Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment:
Download and Install Pan-OS from the following website https://docs.gns3.com/appliances/pan-vm-fw.html or https://me.csdn.net/download/hotbrandon

URL https://IP
Default Username/Password: admin/admin
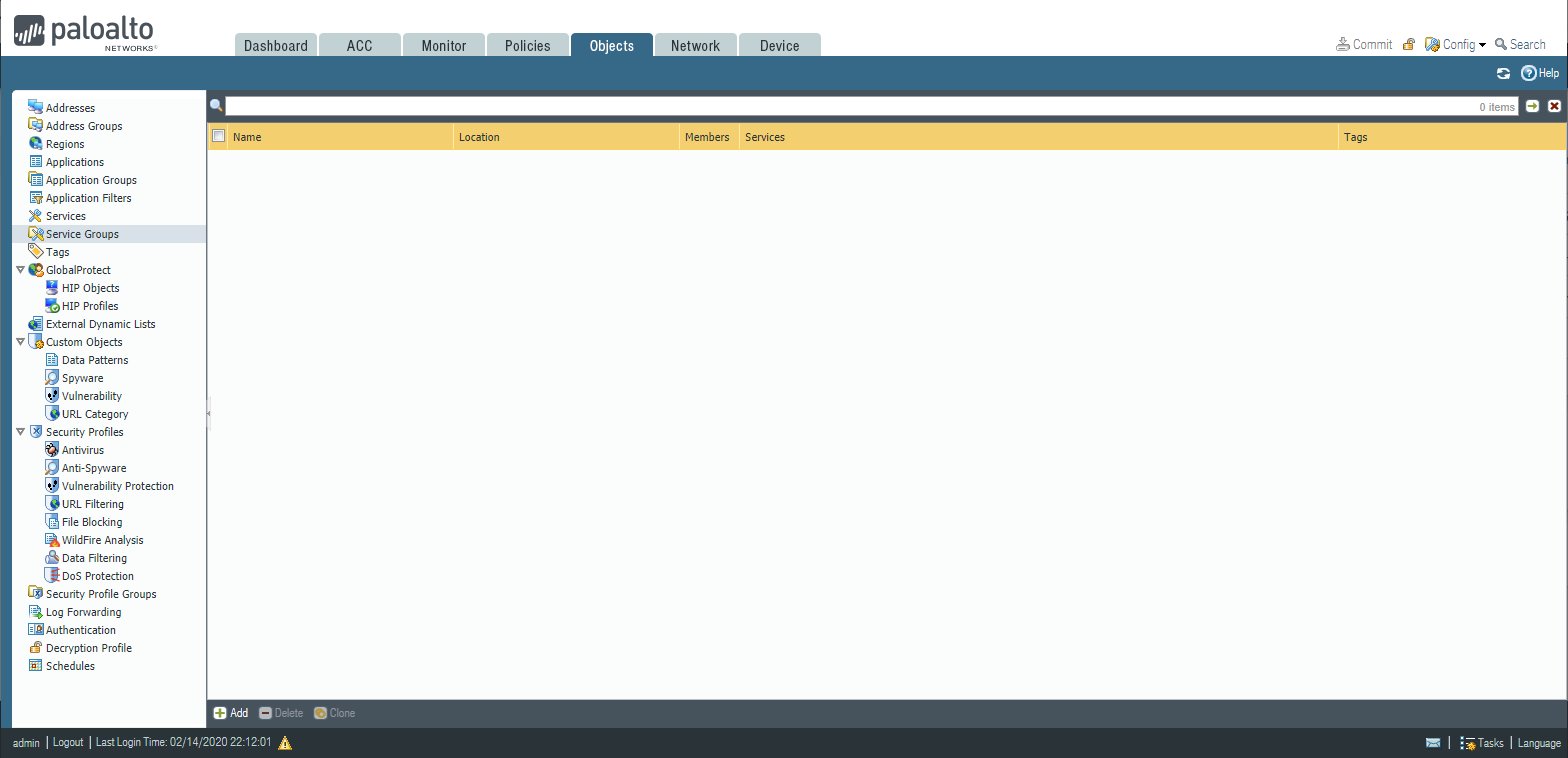
PAN-OS 8 Configuration Tabs:
- Object tab: Configure Firewall objects(address - services - object groups)
- Policy tab: Configure Firewall policies(security -NAT -QoS - PBR)
- Network tab: Configure Firewall interfaces and routing settings
- Device tab: Perform maintenance tasks and administrative tasks.
