kali linux Desktop Environemt types and kali linux install virualbox
1、we know the kali linux desktop environmet can also be costomized ,Desktop environmet can use GNOME(default) ,KDE (K Desktop Environmet) ,and LXDE(Loghtweight x11 Desktop Environmet)
we set command under windows: nbtstat -A [ip address] .we will get the NetBIOS remote Macine Name Tables
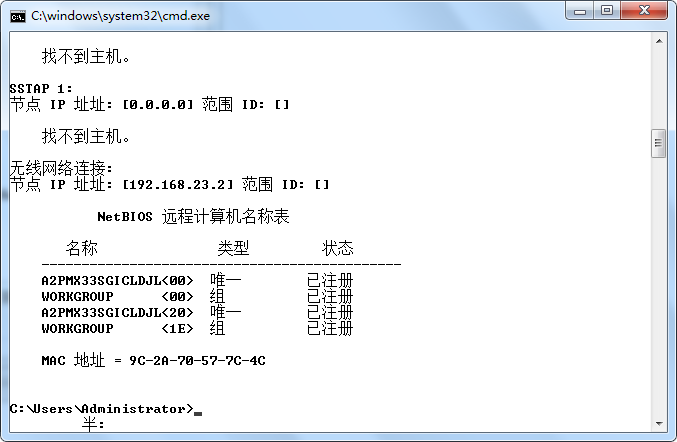
as we see in the picture ,if you do have a hex code <20> then you may have cause for concern now i will explain
if show code of <20> means you have file and printer sharing turned on ., aditional we cna use the command : net share to show the sharing file
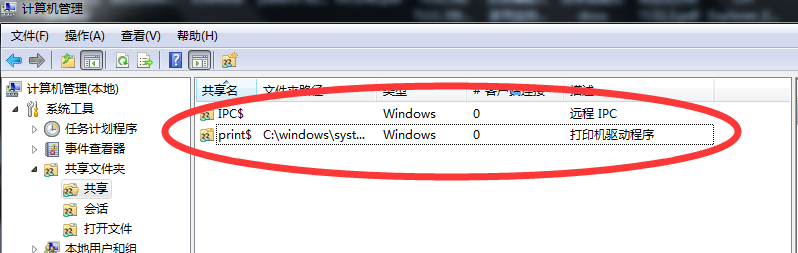

2、OK let we san on the local computer who sharing the file ,we can use the command : net view [ip_address]
then we use the command :net use [ip_address] get the touch the victim computer
above all,this attack was called Netbios attack ,if you want to improved the security closed the sharing
3、 we nest to see the Trojans
for example: Netbus and SubSeven
how we can installl a Trojans file in another computer .we can use the joiner utility will combine the two files together and output one executable file call nice name executed file
another way to spread the Trojans by the Email and Unsafe web Sites and IRC(Internet Relay Chat 因特网中继聊天)、 Chat Sites
4、acceptable file
there is no reasno for any files to be sent to you in any of the above formats if they are text douments ,there is no reason a file should have a double extension ,such files you shoud ever receive them should be treated with suspicion .
5、who are Hackers
A port scanner is a handy tool that scans a computer lookinh for active ports ,with this utility ,a potential hacker can figure out what services are acilable on the target computer form the responses the port scanner receives take a look at the list for reference
for example start scan the target Host: www.shutongyaming.com.cn
we looked the Sub Seven Trojan:
the Sub Seven Trojan has many features and capabilities ,it is in my opinion by far the most advance Trojan I hace seen Take a look at some of the features of SubSeven
- address book
- WWP Page Retrierve Get Windows CD-KEY update vicitim from URL ICQ takeover FTP root floder
- retrieve dial-up passwords along with phone number and usernames prot redirect IRCbot for a list of commands
- UIIn2IP \reomte IP Scanner
6、SQL injection Question
While performing web application and penetration testing following scenario is very command and hides potential exploitable SQL injection scenario.
- We have SQL injection point but it is not throwing any error messages out as part of its response,Applicationg is sending customized erroe page ehich is not revealing any signature bu which we can deduce potential SQL flaw
- knowing SQL injectiong potin or loophole in web application xp_cmdshell seems to be worKing,but we can't say is it working or not since it doesn't return any meaningful signature tthis is blind xp_cmdShell
- FireWall don't allow outbound traffic so can't do ftp tftp ping etc from the box to the internet bu which you can confirm execution of the command on the target system
- we don't know the actual path to path to webroot so can't copy file to location whic can be accessed over Http or Https later to confirm the execution of the command
- if we know path to webroot adn directory structure but can't find execute permission on it so can't copy cmd.exe or any other binary and execute over HTTP/HTTPS
kali linux Desktop Environemt types and kali linux install virualbox的更多相关文章
- Running a Remote Desktop on a Windows Azure Linux VM (远程桌面到Windows Azure Linux )-摘自网络(试了,没成功 - -!)
