Cells Not Under Attack
Vasya has the square chessboard of size n × n and m rooks. Initially the chessboard is empty. Vasya will consequently put the rooks on the board one after another.
The cell of the field is under rook's attack, if there is at least one rook located in the same row or in the same column with this cell. If there is a rook located in the cell, this cell is also under attack.
You are given the positions of the board where Vasya will put rooks. For each rook you have to determine the number of cells which arenot under attack after Vasya puts it on the board.
The first line of the input contains two integers n and m (1 ≤ n ≤ 100 000, 1 ≤ m ≤ min(100 000, n2)) — the size of the board and the number of rooks.
Each of the next m lines contains integers xi and yi (1 ≤ xi, yi ≤ n) — the number of the row and the number of the column where Vasya will put the i-th rook. Vasya puts rooks on the board in the order they appear in the input. It is guaranteed that any cell will contain no more than one rook.
Print m integer, the i-th of them should be equal to the number of cells that are not under attack after first i rooks are put.
3 3
1 1
3 1
2 2
4 2 0
5 2
1 5
5 1
16 9
100000 1
300 400
9999800001
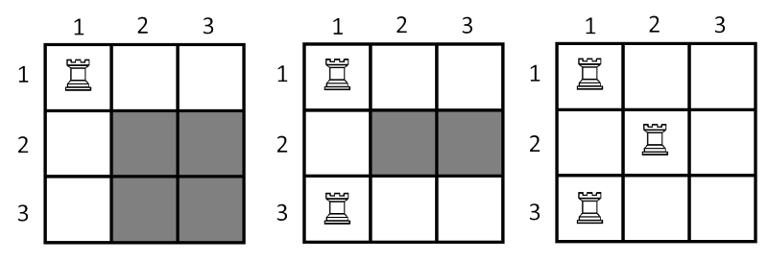
On the picture below show the state of the board after put each of the three rooks. The cells which painted with grey color is not under the attack.
分析:模拟即可;
代码:
#include <iostream>
#include <cstdio>
#include <cstdlib>
#include <cmath>
#include <algorithm>
#include <climits>
#include <cstring>
#include <string>
#include <set>
#include <map>
#include <queue>
#include <stack>
#include <vector>
#include <list>
#include <ext/rope>
#define rep(i,m,n) for(i=m;i<=n;i++)
#define rsp(it,s) for(set<int>::iterator it=s.begin();it!=s.end();it++)
#define vi vector<int>
#define pii pair<int,int>
#define mod 1000000007
#define inf 0x3f3f3f3f
#define pb push_back
#define mp make_pair
#define fi first
#define se second
#define ll long long
#define pi acos(-1.0)
const int maxn=1e5+;
const int dis[][]={{,},{-,},{,-},{,}};
using namespace std;
using namespace __gnu_cxx;
ll gcd(ll p,ll q){return q==?p:gcd(q,p%q);}
ll qpow(ll p,ll q){ll f=;while(q){if(q&)f=f*p;p=p*p;q>>=;}return f;}
int n,m,x,y,cnt1,cnt2;
bool a[maxn],b[maxn];
int main()
{
int i,j,k,t;
scanf("%d%d",&n,&m);
ll now=1ll*n*n;
while(m--)
{
scanf("%d%d",&x,&y);
if(!a[x])
{
now-=n;
now+=cnt2;
}
if(!b[y])
{
now-=n;
now+=cnt1;
}
if(!a[x])cnt1++;
if(!b[y])cnt2++;
if(!a[x]&&!b[y])now++;
a[x]=b[y]=true;
printf("%lld ",now);
}
//system ("pause");
return ;
}
Cells Not Under Attack的更多相关文章
- CF 701B Cells Not Under Attack(想法题)
题目链接: 传送门 Cells Not Under Attack time limit per test:2 second memory limit per test:256 megabyte ...
