Lab 1-3
Lab 1-3
Analyze the file Lab01-03.exe.
Questions and Short Answers
Upload the Lab01-03.exe file to http://www.VirusTotal.com/. Does it match any existing antivirus definitions?
A: As of this writing, 25 of 43 virus engines identify this sample as malware.
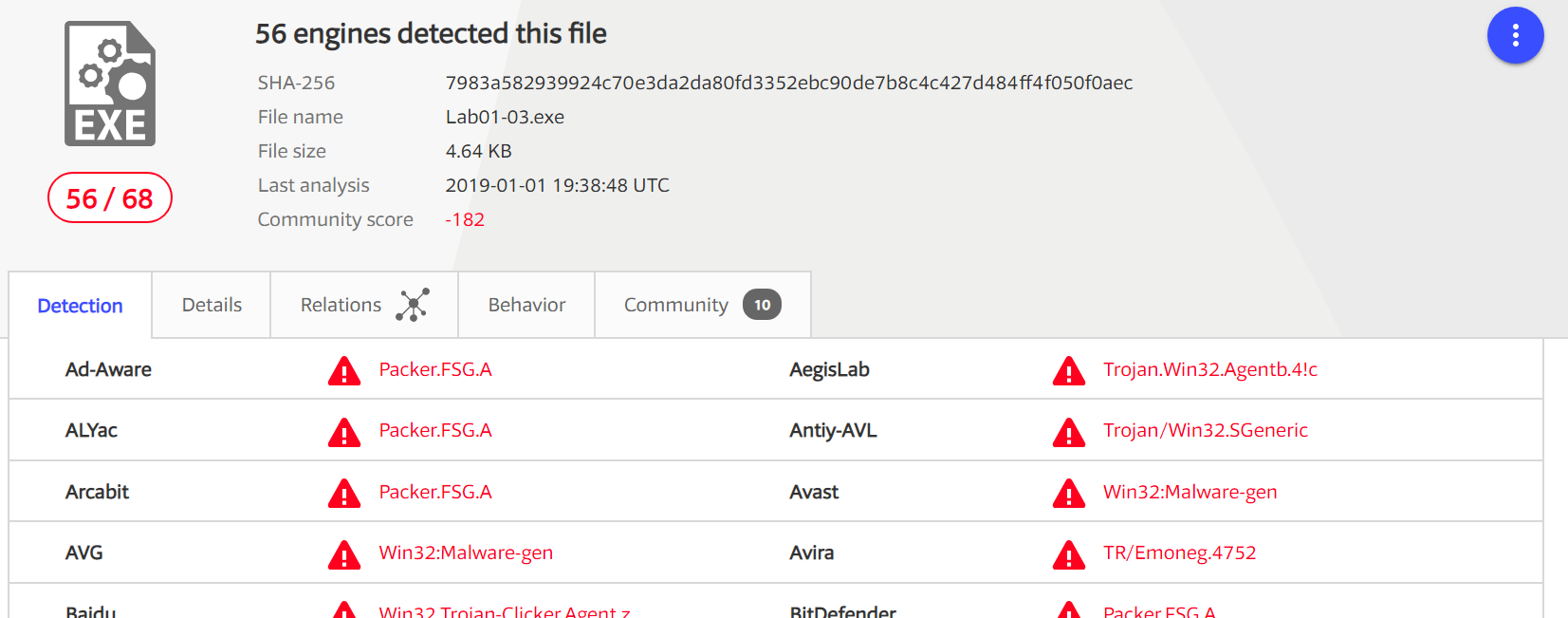
注:在写这篇博客时的数据是 68 反病毒引擎里面 56 个是反病毒签名。
Are there any indications that this file is packed or obfuscated? If so, what are these indicators? If the file is packed, unpack it if possible.
A: The file is packed, but we can’t unpack it at this time.
Do any imports hint at this program’s functionality? If so, which imports are they and what do they tell you?
A: This question can’t be answered without unpacking the file.
What host- or network-based indicators could be used to identify this malware on infected machines?
A: This question can’t be answered without unpacking the file.
Detailed Analysis
For the file Lab01-03.exe, VirusTotal.com reports a variety of different signatures with vague-sounding names. The most common signature is that of a file packed with the FSG packer.
