cookie跨站脚本漏洞解决方案
近日项目碰到一个跨脚本注入的问题:
这安全测评工具也是厉害了,直接将脚本注入到cookie里头,以前没有碰到这样的情况。
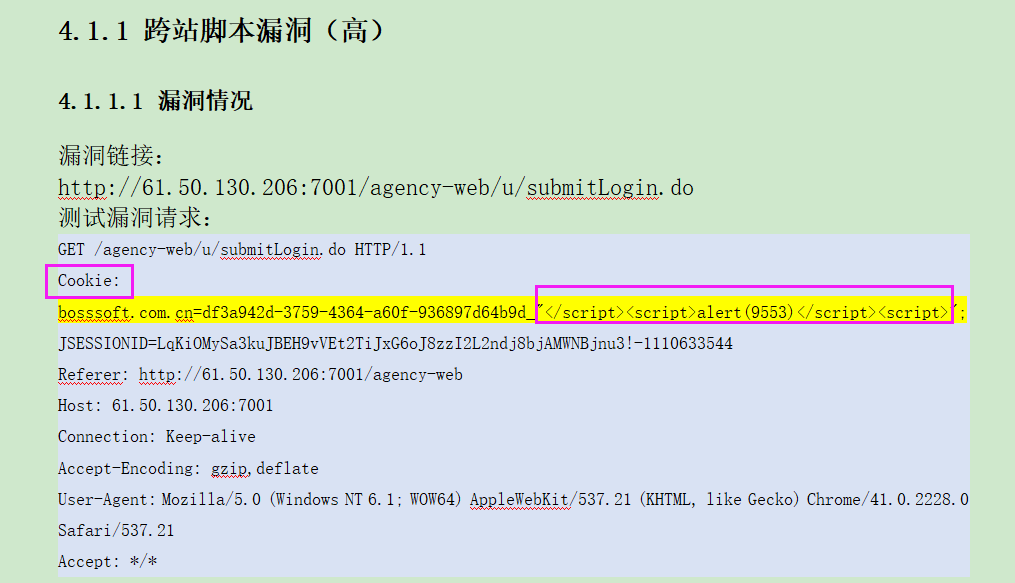
之前写过一篇文章过滤跨脚本注入的问题。《浅谈XSS攻击原理与解决方法》关于跨脚本注入的问题,不晓得原理的同学可以看下。但是里头没有处理cookie注入的问题。接下来介绍下如何处理。
关键代码在这里:首先获取到cookie,检查下是否有敏感字符,如果有的话,就进行替换。
//防止cookie跨站注入问题,替换敏感字符。
Cookie[] cookies = ((HttpServletRequest) request).getCookies();
if(cookies!=null) {
for(Cookie cookie: cookies){
if(CookieFilterUtil.isValidate(cookie.getValue())){
cookie.setValue(CookieFilterUtil.xssClean(cookie.getValue()));
Cookie newCookie=cookie;
cookie.setMaxAge();
((HttpServletResponse) response).addCookie(newCookie);
break;
}
}
}
CookieFilter.java
public class CookieFilterUtil {
//将敏感字符进行替换
public static String xssClean(String value) {
//ClassLoaderUtils.getResourceAsStream("classpath:antisamy-slashdot.xml", XssHttpServletRequestWrapper.class)
if (value != null) {
// NOTE: It's highly recommended to use the ESAPI library and
// uncomment the following line to
// avoid encoded attacks.
