Kubernetes实战总结 - Prometheus部署
什么是普罗米修斯?
Prometheus是最初在SoundCloud上构建的开源系统监视和警报工具包 。
自2012年成立以来,许多公司和组织都采用了Prometheus,该项目拥有非常活跃的开发人员和用户社区。
组件说明
- Prometheus:负责实现对K8s集群监控数据的获取,存储以及查询。
- PrometheusOperator:为Prometheus实例的部署和管理提供了简单的监视定义。
- KubeStateMetrics:是K8s集群资源使用情况的聚合器,收集数据给K8s集群内使用(如HPA)。
- AlertManager:负责将告警信息重复数据删除,分组和路由到正确的接收者集成。
- NodeExporter:用于采集集群中各个节点的资源使用情况。
- Grafana:一个跨平台的开源的度量分析和可视化工具。
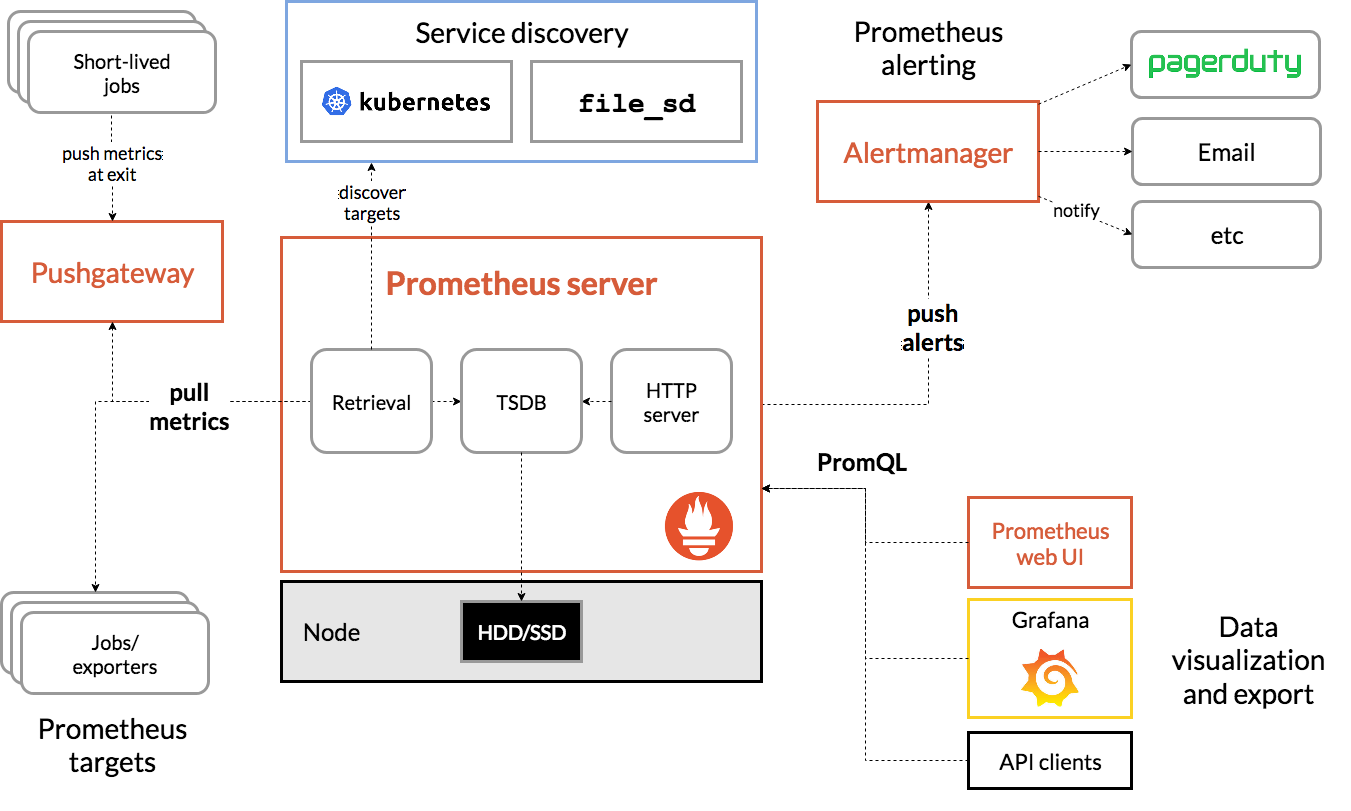
系统架构
什么时候合适?