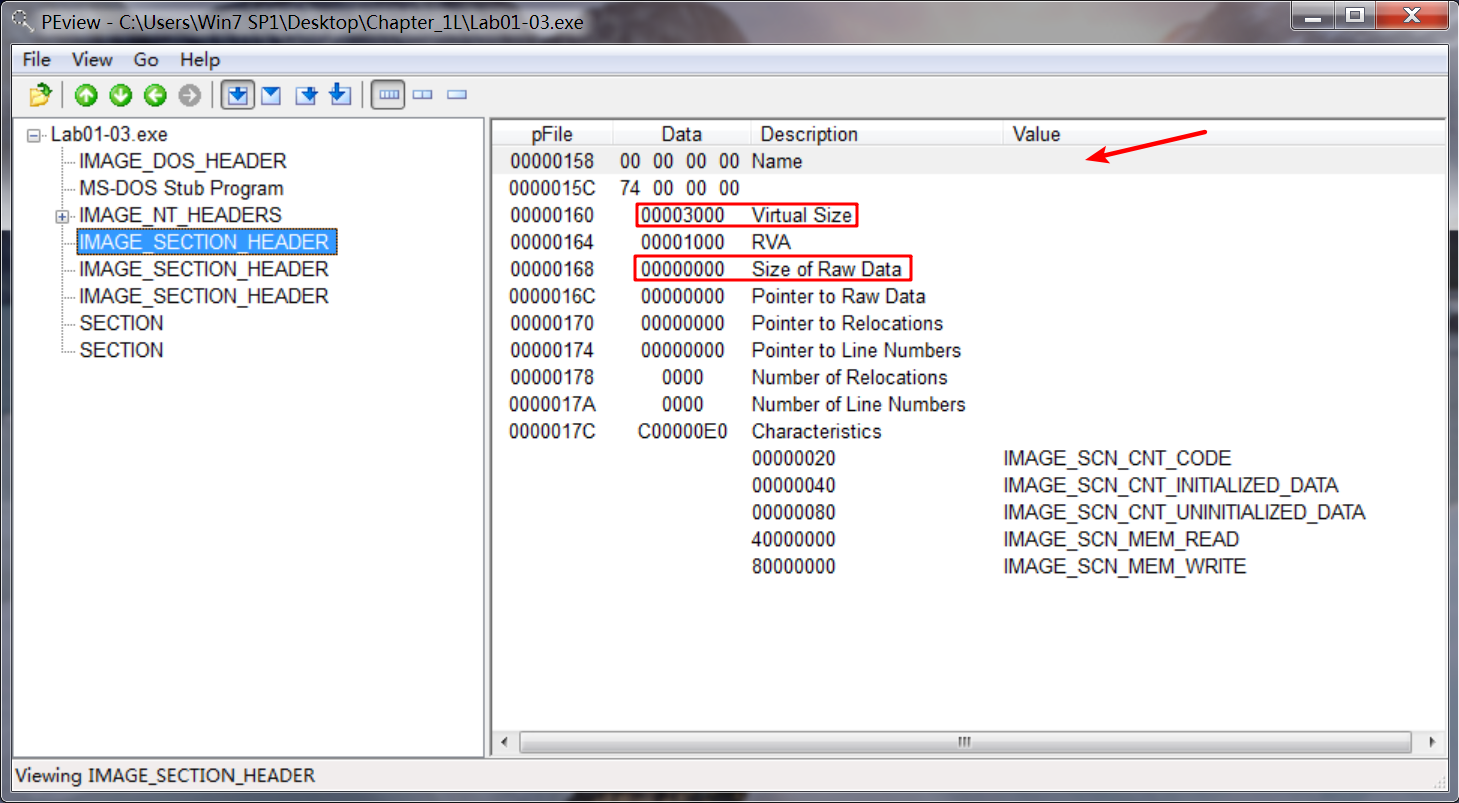
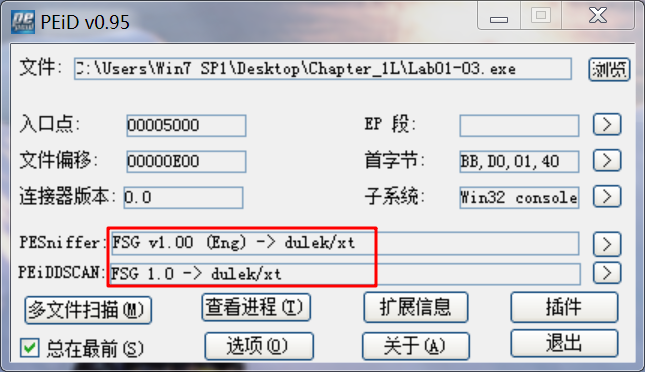
When we open the file in PEview, we see several indications that the file is packed. The first is that the file sections have no names. Next, we see that the first section has a virtual size of 0x3000, but a raw data size of 0. We run PEiD to confirm, and it identifies the packer as FSG 1.0 -> dulek/xt.
