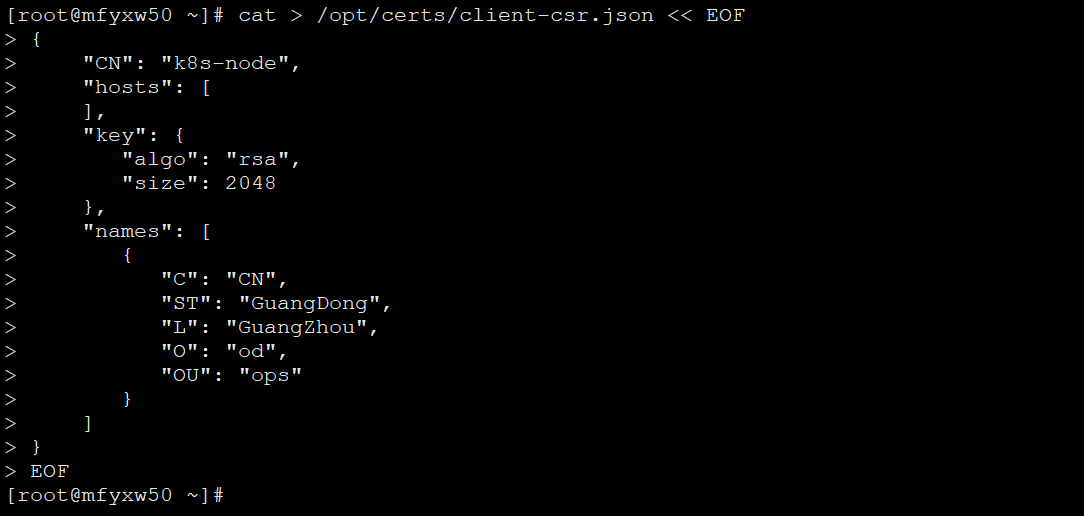
4.创建生成证书签名请求(csr)的JSON配置文件
签发Client证书:apiserver和etcd集群间通信用的证书,在这个通信过程中,etcd是服务端,apiserver是客户端
#生成client证书签名请求配置文件是需要在签发证书的mfyxw50主机上执行
[root@mfyxw50 ~]#cat > /opt/certs/client-csr.json << EOF
{
"CN": "k8s-node",
"hosts": [
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "GuangDong",
"L": "GuangZhou",
"O": "od",
"OU": "ops"
}
]
}
EOF
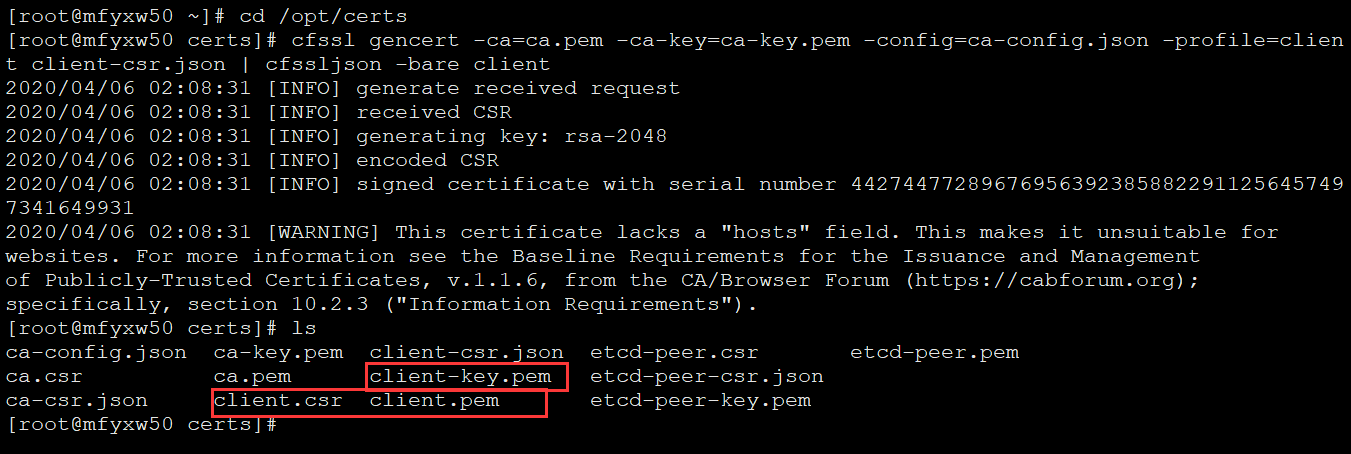
5.生成client证书和私钥
#需要在签发证书主机mfyxw50上执行
[root@mfyxw50 ~]#cd /opt/certs
[root@mfyxw50 certs]#cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=client client-csr.json | cfssljson -bare client
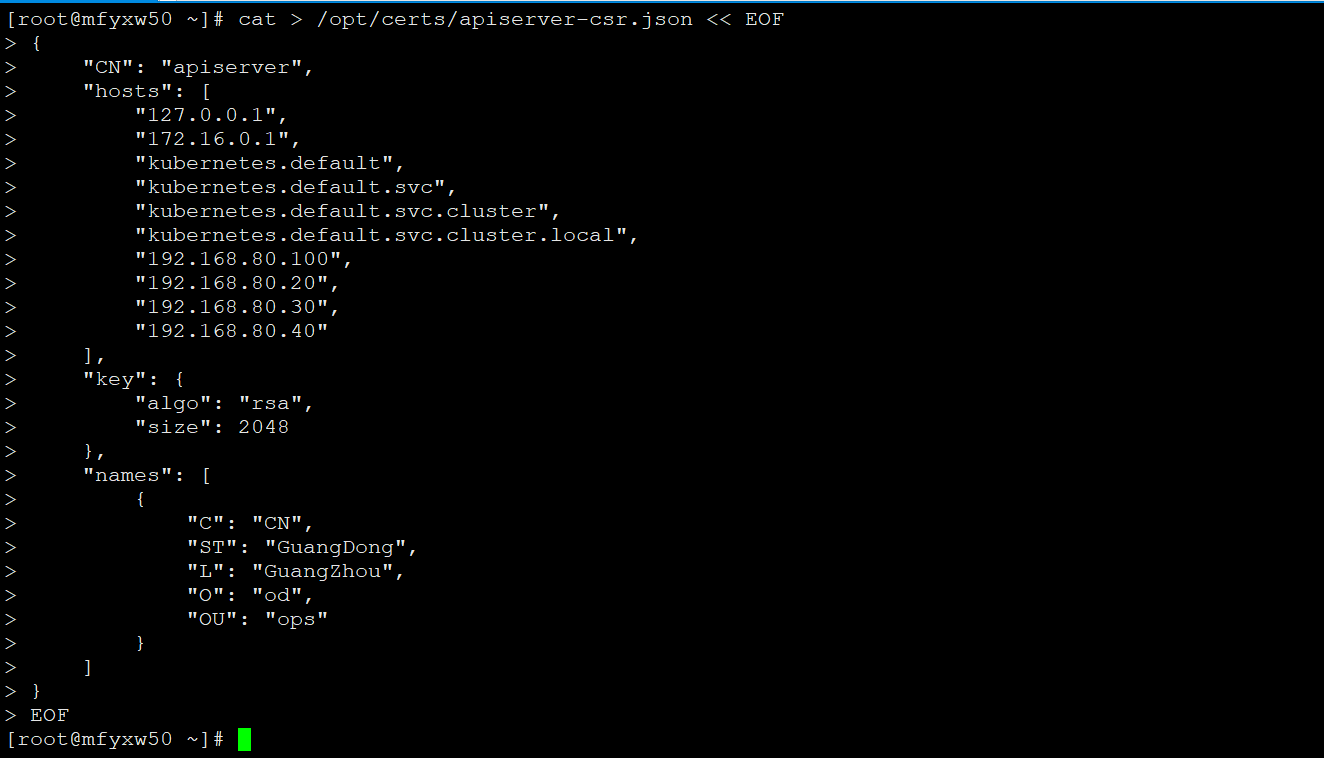
6.创建生成kube-apiserver证书签名请求(csr)的JSON配置文件
#生成kube-apiserver证书签名请求配置文件是需要在签发证书的mfyxw50主机上执行
[root@mfyxw50 ~]# cat > /opt/certs/apiserver-csr.json << EOF
{
"CN": "apiserver",
"hosts": [
"127.0.0.1",
"172.16.0.1",