Prometheus非常适合记录任何纯数字时间序列。
它既适合以机器为中心的监视,也适合于高度动态的面向服务的体系结构的监视。在微服务世界中,它对多维数据收集和查询的支持是一种特别的优势。
Prometheus的设计旨在提高可靠性,使其成为中断期间要使用的系统,以使您能够快速诊断问题。
每个Prometheus服务器都是独立的,而不依赖于网络存储或其他远程服务。当基础结构的其他部分损坏时,您可以依靠它,并且无需设置广泛的基础结构即可使用它。
什么时候不合适?
普罗米修斯重视可靠性。即使在故障情况下,您始终可以查看有关系统的可用统计信息。
如果您需要100%的准确性(例如按请求计费),则Prometheus并不是一个不错的选择,因为所收集的数据可能不会足够详细和完整。
在这种情况下,最好使用其他系统来收集和分析数据以进行计费,并使用Prometheus进行其余的监视。
部署安装
Github : https://github.com/coreos/kube-prometheus
1、下载官方源码文件(默认镜像源来自quay.io)
wget -o kube-prometheus.tgz https://github.com/coreos/kube-prometheus/archive/v0.3.0.tar.gz
- 当然,如果你的国外网不太友好,也可以下载本人百度云文件(已修改镜像源到aliyuncs)kube-prometheus-0.3.0.zip(ccer )
2、解压并部署安装
tar -zxvf kube-prometheus.tgz && cd kube-prometheus-0.3.0/manifests
kubectl create -f setup
until kubectl get servicemonitors --all-namespaces ; do date; sleep 1; echo ""; done
kubectl create -f .
[root@k8s-32 manifests]# ls -R
.:
alertmanager-alertmanager.yaml kube-state-metrics-service.yaml prometheus-clusterRole.yaml
alertmanager-secret.yaml node-exporter-clusterRoleBinding.yaml prometheus-operator-serviceMonitor.yaml
alertmanager-serviceAccount.yaml node-exporter-clusterRole.yaml prometheus-prometheus.yaml
alertmanager-serviceMonitor.yaml node-exporter-daemonset.yaml prometheus-roleBindingConfig.yaml
alertmanager-service.yaml node-exporter-serviceAccount.yaml prometheus-roleBindingSpecificNamespaces.yaml
grafana-dashboardDatasources.yaml node-exporter-serviceMonitor.yaml prometheus-roleConfig.yaml
grafana-dashboardDefinitions.yaml node-exporter-service.yaml prometheus-roleSpecificNamespaces.yaml
grafana-dashboardSources.yaml prometheus-adapter-apiService.yaml prometheus-rules.yaml
grafana-deployment.yaml prometheus-adapter-clusterRoleAggregatedMetricsReader.yaml prometheus-serviceAccount.yaml
grafana-serviceAccount.yaml prometheus-adapter-clusterRoleBindingDelegator.yaml prometheus-serviceMonitorApiserver.yaml
grafana-serviceMonitor.yaml prometheus-adapter-clusterRoleBinding.yaml prometheus-serviceMonitorCoreDNS.yaml
grafana-service.yaml prometheus-adapter-clusterRoleServerResources.yaml prometheus-serviceMonitorKubeControllerManager.yaml
kube-state-metrics-clusterRoleBinding.yaml prometheus-adapter-clusterRole.yaml prometheus-serviceMonitorKubelet.yaml
kube-state-metrics-clusterRole.yaml prometheus-adapter-configMap.yaml prometheus-serviceMonitorKubeScheduler.yaml
kube-state-metrics-deployment.yaml prometheus-adapter-deployment.yaml prometheus-serviceMonitor.yaml
kube-state-metrics-roleBinding.yaml prometheus-adapter-roleBindingAuthReader.yaml prometheus-service.yaml
kube-state-metrics-role.yaml prometheus-adapter-serviceAccount.yaml setup
kube-state-metrics-serviceAccount.yaml prometheus-adapter-service.yaml
kube-state-metrics-serviceMonitor.yaml prometheus-clusterRoleBinding.yaml ./setup:
0namespace-namespace.yaml prometheus-operator-0prometheusruleCustomResourceDefinition.yaml prometheus-operator-deployment.yaml
prometheus-operator-0alertmanagerCustomResourceDefinition.yaml prometheus-operator-0servicemonitorCustomResourceDefinition.yaml prometheus-operator-serviceAccount.yaml
prometheus-operator-0podmonitorCustomResourceDefinition.yaml prometheus-operator-clusterRoleBinding.yaml prometheus-operator-service.yaml
prometheus-operator-0prometheusCustomResourceDefinition.yaml prometheus-operator-clusterRole.yamlls -R
[root@k8s-32 manifests]# kubectl create -f setup/.
