Python Ethical Hacking - VULNERABILITY SCANNER(6)
EXPLOITATION - XSS VULNS
EXPLOITING XSS
- Run any javascript code.
- Beef framework can be used to hook targets.
- Inject Beef hook in vulnerable pages.
- Execute code from beef.
BeEF is short for The Browser Exploitation Framework. It is a penetration testing tool that focuses on the web browser.
https://github.com/beefproject/beef
Start the BeEF service.

Login the DVWA website, then open the XSS Stored page. Sign one record on the guestbook. (Modify the maxlength if necessary)
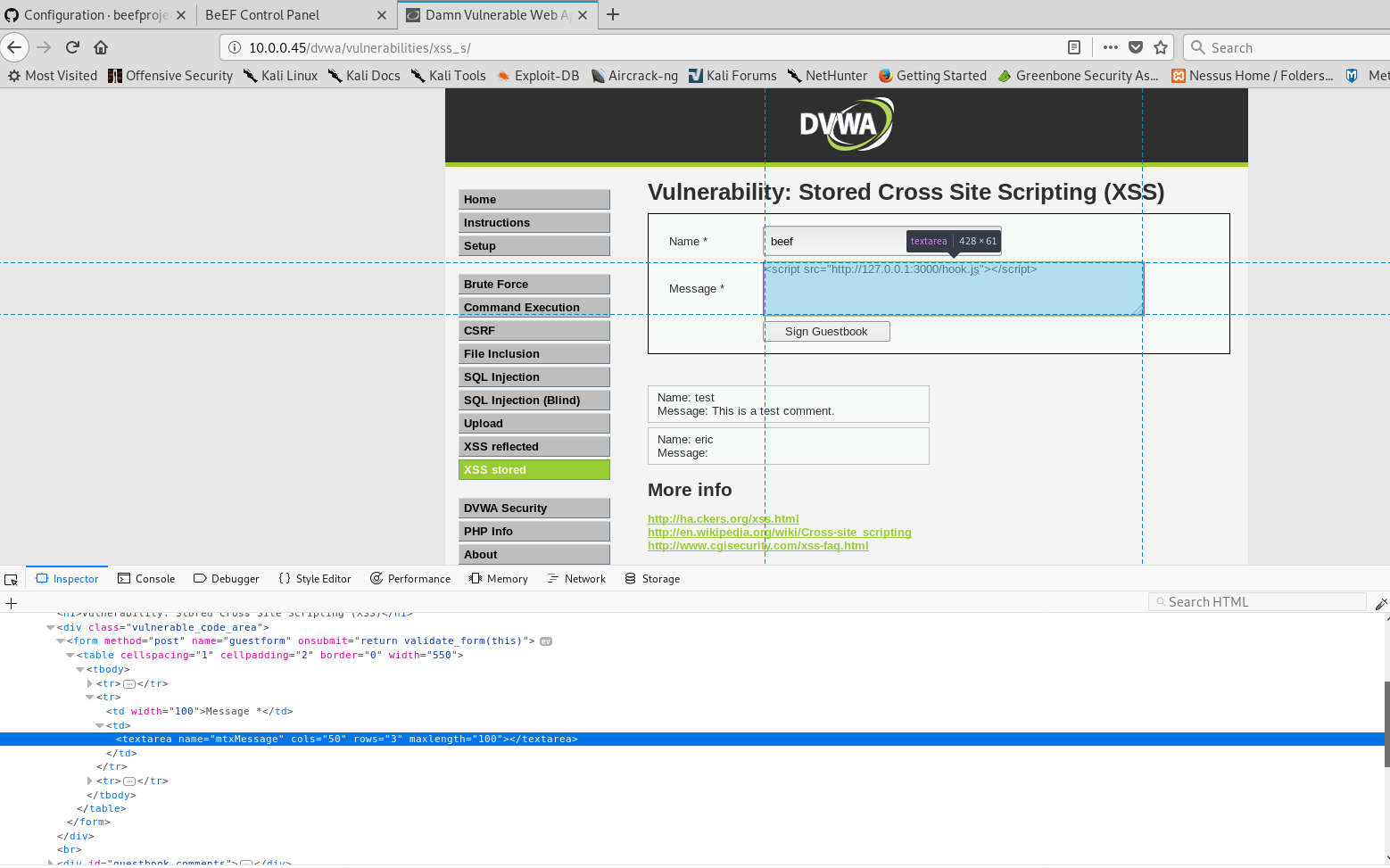
Open the DVWA web site on the victim PC. Then login to the BeEF Control Panel. You can find the information about the hooked PC.