"kubernetes.default",
"kubernetes.default.svc",
"kubernetes.default.svc.cluster",
"kubernetes.default.svc.cluster.local",
"192.168.80.100",
"192.168.80.20",
"192.168.80.30",
"192.168.80.40"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "GuangDong",
"L": "GuangZhou",
"O": "od",
"OU": "ops"
}
]
}
EOF
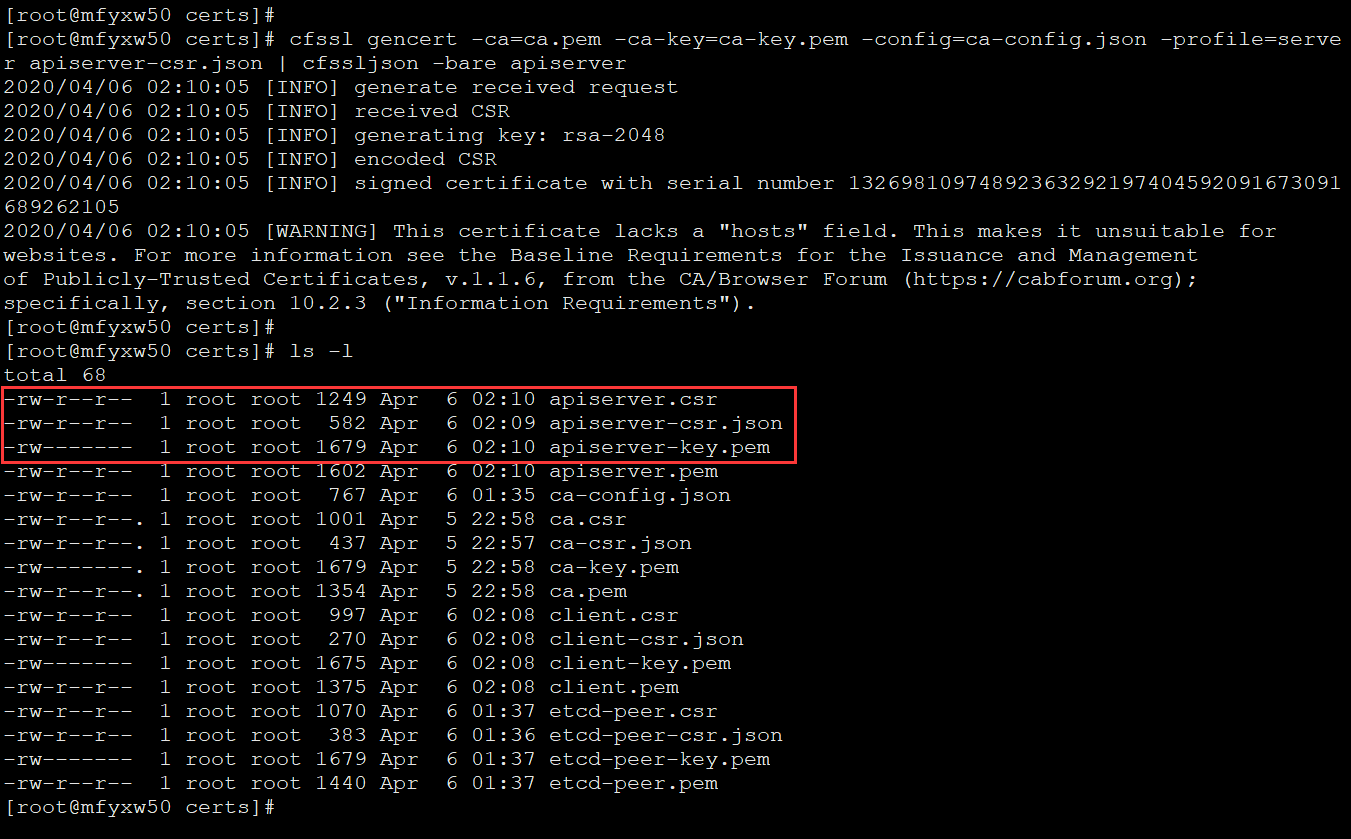
7.生成kube-apiserver证书和私钥
#需要在签发证书主机mfyxw50上执行
[root@mfyxw50 ~]#cd /opt/certs
[root@mfyxw50 certs]#cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=server apiserver-csr.json | cfssljson -bare apiserver
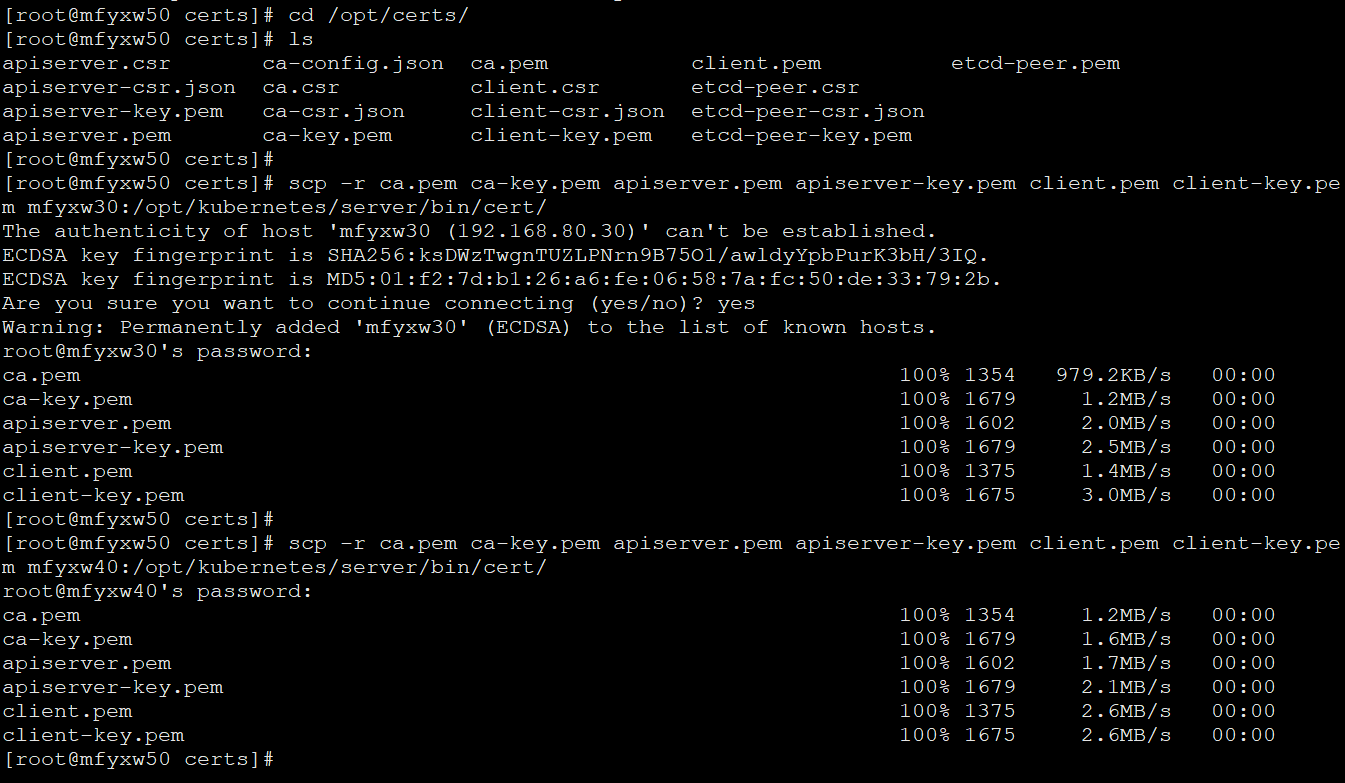
8.将生成的证书复制至各运算节点
#在mfyxw30主机上创建certs目录
[root@mfyxw30 ~]#mkdir -p /opt/kubernetes/server/bin/cert
#在mfyxw40主机上创建cert目录
[root@mfyxw40 ~]#mkdir -p /opt/kubernetes/server/bin/cert
#在mfyxw50(证书签发主机)上把证书和私钥分别复制至mfyxw30和mfyxw40主机下/opt/kubernetes/server/bin/cert目录
[root@mfyxw50 ~]#cd /opt/certs/