- Configuration backup and restore.
- High availability.
- Users and administrators.
- Directory synchronization(Active Directory)
PAN-OS 8 Monitoring Tabs:
- ACC Tab: Application command center overview
- Monitor tab: User traffic monitoring based on applied policies
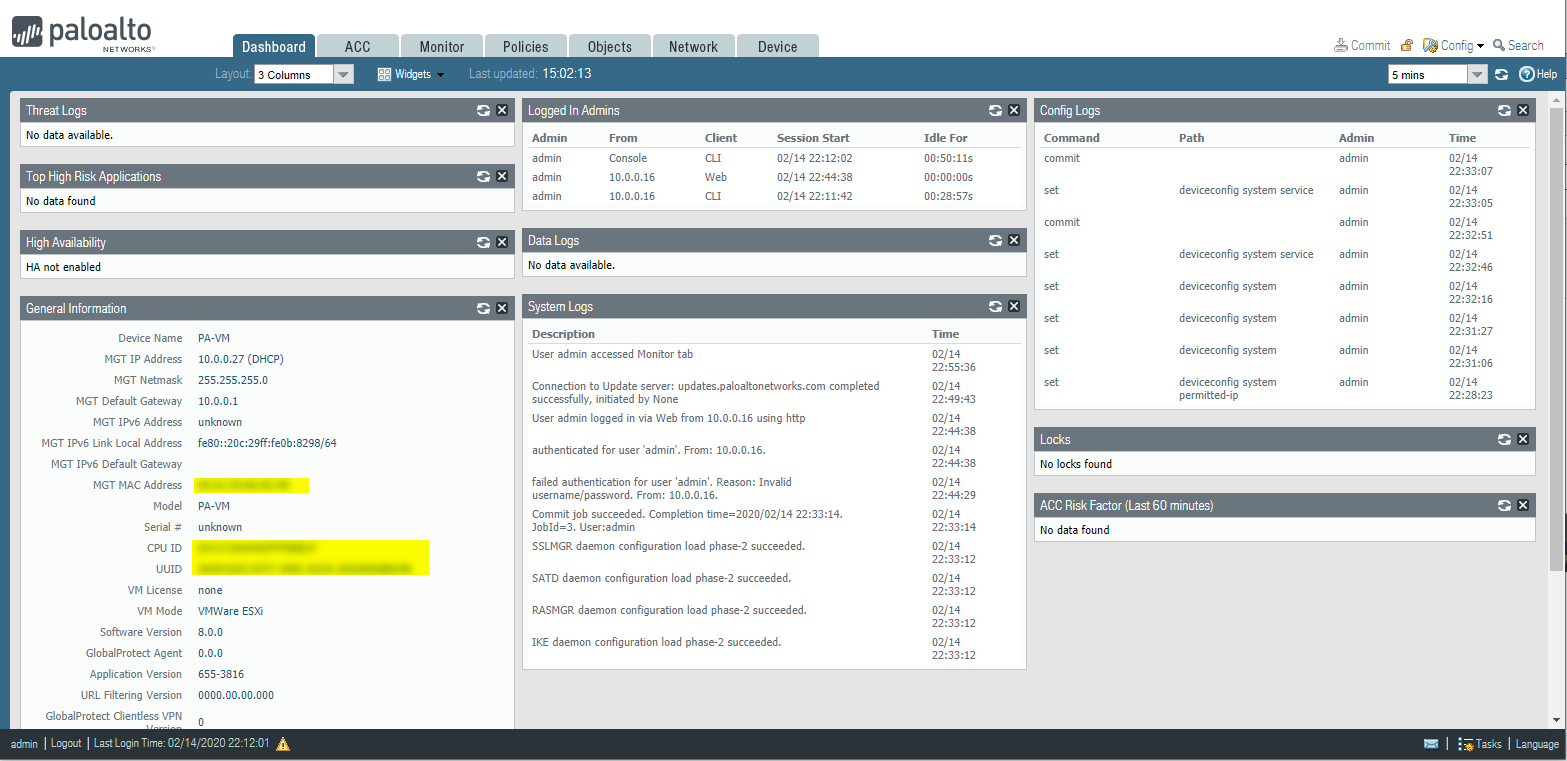
Dashboard:
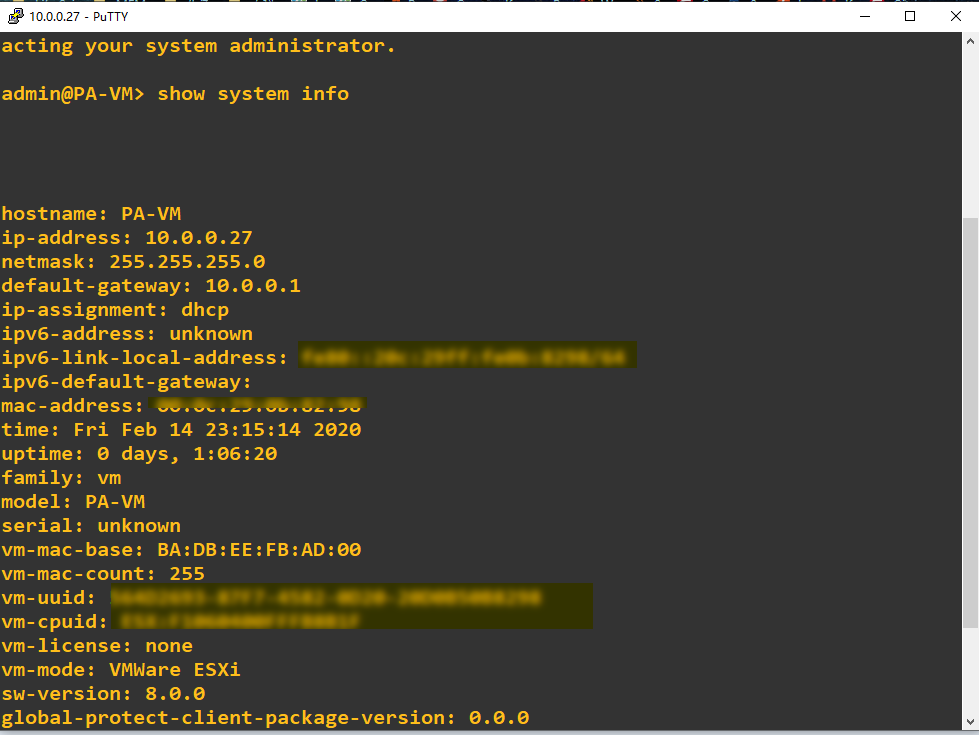
Console - Based Administration
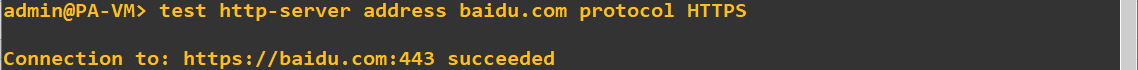
