Openshift 用户,角色和RBAC
OCP中的权限管理沿用的Kubernetes RBAC机制,授权模式主要取决于下面几个因数
|
Rules |
针对主要对象的操作权限,比如建立Pod Sets of permitted verbs on a set of objects. For example, whether something can |
|
Roles |
一系列的Rules的集合,用户和组能关联这些Roles Collections of rules. Users and groups can be associated with, or bound to, multiple roles at the same time. |
|
Bindings |
用户和组针对角色的关联 Associations between users and/or groups with a role. |
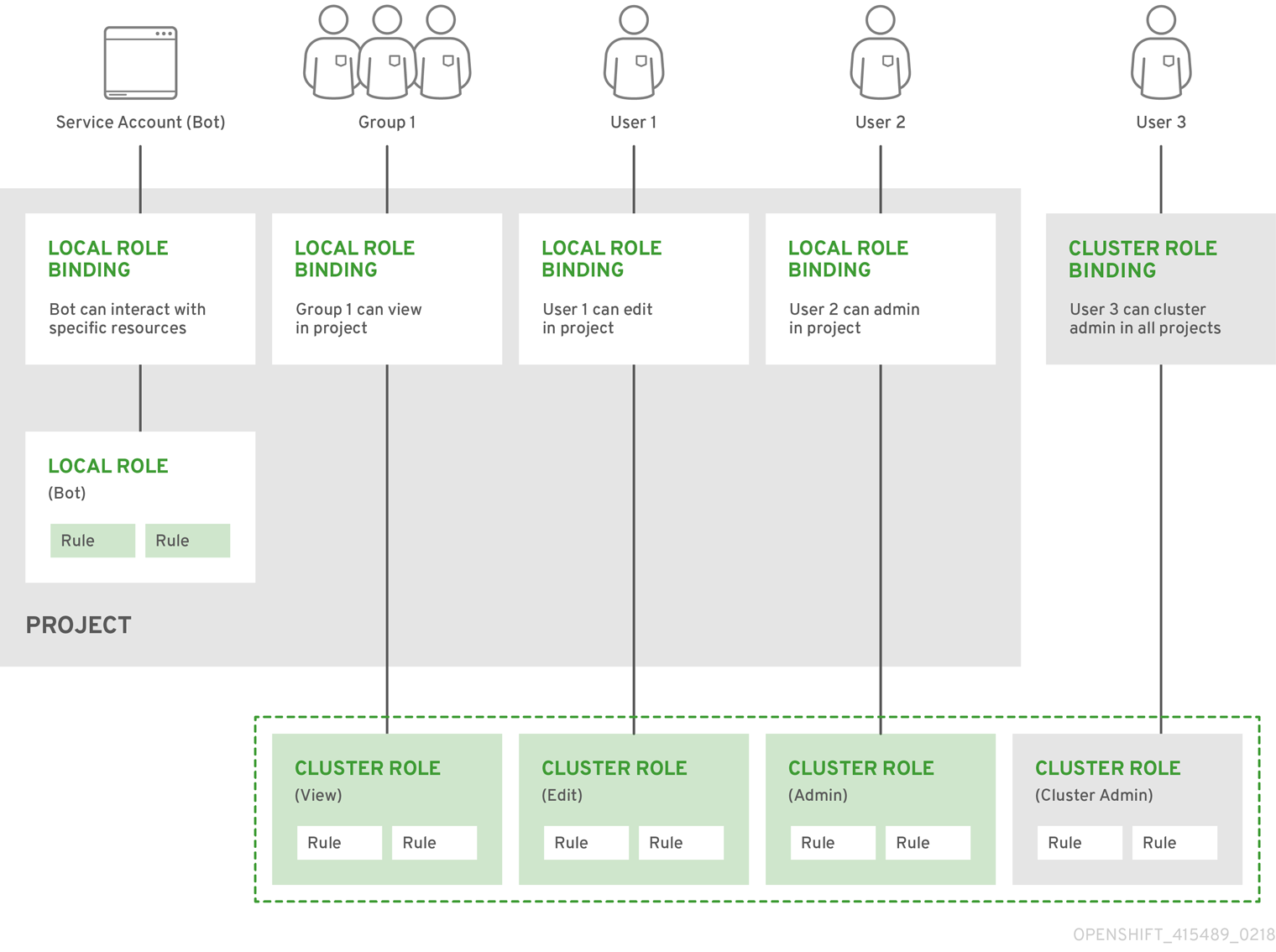
RBAC分成两种,一种是集群范围内的,叫做Cluster RBAC,一种是项目范围内的,叫Local RBAC,官方定义如下
|
Cluster RBAC |
Roles and bindings that are applicable across all projects. Roles that exist cluster-wide are considered cluster roles. Cluster role bindings can only reference cluster roles. |
|
Local RBAC |
Roles and bindings that are scoped to a given project. Roles that exist only in a project are considered local roles. Local role bindings can reference both cluster and local roles. |
而当前的Cluster Role包括如下:
| Default Cluster Role | Description |
|---|---|
|
admin |
A project manager. If used in a local binding, an admin user will have rights to view any resource in the project and modify any resource in the project except for quota. |
|
basic-user |
A user that can get basic information about projects and users. |
|
cluster-admin |
A super-user that can perform any action in any project. When bound to a user with a local binding, they have full control over quota and every action on every resource in the project. |
|
cluster-status |
A user that can get basic cluster status information. |
|
edit |
A user that can modify most objects in a project, but does not have the power to view or modify roles or bindings. |
|
self-provisioner |
A user that can create their own projects. |
|
view |
A user who cannot make any modifications, but can see most objects in a project. They cannot view or modify roles or bindings. |
下面实际操作一下加深理解。
- 添加用户
htpasswd /etc/origin/master/htpasswd eric htpasswd /etc/origin/master/htpasswd alice
- 查看用户
首先需要以管理员身份登录
[root@master ~]# oc login -u system:admin
Logged into "https://master.example.com:8443" as "system:admin" using existing credentials. You have access to the following projects and can switch between them with 'oc project <projectname>': default
kube-public
kube-service-catalog
kube-system
logging
management-infra
myproject
openshift
openshift-ansible-service-broker
openshift-infra
openshift-node
openshift-template-service-broker
openshift-web-console
* test Using project "test".
[root@master ~]# oc get users
NAME UID FULL NAME IDENTITIES
admin 7594833f-efd1-11e8-bd01-0800275a35ec htpasswd_auth:admin
