mosquitto --- 单向认证
1.生成证书
要单向配置SSL 需要 做三项前置工作
1. 生成CA证书
2.生成server 端证书,server 端key
github 的一个开源项目已经做到这点 ,详情可见 https://github.com/iandl/mqttitude/blob/master/tools/TLS/generate-CA.sh
为方便阅读,整个shell 代码先贴出来
#!/bin/sh
#(@)generate-CA.sh - Create CA key-pair and server key-pair signed by CA # Copyright (c) 2013 Jan-Piet Mens <jpmens()gmail.com>
# All rights reserved.
#
# Redistribution and use in source and binary forms, with or without
# modification, are permitted provided that the following conditions are met:
#
# 1. Redistributions of source code must retain the above copyright notice,
# this list of conditions and the following disclaimer.
# 2. Redistributions in binary form must reproduce the above copyright
# notice, this list of conditions and the following disclaimer in the
# documentation and/or other materials provided with the distribution.
# 3. Neither the name of mosquitto nor the names of its
# contributors may be used to endorse or promote products derived from
# this software without specific prior written permission.
#
# THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS"
# AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
# IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
# ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE
# LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
# CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
# SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
# INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
# CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
# ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
# POSSIBILITY OF SUCH DAMAGE. set -e DIR=${TARGET:='.'}
# A space-separated list of alternate hostnames (subjAltName)
# may be empty ""
ALTHOSTNAMES="broker.example.com foo.example.de"
CA_ORG='/O=MQTTitude.org/emailAddress=nobody@example.net'
CA_DN="/CN=An MQTT broker${CA_ORG}"
CACERT=${DIR}/ca
SERVER=${DIR}/server
SERVER_DN="/CN=$(hostname -f)$CA_ORG"
keybits=2048
openssl=$(which openssl) function maxdays() {
nowyear=$(date +%Y)
years=$(expr 2032 - $nowyear)
days=$(expr $years '*' 365) echo $days
} function getipaddresses() {
/sbin/ifconfig |
sed -En '/inet6? /p' |
sed -Ee 's/inet6? (addr:)?//' |
awk '{print $1;}' |
sed -e 's/[%/].*//' |
egrep -v '(::1|127\.0\.0\.1)' # omit loopback to add it later
} function addresslist() { ALIST=""
for a in $(getipaddresses); do
ALIST="${ALIST}IP:$a,"
done
ALIST="${ALIST}IP:127.0.0.1,IP:::1," for h in $(echo ${ALTHOSTNAMES}); do
ALIST="${ALIST}DNS:$h,"
done
ALIST="${ALIST}DNS:localhost"
echo $ALIST } days=$(maxdays) if [ -n "$CAKILLFILES" ]; then
rm -f $CACERT.??? $SERVER.??? $CACERT.srl
fi if [ ! -f $CACERT.crt ]; then
# Create un-encrypted (!) key
$openssl req -newkey rsa:${keybits} -x509 -nodes -days $days -extensions v3_ca -keyout $CACERT.key -out $CACERT.crt -subj "${CA_DN}"
echo "Created CA certificate in $CACERT.crt"
$openssl x509 -in $CACERT.crt -nameopt multiline -subject -noout chmod 400 $CACERT.key
chmod 444 $CACERT.crt
fi if [ ! -f $SERVER.key ]; then
echo "--- Creating server key and signing request"
$openssl genrsa -out $SERVER.key $keybits
$openssl req -new \
-out $SERVER.csr \
-key $SERVER.key \
-subj "${SERVER_DN}"
chmod 400 $SERVER.key
fi if [ -f $SERVER.csr -a ! -f $SERVER.crt ]; then # There's no way to pass subjAltName on the CLI so
# create a cnf file and use that. CNF=`mktemp /tmp/cacnf.XXXXXXXX` || { echo "$0: can't create temp file" >&2; exit 1; }
sed -e 's/^.*%%% //' > $CNF <<\!ENDconfig
%%% [ JPMextensions ]
%%% basicConstraints = critical,CA:false
%%% nsCertType = server
%%% keyUsage = nonRepudiation, digitalSignature, keyEncipherment
%%% nsComment = "Broker Certificate"
%%% subjectKeyIdentifier = hash
%%% authorityKeyIdentifier = keyid,issuer:always
%%% subjectAltName = $ENV::SUBJALTNAME
%%% # issuerAltName = issuer:copy
%%% nsCaRevocationUrl = http://mqttitude.org/carev/
%%% nsRevocationUrl = http://mqttitude.org/carev/
!ENDconfig SUBJALTNAME="$(addresslist)"
export SUBJALTNAME # Use environment. Because I can. ;-) echo "--- Creating and signing server certificate"
$openssl x509 -req \
-in $SERVER.csr \
-CA $CACERT.crt \
-CAkey $CACERT.key \
-CAcreateserial \
-CAserial "${DIR}/ca.srl" \
-out $SERVER.crt \
-days $days \
-extfile ${CNF} \
-extensions JPMextensions rm -f $CNF
chmod 444 $SERVER.crt
fi
实际过程中大家可根据自己的需要修改这段脚本的内容,为了快速搭建我们的单向SSL, 我们这里不做任何修改,直接执行这段shell
执行完成后可生成 server.crt server.csr server.ke ca.crt ca.key ca.srl
$ wget https://github.com/iandl/mqttitude/blob/master/tools/TLS/generate-CA.sh .