[root@mfyxw50 ~]#scp -r ca.pem ca-key.pem apiserver.pem apiserver-key.pem client.pem client-key.pem mfyxw30:/opt/kubernetes/server/bin/cert/
[root@mfyxw50 ~]#scp -r ca.pem ca-key.pem apiserver.pem apiserver-key.pem client.pem client-key.pem mfyxw40:/opt/kubernetes/server/bin/cert/
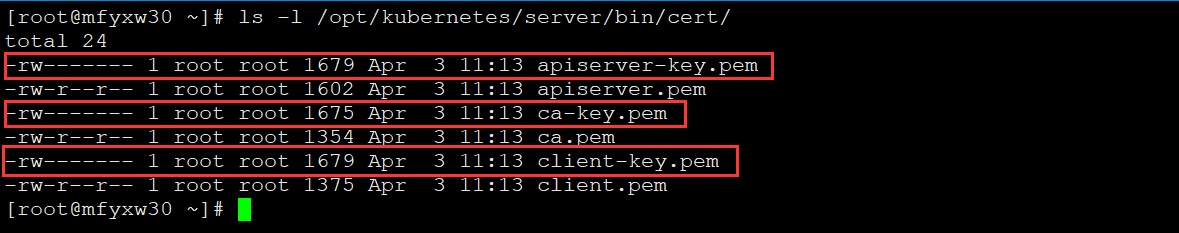
9.查看复制过去的私钥的权限
#分别需要在mfyxw30和mfyxw40主机上查看,在此以mfyxw30截图为例,如果权限不是600,请修改为600
[root@mfyxw30 ~]#ls -l /opt/kubernetes/server/bin/cert/
[root@mfyxw40 ~]#ls -l /opt/kubernetes/server/bin/cert/
10.创建审计日志记录和采集配置文件
分别在mfyxw30和mfyxw40的路径/opt/kubernetes/server/bin/下创建conf目录
[root@mfyxw30 ~]#mkdir -p /opt/kubernetes/server/bin/conf
[root@mfyxw40 ~]#mkdir -p /opt/kubernetes/server/bin/conf
1.在mfyxw30主机上创建审计日志记录和采集配置文件
[root@mfyxw30 ~]#cat > /opt/kubernetes/server/bin/conf/audit.yaml << EOF
apiVersion: audit.k8s.io/v1beta1 # This is required.