alice 517c077e-f094-11e8-bc3a-0800275a35ec htpasswd_auth:alice
eric 9ff08197-f093-11e8-bc3a-0800275a35ec htpasswd_auth:eric
eric和alice各自建立project,eric创建myproject,alice创建test项目
- 以alice登录后查看rolebinding
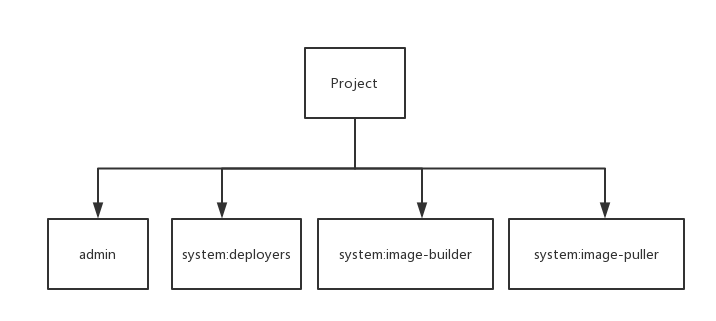
[root@master ~]# oc get rolebinding
NAME ROLE USERS GROUPS SERVICE ACCOUNTS SUBJECTS
admin /admin alice
system:deployers /system:deployer deployer
system:image-builders /system:image-builder builder
system:image-pullers /system:image-puller system:serviceaccounts:test
也就是说每个新建立的项目包含的本地rolebinding包括
- 查看每个rolebinding具体关联的role和用户
[root@master ~]# oc describe rolebinding.rbac
Name: admin
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: admin
Subjects:
Kind Name Namespace
---- ---- ---------
User alice Name: system:deployers
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: system:deployer
Subjects:
Kind Name Namespace
---- ---- ---------
ServiceAccount deployer test Name: system:image-builders
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: system:image-builder
Subjects:
Kind Name Namespace
---- ---- ---------
ServiceAccount builder test Name: system:image-pullers
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: system:image-puller
Subjects:
Kind Name Namespace
---- ---- ---------
Group system:serviceaccounts:test
- 给alice用户授予访问myproject的admin权限
[root@master ~]# oc adm policy add-role-to-user admin alice -n myproject
role "admin" added: "alice"
如果只是需要拉取myproject命名空间下的镜像,可以赋予image-puller权限就可以了
[root@master ~]# oc adm policy add-role-to-user system:image-puller alice -n myproject
role "system:image-puller" added: "alice"
再度describe一下
[root@master ~]# oc describe rolebinding.rbac -n myproject
Name: admin
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: admin
Subjects:
Kind Name Namespace
---- ---- ---------
User eric Name: admin-
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: admin
Subjects:
Kind Name Namespace
---- ---- ---------
User alice
Name: system:deployers
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: system:deployer
Subjects:
Kind Name Namespace
---- ---- ---------
ServiceAccount deployer myproject Name: system:image-builders
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: system:image-builder
Subjects:
Kind Name Namespace
---- ---- ---------
ServiceAccount builder myproject Name: system:image-puller
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: system:image-puller
Subjects:
Kind Name Namespace
---- ---- ---------
User alice Name: system:image-pullers
Labels: <none>
Annotations: <none>
Role:
Kind: ClusterRole
Name: system:image-puller
Subjects:
Kind Name Namespace