- Codeforces Round #364 (Div. 2) B. Cells Not Under Attack
B. Cells Not Under Attack time limit per test 2 seconds memory limit per test 256 megabytes input st ...
- Codeforces Round #364 (Div. 2) Cells Not Under Attack
Cells Not Under Attack 题意: 给出n*n的地图,有给你m个坐标,是棋子,一个棋子可以把一行一列都攻击到,在根据下面的图,就可以看出让你求阴影(即没有被攻击)的方块个数 题解: ...
- codeforces #364b Cells Not Under Attack
比赛的时候 long long sum=n*n,计算不出1e10长度到数,没有搞掉. 哎,以后要注意这个地方.这个题其实不难: 统计能被攻击到的个数,然后用总的个数减掉就可以了.注意有些地方重复计算, ...
- codeforces 701B B. Cells Not Under Attack(水题)
题目链接: B. Cells Not Under Attack 题意: n*n的棋盘,现在放m个棋子,放一个棋子这一行和这一列就不会under attack了,每次放棋子回答有多少点还可能under ...
- codeforces 701 B. Cells Not Under Attack
B. Cells Not Under Attack time limit per test 2 seconds memory limit per test 256 megabytes input st ...
- cf701B Cells Not Under Attack
Vasya has the square chessboard of size n × n and m rooks. Initially the chessboard is empty. Vasya ...
- CodeForces 701B Cells Not Under Attack
题目链接:http://codeforces.com/problemset/problem/701/B 题目大意: 输入一个数n,m, 生成n*n的矩阵,用户输入m个点的位置,该点会影响该行和该列,每 ...
- Codeforces #364 DIV2
~A题 A. Cards time limit per test 1 second memory limit per test 256 megabytes input standard input ...
随机推荐
- C# 16位的GUDI
引用: http://www.cnblogs.com/lcwzj/archive/2009/04/16/1436992.html 当我们想要获得一个唯一的key的时候,通常会想到GUID.这个key ...
- leetcode136 利用异或运算找不同的元素
Given an array of integers, every element appears twice except for one. Find that single one. Note: ...
- arTemplate解析语法
模板解析语法 defaults.parser = function (code, options) { // var match = code.match(/([\w\$]*)(\b.*)/); // ...
- 取出parentid为null的顶级栏目 等号改为 is null 避免null当做字符串,
mysql中查询字段为null或者不为null 在mysql中,查询某字段为空时,不可用等号 = null, 而是 is null,不为空则是 is not null select * from ...
- Entity Framework技巧系列之一 - Tip 1 - 5
提示1. 在Entity Framework中怎样排序关系(Relationships) 问题: 在Entity Framework论坛中常会看到关于排序相关联项目的问题. 例如,想象你要查询客户,并 ...
- knockout.js
最近在使用knockout这个JS的MVVM模型,真的很不错,每次去查英文的文档,的确很累的,抽空的时候就把看到的文档按自己的理解翻译一下.当然我不是逐字的翻译. knockout的官方说明:http ...
- Mysql5.7 安装
1 安装yum源 yum localinstall http://repo.mysql.com//mysql57-community-release-el7-7.noarch.rpm2 参看源 vi ...
- 修改某个UITextField的键盘的返回键类型以及监听键盘的高度变化,取到键盘动画退出弹出的时间,一起随着键盘顶出来或者压下去,
1.修改某个UITextField的键盘的返回键类型: [_bottomTextView setReturnKeyType:UIReturnKeyDone]; 1.1.textFied点击return ...
- 关于spring的注解方式注入默认值(转) -- 首字母小写
1.是首字母小写 比如 UserAction对应的id是userAction 可以通过ApplicationContext 对象的act.getBean("userAction") ...
- 关于tab选项卡,选项的css问题。
刚开始的思路是:让上面的选中的选项背景变成白色,让下面的层position:absolute;z-index:-1;top:1px,就能盖得上上面的横线.实践证明,这样是能盖得上,但是单选按钮不能点了 ...