namespace/monitoring created
customresourcedefinition.apiextensions.k8s.io/alertmanagers.monitoring.coreos.com created
customresourcedefinition.apiextensions.k8s.io/podmonitors.monitoring.coreos.com created
customresourcedefinition.apiextensions.k8s.io/prometheuses.monitoring.coreos.com created
customresourcedefinition.apiextensions.k8s.io/prometheusrules.monitoring.coreos.com created
customresourcedefinition.apiextensions.k8s.io/servicemonitors.monitoring.coreos.com created
clusterrole.rbac.authorization.k8s.io/prometheus-operator created
clusterrolebinding.rbac.authorization.k8s.io/prometheus-operator created
deployment.apps/prometheus-operator created
service/prometheus-operator created
serviceaccount/prometheus-operator created
[root@k8s-32 manifests]# kubectl create -f .
alertmanager.monitoring.coreos.com/main created
secret/alertmanager-main created
service/alertmanager-main created
serviceaccount/alertmanager-main created
servicemonitor.monitoring.coreos.com/alertmanager created
secret/grafana-datasources created
configmap/grafana-dashboard-apiserver created
configmap/grafana-dashboard-cluster-total created
configmap/grafana-dashboard-controller-manager created
configmap/grafana-dashboard-k8s-resources-cluster created
configmap/grafana-dashboard-k8s-resources-namespace created
configmap/grafana-dashboard-k8s-resources-node created
configmap/grafana-dashboard-k8s-resources-pod created
configmap/grafana-dashboard-k8s-resources-workload created
configmap/grafana-dashboard-k8s-resources-workloads-namespace created
configmap/grafana-dashboard-kubelet created
configmap/grafana-dashboard-namespace-by-pod created
configmap/grafana-dashboard-namespace-by-workload created
configmap/grafana-dashboard-node-cluster-rsrc-use created
configmap/grafana-dashboard-node-rsrc-use created
configmap/grafana-dashboard-nodes created
configmap/grafana-dashboard-persistentvolumesusage created
configmap/grafana-dashboard-pod-total created
configmap/grafana-dashboard-pods created
configmap/grafana-dashboard-prometheus-remote-write created
configmap/grafana-dashboard-prometheus created
configmap/grafana-dashboard-proxy created
configmap/grafana-dashboard-scheduler created