kind: Policy
# Don't generate audit events for all requests in RequestReceived stage.
omitStages:
- "RequestReceived"
rules:
# Log pod changes at RequestResponse level
- level: RequestResponse
resources:
- group: ""
# Resource "pods" doesn't match requests to any subresource of pods,
# which is consistent with the RBAC policy.
resources: ["pods"]
# Log "pods/log", "pods/status" at Metadata level
- level: Metadata
resources:
- group: ""
resources: ["pods/log", "pods/status"]
# Don't log requests to a configmap called "controller-leader"
- level: None
resources:
- group: ""
resources: ["configmaps"]
resourceNames: ["controller-leader"]
# Don't log watch requests by the "system:kube-proxy" on endpoints or services
- level: None
users: ["system:kube-proxy"]
verbs: ["watch"]
resources:
- group: "" # core API group
resources: ["endpoints", "services"]
# Don't log authenticated requests to certain non-resource URL paths.
- level: None
userGroups: ["system:authenticated"]
nonResourceURLs:
- "/api*" # Wildcard matching.
- "/version"
# Log the request body of configmap changes in kube-system.
- level: Request
resources:
- group: "" # core API group
resources: ["configmaps"]
# This rule only applies to resources in the "kube-system" namespace.
# The empty string "" can be used to select non-namespaced resources.
namespaces: ["kube-system"]
# Log configmap and secret changes in all other namespaces at the Metadata level.
- level: Metadata
resources:
- group: "" # core API group
resources: ["secrets", "configmaps"]
# Log all other resources in core and extensions at the Request level.
- level: Request
resources:
- group: "" # core API group
- group: "extensions" # Version of group should NOT be included.
# A catch-all rule to log all other requests at the Metadata level.
- level: Metadata
# Long-running requests like watches that fall under this rule will not
# generate an audit event in RequestReceived.
omitStages:
- "RequestReceived"
EOF
2.在mfyxw40主机上创建审计日志记录和采集配置文件
[root@mfyxw40 ~]#cat > /opt/kubernetes/server/bin/conf/audit.yaml << EOF
apiVersion: audit.k8s.io/v1beta1 # This is required.
kind: Policy
# Don't generate audit events for all requests in RequestReceived stage.
omitStages:
- "RequestReceived"
rules:
# Log pod changes at RequestResponse level
- level: RequestResponse
resources:
- group: ""
# Resource "pods" doesn't match requests to any subresource of pods,
# which is consistent with the RBAC policy.
resources: ["pods"]
# Log "pods/log", "pods/status" at Metadata level
- level: Metadata
resources:
- group: ""
resources: ["pods/log", "pods/status"]
# Don't log requests to a configmap called "controller-leader"
- level: None
resources:
- group: ""
resources: ["configmaps"]
resourceNames: ["controller-leader"]
# Don't log watch requests by the "system:kube-proxy" on endpoints or services
- level: None
users: ["system:kube-proxy"]
verbs: ["watch"]
resources:
- group: "" # core API group
resources: ["endpoints", "services"]
# Don't log authenticated requests to certain non-resource URL paths.
- level: None
userGroups: ["system:authenticated"]
nonResourceURLs:
- "/api*" # Wildcard matching.
- "/version"
# Log the request body of configmap changes in kube-system.
- level: Request
resources:
- group: "" # core API group
resources: ["configmaps"]
# This rule only applies to resources in the "kube-system" namespace.
# The empty string "" can be used to select non-namespaced resources.
namespaces: ["kube-system"]
# Log configmap and secret changes in all other namespaces at the Metadata level.
- level: Metadata
resources:
- group: "" # core API group
resources: ["secrets", "configmaps"]
# Log all other resources in core and extensions at the Request level.
- level: Request
resources:
- group: "" # core API group
- group: "extensions" # Version of group should NOT be included.
