Kali linux 2016.2(Rolling)中metasploit的端口扫描
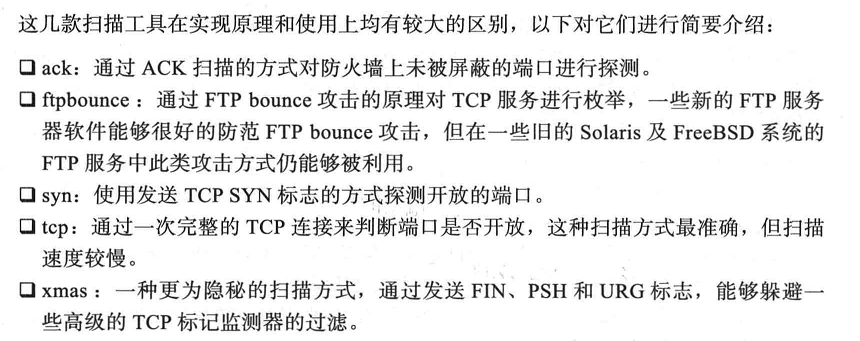
目前常见的端口扫描技术一般有如下几类: TCP Connect、TCP SYN、TCP ACK、TCP FIN。

Metasploit中的端口扫描器
Metasploit的辅助模块中提供了几款实用的端口扫描器。可以输入search portscan命令找到相关的端口扫描器。如下

root@kali:~# msfconsole
...... msf > search portscan Matching Modules
================ Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/scanner/http/wordpress_pingback_access normal Wordpress Pingback Locator
auxiliary/scanner/natpmp/natpmp_portscan normal NAT-PMP External Port Scanner
auxiliary/scanner/portscan/ack normal TCP ACK Firewall Scanner
auxiliary/scanner/portscan/ftpbounce normal FTP Bounce Port Scanner
auxiliary/scanner/portscan/syn normal TCP SYN Port Scanner
auxiliary/scanner/portscan/tcp normal TCP Port Scanner
auxiliary/scanner/portscan/xmas normal TCP "XMas" Port Scanner
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner msf >
Metasploit中ack扫描模块的使用过程
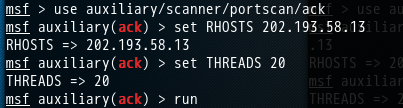
msf > use auxiliary/scanner/portscan/ack
msf auxiliary(ack) > set RHOSTS 202.193.58.13
RHOSTS => 202.193.58.13
msf auxiliary(ack) > set THREADS
THREADS =>
msf auxiliary(ack) > run
Metasploit中ftpbounce扫描模块的使用过程

