PatentTips - Posting interrupts to virtual processors
BACKGROUND
Generally, the concept of virtualization in information processing systems allows multiple instances of one or more operating systems (each, an "OS") to run on a single information processing system, even though each OS is designed to have complete, direct control over the system and its resources. Virtualization is typically implemented by using software (e.g., a virtual machine monitor, or a "VMM") to present to each OS a "virtual machine" ("VM") having virtual resources, including one or more virtual processors, that the OS may completely and directly control, while the VMM maintains a system environment for implementing virtualization policies such as sharing and/or allocating the physical resources among the VMs (the "virtualization environment"). Each OS, and any other software, that runs on a VM is referred to as a "guest" or as "guest software," while a "host" or "host software" is software, such as a VMM, that runs outside of the virtualization environment.
A physical processor in an information processing system may support virtualization, for example, by supporting an instruction to enter a virtualization environment to run a guest on a virtual processor (i.e., a physical processor under constraints imposed by a VMM) in a VM. In the virtualization environment, certain events, operations, and situations, such as external interrupts or attempts to access privileged registers or resources, may be intercepted, i.e., cause the processor to exit the virtualization environment so that a VMM may operate, for example, to implement virtualization policies (a "VM exit").
Therefore, external interrupts may be intercepted by the VMM and routed to the appropriate virtual processor. Alternatively, a virtualization environment may provide for external interrupts to be routed to a virtual processor without a VM exit, for example, if the interrupt request is generated by an input/output ("I/O") device assigned to the currently active VM, or if the interrupt request is an inter-processor interrupt between two virtual processors in the same VM. Whether the interrupt request causes a VM exit or not, routing the interrupt to the appropriate virtual processor may include mapping interrupts requests from a guest's view of the system to a host's view of the system. In existing information processing systems, the VMM may be responsible for remapping interrupt requests whenever a virtual processor is migrated from one physical processor to another physical processor.
DETAILED DESCRIPTION
Embodiments of the present invention provide for posting, in a data structure in a memory, interrupt requests to virtual processors. Posting interrupt requests according to embodiments of the present invention may be desirable for several reasons.
First, as the number of physical processors and cores per system increases, the use of techniques for optimizing system performance and efficiency by migrating virtual processors among the physical processors and cores increases. Embodiments of the present invention may provide for these techniques to be less complex, by providing for all interrupt requests destined for a virtual processor to be migrated atomically.
Second, posting of interrupts according to embodiments of the present invention may provide for the delivery of external interrupts to a virtual processor to depend on the state of the virtual processor, potentially increasing system performance by reducing the number of VM exits. For example, an interrupt request for a virtual processor that is waiting for one of its quanta of time on a physical processor may be held pending in memory, without causing a VM exit, until the virtual processor is running.
Third, I/O device virtualization, for example as provided for the Peripheral Component Interconnect ("PCI") Express Single-Root I/O Virtualization Specification (available from http://www.pcisig.org), may provide for a single physical I/O device to be configured as multiple virtual I/O devices, each assignable to a different VM. Therefore, many more interrupt sources are possible in a virtualization environment than in a conventional system. To accommodate this possibility, embodiments of the present invention may provide for many more interrupt vectors than would be available in a prior art system, by supporting a virtual vector space for each virtual processor.
FIG. 1 illustrates an embodiment of the present invention in information processing system 100. Information processing system 100 includes bare platform hardware 110, which may be any apparatus capable of executing any OS, VMM, or other software. For example, bare platform hardware 110may be the hardware of a personal computer, a mainframe computer, a portable computer, a handheld device, a set-top box, a server, or any other computing system. In this embodiment, bare platform hardware 110 includes processors 120 and 122, chipset 130, system memory 140, and device150.
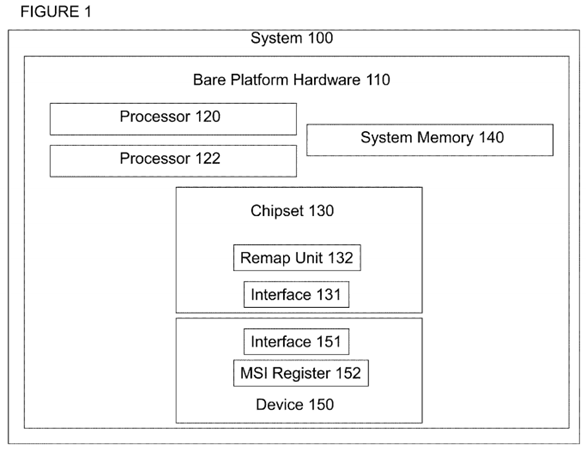
Processors 120 and 122 may be any components having one or more execution cores, where each execution core may be based on any of a variety of different types of processors, including a general purpose microprocessor, such as a processor in the Intel® Pentium® Processor Family, Itanium® Processor Family, or other processor family from Intel® Corporation, or another processor from another company, or a digital signal processor or microcontroller. Although FIG. 1 shows two processors, bare processing hardware 110 may include any number of processors, including any number of multicore processors, each with any number of execution cores, and any number of multithreaded processors, each with any number of threads.