configmap/grafana-dashboard-statefulset created
configmap/grafana-dashboard-workload-total created
configmap/grafana-dashboards created
deployment.apps/grafana created
service/grafana created
serviceaccount/grafana created
servicemonitor.monitoring.coreos.com/grafana created
clusterrole.rbac.authorization.k8s.io/kube-state-metrics created
clusterrolebinding.rbac.authorization.k8s.io/kube-state-metrics created
deployment.apps/kube-state-metrics created
role.rbac.authorization.k8s.io/kube-state-metrics created
rolebinding.rbac.authorization.k8s.io/kube-state-metrics created
service/kube-state-metrics created
serviceaccount/kube-state-metrics created
servicemonitor.monitoring.coreos.com/kube-state-metrics created
clusterrole.rbac.authorization.k8s.io/node-exporter created
clusterrolebinding.rbac.authorization.k8s.io/node-exporter created
daemonset.apps/node-exporter created
service/node-exporter created
serviceaccount/node-exporter created
servicemonitor.monitoring.coreos.com/node-exporter created
apiservice.apiregistration.k8s.io/v1beta1.metrics.k8s.io created
clusterrole.rbac.authorization.k8s.io/prometheus-adapter created
clusterrole.rbac.authorization.k8s.io/system:aggregated-metrics-reader created
clusterrolebinding.rbac.authorization.k8s.io/prometheus-adapter created
clusterrolebinding.rbac.authorization.k8s.io/resource-metrics:system:auth-delegator created
clusterrole.rbac.authorization.k8s.io/resource-metrics-server-resources created
configmap/adapter-config created
deployment.apps/prometheus-adapter created
rolebinding.rbac.authorization.k8s.io/resource-metrics-auth-reader created
service/prometheus-adapter created
serviceaccount/prometheus-adapter created
clusterrole.rbac.authorization.k8s.io/prometheus-k8s created
clusterrolebinding.rbac.authorization.k8s.io/prometheus-k8s created
servicemonitor.monitoring.coreos.com/prometheus-operator created
prometheus.monitoring.coreos.com/k8s created
rolebinding.rbac.authorization.k8s.io/prometheus-k8s-config created
rolebinding.rbac.authorization.k8s.io/prometheus-k8s created
rolebinding.rbac.authorization.k8s.io/prometheus-k8s created
rolebinding.rbac.authorization.k8s.io/prometheus-k8s created
role.rbac.authorization.k8s.io/prometheus-k8s-config created