A complete click-by-click, step-by-step video of this article is available ...
- Redis进阶实践之六Redis Desktop Manager连接Windows和Linux系统上的Redis服务
一.引言 今天本来没有打算写这篇文章,当初我感觉使用这个工具应该很简单,下载的过程也不复杂,也没有打算记录下来.但是在使用的过程中还是出现了一些问题,为了给第一次使用Redis Desktop Man ...
- Redis进阶实践之六Redis Desktop Manager连接Windows和Linux系统上的Redis服务(转载6)
Redis进阶实践之六Redis Desktop Manager连接Windows和Linux系统上的Redis服务 一.引言 今天本来没有打算写这篇文章,但是,今天测试Redis的时候发现了两个问题 ...
- 免费在线 Linux Desktop 环境
免费在线 Linux Desktop 环境 Run Linux OS Distributions online https://www.onworks.net/os-distributions 免费测 ...
- Linux学习总结(17)——Linux新手必须学会的12个命令
今天的用户可以根据自己的意愿选择是否使用作为Linux象征的命令行,确切的证明了Linux已经有了很大的发展.现在很多Linux发行版的图形用户界面已经非常强大,不再需要命令行. 但是命令行在Linu ...
- Linux 验证当前 Video0 不否是v4l设备 linux v4l 编程(1) Video 4 Linux 简介
#include <stdio.h> #include <string.h> #include <errno.h> #include <sys/types.h ...
- linux入门系列3--常见的linux远程登陆管理工具
服务器一般是云服务器或者放置在机房,我们日常工作中通过远程连接工具连接到服务器进行操作,这类工具很多(如SecureCRT.XShell.Putty.FinallShell.TeamViewer以及w ...
- Linux下ps命令详解 Linux下ps命令的详细使用方法
http://www.jb51.net/LINUXjishu/56578.html Linux下的ps命令比较常用 Linux下ps命令详解Linux上进程有5种状态:1. 运行(正在运行或在运行队列 ...
- Linux系统的理解及学习Linux内核的心得
作业列表 (点击作业跳转) linux内核分析作业:以一简单C程序为例,分析汇编代码理解计算机如何工作 linux内核分析作业:操作系统是如何工作的进行:完成一个简单的时间片轮转多道程序内核 ...
随机推荐
- idea里面lombok要如何设置后才会生效
16:31 Lombok Requires Annotation Processing Annotation processing seems to be disabled for the proje ...
- 迅速生成项目-react-scripts
推荐指数:
- 【Leetcode_easy】868. Binary Gap
problem 868. Binary Gap solution1: class Solution { public: int binaryGap(int N) { ; vector<int&g ...
- linux如何找回已经删除的文件?lsof
简介 lsof(list open files)是一个列出当前系统打开文件的工具.在linux环境下,任何事物都以文件的形式存在,通过文件不仅仅可以访问常规数据,还可以访问网络连接和硬件.所以如传输控 ...
- Appium移动自动化测试-----(四)安装 appium Server
我们可以在Appium官方网站上下载操作系统相应的Appium版本. https://bitbucket.org/appium/appium.app/downloads/ 当前最新版本为 Appium ...
- [转帖]HAProxy 7层 负载均衡
HAProxy 7层 负载均衡 https://www.cnblogs.com/jicki/p/5546902.html HAProxy 系统 CentOS 5.8 x64 wget http://h ...
- crontab每小时运行一次
先给出crontab的语法格式 对于网上很多给出的每小时定时任务写法,可以说绝大多数都是错误的!比如对于下面的这种写法: 00 * * * * #每隔一小时执行一次 00 */1 * * * #与上面 ...
- Python34之模块测试(__name__ == "__main__")
def c2f(cel): fah = cel * 1.8 + 32 return fah def f2c(fah): cel = (fah -32) / 1.8 return cel def tes ...
- Django开发常用方法及面试题
目录 1.对Django的认识? 2.Django .Flask.Tornado的对比 3.什么是wsgi,uwsgi,uWSGI? 4. django请求的生命周期? 5. 简述什么是FBV和CBV ...
- Linux基础-03-用户、群组
1. 用户及passwd文件 1) /etc/passwd文件的功能:存储所有用户的相关信息,该文件也被称为用户信息数据库(Database). 2) /etc/passwd文件每个字段的具体含义: ...
