CMDB学习之四 ——DEBUG模式
定义一个debug,进行解析调试,到测试文件
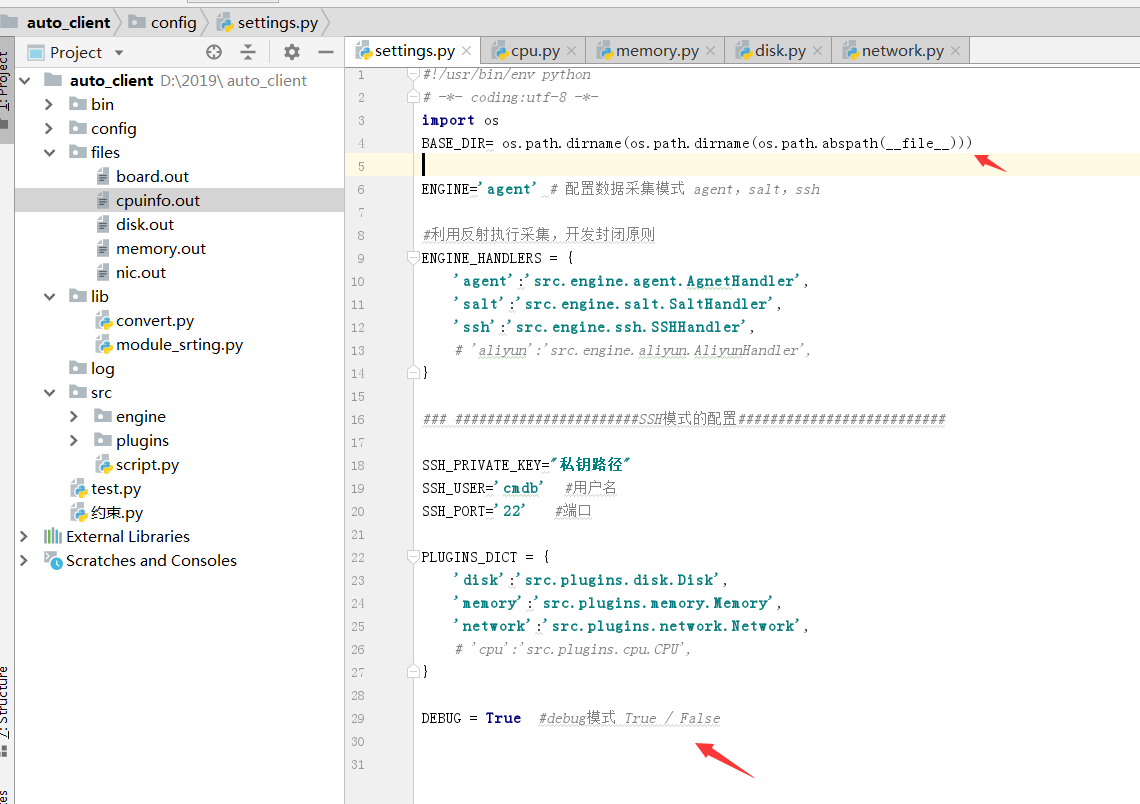
配置文件,配置debug模式,定义环境变量,
#!/usr/bin/env python
# -*- coding:utf-8 -*-
import os
BASE_DIR= os.path.dirname(os.path.dirname(os.path.abspath(__file__))) ENGINE='agent' # 配置数据采集模式 agent,salt,ssh #利用反射执行采集,开发封闭原则
ENGINE_HANDLERS = {
'agent':'src.engine.agent.AgnetHandler',
'salt':'src.engine.salt.SaltHandler',
'ssh':'src.engine.ssh.SSHHandler',
# 'aliyun':'src.engine.aliyun.AliyunHandler',
} ### #######################SSH模式的配置########################## SSH_PRIVATE_KEY="私钥路径"
SSH_USER='cmdb' #用户名
SSH_PORT='' #端口 PLUGINS_DICT = {
'disk':'src.plugins.disk.Disk',
'memory':'src.plugins.memory.Memory',
'network':'src.plugins.network.Network',
# 'cpu':'src.plugins.cpu.CPU',
} DEBUG = True #debug模式 True / False
内存采集解析,内存采集中使用的 convert,导入文件在lib目录下
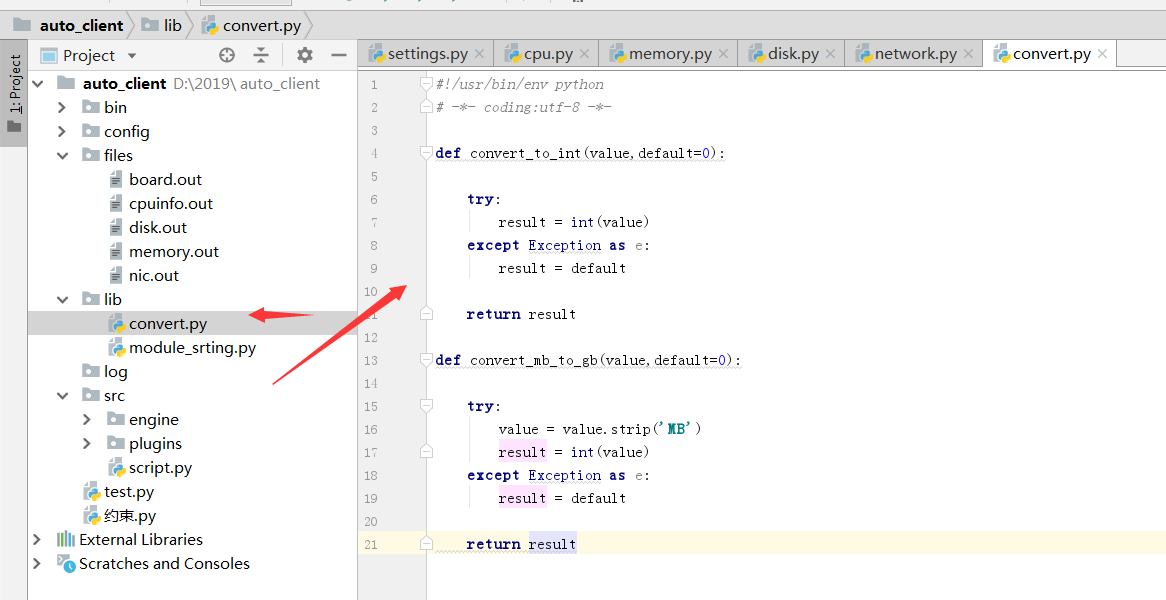
#!/usr/bin/env python
# -*- coding:utf-8 -*- def convert_to_int(value,default=0): try:
result = int(value)
except Exception as e:
result = default return result def convert_mb_to_gb(value,default=0): try:
value = value.strip('MB')
result = int(value)
except Exception as e:
result = default return result
#!/usr/bin/env python
# -*- coding:utf-8 -*-
import os
from .base import BasePlugin
from lib import convert
class Memory(BasePlugin):
def win(self,handler,hostname):
'''
执行命令拿到结果-内存
:return:
'''
print("执行win方法")
ret = handler.cmd('wmic memphysical list brief',hostname)[0:10]
return ret
# def linux(self,handler,hostname):
# '''
# 执行命令拿到结果-内存
# :return:
# '''
# print("执行Linux方法")
# ret = handler.cmd('free',hostname)[0:10]
# return ret
def linux(self, handler, hostname): if self.debug:
output = open(os.path.join(self.base_dir, 'files', 'memory.out'), 'r').read()
else:
shell_command = "sudo dmidecode -q -t 17 2>/dev/null"
output = handler.cmd(shell_command, hostname)
return self.parse(output) def parse(self, content):
"""
解析shell命令返回结果
:param content: shell 命令结果
:return:解析后的结果
"""
ram_dict = {}
key_map = {
'Size': 'capacity',
'Locator': 'slot',
'Type': 'model',
'Speed': 'speed',
'Manufacturer': 'manufacturer',
'Serial Number': 'sn', }
devices = content.split('Memory Device')
for item in devices:
item = item.strip()
if not item:
continue
if item.startswith('#'):
continue
segment = {}