// value = encoder.canonicalize(value);
value = value.replaceAll("\0", "");
// Avoid anything between script tags
Pattern scriptPattern = Pattern.compile("<script>(.*?)</script>",
Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid anything in a src='...' type of expression
scriptPattern = Pattern.compile("src[\r\n]*=[\r\n]*\\\'(.*?)\\\'",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid anything in a href='...' type of expression
scriptPattern = Pattern.compile("href[\r\n]*=[\r\n]*\\\"(.*?)\\\"",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Remove any lonesome </script> tag
scriptPattern = Pattern.compile("</script>",
Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Remove any lonesome <script ...> tag
scriptPattern = Pattern.compile("<script(.*?)>",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid eval(...) expressions
scriptPattern = Pattern.compile("eval\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid expression(...) expressions
scriptPattern = Pattern.compile("expression\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid javascript:... expressions
scriptPattern = Pattern.compile("javascript:",
Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid vbscript:... expressions
scriptPattern = Pattern.compile("vbscript:",
Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid onload= expressions
scriptPattern = Pattern.compile("onload(.*?)=",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
}
return value;
}
//校验是否含有敏感字符
public static boolean isValidate(String value) {
//ClassLoaderUtils.getResourceAsStream("classpath:antisamy-slashdot.xml", XssHttpServletRequestWrapper.class)
boolean flag=false;
if (value != null) {
// NOTE: It's highly recommended to use the ESAPI library and
// uncomment the following line to
// avoid encoded attacks.
// value = encoder.canonicalize(value);
value = value.replaceAll("\0", "");
// Avoid anything between script tags
Pattern scriptPattern = Pattern.compile("<script>(.*?)</script>",
Pattern.CASE_INSENSITIVE);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Avoid anything in a src='...' type of expression
scriptPattern = Pattern.compile("src[\r\n]*=[\r\n]*\\\'(.*?)\\\'",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Avoid anything in a href='...' type of expression
scriptPattern = Pattern.compile("href[\r\n]*=[\r\n]*\\\"(.*?)\\\"",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Remove any lonesome </script> tag
scriptPattern = Pattern.compile("</script>",
Pattern.CASE_INSENSITIVE);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Remove any lonesome <script ...> tag
scriptPattern = Pattern.compile("<script(.*?)>",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Avoid eval(...) expressions
scriptPattern = Pattern.compile("eval\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Avoid expression(...) expressions
scriptPattern = Pattern.compile("expression\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Avoid javascript:... expressions
scriptPattern = Pattern.compile("javascript:",
Pattern.CASE_INSENSITIVE);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Avoid vbscript:... expressions
scriptPattern = Pattern.compile("vbscript:",
Pattern.CASE_INSENSITIVE);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
// Avoid onload= expressions
scriptPattern = Pattern.compile("onload(.*?)=",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
if(scriptPattern.matcher(value).find()){
flag=true;
return flag;
}
}
return flag;
}
}
XssFilter.java
public class XssFilter implements Filter {
@Override
public void init(FilterConfig filterConfig) throws ServletException {
}
@Override
public void doFilter(ServletRequest request, ServletResponse response,
FilterChain chain) throws IOException, ServletException {
//防止cookie跨站注入问题,替换敏感字符。
boolean flag=false;
Cookie[] cookies = ((HttpServletRequest) request).getCookies();
if(cookies!=null) {
for(Cookie cookie: cookies){
if(CookieFilterUtil.isValidate(cookie.getValue())){
flag=true;
cookie.setValue(CookieFilterUtil.xssClean(cookie.getValue()));
Cookie newCookie=cookie;
cookie.setMaxAge();
((HttpServletResponse) response).addCookie(newCookie);
break;
}
}
}
//如果存在跨站注入问题,跳转到登录页。
if(!flag){
String path = ((HttpServletRequest) request).getContextPath();
String protAndPath = request.getServerPort() == ? "" : ":"
+ request.getServerPort();
String basePath = request.getScheme() + "://"
+ request.getServerName() + protAndPath + path + "/";
String returnUrl = basePath+"login.do";