# A catch-all rule to log all other requests at the Metadata level.
- level: Metadata
# Long-running requests like watches that fall under this rule will not
# generate an audit event in RequestReceived.
omitStages:
- "RequestReceived"
EOF
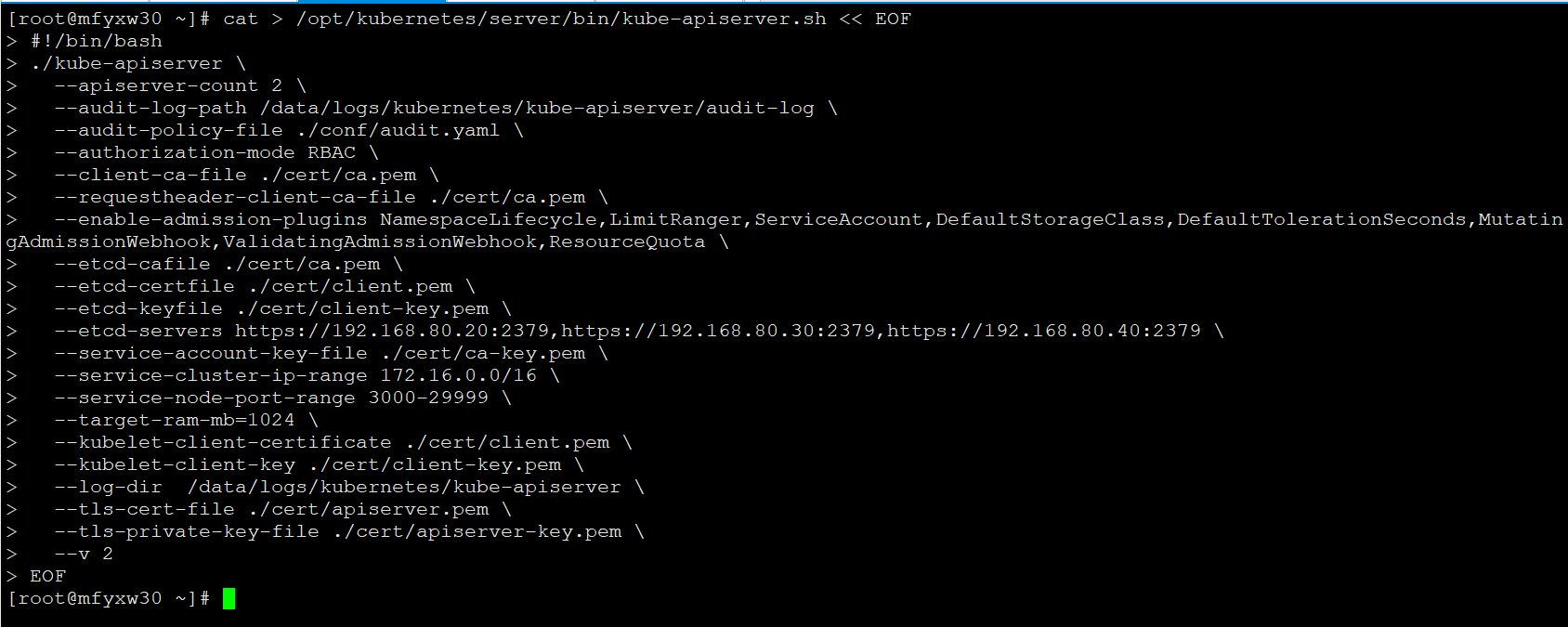
11.创建kube-apiserver启动脚本
在主机mfyxw30上创建kube-apiserver启动脚本
[root@mfyxw30 ~]#cat > /opt/kubernetes/server/bin/kube-apiserver.sh << EOF
#!/bin/bash
./kube-apiserver \
--apiserver-count 2 \
--audit-log-path /data/logs/kubernetes/kube-apiserver/audit-log \
--audit-policy-file ./conf/audit.yaml \
--authorization-mode RBAC \
--client-ca-file ./cert/ca.pem \
--requestheader-client-ca-file ./cert/ca.pem \
--enable-admission-plugins NamespaceLifecycle,LimitRanger,ServiceAccount,DefaultStorageClass,DefaultTolerationSeconds,MutatingAdmissionWebhook,ValidatingAdmissionWebhook,ResourceQuota \
--etcd-cafile ./cert/ca.pem \
--etcd-certfile ./cert/client.pem \
--etcd-keyfile ./cert/client-key.pem \
--etcd-servers https://192.168.80.20:2379,https://192.168.80.30:2379,https://192.168.80.40:2379 \
--service-account-key-file ./cert/ca-key.pem \
--service-cluster-ip-range 172.16.0.0/16 \
--service-node-port-range 3000-29999 \
--target-ram-mb=1024 \
--kubelet-client-certificate ./cert/client.pem \
--kubelet-client-key ./cert/client-key.pem \
--log-dir /data/logs/kubernetes/kube-apiserver \
--tls-cert-file ./cert/apiserver.pem \
--tls-private-key-file ./cert/apiserver-key.pem \
--v 2
EOF
在主机mfyxw40上创建kube-apiserver启动脚本
[root@mfyxw40 ~]#cat > /opt/kubernetes/server/bin/kube-apiserver.sh << EOF
#!/bin/bash
./kube-apiserver \
--apiserver-count 2 \
--audit-log-path /data/logs/kubernetes/kube-apiserver/audit-log \
--audit-policy-file ./conf/audit.yaml \
--authorization-mode RBAC \
--client-ca-file ./cert/ca.pem \
--requestheader-client-ca-file ./cert/ca.pem \
--enable-admission-plugins NamespaceLifecycle,LimitRanger,ServiceAccount,DefaultStorageClass,DefaultTolerationSeconds,MutatingAdmissionWebhook,ValidatingAdmissionWebhook,ResourceQuota \
--etcd-cafile ./cert/ca.pem \
--etcd-certfile ./cert/client.pem \
--etcd-keyfile ./cert/client-key.pem \
--etcd-servers https://192.168.80.20:2379,https://192.168.80.30:2379,https://192.168.80.40:2379 \
--service-account-key-file ./cert/ca-key.pem \
--service-cluster-ip-range 172.16.0.0/16 \
--service-node-port-range 3000-29999 \
--target-ram-mb=1024 \
--kubelet-client-certificate ./cert/client.pem \
