Fibre Channel address weaknesses
http://searchitchannel.techtarget.com/feature/Fibre-Channel-address-weaknesses

Figure 2.1 Five layers of a Fibre Channel frame.
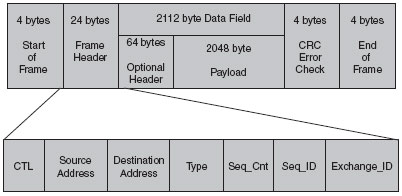
Figure 2.2 shows an example of the header information in Fibre Channel layer 2.



Now that we have established that attacks don't change, but they do get modified, let's discuss another attack that stems network and application history. Manipulation of the 24-bit fabric address can cause significant damage and denial of service in a SAN.
Each node in a SAN has a 24-bit fabric address that is used for routing, among other things. Along with routing frames correctly to/from their source and destinations, the 24-bit address is also used for name server information. The name server is a logical database in each Fibre Channel switch that correlates a node's 24-bit fabric address to their 64-bit WWN. Additionally, the name server is also responsible for other items, such as mapping the 24-bit fabric address and 64-bit WWN to the authorized LUNs in the SAN. Furthermore, address information is also used for soft and hard zoning procedures (discussed in the Chapter 4, "SANs: Zone and Switch Security"). The 24-bit fabric address of a node determines route functions with soft and hard zoning procedures, specifically if a frame is allowed to pass from one zone to the other. While there are several other uses of the 24-bit address, the use of the address in name servers and zoning procedures are by far the most important in terms of security.
The major issues with the 24-bit address is that it is used for identification purposes for both name server information and soft/hard zone routing, almost like an authorization process, but it is an entity that can be easily spoofed. Using any traffic analyzer, the 24-bit source address of a Fibre Channel frame could be spoofed as it performs both PLOGI (Port Login) and FLOGI (Fabric Login) procedures.
In Fibre Channel, there are three different types of login—Port Login, Fabric Login, and Node Login. Two can be corrupted with a spoofed 24-bit fabric address. Before we discuss how spoofing disrupts these processes, let's discuss the login types first.
FABRIC LOGIN (FLOGI), PORT LOGIN (PLOGI), AND NODE LOGIN (NLOGI)
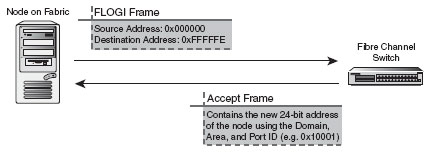
The Fabric Login (FLOGI) process allows a node to log in to the fabric and receive an assigned address from a switch. The FLOGI occurs with any node (N_Port or NL_Port) that is attached to the fabric. The N_Port or NL_Port will carry out the FLOGI with a nearby switch. The node (N_Port or NL_Port) will send a FLOGI frame that contains its node name, its N_Port name, and any service parameters. When the node sends its information to the address of 0xFFFFFE, it uses the 24-bit source address of 0x000000 because it hasn't received a legitimate 24-bit address from the fabric yet. The FLOGI will be sent to the well-known fabric address of 0xFFFFFE, which is similar to the broadcast address in an IP network (though not the same). The FC switches and fabric will receive the FLOGI at the address of 0xFFFFFE. After a switch receives the FLOGI, it will give the N_Port or NL_Port a 24-bit address that pertains to the fabric itself. This 24-bit address with be in the form of Domain-Area-Port address from, where the Domain is the unique domain name (ID) of the fabric, Area is the unique area name (ID) of the switch within the domain, and Port is the unique name (ID) of each port within the switch in the fabric. Table 2.3 shows how the 24-bit address is made.
Table 2.3 24-Bit addresses
24-Bit Address Type
Description
8-bit domain name
Unique domain ID in a fabric. Valid domain IDs are between 1 and 239.
8-bit area name
Unique area ID on a switch within a fabric. Valid area IDs are between 0 and 255.
8-bit port name
Unique area ID on a switch within a fabric. Valid area IDs are between 0 and 255.
A 24-bit address (port ID) uses the following formula to determine a node's address:
An example address for and node on the first domain (domain ID of 1), on the first switch (area ID of 0), and the first port (port ID of 1), would be the following:
After the node has completed the FLOGI and has a valid 24-bit fabric address, it will perform a Port Login (PLOGI) to the well-known address of 0xFFFFFC to register its new 24-bit address with the switch's name server, as well as submit information on its 64-bit port WWN, 64-bit node WWN, port type, and class of service. The switch then registers that 24-bit fabric address, along with all the other information submitted, to the name server and replicates that information to other name servers on the switch fabric. Figures 2.14 and 2.15 show the FLOGI and PLOGI processes.
Figure 2.14 FLOGI process.
Figure 2.15 PLOGI process.
A Node Login is somewhat similar to a Fabric Login, but instead of logging in to the fabric, the node would log in to another node directly (node to node communication). The node will not receive any information from the fabric, but will receive information from the other node as it relates to Exchange IDs (OX_ID and RX_ID) and session information (Seq_ID and Seq_CNT). After this information has been exchanged, the two nodes will begin to communicate with each other directly. Domain_ID x 65536 + Area_ID x 256 + Port_ID = 24 bit Address
1 x 65536 + 0 x 256 + 1 = 65537 (Hex: 0x10001)