Chipset 130 may be any group of circuits and logic that supports memory operations, input/output operations, configuration, control, internal or external interface, connection, or communications functions (e.g., "glue" logic and bus bridges), and/or any similar functions for processors 120 and 122 and/or system 100. Individual elements of chipset 130 may be grouped together on a single chip, a pair of chips, dispersed among multiple chips, and/or be integrated partially, totally, redundantly, or according to a distributed approach into one or more processors, including processors 120 and/or 122. In this embodiment, chipset 130 includes interrupt remapping unit 132 for remapping or posting interrupts according to an embodiment of the invention, as described below. In other embodiments, interrupt remapping unit 132 may be included elsewhere in system 100.
System memory 140 may be any medium on which information, such as data and/or program code, may be stored, such as static or dynamic random access memory, semiconductor-based read-only or flash memory, magnetic or optical disk memory, or any other type of medium readable by processors 120 and 122, or any combination of such mediums.
Device 150 may represent any type of I/O, peripheral, or other device that may be the source of an interrupt request, such as a keyboard, mouse, trackball, pointing device, monitor, printer, media card, network interface, information storage device, etc. Device 150 may be embodied in a discrete component, or may be included in an integrated component with any other devices. In one embodiment, device 150 may represent a function in a multifunctional I/O, peripheral, or other device.
Processors 120 and 122, chipset 130, system memory 140, and device 150 may be coupled to or communicate with each other according to any known approach, such as directly or indirectly through one or more parallel, sequential, pipelined, asynchronous, synchronous, wired, wireless, or other bus or point-to-point connection or means of communication. For example, in this embodiment chipset 130 includes interface 131 to receive signals, messages, and/or transactions, such as interrupt requests, from device 150, or transmit signals, messages, and/or transactions to device 150 and/or any other agents or components in system 100, through any such connection or other means of communication. Similarly, device 150 includes interface151 to transmit and/or receive signals, messages, and/or transactions to chipset 130, and/or any other agents or components in system 100. System100 may also include any number of additional agents, components, or connections.
FIG. 2 illustrates chipset 130, including remapping unit 132, according to one embodiment of the present invention. Remapping unit 132 includes look-up logic 220, routing logic 230, and posting logic 240. Chipset 130 also includes interface 131, described above, and interrupt controller 210.
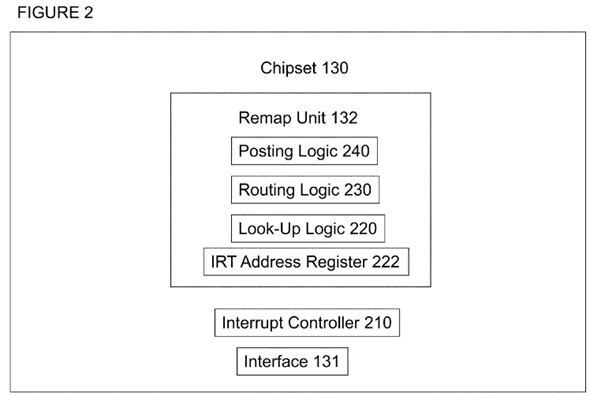
Chipset 130 may receive an interrupt request through interface 131. An interrupt request may also be generated from within chipset 130, for example where a timer or other device that may generate an interrupt is included in chipset 130. In one embodiment, an interrupt request may be received as a signal, such as a level or edge triggered interrupt signal, according to any known signaling protocol. In another embodiment, an interrupt request may be received as a message, such as a bus message or a point-to-point transaction, according to any known message, transaction, or other communication protocol. Other embodiments are possible, including an embodiment using both signal and message based interrupt requests. In such an embodiment, chipset 130 may receive both types of requests; signal based requests through input terminals and message based requests through write transactions to an address or port corresponding to a register or other storage location assigned to the interrupt controller.
Look-up logic 220 is to look up an entry associated with an interrupt request, e.g., from device 150, in a data structure. Look-up logic 220 may be implemented with any logical structure or circuitry that performs a function of looking up or finding an entry in a data structure. The entry may be found using a "handle" as an entry number, address, index, pointer, or other locator of or to a particular entry in the data structure, where the handle is a value supplied directly or indirectly by the interrupt request.