--kubelet-client-key ./cert/client-key.pem \
--log-dir /data/logs/kubernetes/kube-apiserver \
--tls-cert-file ./cert/apiserver.pem \
--tls-private-key-file ./cert/apiserver-key.pem \
--v 2
EOF
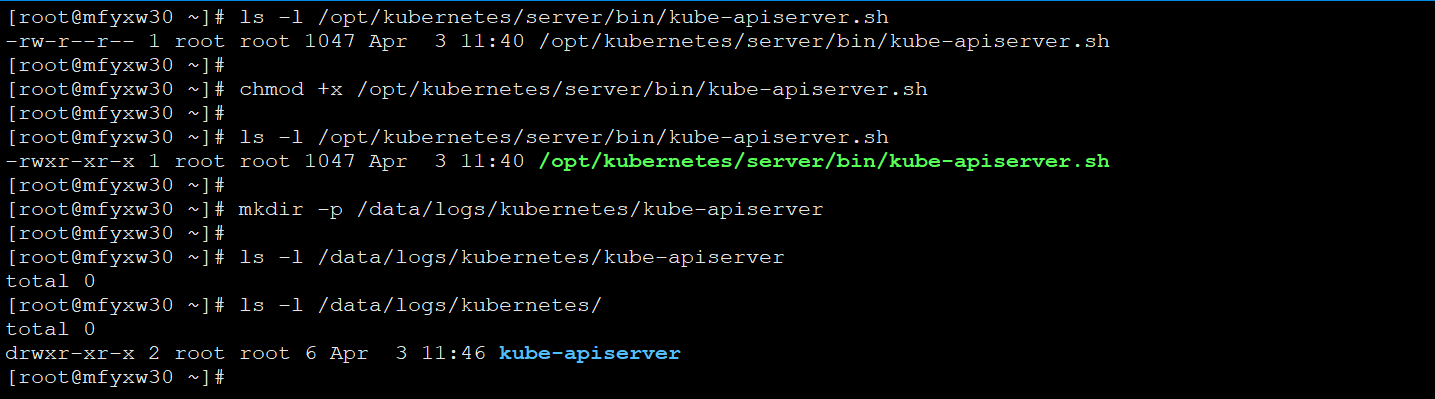
12.调整权限和创建存放kupe-apiserver日志的目录
分别在mfyxw30和mfyxw40主机上对kube-apiserver.sh文件添加可执行权限,并创建存放kube-apiserver的日志文件的目录,以mfyxw30的截图为例
[root@mfyxw30 ~]#chmod +x /opt/kubernetes/server/bin/kube-apiserver.sh
[root@mfyxw30 ~]#mkdir -p /data/logs/kubernetes/kube-apiserver
[root@mfyxw40 ~]#chmod +x /opt/kubernetes/server/bin/kube-apiserver.sh
[root@mfyxw40 ~]#mkdir -p /data/logs/kubernetes/kube-apiserver
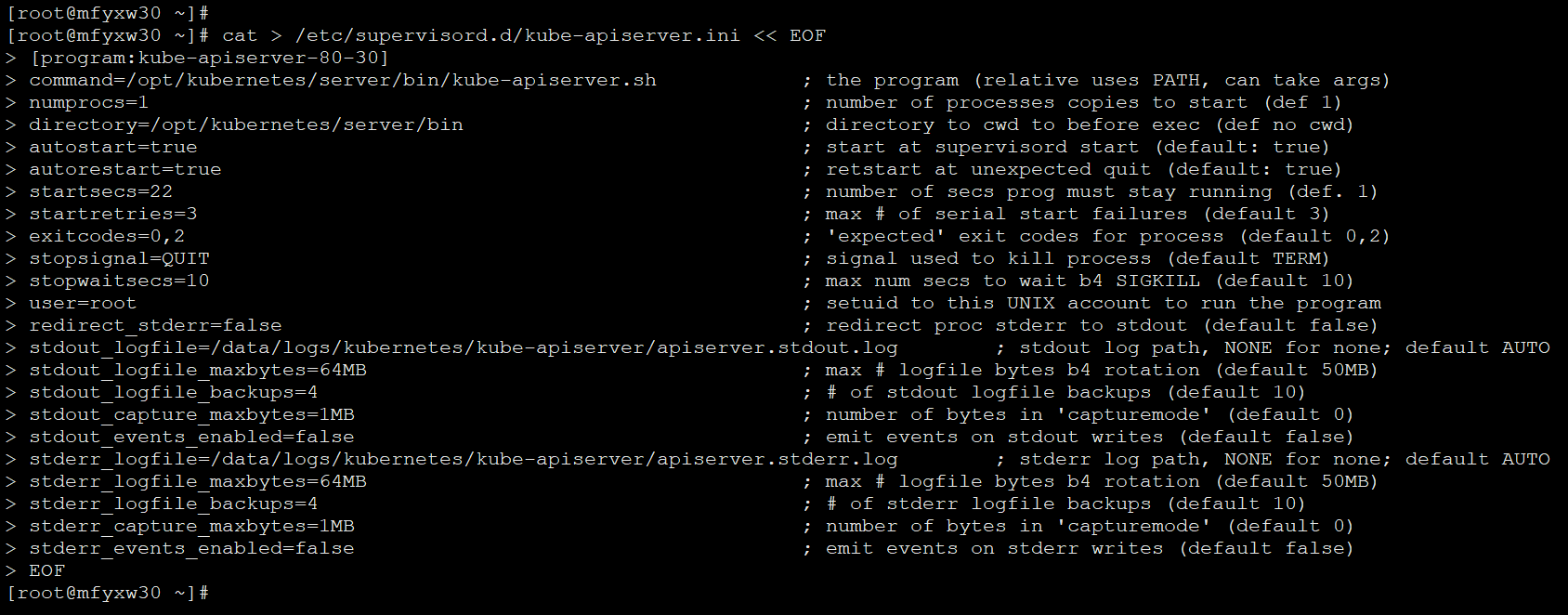
13.创建supervisor配置文件
为mfyxw30主机创建supervisor配置文件
[root@mfyxw30 ~]#cat > /etc/supervisord.d/kube-apiserver.ini << EOF
[program:kube-apiserver-80-30]
command=/opt/kubernetes/server/bin/kube-apiserver.sh ; the program (relative uses PATH, can take args)
numprocs=1 ; number of processes copies to start (def 1)
directory=/opt/kubernetes/server/bin ; directory to cwd to before exec (def no cwd)
autostart=true ; start at supervisord start (default: true)
autorestart=true ; retstart at unexpected quit (default: true)
startsecs=30 ; number of secs prog must stay running (def. 1)
startretries=3 ; max # of serial start failures (default 3)
exitcodes=0,2 ; 'expected' exit codes for process (default 0,2)
stopsignal=QUIT ; signal used to kill process (default TERM)
stopwaitsecs=10 ; max num secs to wait b4 SIGKILL (default 10)
user=root ; setuid to this UNIX account to run the program
redirect_stderr=false ; redirect proc stderr to stdout (default false)
stdout_logfile=/data/logs/kubernetes/kube-apiserver/apiserver.stdout.log ; stdout log path, NONE for none; default AUTO
stdout_logfile_maxbytes=64MB ; max # logfile bytes b4 rotation (default 50MB)
stdout_logfile_backups=4 ; # of stdout logfile backups (default 10)
stdout_capture_maxbytes=1MB ; number of bytes in 'capturemode' (default 0)
stdout_events_enabled=false ; emit events on stdout writes (default false)
stderr_logfile=/data/logs/kubernetes/kube-apiserver/apiserver.stderr.log ; stderr log path, NONE for none; default AUTO
stderr_logfile_maxbytes=64MB ; max # logfile bytes b4 rotation (default 50MB)
stderr_logfile_backups=4 ; # of stderr logfile backups (default 10)
stderr_capture_maxbytes=1MB ; number of bytes in 'capturemode' (default 0)