request.setCharacterEncoding("UTF-8");
response.setContentType("text/html; charset=UTF-8"); // 转码
response.getWriter().println(
"<script language=\"javascript\">if(window.opener==null){window.top.location.href=\""
+ returnUrl
+ "\";}else{window.opener.top.location.href=\""
+ returnUrl
+ "\";window.close();}</script>");
}else{
chain.doFilter(new XssHttpServletRequestWrapper((HttpServletRequest) request), response);
}
}
@Override
public void destroy() {
}
}
这儿的操作如果有敏感字符,那么就调整到登录首页,删除cookie,当然也可以不处理,像以下代码这样
//防止cookie跨站注入问题,替换敏感字符。
Cookie[] cookies = ((HttpServletRequest) request).getCookies();
if(cookies!=null) {
for(Cookie cookie: cookies){
if(CookieFilterUtil.isValidate(cookie.getValue())){
cookie.setValue(CookieFilterUtil.xssClean(cookie.getValue()));
Cookie newCookie=cookie;
cookie.setMaxAge();
((HttpServletResponse) response).addCookie(newCookie);
break;
}
}
}
chain.doFilter(new XssHttpServletRequestWrapper((HttpServletRequest) request), response);
xss过滤器实现XssHttpServletRequestWrapper.java
public class XssHttpServletRequestWrapper extends HttpServletRequestWrapper {
public XssHttpServletRequestWrapper(HttpServletRequest request) {
super(request);
}
@SuppressWarnings("rawtypes")
public Map<String,String[]> getParameterMap(){
Map<String,String[]> request_map = super.getParameterMap();
Iterator iterator = request_map.entrySet().iterator();
while(iterator.hasNext()){
Map.Entry me = (Map.Entry)iterator.next();
String[] values = (String[])me.getValue();
for(int i = ; i < values.length ; i++){
values[i]=HtmlRegexpUtil.fiterHtmlByTagArr(values[i]);
values[i] = xssClean(values[i]);
}
}
return request_map;
}
public String[] getParameterValues(String paramString)
{
String[] arrayOfString1 = super.getParameterValues(paramString);
if (arrayOfString1 == null)
return null;
int i = arrayOfString1.length;
String[] arrayOfString2 = new String[i];
for (int j = ; j < i; j++){
arrayOfString1[j]=HtmlRegexpUtil.fiterHtmlByTagArr(arrayOfString1[j]);
arrayOfString2[j] = xssClean(arrayOfString1[j]);
}
return arrayOfString2;
}
public String getParameter(String paramString)
{
String str = super.getParameter(paramString);
if (str == null)
return null;
return xssClean(str);
}
public String getHeader(String paramString)
{
String str = super.getHeader(paramString);
if (str == null)
return null;
str = str.replaceAll("\r|\n", "");
return xssClean(str);
}
private String xssClean(String value) {
//ClassLoaderUtils.getResourceAsStream("classpath:antisamy-slashdot.xml", XssHttpServletRequestWrapper.class)
if (value != null) {
// NOTE: It's highly recommended to use the ESAPI library and
// uncomment the following line to
// avoid encoded attacks.
// value = encoder.canonicalize(value);
value = value.replaceAll("\0", "");
// Avoid anything between script tags
Pattern scriptPattern = Pattern.compile("<script>(.*?)</script>",
Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid anything in a src='...' type of expression
scriptPattern = Pattern.compile("src[\r\n]*=[\r\n]*\\\'(.*?)\\\'",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid anything in a href='...' type of expression
scriptPattern = Pattern.compile("href[\r\n]*=[\r\n]*\\\"(.*?)\\\"",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Remove any lonesome </script> tag
scriptPattern = Pattern.compile("</script>",
Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Remove any lonesome <script ...> tag
scriptPattern = Pattern.compile("<script(.*?)>",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid eval(...) expressions
scriptPattern = Pattern.compile("eval\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid expression(...) expressions
scriptPattern = Pattern.compile("expression\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid javascript:... expressions
scriptPattern = Pattern.compile("javascript:",
Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid vbscript:... expressions
scriptPattern = Pattern.compile("vbscript:",
Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid onload= expressions
scriptPattern = Pattern.compile("onload(.*?)=",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE
| Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
}
return value;
}
}
cookie跨站脚本漏洞解决方案的更多相关文章
- WordPress FunCaptcha插件跨站脚本漏洞
漏洞名称: WordPress FunCaptcha插件跨站脚本漏洞 CNNVD编号: CNNVD-201311-431 发布时间: 2013-11-29 更新时间: 2013-11-29 危害等级: ...
- WordPress Checkout插件跨站脚本漏洞和任意文件上传漏洞
漏洞名称: WordPress Checkout插件跨站脚本漏洞和任意文件上传漏洞 CNNVD编号: CNNVD-201311-015 发布时间: 2013-11-04 更新时间: 2013-11-0 ...
