Kubernetes Ingress-nginx使用
简介
Kubernetes 提供了两种内建的云端负载均衡机制( cloud load balancing )用于发布公共应用, 工作于传输层的 Service 资源,它实现的是 TCP 负载均衡器”,另种是Ingress 资源,它 现的是“ HTTP(S )负载均衡器”
Ingress和Ingress Controller
Ingress是Kubernetes API的标准资源类型之一,它其实就是基于DNS名称(host)或URL路径把请求转发至指定的Service资源的规则,用于将集群外部的请求流量转发至集群内部完成服务发布。然而,Ingess资源自身并不能运行“流量穿透”,它仅仅是一组路由规则的集合,这些规则要想真正发挥作用还需其它功能的辅助,如监听某个套接字上,根据这些规则匹配机制路由请求流量:这种能够为Ingress资源监听套接字并转发流量的组件称之为Ingress控制器
注意:
不同于 Deployment 控制器等 Ingress 控制器并不直接运行为 kube-controller-rnanager的一部 ,它是Kubemetes集群的重要附件类似于 CoreDNS 需要在集群单独部署
1. 部署Ingress-Controller
此处部署3.0版本
在你需要部署的node节点上拉去Ingerss-Controller镜像
[root@k8s-master01 daem]# docker pull quay.io/kubernetes-ingress-controller/nginx-ingress-controller:0.30.0
进入到GitHub上将mandatory.yaml复制到node节点上
[root@k8s-master01 ingressdeploy]# cat mandatory.yaml
apiVersion: v1
kind: Namespace
metadata:
name: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: nginx-configuration
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
#data:
# whitelist-source-range: 192.168.29.102 #白名单,允许某个IP或IP段的访问
# block-cidrs: 192.168.29.101 #黑名单拒绝访问
---
kind: ConfigMap
apiVersion: v1
metadata:
name: tcp-services
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: udp-services
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRole
metadata:
name: nginx-ingress-clusterrole
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses/status
verbs:
- update
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: Role
metadata:
name: nginx-ingress-role
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
resourceNames:
# Defaults to "<election-id>-<ingress-class>"
# Here: "<ingress-controller-leader>-<nginx>"
# This has to be adapted if you change either parameter
# when launching the nginx-ingress-controller.
- "ingress-controller-leader-nginx"
verbs:
- get
- update
- apiGroups:
- ""
resources:
- configmaps
verbs:
- create
- apiGroups:
- ""
resources:
- endpoints
verbs:
- get
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: RoleBinding
metadata:
name: nginx-ingress-role-nisa-binding
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: nginx-ingress-role
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: nginx-ingress-clusterrole-nisa-binding
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: nginx-ingress-clusterrole
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-ingress-controller
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
spec:
replicas: 1
selector:
matchLabels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
template:
metadata:
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
annotations:
prometheus.io/port: "10254"
prometheus.io/scrape: "true"
spec:
hostNetwork: true ###修改成hostNetwork模式直接共享服务器的网络名称空间
# wait up to five minutes for the drain of connections
terminationGracePeriodSeconds: 300
serviceAccountName: nginx-ingress-serviceaccount
nodeSelector:
kubernetes.io/os: linux
kubernetes.io/hostname: k8s-master02
dnsPolicy: ClusterFirstWithHostNet
containers:
- name: nginx-ingress-controller
imagePullPolicy: IfNotPresent
image: quay.io/kubernetes-ingress-controller/nginx-ingress-controller:0.30.0
args:
- /nginx-ingress-controller
- --configmap=$(POD_NAMESPACE)/nginx-configuration
- --tcp-services-configmap=$(POD_NAMESPACE)/tcp-services
- --udp-services-configmap=$(POD_NAMESPACE)/udp-services
- --publish-service=$(POD_NAMESPACE)/ingress-nginx
- --annotations-prefix=nginx.ingress.kubernetes.io