Action commands - show, request, test, configure
CLI structure:{action}{section}{element}
show:
show system info
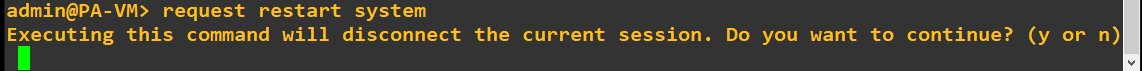
request:
request system restart
Test:
test vpn ike-sa gateway {name}
test vpn ipsec-sa gateway {name}
Device Management Overview
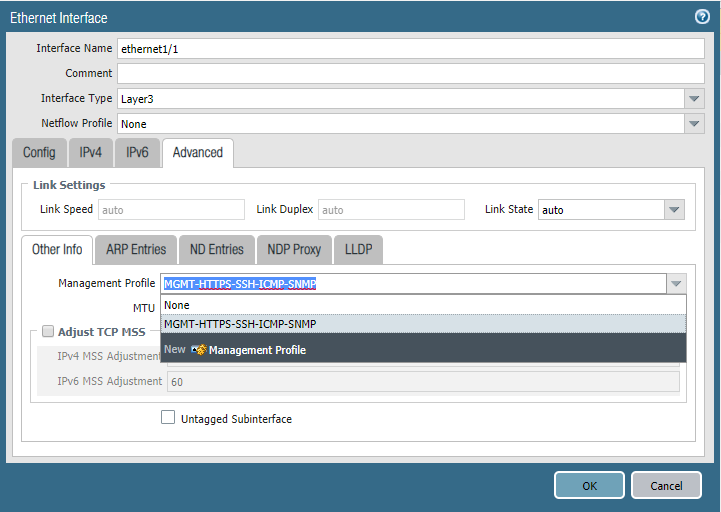
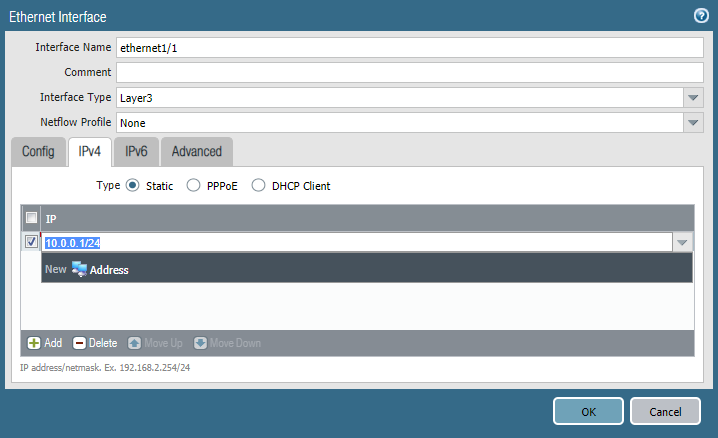
Interface Management Profile
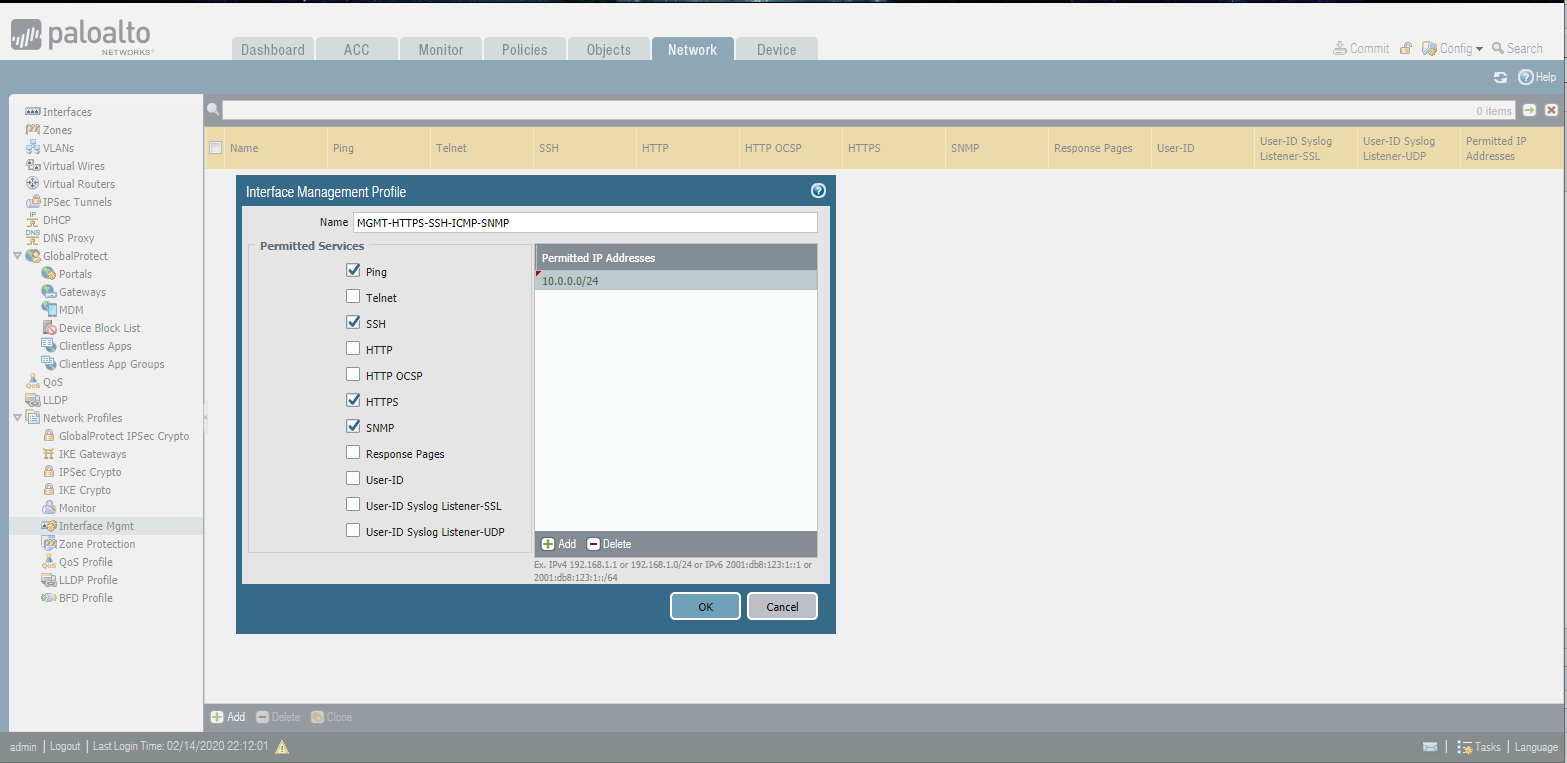