- WordPress Tweet Blender插件跨站脚本漏洞
漏洞名称: WordPress Tweet Blender插件跨站脚本漏洞 CNNVD编号: CNNVD-201310-645 发布时间: 2013-10-30 更新时间: 2013-10-30 危害 ...
- WordPress WooCommerce ‘hide-wc-extensions-message’参数跨站脚本漏洞
漏洞名称: WordPress WooCommerce ‘hide-wc-extensions-message’参数跨站脚本漏洞 CNNVD编号: CNNVD-201310-501 发布时间: 201 ...
- WordPress Videowall插件‘page_id’参数跨站脚本漏洞
漏洞名称: WordPress Videowall插件‘page_id’参数跨站脚本漏洞 CNNVD编号: CNNVD-201310-502 发布时间: 2013-10-23 更新时间: 2013-1 ...
- WordPress MORE+主题‘prettyPhoto’跨站脚本漏洞
漏洞名称: WordPress MORE+主题‘prettyPhoto’跨站脚本漏洞 CNNVD编号: CNNVD-201310-284 发布时间: 2013-10-23 更新时间: 2013-10- ...
- WordPress Bradesco Gateway插件‘falha.php’跨站脚本漏洞
漏洞名称: WordPress Bradesco Gateway插件‘falha.php’跨站脚本漏洞 CNNVD编号: CNNVD-201309-451 发布时间: 2013-09-26 更新时间: ...
- WordPress Sharebar ‘page’参数跨站脚本漏洞
漏洞名称: WordPress Sharebar ‘page’参数跨站脚本漏洞 CNNVD编号: CNNVD-201309-468 发布时间: 2013-09-26 更新时间: 2013-09-26 ...
- WordPress mb.miniAudioPlayer插件多个跨站脚本漏洞
漏洞名称: WordPress mb.miniAudioPlayer插件多个跨站脚本漏洞 CNNVD编号: CNNVD-201309-469 发布时间: 2013-09-26 更新时间: 2013-0 ...
随机推荐
- Book Review of “The practice of programming” (Ⅲ)
The practice of programming Chapter 3 Design and Implementation In this section, we focus on one kin ...
- 部署私有云网盘owncloud
环境说明: [root@localhost ~]# cat /etc/redhat-release CentOS release 6.9 (Final) [root@localhost ~]# una ...
- 织梦DedeCMS实现 三级栏目_二级栏目_一级栏目_网站名称 的效果代码
1.将官方原来的排列方式反过来,找到include/typelink.class.php第164行 $this->valuePositionName = $tinfos['typename']. ...
- 编写一个程序,将 d:\java 目录下的所有.java 文件复制到 d:\jad 目录下,并将原来文件的扩展名从.java 改为.jad。
package IO; import java.io.*; public class FileCopy { public static void main(String[] args) throws ...
- iOS CoreData版本升级和数据库迁移
app中使用了CoreData,并且在下一个版本中有实体变动,比如实体新增字段.修改字段等改动, 那么app在覆盖安装时就要进行数据库迁移, 否则app就会crash. 那如何实现数据库迁移呢?大概需 ...
- WPF的外观装饰类——Border
public class Border : System.Windows.Controls.Decorator 说明:在另一个元素的周围绘制边框.背景或同时绘制二者.
- InnoDB存储引擎的B+树索引算法
关于B+树数据结构 ①InnoDB存储引擎支持两种常见的索引. 一种是B+树,一种是哈希. B+树中的B代表的意思不是二叉(binary),而是平衡(balance),因为B+树最早是从平衡二叉树演化 ...
- is(':visible')
.end()为结束前面处理函数,返回到最初的元素 .next()为此元素的下一个元素,可以再加上.next()表示下下一个元素,以此类推 :visible 选择器选取每个当前是可见的元素.语法:$(& ...
- react: typescript-webpack项目基本配置
1.webpack.config.js basic const webpack = require('webpack'); const autoprefixer = require('autopref ...
- charles抓包并分析问题
1.抓包并分析 某列表页 传入的参数: -------------------------------------------------------------------------------- ...