securityContext:
allowPrivilegeEscalation: true
capabilities:
drop:
- ALL
add:
- NET_BIND_SERVICE
# www-data -> 101
runAsUser: 101
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
ports:
- name: http
containerPort: 80
protocol: TCP
#hostPort: 80
- name: https
containerPort: 443
protocol: TCP
#hostPort: 443
livenessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 10
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 10
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
---
apiVersion: v1
kind: LimitRange
metadata:
name: ingress-nginx
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
spec:
limits:
- min:
memory: 90Mi
cpu: 100m
type: Container
需修改:
hostNetwork: true ###修改成hostNetwork模式直接共享服务器的网络名称空间
执行create创建Ingress-Controller
[root@k8s-master01 ingressdeploy]# kubectl get deploy -n ingress-nginx
NAME READY UP-TO-DATE AVAILABLE AGE
nginx-ingress-controller 1/1 1 1 76m
Ingress-Controller已部署完成
2. 使用Ingress规则
创建测试的web应用
[root@k8s-master01 daem]# cat deploy.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
namespace: default
name: nginxapp
labels:
app: nginx-deploy
spec:
replicas: 2
selector:
matchLabels:
app: mynginx
template:
metadata:
labels:
app: mynginx
spec:
containers:
- name: nginxweb
image: nginx:1.15-alpine
[root@k8s-master01 daem]# cat svc.yaml
apiVersion: v1
kind: Service
metadata:
name: nginx-svc
labels:
app: nginx-svc
spec:
ports:
- name: http
port: 80
protocol: TCP
nodePort: 30001 #node节点的映射端口 可以通过外部访问
targetPort: 80
selector:
app: mynginx
sessionAffinity: None
type: NodePort
创建Ingress规则
[root@k8s-master01 daem]# cat ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-daem
annotations:
kubernetes.io/ingress.class: "nginx"
#nginx.ingress.kubernetes.io/limit-connections: 10
#nginx.ingress.kubernetes.io/limit-rate: 100K
#nginx.ingress.kubernetes.io/limit-rps: 1
#nginx.ingress.kubernetes.io/limit-rpm: 30
spec:
rules:
- host: test.nginxsvc.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /
浏览器访问
添加hosts解析
192.168.29.102 test.nginxsvc.com test-tls.test.com
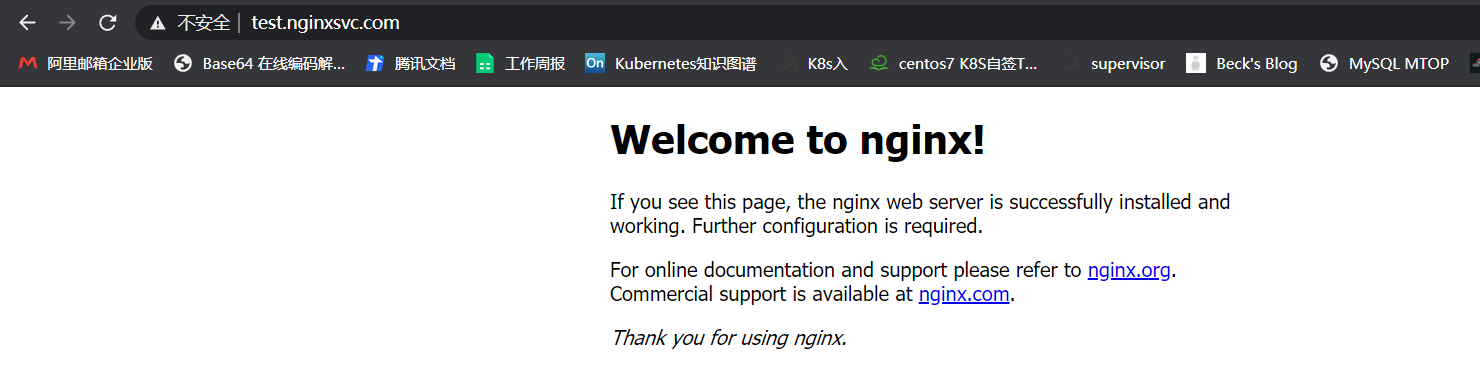
[root@k8s-master01 daem]# curl -I http://test.nginxsvc.com/
HTTP/1.1 200 OK
Server: nginx/1.17.8
Date: Thu, 03 Dec 2020 06:56:49 GMT
Content-Type: text/html
Content-Length: 612
Connection: keep-alive
Vary: Accept-Encoding
Last-Modified: Sat, 11 May 2019 00:35:53 GMT
ETag: "5cd618e9-264"
Accept-Ranges: bytes
2.1 Ingress地址重写
流量重定向到目标URL
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-daem
annotations:
#kubernetes.io/ingress.class: "nginx"
nginx.ingress.kubernetes.io/permanent-redirect: https://www.baidu.com #当访问 test.nginxsvc.com会被重写到百度上
spec:
rules:
- host: test.nginxsvc.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /
前后端分离
[root@k8s-master01 daem]# cat ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-daem
annotations:
#kubernetes.io/ingress.class: "nginx"
#nginx.ingress.kubernetes.io/permanent-redirect: https://www.baidu.com
nginx.ingress.kubernetes.io/rewrite-target: / #当访问test.nginxsvc.com/foo 会把请求打到 nginx-svc此service上
spec:
rules:
- host: test.nginxsvc.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /foo
[root@k8s-master01 daem]# cat ingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-daem
annotations:
#kubernetes.io/ingress.class: "nginx"
#nginx.ingress.kubernetes.io/permanent-redirect: https://www.baidu.com
nginx.ingress.kubernetes.io/rewrite-target: /$2