stderr_events_enabled=false ; emit events on stderr writes (default false)
EOF
为mfyxw40主机创建supervisor配置文件
[root@mfyxw40 ~]#cat > /etc/supervisord.d/kube-apiserver.ini << EOF
[program:kube-apiserver-80-40]
command=/opt/kubernetes/server/bin/kube-apiserver.sh ; the program (relative uses PATH, can take args)
numprocs=1 ; number of processes copies to start (def 1)
directory=/opt/kubernetes/server/bin ; directory to cwd to before exec (def no cwd)
autostart=true ; start at supervisord start (default: true)
autorestart=true ; retstart at unexpected quit (default: true)
startsecs=30 ; number of secs prog must stay running (def. 1)
startretries=3 ; max # of serial start failures (default 3)
exitcodes=0,2 ; 'expected' exit codes for process (default 0,2)
stopsignal=QUIT ; signal used to kill process (default TERM)
stopwaitsecs=10 ; max num secs to wait b4 SIGKILL (default 10)
user=root ; setuid to this UNIX account to run the program
redirect_stderr=false ; redirect proc stderr to stdout (default false)
stdout_logfile=/data/logs/kubernetes/kube-apiserver/apiserver.stdout.log ; stdout log path, NONE for none; default AUTO
stdout_logfile_maxbytes=64MB ; max # logfile bytes b4 rotation (default 50MB)
stdout_logfile_backups=4 ; # of stdout logfile backups (default 10)
stdout_capture_maxbytes=1MB ; number of bytes in 'capturemode' (default 0)
stdout_events_enabled=false ; emit events on stdout writes (default false)
stderr_logfile=/data/logs/kubernetes/kube-apiserver/apiserver.stderr.log ; stderr log path, NONE for none; default AUTO
stderr_logfile_maxbytes=64MB ; max # logfile bytes b4 rotation (default 50MB)
stderr_logfile_backups=4 ; # of stderr logfile backups (default 10)
stderr_capture_maxbytes=1MB ; number of bytes in 'capturemode' (default 0)
stderr_events_enabled=false ; emit events on stderr writes (default false)
EOF
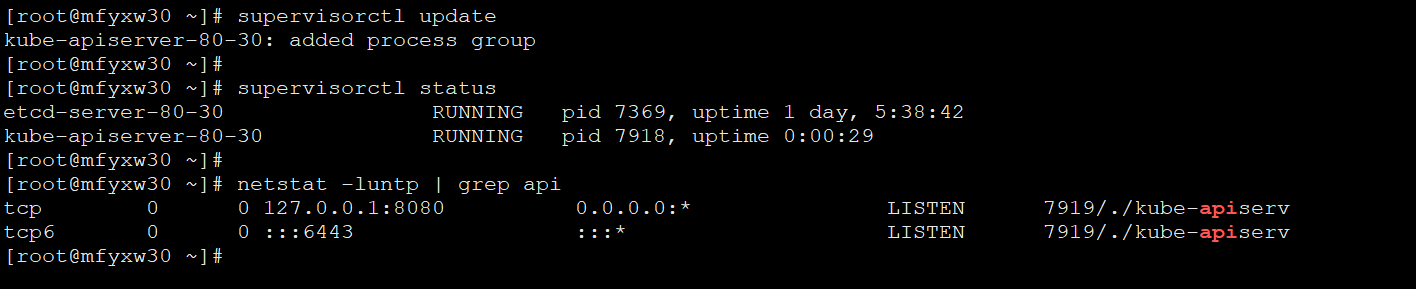
14.启动supervisor服务并检查
在mfyxw30主机上,启动supervisor服务并检查,以mfyxw30图片为例,另一台机器同样方法启动服务和查看
[root@mfyxw30 ~]#supervisorctl update
[root@mfyxw30 ~]#supervisorctl status
[root@mfyxw30 ~]# netstat -luntp | grep api
在mfyxw40主机上,启动supervisor服务并检查
[root@mfyxw40 ~]#supervisorctl update
[root@mfyxw40 ~]#supervisorctl status
[root@mfyxw40 ~]# netstat -luntp | grep api
Kubernets二进制安装(7)之部署主控节点服务--apiserver二进制安装的更多相关文章
- Kubernets二进制安装(7)之部署主控节点服务--apiserver简介
API Server简介 Kubernetes API Server提供了K8S各类资源对象(如:pod.RC.Service等)的增删改查及watch等HTTP Rest接口,是整个系统的数据总线和 ...