role.rbac.authorization.k8s.io/prometheus-k8s created
role.rbac.authorization.k8s.io/prometheus-k8s created
role.rbac.authorization.k8s.io/prometheus-k8s created
prometheusrule.monitoring.coreos.com/prometheus-k8s-rules created
service/prometheus-k8s created
serviceaccount/prometheus-k8s created
servicemonitor.monitoring.coreos.com/prometheus created
servicemonitor.monitoring.coreos.com/kube-apiserver created
servicemonitor.monitoring.coreos.com/coredns created
servicemonitor.monitoring.coreos.com/kube-controller-manager created
servicemonitor.monitoring.coreos.com/kube-scheduler created
servicemonitor.monitoring.coreos.com/kubelet createdkubectl create -f .
3、等待部署完成
kubectl get pod -n monitoring
NAME READY STATUS RESTARTS AGE
alertmanager-main-0 2/2 Running 0 65m
alertmanager-main-1 2/2 Running 0 65m
alertmanager-main-2 2/2 Running 0 65m
grafana-7c54b4677d-btwfb 1/1 Running 0 65m
kube-state-metrics-58b656b699-p8m29 3/3 Running 0 65m
node-exporter-rc5mx 2/2 Running 0 65m
node-exporter-vdzkb 2/2 Running 0 65m
node-exporter-xzdw2 2/2 Running 0 65m
prometheus-adapter-7d6f96974c-76m4z 1/1 Running 0 65m
prometheus-k8s-0 3/3 Running 1 65m
prometheus-k8s-1 3/3 Running 1 65m
prometheus-operator-5bd99d6457-89n7h 1/1 Running 0 66m
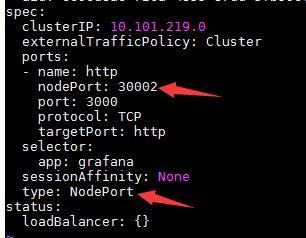
4、更改访问模式(ClusterIP => NodePort)
1)Prometheus
kubectl edit svc/prometheus-k8s -n monitoring
2)Alert Manager
kubectl edit svc/alertmanager-main -n monitoring
3)Grafana
kubectl edit svc/grafana -n monitoring
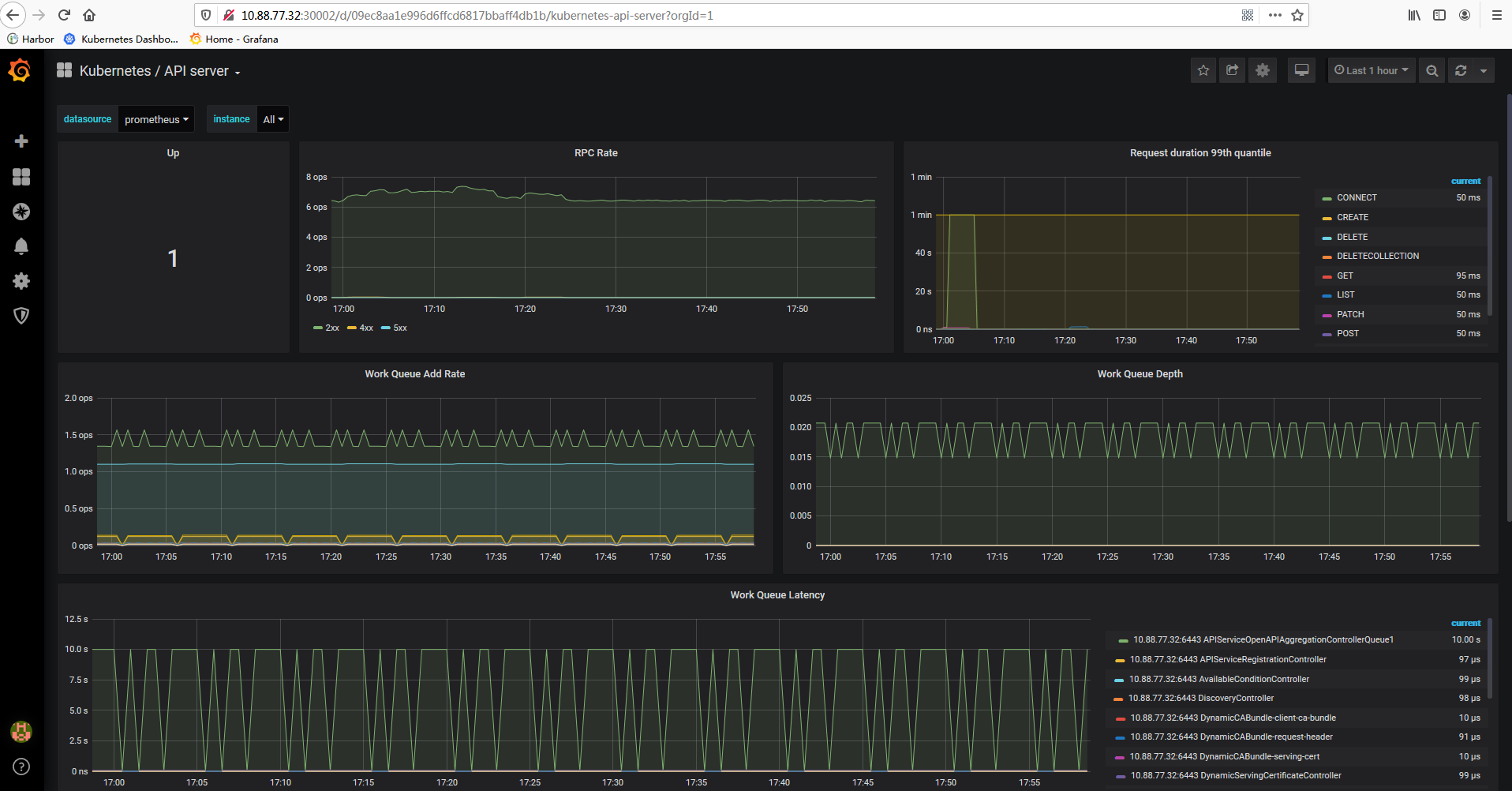
5、访问MasterIP:Port,其中Grafana默认用户名和密码都是admin
>>> 普罗米修斯功能强大,目前我也还没有完全掌握,具体应用还需要大家自己深度学习。
作者:Leozhanggg
出处:https://www.cnblogs.com/leozhanggg/p/12661566.html
本文版权归作者和博客园共有,欢迎转载,但未经作者同意必须保留此段声明,且在文章页面明显位置给出原文连接,否则保留追究法律责任的权利。
Kubernetes实战总结 - Prometheus部署的更多相关文章
- kubernetes实战篇之部署一个.net core微服务项目
目录 继上一篇kubernetes理论知识完结.本篇主要讲解基于nexus搭建一个docker镜像仓库(当然大家实践过程是不必完全跟着做,也可以搭建harbor仓库或者直接把镜像推送到docker h ...
- Kubernetes实战总结 - 自定义Prometheus
一.概述 首先Prometheus整体监控结构略微复杂,一个个部署并不简单.另外监控Kubernetes就需要访问内部数据,必定需要进行认证.鉴权.准入控制, 那么这一整套下来将变得难上加难,而且还需 ...
- kubernetes二进制高可用部署实战
环境: 192.168.30.20 VIP(虚拟) 192.168.30.21 master1 192.168.30.22 master2 192.168.30.23 node1 192.168.30 ...