spec:
rules:
- host: test.nginxsvc.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /nginxservice(/|$)(.*)
paths:
- backend:
serviceName: tomcat-svc
servicePort: 80
path: /tomcatservice(/|$)(.*) #当访问test.nginxsvc.com:PORT/tomcatservice -> 就会被重定向到tomcat-svc / 资源下
2.2 配置HTTPS
[root@k8s-master01 ~]# openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.cert -subj "/CN=test-tls.test.com/O=test-tls.test.com"
Generating a 2048 bit RSA private key
..............................................+++
.........................................................................................+++
writing new private key to 'tls.key'
-----
[root@k8s-master01 ~]# kubectl create secret tls ca-cert --key tls.key --cert tls.cert
secret/ca-cert created
[root@k8s-master01 ~]# cat tlsingress.yaml
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
annotations:
nginx.ingress.kubernetes.io/ssl-redirect: "false"
name: test-tls
spec:
rules:
- host: test-tls.test.com
http:
paths:
- backend:
serviceName: nginx-svc
servicePort: 80
path: /
tls:
- hosts:
- test-tls.test.com
secretName: ca-cert
2.3 黑白名单配置
黑白名单
[root@k8s-master01 ingressdeploy]# cat mandatory.yaml
apiVersion: v1
kind: Namespace
metadata:
name: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: nginx-configuration
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
data:
#############添加如下信息#################
whitelist-source-range: 192.168.29.102 #白名单,允许某个IP或IP段的访问
block-cidrs: 192.168.29.101 #黑名单拒绝访问
2.4 匹配请求头
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
annotations:
nginx.ingress.kubernetes.io/server-snippet: |
set $agentflag 0;
if ($http_user_agent ~* "(Mobile)" ){
set $agentflag 1;
}
if ( $agentflag = 1 ) {
return 301 https://m.example.com;
}
解释:
如果你的http_user_agent == Mobile。那么就把agentflag set成1 ,然后当agentflag == 1时,就会return 到这个域名 https://m.example.com
2.5 速率限制
apiVersion: networking.k8s.io/v1beta1
kind: Ingress
metadata:
name: ingress-nginx
annotations:
kubernetes.io/ingress.class: "nginx"
nginx.ingress.kubernetes.io/limit-rate: 100K
nginx.ingress.kubernetes.io/limit-rps: 1
nginx.ingress.kubernetes.io/limit-rpm: 30
spec:
......
nginx.ingress.kubernetes.io/limit-connections
单个IP地址允许的并发连接数。超过此限制时返回503错误
nginx.ingress.kubernetes.io/limit-rps:
每秒从给定IP接受的请求数。突发限制设置为该限制乘以突发乘数,默认乘数为5。当客户机超过此限制时,将返回limit req status code default:503
nginx.ingress.kubernetes.io/limit-rpm:
每分钟从给定IP接受的请求数。突发限制设置为该限制乘以突发乘数,默认乘数为5。当客户机超过此限制时,将返回limit req status code default:503
nginx.ingress.kubernetes.io/limit-burst-multiplier:
突发大小限制速率的乘数。默认的突发乘数为5,此批注覆盖默认乘数。当客户机超过此限制时,将返回limit req status code default:503。
nginx.ingress.kubernetes.io/limit-rate-after
初始千字节数,此后对给定连接的响应的进一步传输将受到速率限制。此功能必须在启用代理缓冲的情况下使用
nginx.ingress.kubernetes.io/limit-rate
每秒允许发送到给定连接的KB数。零值禁用速率限制。此功能必须在启用代理缓冲的情况下使用
nginx.ingress.kubernetes.io/limit-whitelist
要从速率限制中排除的客户端IP源范围。该值是一个逗号分隔的cidr列表
以上就是Ingress常用的相关配置,所有配置均来自官方文档:https://kubernetes.github.io/ingress-nginx/user-guide/nginx-configuration/annotations/
Kubernetes Ingress-nginx使用的更多相关文章
- Kubernetes Ingress Controller的使用及高可用落地
Kubernetes Ingress Controller的使用及高可用落地 看懂本文要具备一下知识点: Service实现原理和会应用 知道反向代理原理,了解nginx和apache的vhost概念 ...
- Kubernetes Ingress 学习
Kubernetes 中暴露服务的方式有三种 Loadbalancer 这种方式往往需要云供应商支持,或者本地F5等设备支持 NodePort 这种方式调用方通过NodeIP:NodePort 的方式 ...
- Kubernetes Ingress管理
目录 Ingress介绍 1.Pod漂移问题 2.端口管理问题 3.域名分配及动态更新问题 Nginx Ingress配置 1.部署默认后端 2.部署Ingress Controller 3.部署In ...