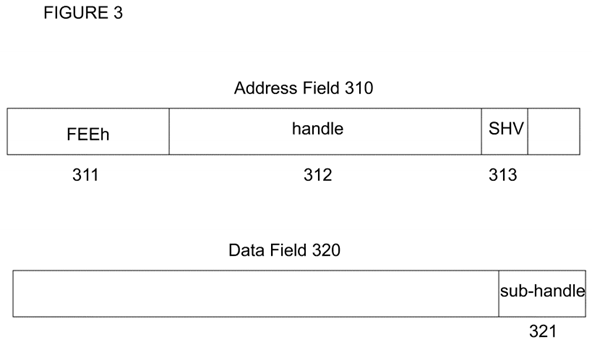
For example, according to a message signaled interrupt ("MSI") protocol of a PCI-Express bus, an interrupt message may include a 32-bit address field and a 32-bit data field, where bits 31:20 of the address field are set to the hexadecimal value "FEE" to indicate that the message is an interrupt request. The remaining bits of the fields may be used to indicate other information, such as the interrupt vector and the desired destination for the interrupt request. An embodiment of the present invention compatible with this protocol may use the formats shown in FIG. 3.
In FIG. 3, 32-bit address field 310 includes bit-fields 311, 312, and 313, and 32-bit data field 320 includes bit-field 321. Bit-field 311 may include bits31:20 of address field 310, and may be set to the hexadecimal value "FEE" to indicate that the message is an interrupt request. Bit-field 312 may include bits 19:5 and bit 2 of address field 310, and may be used to indicate a 16-bit handle value. Bit-field 313 may include bit 3 of address field 310, and may be used to indicate a 1-bit sub-handle valid ("SHV") value. Bit-field 321 may include bits 15:0 of data field 320, and may be used to indicate a 16-bit sub-handle value. The use of the SHV and sub-handle values will be described below. The remaining bits of address field 310 and data field 320may be treated as reserved or ignored.
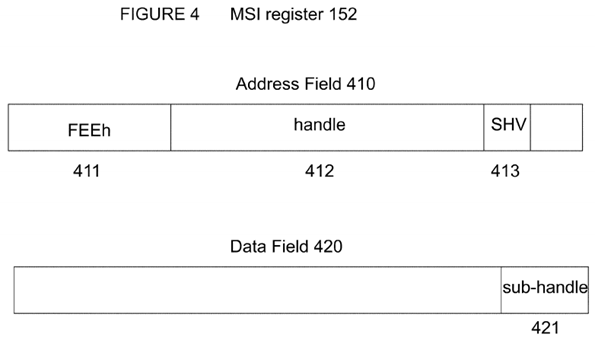
In order to generate an MSI transaction in such a format, device 150, or any other device in system 100, including a device integrated into chipset 130, may include a register or other storage location such as MSI register 152, as shown in FIG. 4. MSI register 152 may include 32-bit address field 410and 32-bit data field 420. Address field 410 includes bit-fields 411, 412, and 413, and data field 420 includes bit-field 421. Bit-field 411 may include bits31:20 of address field 410, and may be set to the hexadecimal value "FEE" to indicate that the message is an interrupt request. Bit-field 412 may include bits 19:5 and bit 2 of address field 410, and may be used to indicate a 16-bit handle value. Bit-field 413 may include bit 3 of address field 410, and may be used to indicate a 1-bit sub-handle valid ("SHV") value. Bit-field 421 may include bits 15:0 of data field 420, and may be used to indicate a 16-bit sub-handle value. The use of the SHV and sub-handle values will be described below. The remaining bits of address field 410 and data field 420may be treated as reserved or ignored.
In an embodiment where an interrupt request is sent as a signal, the signal may be received by or passed to interrupt controller 210. For example, interrupt controller 210 may have any number of input terminals (e.g., 24), each of which may be connected to a device (e.g., through an internal connector to a device within chipset 130, or through an internal connector to a pin or other terminal of chipset 130 to an external connector to a device external to chipset 130) that may generate an interrupt request, and interrupt controller 210 may include or have access to the same number (e.g., 24) of storage locations that may be programmed with or otherwise contain the information associated with each interrupt request, including a handle value.