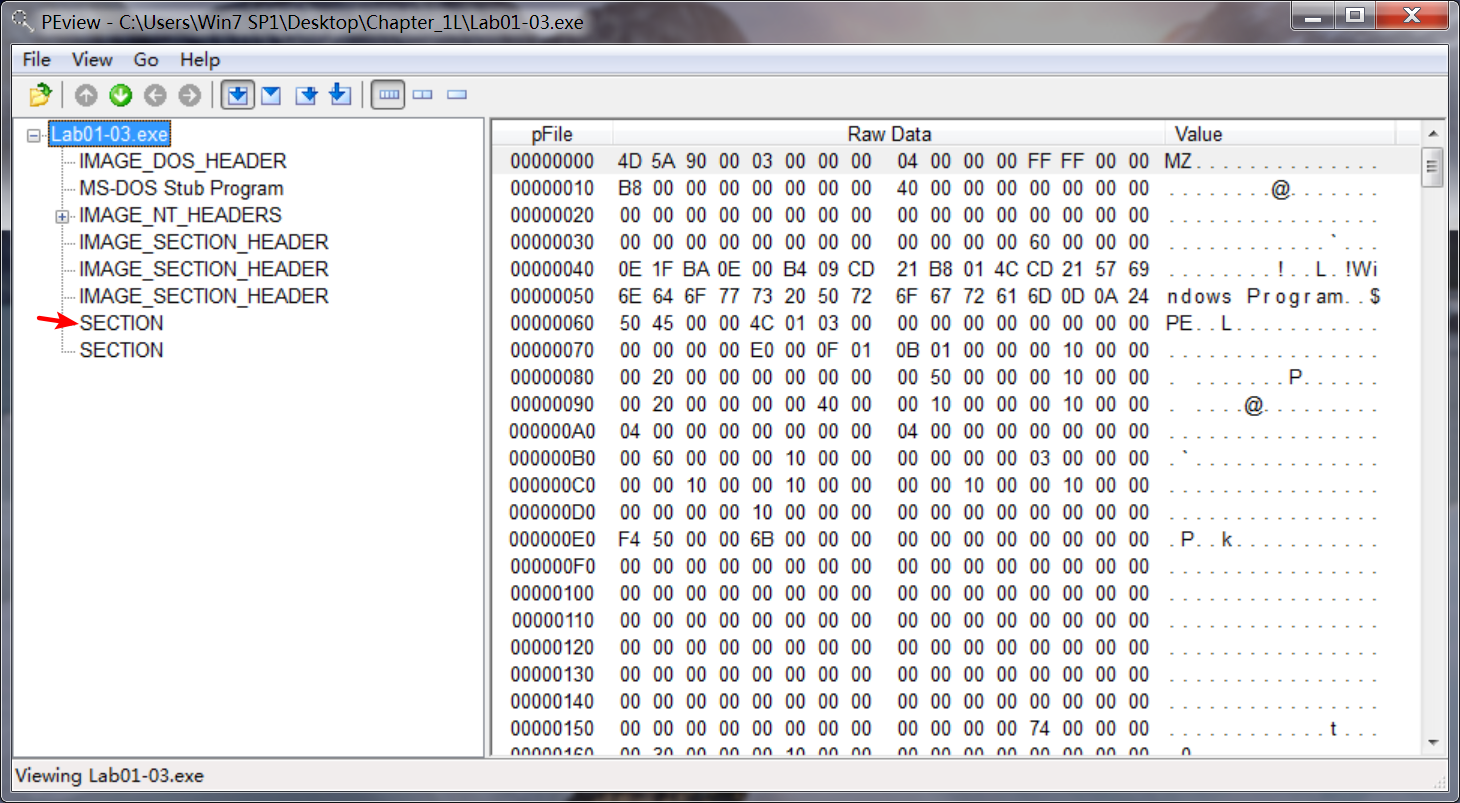
To confirm that the file is packed, we search for the imports, but there doesn’t seem to be an import table. An executable file without an import table is extremely rare, and its absence tells us that we should try another tool, because PEview is having trouble processing this file.