- Kubernetes Ingress 部署
Kubernetes Ingress 部署 Pod与Ingress的关系• 通过service相关联• 通过Ingress Controller实现Pod的负载均衡- 支持TCP/UDP 4层和HTT ...
- 基于k8s集群部署prometheus监控ingress nginx
目录 基于k8s集群部署prometheus监控ingress nginx 1.背景和环境概述 2.修改prometheus配置 3.检查是否生效 4.配置grafana图形 基于k8s集群部署pro ...
- [转帖]kubernetes ingress 在物理机上的nodePort和hostNetwork两种部署方式解析及比较
kubernetes ingress 在物理机上的nodePort和hostNetwork两种部署方式解析及比较 https://www.cnblogs.com/xuxinkun/p/11052646 ...
- Kubernetes Ingress日志分析入门
本文主要介绍如何基于日志服务构建Kubernetes Ingress日志分析平台,并提供一些简单的动手实验方便大家快速了解日志服务相关功能. 部署Ingress日志方案 登录容器服务管理控制台. 将上 ...
- Kubernetes Ingress简单入门
作者:Nick Ramirez 原文链接:https://thenewstack.io/kubernetes-ingress-for-beginners/ 本文转载自Rancher Labs 不知道你 ...
- CORS跨源资源共享概念及配置(Kubernetes Ingress和Spring Cloud Gateway)
我最新最全的文章都在南瓜慢说 www.pkslow.com,欢迎大家来喝茶! 1 跨源资源共享CORS 跨源资源共享 (CORS) (或通俗地译为跨域资源共享)是一种基于HTTP 头的机制,该机制通过 ...
- 几张图解释明白 Kubernetes Ingress
来源:K8s技术圈 作者:阳明 Kubernetes Ingress 只是 Kubernetes 中的一个普通资源对象,需要一个对应的 Ingress 控制器来解析 Ingress 的规则,暴露服务到 ...
随机推荐
- mysql运维-slave_skip_errors
1 简介 mysql在主从复制过程中,由于各种的原因,从服务器可能会遇到执行BINLOG中的SQL出错的情况,在默认情况下,服务器会停止复制进程,不再进行同步,等到用户自行来处理. sla ...
- docker容器与宿主机的数据交互
在生产环境中使用 Docker ,往往需要对数据进行持久化,或者需要在多个容器之间进行数据共享,这必然涉及容器的数据管理操作. 方式一.Docker cp命令 docker cp :用于容器与主机之间 ...
- 从直播商城系统的KOL效应分析,直播带货井喷的必然性
网红营销.直播带货作为近年来的热点发展迅猛,同时也捧红了一个概念:KOL.随着直播商城系统的不断完善发展,让KOL成为近年来营销最热门的香饽饽.随着原创直播平台低门槛化.模板化内容创作和大数据智能分发 ...
- 【SpringBoot】11-1.Springboot整合Springmvc+Mybatis增删改查操作(下)
整合过程:https://www.isdxh.com/68.html 一.增--增加用户 1.创建实体类 package com.dxh.pojo; public class Users { priv ...
- JavaScript的原型对象prototype、原型属性__proto__、原型链和constructor
先画上一个关系图: 1. 什么是prototype.__proto__.constructor? var arr = new Array; 1. __proto__是原型属性,对象特有的属性,是对象指 ...
- 咀嚼Lock和Synchronized锁
1.Synchronized锁 底层是monitor监视器,每一个对象再创建的时候都会常见一个monitor监视器,在使用synchronized代码块的时候,会在代码块的前后产生一个monitorE ...
- 数字取证autopsy——性能优化(二)
介绍: 在开始使用autopsy之前,我们先对autopsy进行性能优化.如果还没有安装autopsy,请点击连接https://github.com/sleuthkit/autopsy/releas ...
- Andrew Ng 机器学习公开课 - 线性回归
我的机器学习系列从现在开始将会结合Andrew Ng老师与sklearn的api是实际应用相结合来写了. 吴恩达(1976-,英文名:Andrew Ng),华裔美国人,是斯坦福大学计算机科学系和电子工 ...
- Python input用户交互
1.input(),阻塞等待用户输入内容并敲回车. 1 #-*- encoding:utf-8 -*- 2 3 name = input('请输入你的名字') 4 5 age = input('请输入 ...
- vue-子组件为接受到父组件的数据
问题描述: 父组件请求数据,正在处理,未处理完,子组件已经加载,传递的为对象,子组件打印接受的数据为空 解决方式:(数据处理完之后,再强行给子组件赋值) 1.在子组件中添加 :ref="ch ...