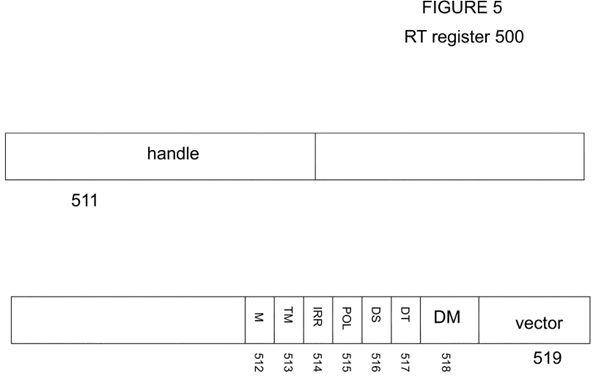
For example, in an embodiment using where interrupt controller 210 is an I/O Advanced Programmable Interrupt Controller ("IO APIC") according to the architecture of the Intel® Pentium® Processor Family, the redirection table ("RT") register of the I/O APIC may be programmed as shown in FIG. 5 in order to generate interrupts that are compatible with an embodiment of the invention. In FIG. 5, RT entry 500 includes bit-fields 511, 512, 513, 514,515, 516, 517, 518, and 519. Bit-field 511 includes bits 63:48 of RT entry 500, to indicate a 16-bit handle value. Bit-fields 512, 513, 514, 515, 516, and517 include bits 16, 15, 14, 13, 12, and 11, respectively, of RT entry 500, to indicate mask, trigger mode, remote interrupt request register, interrupt input pin polarity, delivery status, and destination mode values, respectively, and provide the functionality of the known programming model. Bit-field 518includes bits 10:8 of RT entry 500, to be set to logical '000' or '111' to indicate that the delivery mode is fixed or external, respectively. Bit-field 519includes bits 7:0 of RT entry 500, to indicate an 8-bit interrupt vector.
Returning to look-up logic 220 of FIG. 2, in one embodiment look-up logic 220 may use a 16-bit handle from an MSI transaction or a 16-bit handle from an IO APIC to find an entry in a single level interrupt remapping table ("IRT") having 64K entries, each entry having 128 bits (each an "IRTE"). In another embodiment, where an MSI transaction includes an SHV that is set to a logical '1', or otherwise indicates that it includes a valid sub-handle, a 16-bit sub-handle from the transaction may be applied (e.g., logically or arithmetically combined with, as a mask or offset value) to a 16-bit handle from the transaction to form an effective handle, and the effective handle may be used by look-up logic 220 to find an IRTE. The value of the effective handle may be checked to ensure that it is directing look-up logic 220 to a location within the IRT. Other embodiments may use different sizes of handles, sub-handles, effective handles, and IRTs.
An IRT, or any other data structure to which look-up logic 220 refers, may be stored in system memory 140, or in any other storage area in system 100. In some embodiments, IRTEs may be cached in a storage area in remapping unit 132 or in any other area that is temporally or physically nearer to look-up logic 220 than the IRT. The base address of the IRT may be stored in IRT address register 222, or any other storage location accessible to look-up logic 220.
In one embodiment, each IRTE may have the format shown in FIG. 6. In FIG. 6, IRTE 600 includes bit-fields 610, 612, 614, and 616. Bit-field 610 may include bit 15 ("PST") to indicate whether the interrupt request directed to this IRTE is to be remapped or posted. For example, if this bit is clear (PST is '0'), then an interrupt request directed to this IRTE will be forwarded by routing logic 240 to a destination corresponding to a destination value in the IRTE, depending on the values of other bit-fields in the IRTE. For example, if a requestor identifier from the interrupt request does not match a source value in the IRTE, the interrupt request may be blocked. Routing logic 240 may also block the interrupt request based on other criteria.

However, in this embodiment, if this bit is set (PST is '1'), then an interrupt request directed to this IRTE will be posted by posting logic 250, as described below. If the IRTE is designated for posting (e.g., PST is '1'), then bit-fields 612, 614, and 616 are defined and used as set forth below, and the remaining bits of the IRTE may be treated as reserved or ignored. However, if the IRTE is designated for remapping (e.g., PST is '0'), then the entire IRTE is defined and used as according to the specified remapping protocol, which is not described here.
If the IRTE is designated for posting (e.g., PST is '1'), then bit-field 612, 614, and 616 may be defined and used as follows. Bit-field 612 may include bit12 ("URG") to indicate is the interrupt request is urgent (i.e., time sensitive). The URG bit may be used to differentiate between interrupt requests that are urgent, such as from media devices, and interrupt requests that are more tolerant to interrupt processing latencies. Bit-field 614 ("Virtual Vector") may include bits 23:16 to indicate an eight bit virtual interrupt vector that is assigned to this interrupt request by the guest software running on the virtual processor that is the target of this interrupt request. Bit field 616 ("Posted-Interrupt Descriptor Address") may include bits 127:96 and 63:38 to indicate an address of a data structure for posting interrupts (a "posted-interrupt descriptor").
The posted-interrupt descriptor, or any other data structure to which the IRTE for a posted interrupt request refers, may be stored in system memory140, or in any other storage area in system 100. In one embodiment, a posted-interrupt descriptor may be the size of a line of a cache accessible to processors 120 and 122, and the address may be aligned to a cache line. For example, a posted-interrupt descriptor may be 64 bytes, with an address having all zeroes in the six least significant bits, therefore bit-field 616 may be used to store bits 63:6 of an address in the address space of processors120 and 122.
Software, such as a VMM, may allocate a posted-interrupt descriptor for each virtual processor that may be the target of external interrupt requests. A posted-interrupt descriptor according to one embodiment of the present invention is illustrated in FIG. 7. Posted-interrupt descriptor 700 in FIG. 7 includes bit-fields 710, 720, 730, and 740.