$ bash ./generate-CA.sh
配置mosquitto 配置文件
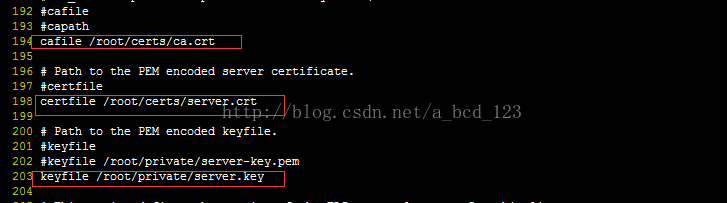
ca.crt, sever.crt, server.key 是上面生成的文件
启动 broker
启动 subscribe 端, 这里需要注意,如果sbuscreibe 端和broker 不在同一台机器,请将第一步生成的ca.crt 拷贝到 该机器的/root/certs下

启动 publish 端, 如果publish 端和broker 不在同一台机器,请将第一步生成的ca.crt 拷贝到 该机器的/root/certs下

mosquitto --- 单向认证的更多相关文章
- mosquitto ---SSL/TLS 单向认证+双向认证
生成证书 # * Redistributions in binary form must reproduce the above copyright # notice, this list of ...
- 基于mosquitto的MQTT服务器---SSL/TLS 单向认证+双向认证
基于mosquitto的MQTT服务器---SSL/TLS 单向认证+双向认证 摘自:https://blog.csdn.net/ty1121466568/article/details/811184 ...
- mosquitto SSL认证
[11]MQTT mosquitto 双向SSL认证配置方式 [12]MQTT mosquitto 单向SSL认证的配置方式 Mosquitto服务器的搭建以及SSL/TLS安全通信配置(比较可信) ...
- java https单向认证(忽略认证)并支持http基本认证
https单向认证(忽略认证)并支持http基本认证, 温馨提示 1,jar包要导入对 2,有匿名类编译要注意 3,欢迎提问,拿走不谢!背景知识 Https访问的相关知识中,主要分为单向验证和双向验证 ...
- https单向认证和双向认证
单向认证: .clinet<--server .clinet-->server .client从server处拿到server的证书,通过公司的CA去验证该证书,以确认server是真实的 ...
- ssl双向认证和单向认证原理
有朋友在搞一个项目,周末有聊到一些安全性的东西,很自然会想起https,但https究竟如何实施,其原理又是什么? 基于ssl,一般的应用都是单向认证,如果应用场景要求对客户来源做验证也可以实现成双向 ...
- wildfly9 配置SSL单向认证/https
D:\>keytool -genkey -keystore cdi-init.keystore -alias cdi-init -keyalg RSA -keysize 2048 -validi ...
- tomcat 配置https (单向认证)
1.单向认证,就是传输的数据加密过了,但是不会校验客户端的来源 2.双向认证,如果客户端浏览器没有导入客户端证书,是访问不了web系统的,找不到地址 如果只是加密,单向就行 如果想要用系统的人没有证书 ...
- tomcat------https单向认证和双向认证
一.https分为单向认证和双向认证: 单向认证就是说,只有客户端使用ssl时对服务器端的证书进行认证,也就是说,客户端在请求建立之前,服务器端会向客户端发送一个证书,一般情况下,这种证书都是由自己 ...
随机推荐
- timeago.js-时间显示插件
注意事项: 1. 时间格式 = “2018-03-02 17:13:00”时,动态获取的时间无法通过 拼接字符串的方法 添加到 dom元素的 datetime属性上,结果为 <div class ...
- css中!important的优先级问题
css中!important的优先级在主页面中写>在外部引用的css文件 之前我一直以为css的样式不管写在哪里只要加上!important那么它的优先级就是最高的,事实上并不是这样的,尤其在动 ...
- iOS开发中虚拟键盘相关的坑
初学者在学习iOS开发时,遇到在一个textField中输入完内容后却发现虚拟键盘无法隐藏起来而不知所措的情况的人一定不占少数吧.这篇文章就说说我遇到的和虚拟键盘有关的三个问题及解决对策. 在模拟器测 ...
- Talairach空间、MNI空间、Native空间、Stereotaxic空间
Talairach空间.MNI空间.Native空间.Stereotaxic空间 Native空间就是原始空间. 图像没有做任何变换时就是在原始空间.在这个空间中图像的维度.原点.voxel size ...
- Android 下文件cannot execute - Permission denied
安卓下执行交叉编译的可执行文件发现提示不允许. 原因是mount的方式问题,root后运行 su mount -o rw,remount /mnt/sdcard 就可以了 mount -o rw,re ...
- UBUNTU 14.04 INSTALL nsenter
cd /tmp; curl https://www.kernel.org/pub/linux/utils/util-linux/v2.25/util-linux-2.25.tar.gz | tar - ...
- [Linux] git send-email的使用
1. git send-email is included in an individual package, named "git-email":$ sudo apt-get i ...
- Python学习(九)IO 编程 —— 文件读写
Python 文件读写 Python内置了读写文件的函数,用法和C是兼容的.本节介绍内容大致有:文件的打开/关闭.文件对象.文件的读写等. 本章节仅示例介绍 TXT 类型文档的读写,也就是最基础的文件 ...
- Python学习 —— 阶段综合练习三
Python学习 —— 阶段综合练习三 综合之前文件与文件夹操作的学习,做以下实例练习:(建议先不要看代码,自己先试着写:代码仅供参考,有多种实现方法) 1. 目录文件遍历(二层目录结构) 1). ...
- python的with和__enter__ 、 __exit__
__enter__(): 在使用with语句时调用,会话管理器在代码块开始前调用,返回值与as后的参数绑定 __exit__(): 会话管理器在代码块执行完成好后调用,在with语句完成时,对象销 ...