- Kubernets二进制安装(6)之部署主控节点服务--etcd
Etcd是Kubernetes集群中的一个十分重要的组件,用于保存集群所有的网络配置和对象的状态信息. 整个kubernetes系统中一共有两个服务需要用到etcd用来协同和存储配置,分别是 网络插件 ...
- Kubernets二进制安装(9)之部署主控节点控制器controller-manager
kube-controller-manager运行控制器,它们是处理集群中常规任务的后台线程 Controller Manager就是集群内部的管理控制中心,由负责不同资源的多个Controller构 ...
- Kubernets二进制安装(10)之部署主控节点部署调度器服务kube-scheduler
Kubernetes Scheduler是一个策略丰富.拓扑感知.工作负载特定的功能,调度器显著影响可用性.性能和容量.调度器需要考虑个人和集体的资源要求.服务质量要求.硬件/软件/政策约束.亲和力和 ...
- Kubernets二进制安装(12)之部署Node节点服务的kube-Proxy
kube-proxy是Kubernetes的核心组件,部署在每个Node节点上,它是实现Kubernetes Service的通信与负载均衡机制的重要组件; kube-proxy负责为Pod创建代理服 ...
- Kubernets二进制安装(11)之部署Node节点服务的kubelet
集群规划 主机名 角色 IP地址 mfyxw30.mfyxw.com kubelet 192.168.80.30 mfyxw40.mfyxw.com kubelet 192.168.80.40 注意: ...
- 说说单节点集群里安装hive、3\5节点集群里安装hive的诡异区别
这几天,无意之间,被这件事情给迷惑,不解!先暂时贴于此,以后再解决! 详细问题如下: 在hive的安装目录下(我这里是 /home/hadoop/app/hive-1.2.1),hive的安装目录的l ...
- MySQL的安装(比较详细的安装步骤,包括客户端和服务端的安装,还有环境变量的配置以及使用Windows service启动MySQL)
1.MySQL官网下载操作系统对应的MySQL安装包,解压之后就可以直接使用(免安装). MySQL安装包,一种是MySQL Enterprise Edition (commercial)企业版,还有 ...
- Dubbo入门到精通学习笔记(八):ActiveMQ的安装与使用(单节点)、Redis的安装与使用(单节点)、FastDFS分布式文件系统的安装与使用(单节点)
文章目录 ActiveMQ的安装与使用(单节点) 安装(单节点) 使用 目录结构 edu-common-parent edu-demo-mqproducer edu-demo-mqconsumer 测 ...
随机推荐
- 什么是xss攻击
概述: XSS攻击是Web攻击中最常见的攻击方法之一,它是通过对网页注入可执行代码且成功地被浏览器 执行,达到攻击的目的,形成了一次有效XSS攻击,一旦攻击成功,它可以获取用户的联系人列 表,然后向联 ...
- uni-app开发经验分享二: uni-app生命周期记录
应用生命周期(仅可在App.vue中监听) 页面生命周期(在页面中添加) 当页面中需要用到下拉刷新功能时,打开pages.json,在"globalStyle"里设置"e ...
- Linux、JDK、Netty中的NIO与零拷贝
一.先理解内核空间与用户空间 Linux 按照特权等级,把进程的运行空间分为内核空间和用户空间,分别对应着下图中, CPU 特权等级分为4个,Linux 使用 Ring 0 和 Ring 3. 内核空 ...
- unstable sort
$sort (aggregation) - MongoDB Manual https://docs.mongodb.com/manual/reference/operator/aggregation/ ...
- 题解 P3833 【[SHOI2012]魔法树】
题目 直通车 很显然这是个树刨的板子,树上链查询和子树查询 注意: 1.这个点的树根为 0 而不是 1 所以注意读图时点标号 +1 就解决了 2.注意数据范围\(2^{32}\) 然后板子就能过了 n ...
- loj10161 叶子的颜色
CQOI 2009 给一棵有 mm 个节点的无根树,你可以选择一个度数大于 11 的节点作为根,然后给一些节点(根.内部节点.叶子均可)着以黑色或白色.你的着色方案应保证根节点到各叶子节点的简单路径上 ...
- PowerQuery合并查询原理
PowerQuery的合并查询比Excel中的VLOOKUP更加强大,下面对查询的类型做一个梳理, 1.左外部(第一个中的所有行,第二个中的匹配行):用左边表内的所有行去右边找它的匹配项 2.右外部( ...
- Grafana Prometheus系统监控Redis服务
Grafana Prometheus系统监控Redis服务 一.Grafana Prometheus系统监控Redis服务 1.1流程 1.2安装redis_exporter 1.3配置prometh ...
- BGP总结(二)
BGP属性 路由器发送关于目标网络的BGP更新消息,更新的度量值被称为路径属性.属性可以是公认的或可选的.强制的或自由决定的.传递的或非传递的.属性也可以是部分的.并非组织的和有组合都是合法的,路径属 ...
- idea中类注释和方法注释的设置
类注释设置 近几年版本的idea在设置类名时从Includes中引用文件,所以只需要在被引用的文件中设置对应注释即可. /** *@className: ${NAME} *@description: ...