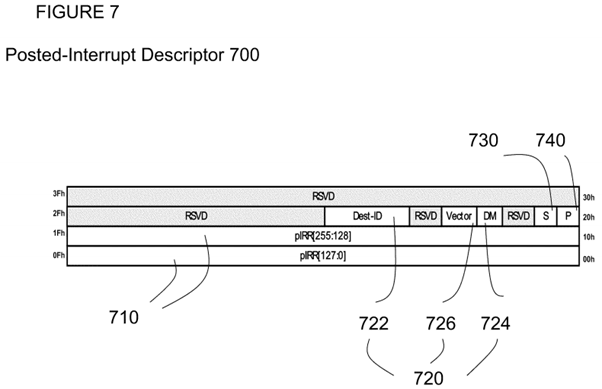
Bit-field 710 may include the lowest 32 bytes of the 64-byte posted-interrupt descriptor to form a 256-bit posted interrupt request register ("pIRR"). Each bit of the pIRR may correspond to one of 256 virtual interrupt vectors for the virtual processor corresponding to the posted-interrupt descriptor. Each bit of the pIRR may be set to post an interrupt request for the corresponding virtual interrupt vector.
Bit-field 720 may include three smaller bit-fields to indicate attributes of a notify event to be used to inform a VMM of pending posted interrupts. In one embodiment, the event used to notify a VMM that posted interrupts are pending may be a physical interrupt request to a physical processor. Therefore, using a physical processor that may support over one hundred physical interrupts, embodiments of the present invention may provide for over one hundred virtual processors per physical processor.
Notify event attributes bit-field 720 may include bit-fields 722, 724, and 726. Bit-field 722 ("Dest-ID") may include 32 bits to identify the destination of the interrupt request, which, for example, may be the local APIC for the physical processor on which the virtual processor that is the target of the interrupt request is running. The physical processor to which the target virtual processor has temporal affinity may change as virtual processors are migrated, so this field may be reprogrammed, by the VMM, with a new local APIC identifier in connection with a migration for load balancing or any other reason. The physical processor to which a target virtual processor has temporal affinity at any given time may be called the "notify-CPU" in this description, as it will be the physical processor to which a notify event will be sent when there are pending posted interrupts for that virtual processor.
Bit-field 724 ("DM") may include a single bit to indicate the mode for the notify event. For example, in an embodiment where the notify event is a physical interrupt, DM may indicate whether the value of Dest-ID should be interpreted as a physical or a logical identifier ("ID"). Bit-field 726 ("Physical Vector") may include eight bits to indicate the physical vector to be used for the notify event. When a notify event is delivered to the VMM, the VMM may use the physical vector to determine which virtual processor has pending posted interrupts in its posted-interrupt descriptor. Therefore, embodiments of the present invention provide for a single physical vector per virtual processor, instead of a physical vector for each virtual interrupt.
Bit-field 730 ("Supress" or "S") may include one bit to store a suppress flag to indicate whether notify events are to be suppressed when posting interrupts to this posted-interrupt descriptor. Software, such as VMM, may set this bit at any time to suppress notify events, such as when the corresponding virtual processor is not running because it is in the scheduler wait queue, waiting for one of its quanta of time to run. Bit-field 740("Pending" or "P") may include one bit to store a pending flag to indicate whether there is a pending notify event for this posted-interrupt descriptor that has not been serviced yet. If this flag is already set at the time an interrupt request is posted, then there is no need to send another notify event. This flag may be set by hardware when it sends a notify event, and cleared by software as part of servicing the notify event.
FIGS. 8 and 9 illustrate embodiments of the present invention in methods, specifically methods 800 for posting interrupts to virtual processors and method 900 for managing posted interrupts. Although method embodiments are not limited in this respect, reference may be made to the elements in the system embodiment of FIG. 1 and the apparatus embodiment of FIG. 2 to describe the method embodiments of FIGS. 8 and 9.
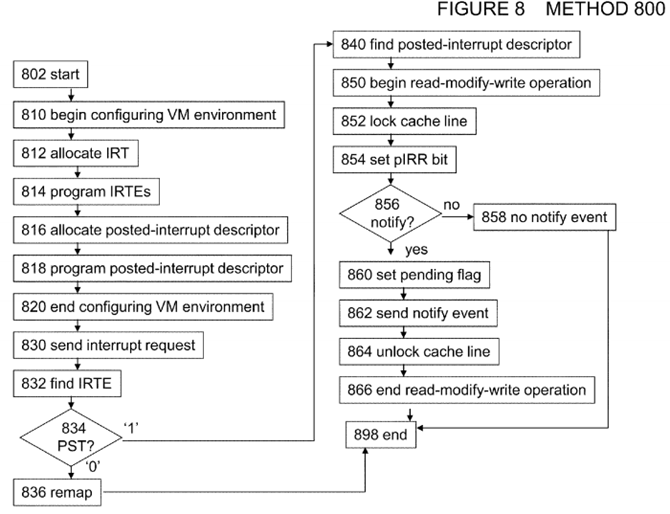
In box 802 of FIG. 8, method 800 begins.