- 新书推荐《再也不踩坑的Kubernetes实战指南》
<再也不踩坑的Kubernetes实战指南>终于出版啦.目前可以在京东.天猫购买,京东自营和当当网预计一个星期左右上架. 本书贴合生产环境经验,解决在初次使用或者是构建集群中的痛点,帮 ...
- 2020 最新 Kubernetes实战指南
1.Kubernetes带来的变革 对于开发人员 由于公司业务多,开发环境.测试环境.预生产环境和生产环境都是隔离的,而且除了生产环境,为了节省成本,其他环境可能是没有日志收集的,在没有用k8s的 ...
- Kubernetes实战总结 - 阿里云ECS自建K8S集群
一.概述 详情参考阿里云说明:https://help.aliyun.com/document_detail/98886.html?spm=a2c4g.11186623.6.1078.323b1c9b ...
- OpenFaaS实战之一:部署
欢迎访问我的GitHub https://github.com/zq2599/blog_demos 内容:所有原创文章分类汇总及配套源码,涉及Java.Docker.Kubernetes.DevOPS ...
- Kubernetes(k8s)集群部署(k8s企业级Docker容器集群管理)系列目录
0.目录 整体架构目录:ASP.NET Core分布式项目实战-目录 k8s架构目录:Kubernetes(k8s)集群部署(k8s企业级Docker容器集群管理)系列目录 一.感谢 在此感谢.net ...
- kubernetes实战(二十五):kubeadm 安装 高可用 k8s v1.13.x
1.系统环境 使用kubeadm安装高可用k8s v.13.x较为简单,相比以往的版本省去了很多步骤. kubeadm安装高可用k8s v.11 和 v1.12 点我 主机信息 主机名 IP地址 说明 ...
随机推荐
- JS数组遍历方法集合
就让我们在逆战中成长吧,加油武汉,加油自己 1.for循环 使用零时变量将长度存起来,当数组较大时优化效果才会比较明显. var ar1=[2,4,6,8] for(var i=0;i<ar1. ...
- 关于使用ajax导出excel问题
最近有个需求是在页面导入文件,后端进行处理后返回处理结果的excel,前端使用的是ajax.我最开始的做法是:在原有代码后加一段导出excel的代码,结果代码能正常运行,但页面始终没有返回我需要的ex ...
- TCP数据报结构以及三次握手(图解)
简要介绍 TCP(Transmission Control Protocol,传输控制协议)是一种面向连接的.可靠的.基于字节流的通信协议,数据在传输前要建立连接,传输完毕后还要断开连接.客户端在收发 ...
- django中CBV源码分析
前言:Django的视图处理方式有两种: FBV(function base views) 是在视图里基于函数形式处理请求. CBV(class base views)是在视图里基于类的形式处理请求. ...
- go bufio 、os 包
程序使用短变量声明创建bufio.Scanner类型的变量input. input := bufio.NewScanner(os.Stdin) 该变量从程序的标准输入中读取内容.每次调用input.S ...
- web自动化的三大等待
由于web网页打开后需要时间进行数据的传送,页面的渲染,所以我们在写web自动化脚本的时候,需要等待它加载完所有的页面元素,我们才进行操作或点击.同时这种等待也是为了提高脚本的稳定性. seleniu ...
- 一口气说出 6种,@Transactional注解的失效场景
整理了一些Java方面的架构.面试资料(微服务.集群.分布式.中间件等),有需要的小伙伴可以关注公众号[程序员内点事],无套路自行领取 一口气说出 9种 分布式ID生成方式,面试官有点懵了 面试总被问 ...
- 一文带你解读:卷积神经网络自动判读胸部CT图像的机器学习原理
本文介绍了利用机器学习实现胸部CT扫描图像自动判读的任务,这对我来说是一个有趣的课题,因为它是我博士论文研究的重点.这篇文章的主要参考资料是我最近的预印本 “Machine-Learning-Base ...
- 从零搭建Spring Cloud Gateway网关(二)—— 打印请求响应日志
作为网关,日志记录是必不可少的功能,可以在网关出增加requestId来查询整个请求链的调用执行情况等等. 打印请求日志 打印请求日志最重要的就是打印请求参数这些东西,不过RequestBody通常情 ...
- vscode 的tab空格设置设置为4的方法
1.点击“文件>首选项>设置” 进入设置页面,设置如下几个选项 2.在“文件>首选项>设置” 的“用户设置”里添加 "editor.detectIndentation ...
