Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap
Nmap is a network discovery tool that can be used to gather detailed information about any client or network.
We shall have a look at some of its uses to discover connected clients and gather information about them.
We are going to use Zenmap - the GUI for Namp.
1. Ping scan: Very quick - only shows connected clients.

2. Quick scan plus: Quick - shows MAC and open clients.
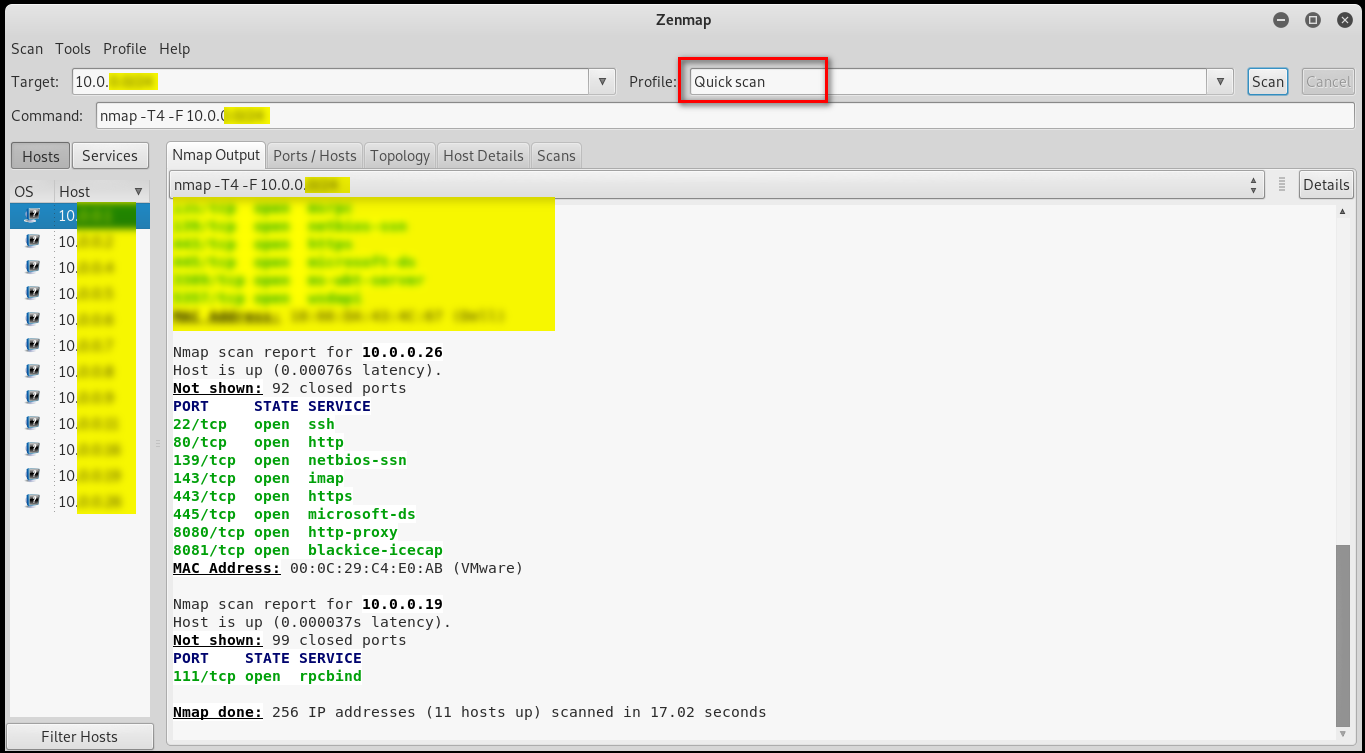
3. Quick scan plus: Slower than the 2 above, more detailed info.

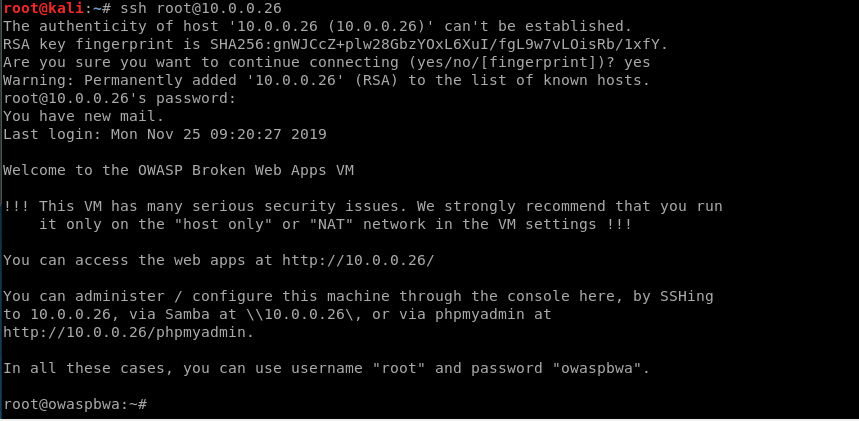
Many people are too lazy to change the password, so I log in to the target victim pc through default username/password.
Ethical Hacking - NETWORK PENETRATION TESTING(13)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- yii2.0AR两表联查
首先,建两个关联表. 表一 -- Table structure for article -- ---------------------------- DROP TABLE IF EXISTS `a ...
- 腾讯云Redis混合存储版重磅推出,万字长文助你破解缓存难题!
导语 | 缓存+存储的系统架构是目前常见的系统架构,缓存层负责加速访问,存储层负责存储数据.这样的架构需要业务层或者是中间件去实现缓存和存储的双写.冷热数据的交换,同时还面临着缓存失效.缓存刷脏.数据 ...
- Java架构师如何学习?
引言 古人云:"活到老,学到老."互联网算是最辛苦的行业之一,"加班"对工程师来说已是"家常便饭",同时互联网技术又日新月异,很多工程师都疲 ...
- Docker 快速入门(一)- 情况介绍和安装
欢迎您! 很高兴您想学习 Docker . 这个页面包含了如何开始使用 Docker 的循序渐进的说明. Docker 快速入门培训模块教你如何: 设置 Docker 环境(在本页) 构建并运行您的镜 ...
- dart快速入门教程 (5)
5.函数 5.1.函数定义 语法: 返回值类型 函数名(参数类型 参数1, 参数类型 参数2,...) { // 函数体 return '返回值' } 举例: void main() { print( ...
- webpack入门进阶(2)
1.4.webpack-dev-server webpack-dev-server是我们在开发阶段需要用到的一个服务器,它会把代码打包到内存,我们可以通过http的方式访问到打包到内存的代码 安装 n ...
- 最简单的jQuery轮播图(原理解析)
html: <div class="middle_right"> <div id="lunbobox"> <div id=&quo ...
- StringBuider 在什么条件下、如何使用效率更高?
声明:本文首发于博客园,作者:后青春期的Keats:地址:https://www.cnblogs.com/keatsCoder/ 转载请注明,谢谢! 引言 都说 StringBuilder 在处理字符 ...
- JavaScript基础对象创建模式之模块模式(Module Pattern)(025)
模块模式可以提供软件架构,为不断增长的代码提供组织形式.JavaScript没有提供package的语言表示,但我们可以通过模块模式来分解并组织 代码块,这些黑盒的代码块内的功能可以根据不断变化的软件 ...
- Rancher1.6 部署prometheus
一.rancher基础配置 镜像:prom/prometheus:latest 映射端口:9090:9090 服务连接: blackbox-exporter cadvisor node-exporte ...