lines = item.split('\n\t')
for line in lines:
if len(line.split(':')) > 1:
key, value = line.split(':')
else:
key = line.split(':')[0]
value = ""
if key in key_map:
if key == 'Size':
segment[key_map['Size']] = convert.convert_mb_to_gb(value, 0)
else:
segment[key_map[key.strip()]] = value.strip()
ram_dict[segment['slot']] = segment return ram_dict
磁盘采集解析
# !/usr/bin/env python
# -*- coding:utf-8 -*-
from .base import BasePlugin
import os,re
class Disk(BasePlugin):
def win(self,handler,hostname):
'''
执行命令拿到结果-磁盘
:return:
'''
print("执行win方法")
ret = handler.cmd('wmic diskdrive',hostname)[0:10]
return ret
# def linux(self,handler,hostname):
# '''
# 执行命令拿到结果-磁盘
# :return:
# '''
# print("执行Linux方法")
#
# ret = handler.cmd('df -h',hostname)[0:10]
# return ret
def linux(self, handler, hostname): if self.debug:
output = open(os.path.join(self.base_dir, 'files', 'disk.out'), 'r').read()
else:
shell_command = "sudo MegaCli -PDList -aALL" #根据执行的命令
output = handler.cmd(shell_command, hostname) return self.parse(output) def parse(self, content):
"""
解析shell命令返回结果
:param content: shell 命令结果
:return:解析后的结果
"""
response = {}
result = []
for row_line in content.split("\n\n\n\n"):
result.append(row_line)
for item in result:
temp_dict = {}
for row in item.split('\n'):
if not row.strip():
continue
if len(row.split(':')) != 2:
continue
key, value = row.split(':')
name = self.mega_patter_match(key)
if name:
if key == 'Raw Size':
raw_size = re.search('(\d+\.\d+)', value.strip())
if raw_size:
temp_dict[name] = raw_size.group()
else:
raw_size = ''
else:
temp_dict[name] = value.strip()
if temp_dict:
response[temp_dict['slot']] = temp_dict
return response @staticmethod
def mega_patter_match(needle):
grep_pattern = {'Slot': 'slot', 'Raw Size': 'capacity', 'Inquiry': 'model', 'PD Type': 'pd_type'}
for key, value in grep_pattern.items():
if needle.startswith(key):
return value
return False
网络采集解析
#!/usr/bin/env python
# -*- coding:utf-8 -*-
import os,re
from .base import BasePlugin
class Network(BasePlugin):
def win(self,handler,hostname):
'''
执行命令拿到结果-网卡
:return:
'''
print("执行win方法")
ret = handler.cmd('ipconfig',hostname)[0:10]
return ret
# def linux(self,handler,hostname):
# '''
# 执行命令拿到结果-网卡
# :return:
# '''
# print("执行Linux方法")
# ret = handler.cmd('ifconfig',hostname)[0:10]
# return ret
def linux(self, handler, hostname):