---- ---- ---------
Group system:serviceaccounts:myproject
- 查看所有的clusterrole
[root@master ~]# oc get clusterrole
NAME
admin
asb-access
asb-auth
basic-user
cluster-admin
cluster-debugger
cluster-reader
cluster-status
edit
hawkular-metrics
hawkular-metrics-admin
.....
- 查看具体的一个clusterrole能做的内容
[root@master ~]# oc describe clusterrole system:image-builder
Name: system:image-builder
Created: hours ago
Labels: <none>
Annotations: openshift.io/description=Grants the right to build, push and pull images from within a project. Used primarily with service accounts for builds.
openshift.io/reconcile-protect=false
Verbs Non-Resource URLs Resource Names API Groups Resources
[get update] [] [] [image.openshift.io ] [imagestreams/layers]
[create] [] [] [image.openshift.io ] [imagestreams]
[update] [] [] [build.openshift.io ] [builds/details]
[get] [] [] [build.openshift.io ] [builds]
所有缺省的ClusterRole都能绑定用户或组到本地项目中。此外可以自己定义本地Role
==============================================================================================
给权限和回收权限
给一个imager:pruner的权限,以及给一个集群管理员的权限
oc adm policy add-cluster-role-to-user system:image-pruner eric oc adm policy add-cluster-role-to-user cluster-admin eric
查看
[root@master ~]# oc get rolebindings
NAME ROLE USERS GROUPS SERVICE ACCOUNTS SUBJECTS
admin /admin eric
system:deployers /system:deployer deployer
system:image-builders /system:image-builder builder
system:image-pruner /system:image-pruner eric
system:image-pullers /system:image-puller system:serviceaccounts:openshift3
回收
[root@master ~]# oc adm policy remove-role-from-user system:image-pruner eric
role "system:image-pruner" removed: "eric"
取消eric的对项目的admin权限,而给只读权限
[root@master ~]# oc adm policy add-role-to-user view eric
role "view" added: "eric"
[root@master ~]# oc adm policy remove-role-from-user admin eric
role "admin" removed: "eric"
[root@master ~]# oc get rolebinding
NAME ROLE USERS GROUPS SERVICE ACCOUNTS SUBJECTS
system:deployers /system:deployer deployer
system:image-builders /system:image-builder builder
system:image-pullers /system:image-puller system:serviceaccounts:openshift3
view /view eric
可以参考
https://docs.openshift.com/container-platform/3.9/admin_guide/manage_rbac.html
Openshift 用户,角色和RBAC的更多相关文章
- [转]扩展RBAC用户角色权限设计方案
原文地址:http://www.iteye.com/topic/930648 RBAC(Role-Based Access Control,基于角色的访问控制),就是用户通过角色与权限进行关联.简单地 ...
- 扩展RBAC用户角色权限设计方案
RBAC(Role-Based Access Control,基于角色的访问控制),就是用户通过角色与权限进行关联.简单地说,一个用户拥有若干角色,每一个角色拥有若干权限.这样,就构造成“用户-角色- ...
- RBAC用户角色权限设计方案
RBAC(Role-Based Access Control,基于角色的访问控制),就是用户通过角色与权限进行关联.简单地说,一个用户拥有若干角色,每一个角色拥有若干权限.这样,就构造成“用 户-角色 ...
