Ethical Hacking - NETWORK PENETRATION TESTING(2)
ALFA AWUS 1900 RTL8814AU
https://www.alfa.com.tw/products_detail/2.htm

Follow the guide on aircrack-ng/rtl8812au step by step.
https://github.com/aircrack-ng/rtl8812au
Because VMware Workstation has issues, giving kernel oops on module load. I swith to VirtualBOX VM platform.
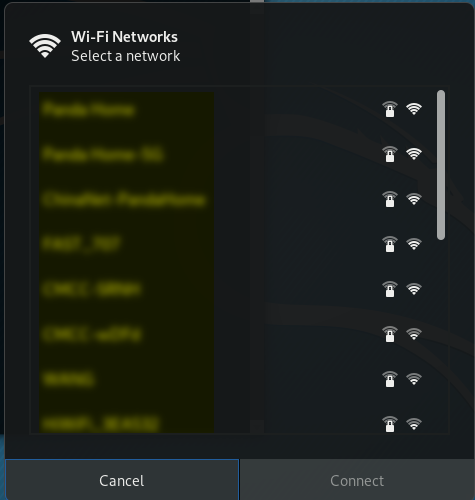
Wahoo!! It works in Kali Linux on VirtualBox VM.
Ethical Hacking - NETWORK PENETRATION TESTING(2)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- CSS中可以继承的元素(需要记住)
可以继承的属性很少,只有颜色,文字,字体间距行高对齐方式,和列表的样式可以继承. 所有元素可继承:visibility和cursor. 内联元素可继承:letter-spacing.word-spac ...
- 添加现有项目到git仓库
情景: 做了一个项目,需要放到git仓库里 为什么做这个记录? 我们一般的操作是先有仓库, 然后 git clone 到一个空文件夹. 然后再这个空文件夹里加项目文件. 再git push ...
- 解除git文件处于lock状态方法
解决办法: 去git文件夹下删除lock文件就可以
- WeChair项目Beta冲刺(2/10)
团队项目进行情况 1.昨日进展 Beta冲刺第二天 昨日进展: 昨天由于组内成员课程繁重,但是大家还是花时间一起开会谈论了开发的一些细节和交流了一些问题 2.今日安排 前端:扫码占座功能和预约功 ...
- python3.6 + django2.0.6 + xadmin0.6
django2.0集成xadmin0.6报错集锦 http://www.lybbn.cn/data/bbsdatas.php?lybbs=50 1.django2.0把from django.core ...
- opencv C++矩阵操作
int main(){ cv::Mat src1=(cv::Mat_<float>(2,3)<<1,2,3,4,5,6); cv::Mat src2=(cv::Mat_< ...
- 计算机网络之tcp/ip协议族
TCP/IP协议族是一个四层协议系统: 1. 数据链路层 1.1 作用 (1) 实现网卡接口的网络驱动,以处理数据在以太网线等物理媒介上的传输 (2) 网络驱动程序隐藏了不同物理网络的不同电气 ...
- Selenium Grid的原理、配置与使用(转)
Selenium GridSelenium Grid在前面介绍Selenium的时候说过它有三大组件,Selenium Grid就是其中之一而作用就是分布式执行测试.讲分布式之前还是要说说UI自动化的 ...
- HDU3686 Traffic Real Time Query【缩点+lca】
题目 City C is really a nightmare of all drivers for its traffic jams. To solve the traffic problem, t ...
- Python之浅谈装饰器
目录 闭包函数 装饰器 迭代器 闭包函数 就是将原先需要调用好几遍的函数和参数写入一个包内,下次调用时一起调用 def name(x): x=1 def age(): print(x) return ...