msf > use auxiliary/scanner/portscan/ftpbounce
msf auxiliary(ftpbounce) > set RHOSTS 202.193.58.13
RHOSTS => 202.193.58.13
msf auxiliary(ftpbounce) > set THREADS
THREADS =>
msf auxiliary(ftpbounce) > run
[-] Auxiliary failed: Msf::OptionValidateError The following options failed to validate: BOUNCEHOST.
msf auxiliary(ftpbounce) >
Metasploit中tcp扫描模块的使用过程
msf > use auxiliary/scanner/portscan/tcp
msf auxiliary(tcp) > set RHOSTS 202.193.58.13
RHOSTS => 202.193.58.13
msf auxiliary(tcp) > set THREADS
THREADS =>
msf auxiliary(tcp) > run [*] 202.193.58.13: - 202.193.58.13: - TCP OPEN
[*] 202.193.58.13: - 202.193.58.13: - TCP OPEN
[*] 202.193.58.13: - 202.193.58.13: - TCP OPEN
[*] 202.193.58.13: - 202.193.58.13: - TCP OPEN
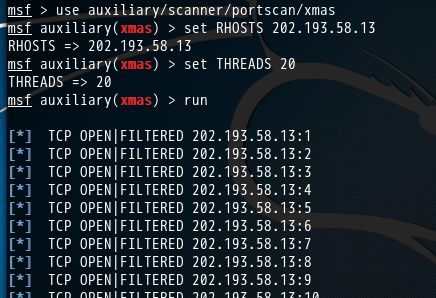
Metasploit中xmas扫描模块的使用过程
msf > use auxiliary/scanner/portscan/xmas
msf auxiliary(xmas) > set RHOSTS 202.193.58.13
RHOSTS => 202.193.58.13
msf auxiliary(xmas) > set THREADS
THREADS =>
msf auxiliary(xmas) > run [*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
[*] TCP OPEN|FILTERED 202.193.58.13:
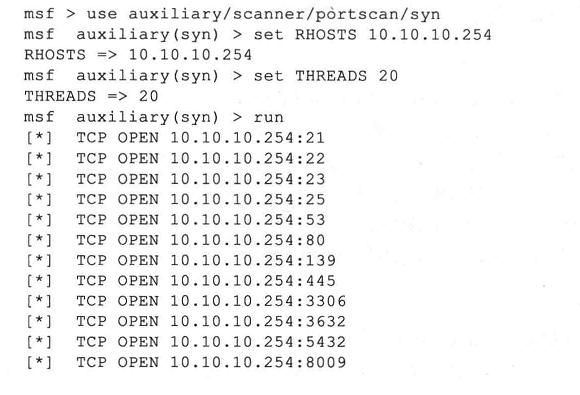
Metasploit中syn扫描模块的使用过程
在一般的情况下,推荐使用syn端口扫描器,因为它的扫描速度较快、结果准确切不容易被对方察觉。下面是针对网关服务器(Ubuntu Metasploitable)主机的扫描结果,可以看出与Nmap的扫描结果基本一致。如下。
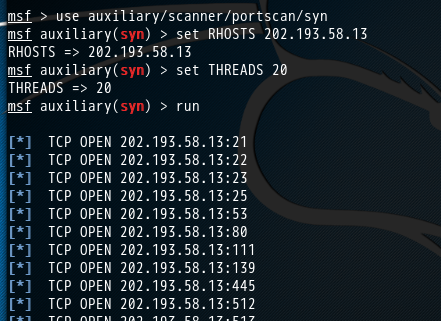
msf > use auxiliary/scanner/portscan/syn
msf auxiliary(syn) > set RHOSTS 202.193.58.13
RHOSTS => 202.193.58.13
msf auxiliary(syn) > set THREADS 20
THREADS => 20
msf auxiliary(syn) > run [*] TCP OPEN 202.193.58.13:21
[*] TCP OPEN 202.193.58.13:22
[*] TCP OPEN 202.193.58.13:23
[*] TCP OPEN 202.193.58.13:25
[*] TCP OPEN 202.193.58.13:53
[*] TCP OPEN 202.193.58.13:80
[*] TCP OPEN 202.193.58.13:111
[*] TCP OPEN 202.193.58.13:139
[*] TCP OPEN 202.193.58.13:445
[*] TCP OPEN 202.193.58.13:512
[*] TCP OPEN 202.193.58.13:513
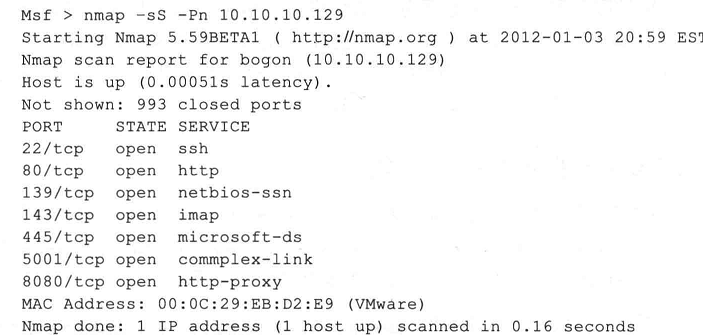
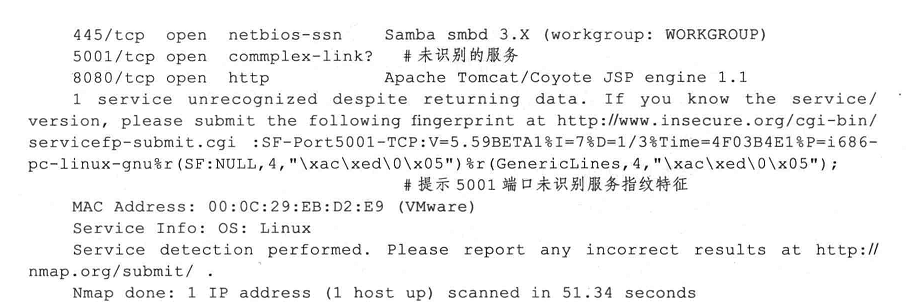
当然,大家也可以拿下面的主机来扫描