if self.debug:
output = open(os.path.join(self.base_dir, 'files', 'nic.out'), 'r').read()
interfaces_info = self._interfaces_ip(output)
else:
interfaces_info = self.linux_interfaces(handler)
self.standard(interfaces_info)
return interfaces_info def linux_interfaces(self, handler):
'''
Obtain interface information for *NIX/BSD variants
'''
ifaces = dict()
ip_path = 'ip'
if ip_path:
cmd1 = handler.cmd('sudo {0} link show'.format(ip_path))
cmd2 = handler.cmd('sudo {0} addr show'.format(ip_path))
ifaces = self._interfaces_ip(cmd1 + '\n' + cmd2)
return ifaces def which(self, exe):
def _is_executable_file_or_link(exe):
# check for os.X_OK doesn't suffice because directory may executable
return (os.access(exe, os.X_OK) and
(os.path.isfile(exe) or os.path.islink(exe))) if exe:
if _is_executable_file_or_link(exe):
# executable in cwd or fullpath
return exe # default path based on busybox's default
default_path = '/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin'
search_path = os.environ.get('PATH', default_path)
path_ext = os.environ.get('PATHEXT', '.EXE')
ext_list = path_ext.split(';') search_path = search_path.split(os.pathsep)
if True:
# Add any dirs in the default_path which are not in search_path. If
# there was no PATH variable found in os.environ, then this will be
# a no-op. This ensures that all dirs in the default_path are
# searched, which lets salt.utils.which() work well when invoked by
# salt-call running from cron (which, depending on platform, may
# have a severely limited PATH).
search_path.extend(
[
x for x in default_path.split(os.pathsep)
if x not in search_path
]
)
for path in search_path:
full_path = os.path.join(path, exe)
if _is_executable_file_or_link(full_path):
return full_path return None def _number_of_set_bits_to_ipv4_netmask(self, set_bits): # pylint: disable=C0103
'''
Returns an IPv4 netmask from the integer representation of that mask. Ex. 0xffffff00 -> '255.255.255.0'
'''
return self.cidr_to_ipv4_netmask(self._number_of_set_bits(set_bits)) def cidr_to_ipv4_netmask(self, cidr_bits):
'''
Returns an IPv4 netmask
'''
try:
cidr_bits = int(cidr_bits)
if not 1 <= cidr_bits <= 32:
return ''
except ValueError:
return '' netmask = ''
for idx in range(4):
if idx:
netmask += '.'