In box 810 of FIG. 8, software such as a VMM begins to configure system 100 to support a virtualization environment, including posting interrupts to virtual processors. In box 812, the VMM allocates a memory region for an IRT, for example by programming IRT address register 222 with the base address of a memory region for an IRT. In box 814, the VMM begins to set up the IRT by programming each IRTE, including setting the PST bit for each IRTE for which posting (e.g., instead of remapping) will be performed. In box 816, the VMM allocates a posted-interrupt descriptor for each virtual processor, for example by programming each IRTE for which posting will be performed with the address of a memory region for a posted-interrupt descriptor. In box 818, the VMM programs each posted-interrupt descriptor with the desired attributes and other information. In box 820, configuration of system 100 to support the virtualization environment, including programming of the IRT and posted-interrupt descriptors, ends.
In box 830, an interrupt request, including the handle, is sent to chipset 130. In box 832, look-up logic 220 uses the handle from the interrupt request to find an IRTE. In box 834, the value of the PST bit in the IRTE is determined. If the PST bit is clear, method 800 continues to box 836, where the interrupt is remapped and forwarded, by routing logic 230, to the destination specified in the IRTE. However, if the PST bit is set, method 700 continues to box 840.
In box 840, the Posted-Interrupt Descriptor Address from the IRTE is used, for example by posting logic 240, to find the Posted-Interrupt Descriptor for this IRTE.
In box 850, a read-modify-write operation, for example by posting logic 240, is begun on the Posted-Interrupt Descriptor. An atomic read-modify-write operation is used to allow access to the Posted-Interrupt Descriptor by multiple sources, such as multiple instances of posting logic 240, other interrupt posting hardware, and software such as a VMM. In box 852, the cache line storing the Posted-Interrupt Descriptor is locked. In box 854, the pIRR bit corresponding to the Virtual Vector from the IRTE is set (or, if already set, it remains set).
In box 856, it is determined whether to generate a notify event. In one embodiment, the determination is based on the values of the URG bit in the IRTE and the Pending and Suppress bits in the Posted-Interrupt Descriptor, as follows. If the URG bit is set (i.e., the interrupt request is urgent) or the Suppress flag is not set (i.e., the VMM has not temporarily suppressed interrupt requests to this virtual processor), and the Pending bit is not set (i.e., there is not already a notify event pending for this virtual processor), then method 800 continues to box 860, where a notify event will be sent. Otherwise, method 800 continues to box 858, where no notify event is sent.
In box 860, the Pending flag in this posted-interrupt descriptor is set. In box 862, a notify event is sent to the destination specified by the Dest-ID and DM fields of the posted-interrupt descriptor, using the value in the Physical Vector field. For example, an interrupt message may be sent to the local APIC specified by the Dest-ID and DM fields, the interrupt message including the vector from the Physical Vector field. In box 864, the cache line is unlocked. In box 866, the atomic read-modify-write operation, begun in box 850, ends.
In box 898, method 800 ends.
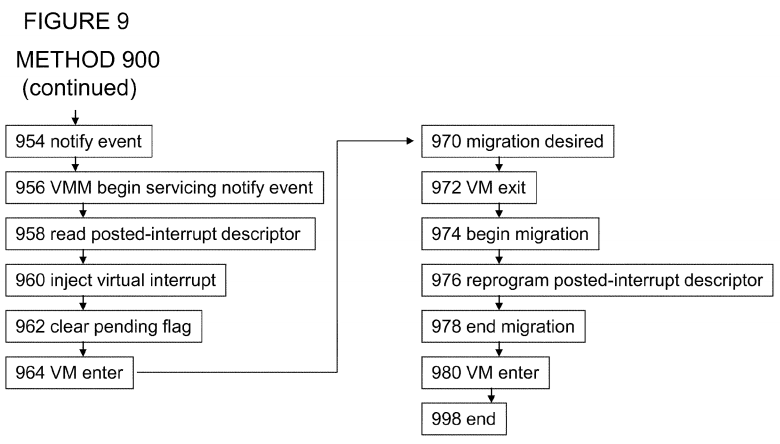
Turning to FIG. 9, method 900 is a method for managing posted interrupts according to an embodiment of the present invention. In box 902, method 900begins.