Fibre Channel address weaknesses的更多相关文章
- Fibre Channel和Fiber Channel
Fibre Channel也就是"网状通道"的意思,简称FC. 由于Fiber和Fibre只有一字之差,所以产生了很多流传的误解. FC只代表Fibre Channel,而不是 ...
- Fiber Channel SAN Storage
http://www.infotechguyz.com/VMware/FiberChannelSANStorage.html Using Fibre Channel with ESX/ESXi Fib ...
- Firbe Channel光纤信道
简介 中文名:网状信道 外文名:Fibre Channel 简 称:FC 光纤信道是一种高速网络技术标准(T11),主要应用于SAN(存储局域网).其拓扑结构分为三种,点到点.仲裁循环.交换结构 ...
- EtherType
EtherType is a two-octet field in an Ethernet frame. It is used to indicate which protocol is encaps ...
- ibm v3700
raid5总容量计算(n-1)*最小盘容量RAID0:N块盘组成,逻辑容量为N块盘容量之和:RAID1:两块盘组成,逻辑容量为一块盘容量:RAID3:N+1块盘组成,逻辑容量为N块盘容量之和:RAID ...
- openstack Icehouse发布
OpenStack 2014.1 (Icehouse) Release Notes General Upgrade Notes Windows packagers should use pbr 0.8 ...
- Linux就这个范儿 第16章 谁都可以从头再来--从头开始编译一套Linux系统 nsswitch.conf配置文件
Linux就这个范儿 第16章 谁都可以从头再来--从头开始编译一套Linux系统 nsswitch.conf配置文件 朋友们,今天我对你们说,在此时此刻,我们虽然遭受种种困难和挫折,我仍然有一个梦 ...
- WebLogic集群案例分析
WebLogic集群案例分析 2012年8月,某证券交易系统(采用Weblogic中间件),由于基金业务火爆,使系统压力太大,后台服务器频繁死机时,这时工程师们紧急调试系统及恢复操作,等完成这些操作花 ...
- Linux下编译内核配置选项简介
Code maturity level options代码成熟度选项 Prompt for development and/or incomplete code/drivers 显示尚在开发中或尚未完 ...
随机推荐
- Javascript 身份证号获得出生日期、获得性别、检查身份证号码
//---------------------------------------------------------- // 功能:根据身份证号获得出生日期 // 参数:身份证号 psidno // ...
- 异步图片下载引擎(升级版——ExecutorService+handler)
[Android分享] 异步图片下载引擎(升级版——ExecutorService+handler) [复制链接] 皮诺 13 主题 5 好友 844 积分 No.4 中级开发者 升级 2 ...
- YAML 语言教程
编程免不了要写配置文件,怎么写配置也是一门学问. YAML 是专门用来写配置文件的语言,非常简洁和强大,远比 JSON 格式方便. 本文介绍 YAML 的语法,以 JS-YAML 的实现为例.你可以去 ...
- Android之找回打包key密码的方法
昨天准备给自己的应用发布一个新版本,在apk打包时,发现之前的用的keystore密码忘了.蛋碎了一地,我把我所能想到的密码都试了一遍(注:我平常在各个门户网站注册基本上用的都是那几个字母和数字组合做 ...
- [wxWidgets]_[0基础]_[不常见但有用的类wxStandardPaths]
场景: 1.wxStandardPaths 用来获取各种系统路径.能够用于存放app的配置数据.比方文档文件夹,appData等. 代码: #include "wx/wxprec.h&q ...
- COUNT DISTINCT ROW_NUMBER DENSE_RANK 以及对COUNT去重(非PARTITION)
1:COUNT DISTINCT SELECT COUNT(DISTINCT [QS_QuestionStem].Id) AS ReqCount1, ...
- C# 获取文件的MIME类型
在C#中获取文件的MIME类型(Content Type)的方法如下 一.使用MimeMapping类 在System.Web程序集中,当前为静态类,就一个获取 // // 摘要: // 映射文档扩展 ...
- HTTPS安全证书介绍
IIS配置web SSL 安全证书Https访问 From : http://cao416451347ming.blog.163.com/blog/static/1154556162010217441 ...
- 相声段子:How Are You
/**************************************************************** File name : HowAreYou Author : 叶飞影 ...
- 中文分词库及NLP介绍,jieba,gensim的一些介绍
六款中文分词软件介绍: https://blog.csdn.net/u010883226/article/details/80731583 里面有jieba, pyltp什么的.另外下面这个博客有不少 ...