if cidr_bits >= 8:
netmask += ''
cidr_bits -= 8
else:
netmask += '{0:d}'.format(256 - (2 ** (8 - cidr_bits)))
cidr_bits = 0
return netmask def _number_of_set_bits(self, x):
'''
Returns the number of bits that are set in a 32bit int
'''
# Taken from http://stackoverflow.com/a/4912729. Many thanks!
x -= (x >> 1) & 0x55555555
x = ((x >> 2) & 0x33333333) + (x & 0x33333333)
x = ((x >> 4) + x) & 0x0f0f0f0f
x += x >> 8
x += x >> 16
return x & 0x0000003f def _interfaces_ip(self, out):
'''
Uses ip to return a dictionary of interfaces with various information about
each (up/down state, ip address, netmask, and hwaddr)
'''
ret = dict()
right_keys = ['name', 'hwaddr', 'up', 'netmask', 'ipaddrs'] def parse_network(value, cols):
'''
Return a tuple of ip, netmask, broadcast
based on the current set of cols
'''
brd = None
if '/' in value: # we have a CIDR in this address
ip, cidr = value.split('/') # pylint: disable=C0103
else:
ip = value # pylint: disable=C0103
cidr = 32 if type_ == 'inet':
mask = self.cidr_to_ipv4_netmask(int(cidr))
if 'brd' in cols:
brd = cols[cols.index('brd') + 1]
return (ip, mask, brd) groups = re.compile('\r?\n\\d').split(out)
for group in groups:
iface = None
data = dict() for line in group.splitlines():
if ' ' not in line:
continue
match = re.match(r'^\d*:\s+([\w.\-]+)(?:@)?([\w.\-]+)?:\s+<(.+)>', line)
if match:
iface, parent, attrs = match.groups()
if 'UP' in attrs.split(','):
data['up'] = True
else:
data['up'] = False
if parent and parent in right_keys:
data[parent] = parent
continue cols = line.split()
if len(cols) >= 2:
type_, value = tuple(cols[0:2]) iflabel = cols[-1:][0]
if type_ in ('inet',):
if 'secondary' not in cols:
ipaddr, netmask, broadcast = parse_network(value, cols)
if type_ == 'inet':
if 'inet' not in data:
data['inet'] = list()
addr_obj = dict()
addr_obj['address'] = ipaddr
addr_obj['netmask'] = netmask
addr_obj['broadcast'] = broadcast
data['inet'].append(addr_obj)
else:
if 'secondary' not in data:
data['secondary'] = list()
ip_, mask, brd = parse_network(value, cols)
data['secondary'].append({
'type': type_,
'address': ip_,
'netmask': mask,
'broadcast': brd,
})
del ip_, mask, brd
elif type_.startswith('link'):
data['hwaddr'] = value
if iface:
if iface.startswith('pan') or iface.startswith('lo') or iface.startswith('v'):
del iface, data
else:
ret[iface] = data
del iface, data
return ret def standard(self, interfaces_info): for key, value in interfaces_info.items():
ipaddrs = set()
netmask = set()
if not 'inet' in value:
value['ipaddrs'] = ''
value['netmask'] = ''
else:
for item in value['inet']:
ipaddrs.add(item['address'])
netmask.add(item['netmask'])
value['ipaddrs'] = '/'.join(ipaddrs)
value['netmask'] = '/'.join(netmask)
del value['inet']
CMDB学习之四 ——DEBUG模式的更多相关文章
- python flask框架学习——开启debug模式
学习自:知了课堂Python Flask框架——全栈开发 1.flask的几种debug模式的方法 # 1.app.run 传参debug=true app.run(debug=True) #2 设置 ...