- 扩展RBAC用户角色权限设计方案(转载)
扩展RBAC用户角色权限设计方案 来源:https://www.cnblogs.com/zwq194/archive/2011/03/07/1974821.html https://blog.csd ...
- RBAC用户角色权限设计方案【转载】
RBAC(Role-Based Access Control,基于角色的访问控制),就是用户通过角色与权限进行关联.简单地说,一个用户拥有若干角色,每一个角色拥有若干权限.这样,就构造成“用户-角色- ...
- 扩展RBAC用户角色权限设计方案<转>
RBAC(Role-Based Access Control,基于角色的访问控制),就是用户通过角色与权限进行关联.简单地说,一个用户拥有若干角色,每一个角色拥有若干权限.这样,就构造成“用户-角色- ...
- MVC开发模式下的用户角色权限控制
前提: MVC开发模式 大概思想: 1.在MVC开发模式下,每个功能都对应着不同的控制器或操作方法名(如修改密码功能可能对应着User/changepd),把每个功能对应的控制器名和操作方法名存到数据 ...
- [.Net MVC] 用户角色权限管理_使用CLK.AspNet.Identity
项目:后台管理平台 意义:一个完整的管理平台需要提供用户注册.登录等功能,以及认证和授权功能. 一.为何使用CLK.AspNet.Identity 首先简要说明所采取的权限控制方式.这里采用了基于角色 ...
- spring-boot-plus V1.4.0发布 集成用户角色权限部门管理
RBAC用户角色权限 用户角色权限部门管理核心接口介绍 Shiro权限配置
- Django-用户权限,用户角色使用指南
RBAC(Role-Based Access Control,基于角色的访问控制)就是用户通过角色与权限进行关联.简单地说,一个用户拥有若干角色,每一个角色拥有若干权限.这样,就构造成"用户 ...
随机推荐
- 16:django 有条件的视图处理(Last-Modified和ETag)&&加密签名
有条件的视图处理 上一节我们介绍了缓存来减轻服务器的负担,这里的有条件的视图处理也从一定程度上减轻了服务器的负担,在正式介绍之前,先来看两个概念:Last-Modified和ETag Last-Mod ...
- 字符串截取,SubString
aaarticlea/png;base64,iVBORw0KGgoAAAANSUhEUgAAAk8AAACYCAIAAAByAZqHAAAYgklEQVR4nO2dL28ku5qHTS4ctuTSQf ...
- redis之(三)redis的数据类型
[一]字符串类型(基本数据类型) --->字符串类型是redis的最基本的数据类型 --->能存储任何形式的字符串,(用户邮箱,json化的对象,一张图片) --->一个字符串类型的 ...
- hdu 1426(DFS+坑爹的输入输出)
Sudoku Killer Time Limit: 2000/1000 MS (Java/Others) Memory Limit: 65536/32768 K (Java/Others)Tot ...
- mybatis spring sqlsession
sqlsession是什么? 从 http://blog.csdn.net/hupanfeng/article/details/9238127 知道 sqlsession创建 可以看出,创建sqlse ...
- PHP生成随机字符串与唯一字符串
代码如下: <?php /* * 生成随机字符串 * @param int $length 生成随机字符串的长度 * @param string $char 组成随机字符串的字符串 * @ret ...
- Ant Design React按需加载
Ant Design是阿里巴巴为React做出的组件库,有统一的样式及一致的用户体验 官网地址:https://ant.design 1.安装: npm install ant --save 2.引用 ...
- vmware漏洞之三——Vmware虚拟机逃逸漏洞(CVE-2017-4901)Exploit代码分析与利用
本文简单分析了代码的结构.有助于理解. 转:http://www.freebuf.com/news/141442.html 0×01 事件分析 2017年7月19 unamer在其github上发布了 ...
- git "Could not read from remote repository.Please make sure you have the correct access rights."解决方案
我们在使用git clone 或其他命令的时候,有时候会遇到这类问题,如图: fatal: Could not read from remote repository.Please make sure ...
- angularjs学习笔记1-angular总体简介及其特点
以前开发(web或者移动端)前端主要使用jQuery+原生js,如果使用某些前端UI框架的话,它自己还可能提供一些API可以使用.而且目前很多UI框架都是基于jQuery的,所以说一下由jQuery跨 ...