Metasploit中sap_router_portscanner扫描模块的使用过程

msf > use auxiliary/scanner/sap/sap_router_portscanner
msf auxiliary(sap_router_portscanner) > set RHOSTS 202.193.58.13
RHOSTS => 202.193.58.13
msf auxiliary(sap_router_portscanner) > set THREADS
THREADS =>
msf auxiliary(sap_router_portscanner) > run
[-] Auxiliary failed: Msf::OptionValidateError The following options failed to validate: RHOST, TARGETS.
msf auxiliary(sap_router_portscanner) >
Metasploit中也可以使用namp
常用nmap扫描类型参数:
-sT:TCP connect扫描
-sS:TCP syn扫描
-sF/-sX/-sN:通过发送一些标志位以避开设备或软件的检测
-sP:ICMP扫描
-sU:探测目标主机开放了哪些UDP端口
-sA:TCP ACk扫描
扫描选项:
-Pn:在扫描之前,不发送ICMP echo请求测试目标是否活跃
-O:辨识操作系统等信息
-F:快速扫描模式
-p<端口范围>:指定端口扫描范围
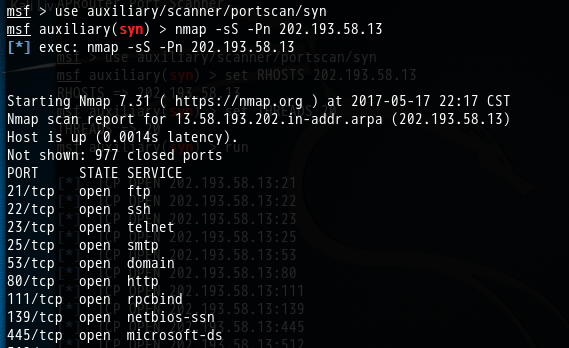
msf auxiliary(syn) > nmap -sS -Pn 202.193.58.13
[*] exec: nmap -sS -Pn 202.193.58.13 Starting Nmap 7.31 ( https://nmap.org ) at 2017-05-17 22:17 CST
Nmap scan report for 13.58.193.202.in-addr.arpa (202.193.58.13)
Host is up (.0014s latency).
Not shown: closed ports
PORT STATE SERVICE
/tcp open ftp
/tcp open ssh
/tcp open telnet
/tcp open smtp
/tcp open domain
/tcp open http
/tcp open rpcbind
/tcp open netbios-ssn
/tcp open microsoft-ds
/tcp open exec
/tcp open login
/tcp open shell
/tcp open rmiregistry
/tcp open ingreslock
/tcp open nfs
/tcp open ccproxy-ftp
/tcp open mysql
/tcp open postgresql
/tcp open vnc
/tcp open X11
/tcp open irc
/tcp open ajp13
/tcp open unknown
MAC Address: :AD::::5C (Unknown) Nmap done: IP address ( host up) scanned in 1.49 seconds
msf auxiliary(syn) >

msf auxiliary(syn) > nmap -sV -Pn 202.193.58.13
[*] exec: nmap -sV -Pn 202.193.58.13 Starting Nmap 7.31 ( https://nmap.org ) at 2017-05-17 22:18 CST
Nmap scan report for 13.58.193.202.in-addr.arpa (202.193.58.13)
Host is up (.0016s latency).
Not shown: closed ports
PORT STATE SERVICE VERSION
/tcp open ftp vsftpd 2.3.
/tcp open ssh OpenSSH .7p1 Debian 8ubuntu1 (protocol 2.0)
/tcp open telnet Linux telnetd
/tcp open smtp Postfix smtpd
/tcp open domain?
/tcp open http?
/tcp open rpcbind?
/tcp open netbios-ssn?
/tcp open microsoft-ds?
/tcp open exec netkit-rsh rexecd
/tcp open login?
/tcp open shell Netkit rshd
/tcp open rmiregistry?
/tcp open shell Metasploitable root shell
/tcp open nfs?
/tcp open ccproxy-ftp?
/tcp open mysql MySQL 5.0.51a-3ubuntu5
/tcp open postgresql?
/tcp open vnc VNC (protocol 3.3)
/tcp open X11?
/tcp open irc Unreal ircd
/tcp open ajp13?
/tcp open unknown
MAC Address: :AD::::5C (Unknown)
Service Info: Hosts: metasploitable.localdomain, irc.Metasploitable.LAN; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: IP address ( host up) scanned in 22.50 seconds
msf auxiliary(syn) >
可以,与下面进行对比。
kali 2.0 linux中的Nmap的端口扫描功能
当然,大家也可以拿下面的主机来扫描