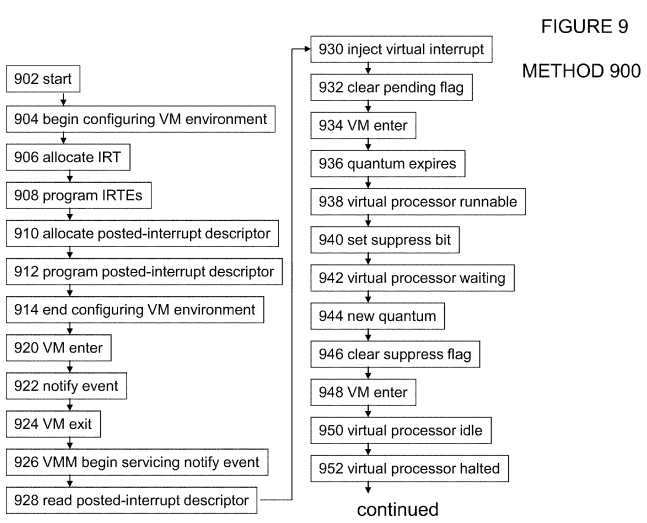
In box 904, software such as a VMM begins to configure system 100 to support a virtualization environment, including posting interrupts to virtual processors. In box 906, the VMM allocates a memory region for an IRT, for example by programming IRT address register 222 with the base address of a memory region for an IRT. In box 908, the VMM begins to set up the IRT by programming each IRTE, including setting the PST bit for each IRTE for which posting (e.g., instead of remapping) will be performed. In box 910, the VMM allocates a posted-interrupt descriptor for each virtual processor, for example by programming each IRTE for which posting will be performed with the address of a memory region for a posted-interrupt descriptor.
In box 912, the VMM programs each posted-interrupt descriptor with the desired attributes and other information. For example, the Dest-ID field of a posted-interrupt descriptor for a virtual processor set up to run on processor 120 may be programmed with the ID of the local APIC for processor 120, the DM may be set to physical, and the Physical Vector field may be programmed with the vector to be used by processor 120 to service the physical interrupt used as the posted-interrupt notify event. In box 914, configuration of system 100 to support the virtualization environment, including programming of the IRT and posted-interrupt descriptors, ends.
In box 920, a virtual processor may begin to run on a physical processor, such as processor 120, in system 100. Therefore, the virtual processor is in an active state and its notify-CPU is processor 120. In box 922, a notify event for the virtual processor, for example a physical interrupt from box 862 of method 800, may be received by processor 120, causing a VM exit in box 924. In box 926, the VMM begin to service the physical interrupt, using the physical vector to identify the virtual processor for which the notify event was sent. In box 928, the VMM may read the posted-interrupt descriptor for the virtual processor to determine the virtual interrupt request that is pending, according to the pIRR. In box 930, the VMM may inject the virtual interrupt request into the virtual processor for servicing. In box 932, the VMM may clear the Pending flag in the posted-interrupt descriptor. In box 934, the virtual processor may be restarted on physical processor 120.
In box 936, the virtual processor's quantum may expire, so in box 938, the virtual processor may move into a runnable state. In box 940, the VMM may set the Suppress flag in the posted-interrupt descriptor, in order to prevent a virtual interrupt for the virtual processor from causing a VM exit while the virtual processor is in the runnable state. In box 942, the virtual processor may be waiting for the scheduler to activate it on its notify-CPU. In box 944, the next quantum for the virtual processor may arrive. Therefore, in box 946, the VMM may clear the Suppress flag that it set in box 940.
In box 948, the virtual processor may begin to run on processor 120. Therefore, the virtual processor is in an active state and its notify-CPU is processor 120, so in box In box 950, a guest running on the virtual processor may issue an instruction, such as a HLT or MWAIT instruction, to inform the VMM that it is idle, and give up its quantum of time. Therefore, in box 952, the virtual processor may move into a halted state.
In box 954, a notify event for the virtual processor, for example a physical interrupt from box 862 of method 800, may be received by processor 120. In box 956, the VMM begin to service the physical interrupt, using the physical vector to identify the virtual processor for which the notify event was sent. In box 958, the VMM may read the posted-interrupt descriptor for the virtual processor to determine the virtual interrupt request that is pending, according to the pIRR. In box 960, the VMM may inject the virtual interrupt request into the virtual processor for servicing. In box 962, the VMM may clear the Pending flag in the posted-interrupt descriptor. In box 964, the virtual processor may be restarted on physical processor 120.
In box 970, the VMM may desire to migrate the virtual processor from physical processor 120 to physical processor 122 for load balancing or any other reason. Therefore, in box 972, the VMM may cause a VM exit. In box 974, the VMM may begin migrating the virtual processor from physical processor120 to physical processor 122.