Ethernet Interface
Local admin
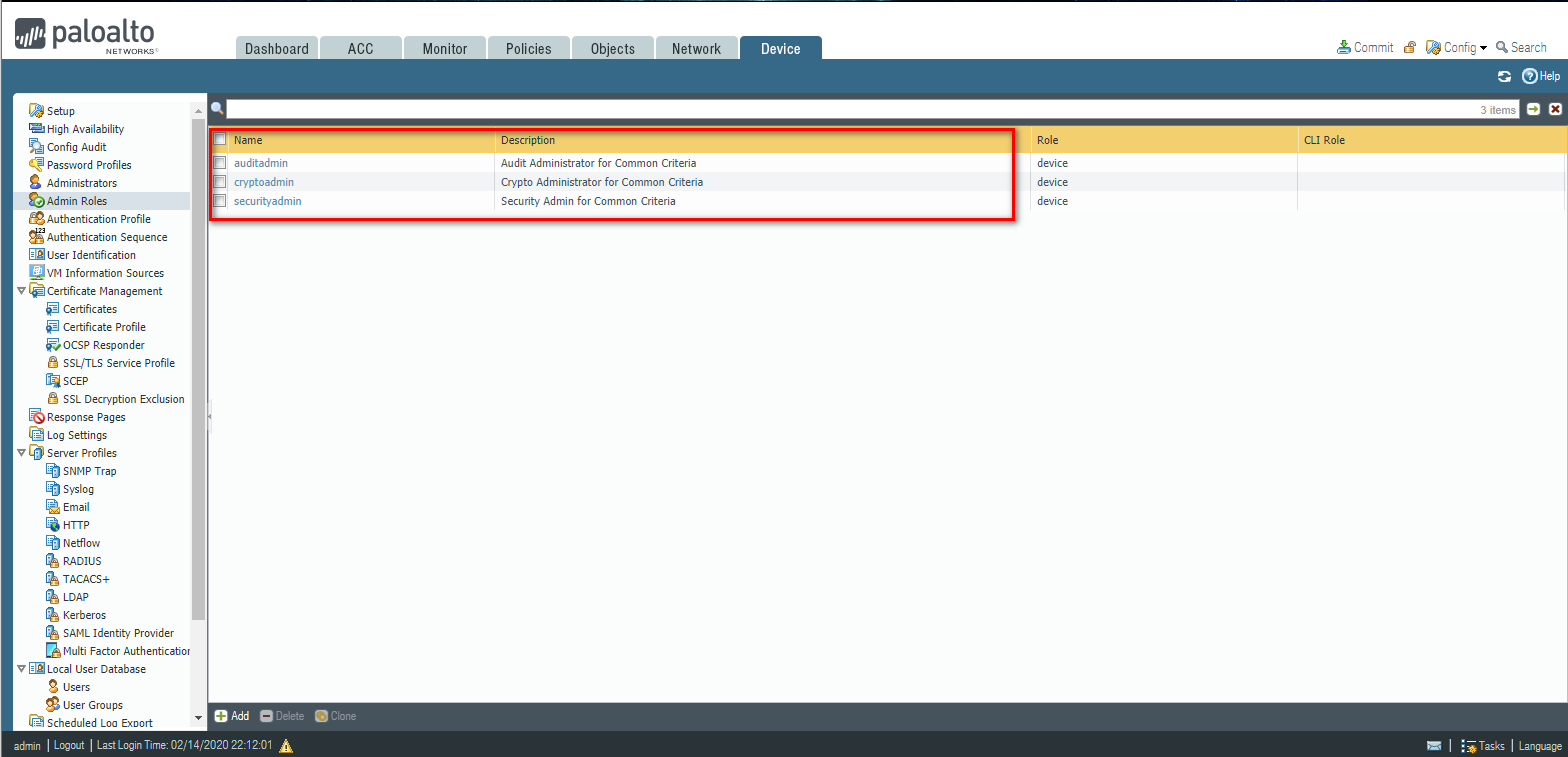
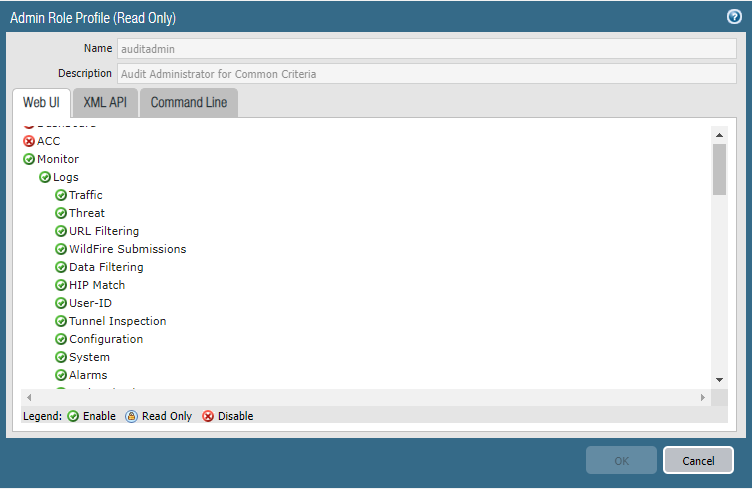
Create a new Role Profile(All function except Policies, Objects, Device, and Privacy.)