Kali linux 2016.2(Rolling)中metasploit的端口扫描的更多相关文章
- MetaSploit攻击实例讲解------社会工程学set攻击(kali linux 2016.2(rolling))(详细)
不多说,直接上干货! 首先,如果你是用的BT5,则set的配置文件是在 /pentest/exploits/set/set_config下. APACHE_SERVER=ONSELF_SIGNED_A ...
- MetaSploit攻击实例讲解------Metasploit自动化攻击(包括kali linux 2016.2(rolling) 和 BT5)
不多说,直接上干货! 前期博客 Kali linux 2016.2(Rolling)里Metasploit连接(包括默认和自定义)的PostgreSQL数据库 Kali linux 2016.2(Ro ...
- MetaSploit攻击实例讲解------终端下PostgreSQL数据库的使用(包括kali linux 2016.2(rolling) 和 BT5)
不多说,直接上干货! 配置msf连接postgresql数据库 我这里是使用kali linux 2016.2(rolling) 用过的博友们都知道,已经预安装好了PostgreSQL. 1. p ...
- MetaSploit攻击实例讲解------工具Meterpreter常用功能介绍(kali linux 2016.2(rolling))(详细)
不多说,直接上干货! 说在前面的话 注意啦:Meterpreter的命令非常之多,本篇博客下面给出了所有,大家可以去看看.给出了详细的中文 由于篇幅原因,我只使用如下较常用的命令. 这篇博客,利用下面 ...
- MetaSploit攻击实例讲解------攻击445端口漏洞(kali linux 2016.2(rolling))(详细)
不多说,直接上干货! 大家,相信最近的这个事件,对于445端口已经是非常的小心了.勒索病毒 445端口是一个毁誉参半的端口,有了它我们可以在局域网中轻松访问各种共享文件夹或共享打印机,但也正是因为有了 ...
- Kali linux 2016.2 的 plyload模块之meterpreter plyload详解
不多说,直接上干货! 前期博客 Kali linux 2016.2(Rolling)中的payloads模块详解 当利用成功后尝试运行一个进程,它将在系统进程列表里显示,即使在木马中尝试执行系统命令, ...
- Kali linux 2016.2(Rolling)中的Metasploit如何更新与目录结构初步认识
如何更新MSF 1.Windows平台 方法1: 运行msfupdate.bat 在msfconsole里执行命令svn update 或者 方法2: 2.unix/linux平台 方法1: 运行m ...
- Kali linux 2016.2(Rolling)中的payloads模块详解
不多说,直接上干货! 前期博客 Kali linux 2016.2(Rolling)中的Exploits模块详解 payloads模块,也就是shellcode,就是在漏洞利用成功后所要做的事情.在M ...
- Kali linux 2016.2(Rolling)里Metasploit连接(包括默认和自定义)的PostgreSQL数据库之后的切换到指定的工作空间
不多说,直接上干货! 为什么要这么做? 答: 方便我们将扫描不同的目标或目标的不同段,进行归类.为了更好的后续工作! 前期博客 Kali linux 2016.2(Rolling)里Metasploi ...
随机推荐
- Android应用常规开发技巧——善用组件生命周期
数据管理 对于仅仅读数据.一种经常使用的管理模式是在onCreate函数中进行数据的载入,直到组件的onDestory函数被调用时在进行释放. // 缓存仅仅读的数据 private Object r ...
- [Javascript] Delegate JavaScript (ES6) generator iteration control
We can execute generators from generators, and delegate the iteration control with the yield* keywor ...
- 博客迁移到reetsee.com
正如上一篇博客所言.眼下CSDN的博客已经基本完毕它的使命了.感谢CSDN带给我的全部美好回顾. 如今我想尝试一下自己维护一个博客,所以博客的全部内容都迁移到了reetsee.com. 以后博客更新会 ...
- 对Shell几个冷知识的总结(IFS,数组,替换,分割,查找)
IFS: 对IFS的用处直接进行说明,详细IFS是干什么的...自行谷歌 首先创建一个 "a a",和"a"的文件: 然后我们 ls查看一下: --> l ...
- ARIMA模型实例讲解——网络流量预测可以使用啊
ARIMA模型实例讲解:时间序列预测需要多少历史数据? from:https://www.leiphone.com/news/201704/6zgOPEjmlvMpfvaB.html 雷锋网按:本 ...
- [JZOJ NOIP2018模拟10.20 B组]
T1:原根(math) 题目链接: http://172.16.0.132/senior/#contest/show/2532/0 题目: 题解: 一个数m原根的个数是$\phi{(\phi{(m)} ...
- C#线程调用带参数的方法,给控件赋值
System.Threading.Thread thread = new System.Threading.Thread(() => { //各种业务 //定义一个委托 public deleg ...
- AOJ 0118: Property Distribution (简单DFS)
题目链接:http://judge.u-aizu.ac.jp/onlinejudge/description.jsp?id=0118 题意:给定一个矩阵,同类字符相连的为一个块,问总共有几个块. 输入 ...
- e.Row.Attributes.Add
其实看到属性这个单词,还有点发憷呢,C#里面有个关键词是Attributes, 搞了半天貌似没有弄清楚 e.Row.Attributes.Add()函数的介绍,包括参数,什么是Attributes 就 ...
- 【原创】Apache和Tomcat实现动静分离
集群中每个节点都启用了页面静态化功能,所以,为了防止单个节点刷新造成找不到页面问题,将每个节点刷新的页面都放入apache虚拟目录下,由apache统一来处理.静态页面由apache处理,动态页面仍然 ...