- 8086汇编语言学习(二) 8086汇编开发环境搭建和Debug模式介绍
1. 8086汇编开发环境搭建 在上篇博客中简单的介绍了8086汇编语言.工欲善其事,必先利其器,在8086汇编语言正式开始学习之前,先介绍一下如何搭建8086汇编的开发环境. 汇编语言设计之初是用于 ...
- 初学node.js,安装nodemon,学习debug模式,安装cpu-stat
1.运行node 文件 node .\01.js 文件内容 console.log('aaaa'); 2.因为每次更新文件都需要重新,所以安装nodemon npm i ...
- flask学习(四):debug模式
一. 设置debug模式 1. flask 1.0之前 在app.run()中传入一个关键字参数debug,app.run(debug=True),就设置当前项目为debug模式 2. flask 1 ...
- odoo Windows10启动debug模式报错(Process finished with exit code -1073740940 (0xC0000374))
之前用win10系统,安装odoo总是启动debug模式启动不起来很恼火. 报错问题:Process finished with exit code -1073740940 (0xC0000374) ...
- Flask debug 模式 PIN 码生成机制安全性研究笔记
Flask debug 模式 PIN 码生成机制安全性研究笔记 0x00 前言 前几天我整理了一个笔记:Flask开启debug模式等于给黑客留了后门,就Flask在生产网络中开启debug模式可能产 ...
- Eclipse Debug模式的开启与关闭问题简析_java - JAVA
文章来源:嗨学网 敏而好学论坛www.piaodoo.com 欢迎大家相互学习 默认情况下,eclipse中右键debug,当运行到设置的断点时会自动跳到debug模式下.但由于我的eclipse环境 ...
- IDea 工具debug模式详细使用说明
IDea 工具debug模式详细使用说明 IDEA中如何使用debug调试项目 一步一步详细教程 Debug用来追踪代码的运行流程,通常在程序运行过程中出现异常,启用Debug模式可以分析定位异常发生 ...
- 手机改 user模式为debug模式
logcat 是Android中一个命令行工具,可用于监控手机应用程序的log信息.网上相关的教学很多,这里只想把自己折腾 2 部手机(一个是三星S4 I9500 港水,Android 5.01,一个 ...
随机推荐
- c3p0-config.xml
<?xml version="1.0" encoding="UTF-8"?> <!DOCTYPE xml> <c3p0-confi ...
- 20180929 北京大学 人工智能实践:Tensorflow笔记06
入戏 需要修改成如下: (完)
- shrio 加密/编码
在涉及到密码存储问题上,应该加密/生成密码摘要存储,而不是存储明文密码.比如之前的600w csdn账号泄露对用户可能造成很大损失,因此应加密/生成不可逆的摘要方式存储. 5.1 编码/解码 Shir ...
- Java读取txt文件和覆盖写入txt文件和追加写入txt
//创建文件 public static void createFile(File filename) { try { if(!filename.exists()) { filename.create ...
- 在performancepoint里面建立数据源的时候,总是发生以下的报警
就是我在performancepoint里面建立数据源的时候,总是发生以下的报警. 在管理中心主页的“应用程序管理”部分,单击“管理服务应用程序”,然后单击“PerformancePoint Se ...
- SELinux 入门
几乎可以肯定每个人都听说过 SELinux (更准确的说,尝试关闭过),甚至某些过往的经验让您对 SELinux 产生了偏见.不过随着日益增长的 0-day 安全漏洞,或许现在是时候去了解下这个在 L ...
- 联想杨天 S4130-12 win10改win7 bios参数设置
一.进入bios 开机后按 F1 二.改bion参数 1.移动到 save& Exit ,修改 OS optimized defaults 为“Disbled” 再 “F9” 保存 2. ...
- GridView单元格取值显示为
在通过GridView取一个单元格(cell)的值时,数据库中为NULL,而页面上显示为空格.发现通过gridview.cell[i].text取出来的值为 ,导致获取数据出现问题. 解决方法: 一. ...
- 【Django】Cookie
目录 Cookie介绍 操作Cookie 获取Cookie 设置 Cookie 删除Cookie @ Cookie介绍 Cookie的由来 大家都知道==HTTP协议是无状态的==. ==无状态的的意 ...
- 本地运行github上的vue2.0仿饿了么webapp项目
在vue刚刚开始流行的时候,大多数人学习大概都见到过这样的一个项目吧,可以作为学习此框架的一个模板了 github源码地址:https://github.com/RegToss/Vue-SPA 课程教 ...