Create Alert Dialog and execute it.

Python Ethical Hacking - VULNERABILITY SCANNER(6)的更多相关文章
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
- Python Ethical Hacking - VULNERABILITY SCANNER(7)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(4)
Extracting & Submitting Forms Automatically Target website:http://10.0.0.45/dvwa/vulnerabilities ...
- Python Ethical Hacking - VULNERABILITY SCANNER(2)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(8)
Implementing Code To Discover XSS in Parameters 1. Watch the URL of the XSS reflected page carefully ...
- Python Ethical Hacking - VULNERABILITY SCANNER(3)
Polish the Python code using sending requests in a session Class Scanner. #!/usr/bin/env python impo ...
- Python Ethical Hacking - VULNERABILITY SCANNER(1)
HTTP REQUESTS BASIC INFORMATION FLOW The user clicks on a link. HTML website generates a request(cli ...
- Python Ethical Hacking - VULNERABILITY SCANNER(5)
EXPLOITATION - XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript cod ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- php 判断设备是手机还是平板还是pc
1 <?php 2 //获取USER AGENT 3 $agent = strtolower($_SERVER['HTTP_USER_AGENT']); 4 5 //分析数据 6 $is_pc ...
- Redis的String探索之路
String是redis最基本的类型,键值对(Key : Value 形式),Redis 的 String 可以包含任何数据,最大能存储 512 MB.(一个键最大能存储 512MB) Redis 的 ...
- elasticSearch中集群状态的guan'l
es中集群出现上面的问题一般是磁盘空间不够引起的,就是node节点所在的磁盘空间不足引起的 es整个集群放在c盘,都快满了 说明es的磁盘已经快被使用完了,我们可以临时更新下磁盘空间大小 修改 ES分 ...
- skywalking中文文档
https://github.com/apache/skywalking/blob/v5.0.0-alpha/docs/README_ZH.md 大家可以前往如下地址下载我们的发布包: l Apac ...
- CentOS 安装 VMware Tools 详细方法
点击虚拟机,选择安装vmware Tools工具 弹出上面的界面,右键选择奖上面的vmwaraTools.tar.gz解压到你要解压的目录下面 记得一定要使用root用户,进入到解压的目录 然后执行 ...
- JavaWeb网上图书商城完整项目--day02-27.查询所有分类功能之Servlet和Service层
我们在上面实现了数据库层的代码,现在我们来实现业务层和Servlet层的代码:业务层的代码如下: package com.weiyuan.goods.category.service; import ...
- Python-argparse模块-获取命令行参数
#!/usr/bin/python3 """ Author : Jet Bi License : www.cyeap.com Summary : 获取命令行的参数 Not ...
- C#数据结构与算法系列(十五):排序算法(SortAlgorithm)
1.介绍 排序是将一组数据,以指定的顺序进行排序的过程 2.分类 内部排序法:指将需要处理的所有数据都加载到内部存储器中进行排序 外部排序法:数据量过大,无法全部加载到内存中,需要借助外部存储进行排序
- Codeforces Round #652 (Div. 2) 总结
A:问正n边形的一条边和x轴平行的时候有没有一条边和y轴重合,直接判断n是否是4的倍数 #include <iostream> #include <cstdio> #inclu ...
- maven跳过测试打包
1.在执行run as时候加上参数: clean install compile -Dmaven.test.skip=true 2.在pom文件中添加如下: <plugins> < ...