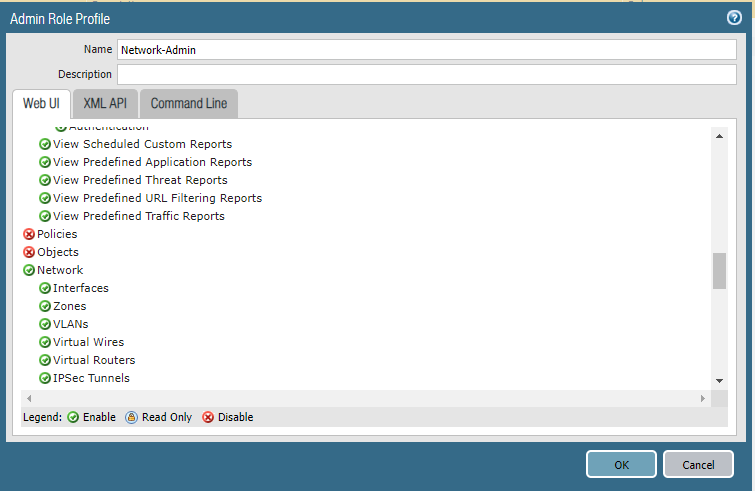
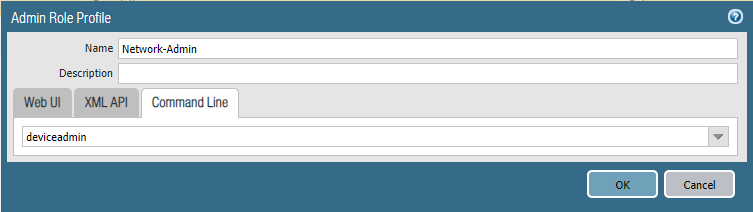
Add a new network administrator.

Cyber Security - Palo Alto Basic Introduction的更多相关文章
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups Create Remote User Objects and LDAP Integration: sam ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups Creating address objects. Organizing address objects with address groups ...
- Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your: Network Layer 2 interfaces and VLAN ...
- Cyber Security - Palo Alto Security Policies(2)
Task 3 The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to ...
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires Bridge two physical connections and apply security Policies without influencing a ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- 【服务器】VMware Workstation Pro虚拟机搭建本地服务器CentOs7和宝塔面板(保姆式教程)
内容繁多,请耐心跟着流程走,在过程中遇到问题请在下面留言. 前言 这几天一直在复习thinkphp5.1,学习环境是phpStudy8.1,但是遇到了文件有缓存的问题(thinkphp5.1.39,修 ...
- java并发编程-线程生命周期
线程生命周期 现代操作系统在运行一个程序时,会为其创建一个进程.例如,启动一个Java程序,操作系统就会创建一个Java进程.现代操作系统调度的最小单元是线程,也叫轻量级进程(Light Weight ...
- 从Spring Initializr开始
出识springcloud我们这里需要建立两个项目 来感受下微服务 一.配置服务 1. Spring Initializr. 用idea自带的 Spring Initializr. 建立第一个项目 2 ...
- [ APUE ] 第三章 文件系统
1. 文件描述符 打开或创建一个文件时,内核向进程返回一个文件描述符,当读.写一个文件时,用open()或creat()返回的文件描述符标识该文件,将其作为参数传递给write.read. stdin ...
- 【解读】TCP协议
本文内容如下: 1)TCP协议概念 2)TCP头部结构和字段介绍 3)TCP流量控制 滑动窗口 4)TCP拥塞控制 慢 ...
- JavaWeb网上图书商城完整项目--day02-11.激活功能流程分析
1.当用户注册成功之后,会给用户发送邮件,当用户点击邮件的激活按钮的时候,会调用UserServlet中的activation的方法,并且会把激活码传递到后台,后台业务层对业务进行操作
- ImageLoader在Listview中的使用
图片加载框架之ImageLoader 1_特点 1)多线程下载图片,图片可以来源于网络,文件系统,项目文件夹assets中以及drawable中等 2)支持随意的配置ImageLoader,例如线程池 ...
- JNI调用Cython生成库‘undefined symbol: PyInit_’问题
最近项目需要提升所有 Python 算法的执行时间,并给 Java 框架调用,根据 Python一键转Jar包,Java调用Python新姿势!的思路可以用 Cython 将 Python 代码转换为 ...
- 如何在 asp.net core 3.x 的 startup.cs 文件中获取注入的服务
一.前言 从 18 年开始接触 .NET Core 开始,在私底下.工作中也开始慢慢从传统的 mvc 前后端一把梭,开始转向 web api + vue,之前自己有个半成品的 asp.net core ...
- Java 线程基础,从这篇开始
线程作为操作系统中最少调度单位,在当前系统的运行环境中,一般都拥有多核处理器,为了更好的充分利用 CPU,掌握其正确使用方式,能更高效的使程序运行.同时,在 Java 面试中,也是极其重要的一个模块. ...