In box 976, the VMM may reprogram the notify event attributes in the posted-interrupt descriptor for the virtual processor. For example, the Dest-ID field of the posted-interrupt descriptor may be reprogrammed with the ID of the local APIC for processor 122, and the Physical Vector field may be reprogrammed with the vector to be used by processor 122 to service the physical interrupt used as the posted-interrupt notify event. Therefore, embodiments of the present invention provide for migrating a virtual processor from one physical processor to another without reprogramming all of the virtual processor's IRTEs or other mapping information.
In box 978, the migration of the virtual processor from physical processor 120 to physical processor 122 may end. In box 980, the virtual processor may begin to run on physical processor 122.
In box 998, method 900 ends.
Within the scope of the present invention, methods 800 and 900 may be performed with illustrated boxes omitted, with additional boxes added, or with a combination of reordered, omitted, or additional boxes.
SRC=http://www.freepatentsonline.com/8566492.html
PatentTips - Posting interrupts to virtual processors的更多相关文章
- PatentTips - Interrupt redirection for virtual partitioning
BACKGROUND The present disclosure relates to the handling of interrupts in a environment that utiliz ...
- PatentTips - Safe general purpose virtual machine computing system
BACKGROUND OF THE INVENTION The present invention relates to virtual machine implementations, and in ...
- PatentTips - Use of multiple virtual machine monitors to handle privileged events
BACKGROUND OF THE INVENTION A conventional virtual-machine monitor (VMM) typically runs on a compute ...
- PatentTips - Transparent unification of virtual machines
BACKGROUND Virtualization technology enables a single host computer running a virtual machine monito ...
- Reentrant protected mode kernel using virtual 8086 mode interrupt service routines
A method for allowing a protected mode kernel to service, in virtual 8086 mode, hardware interrupts ...
- PatentTips - Virtualizing performance counters
BACKGROUND Generally, the concept of virtualization in information processing systems allows multipl ...
- Hypervisor, computer system, and virtual processor scheduling method
A hypervisor calculates the total number of processor cycles (the number of processor cycles of one ...
- PatentTips - Enhanced I/O Performance in a Multi-Processor System Via Interrupt Affinity Schemes
BACKGROUND OF THE INVENTION This relates to Input/Output (I/O) performance in a host system having m ...
- [自制操作系统] 原子操作&核间中断&读写锁&PRWLock
本文主要为读论文Scalable Read-mostly Synchronization Using Passive Reader-Writer Locks的记录. 并将其在JOS上实现.其中包括la ...
随机推荐
- POJ 3190 Stall Reservations 【贪心 优先队列】
题意:给出n头牛必须单独占用一台机器的时间段,问至少需要多少台机器 先按照每头牛的时间的x来排序,然后用一个优先队列(优先选取最小的)维护已经喂好的牛的最小的结束时间 比如现在优先队列里面有m头牛已经 ...
- HDU 1505 City Game【DP】
题意:是二维的1506,即在1506的基础上,再加一个for循环,即从第一行到最后一行再扫一遍--- 自己写的时候,输入的方法不对---发现输不出结果,后来看了别人的----@_@发现是将字母和空格当 ...
- thread.h
https://github.com/wookayin/pintos/blob/master/src/threads/thread.h #ifndef THREADS_THREAD_H #defi ...
- 快速傅里叶变换(Fast-Fourier Transform,FFT)
数学定义: (详细参考:https://www.baidu.com/link?url=oYAuG2o-pia_U3DlF5n_MJZyE5YKfaVRUHTTDbM1FwM_kDTjGCxKpw_Pb ...
- ajax请求携带 cookie
之前都有这样一个理解:ajax请求时是不会自动带上cookie的,要是想让他带上的话,必须哟啊设置withCredential为true.这个说法会让人产生完全扭曲的误解,我就是其中之一.完整的无歧义 ...
- Python2x,3x源码的区别,编译型解释型,变量,注释,if,用户交互input,基本数据类型3种
cpu 内存 硬盘 操作系统 cpu: 计算机的运算和计算中心,相当于人类的大脑. 内存:暂时存储数据,临时加载数据应用程序,4G,8G,16G,32G #速度快,造价高,断电即消失 硬盘 ...
- 完毕乔布斯的梦想:一个免费wifi共享的乌托邦
早在2007年推出iPhone时,乔布斯就提出这种如果:商业区与居民区的wifi路由器全民开放,实现与路人共享网络之便.能够想象,那算是一个wifi共享的乌托邦. 数年过去了,乔布斯的梦想依然没能全然 ...
- Unity渲染
我们先大概了解一下对渲染的优先级有影响的几个因素 1.Camera.Depth 不同相机的深度,在渲染顺序的优先度里面是最高的,Depth越大,渲染的图像越靠前 2.Render.SortingOrd ...
- select多选 multiple的使用
select多选 multiple的使用 <html> <head> <script type="text/javascript"> func ...
- oracle新手随记10
1. unpivot注意点:select new_col from (select ename,job,to_char(sal) as sal,null as c from emp) ...