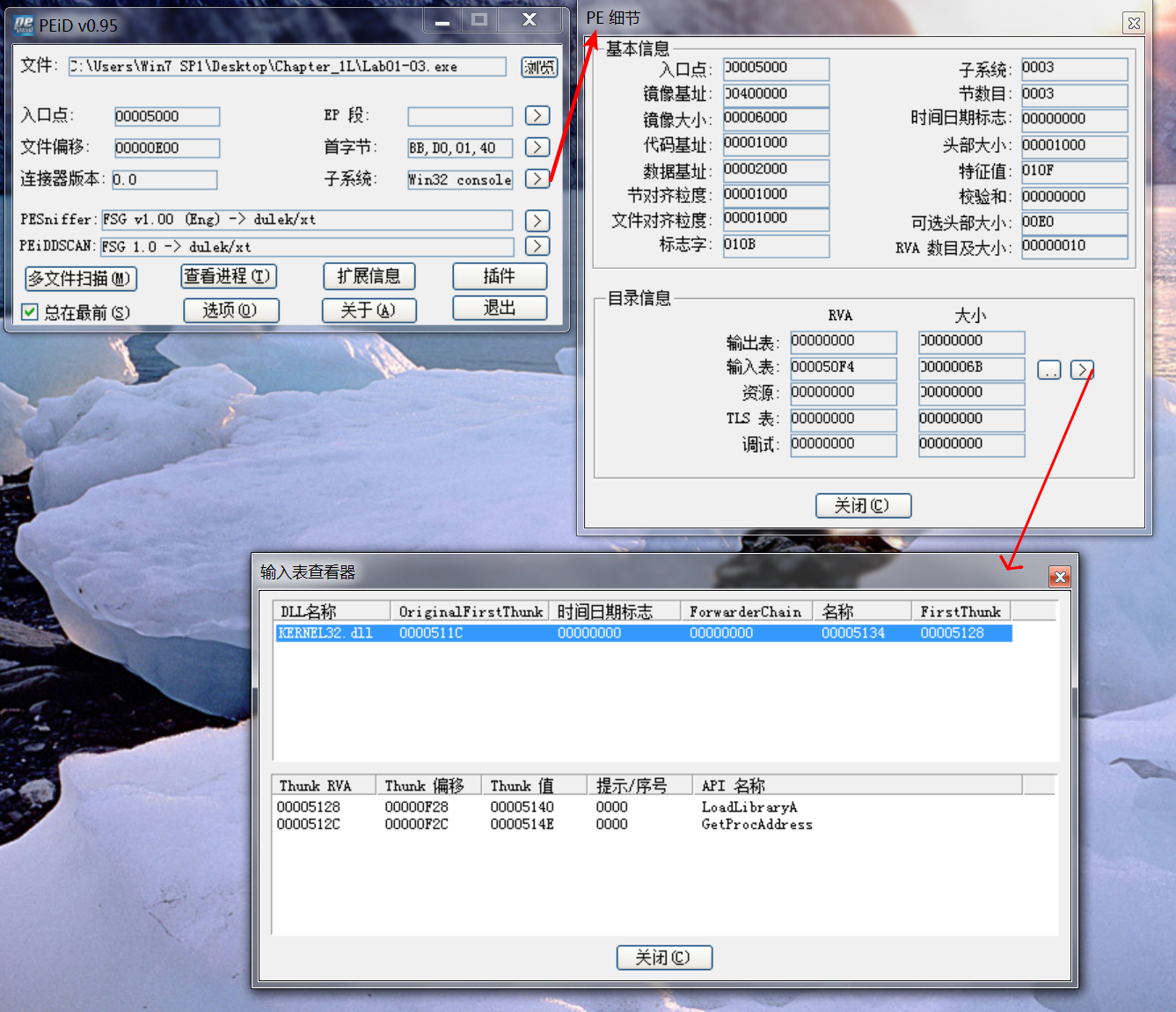
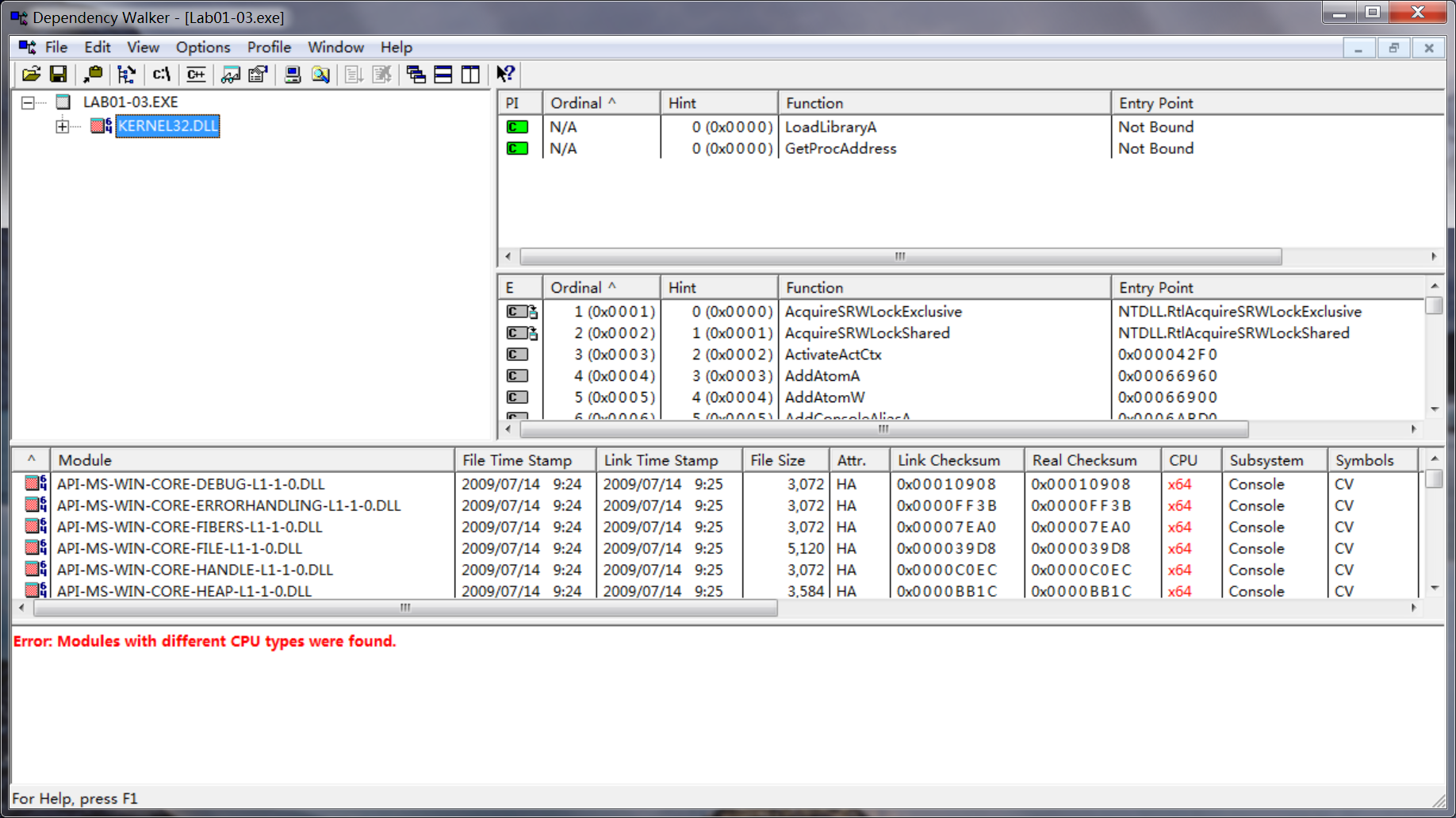
We open the file with Dependency Walker, and see that it does have an import table, but it imports only two functions: LoadLibrary and GetProcAddress. Packed files often import only these two functions, which further indicate that this file is packed. We can try to unpack the file using UPX, but we know that the file is packed with FSG, rather than UPX. We’ll return to this file in Chapter 18, once we have covered the skills to unpack it.
Preference
Lab 1-3的更多相关文章
- MIT 6.828 JOS学习笔记18. Lab 3.2 Part B: Page Faults, Breakpoints Exceptions, and System Calls
现在你的操作系统内核已经具备一定的异常处理能力了,在这部分实验中,我们将会进一步完善它,使它能够处理不同类型的中断/异常. Handling Page Fault 缺页中断是一个非常重要的中断,因为我 ...
- MIT 6.828 JOS学习笔记17. Lab 3.1 Part A User Environments
Introduction 在这个实验中,我们将实现操作系统的一些基本功能,来实现用户环境下的进程的正常运行.你将会加强JOS内核的功能,为它增添一些重要的数据结构,用来记录用户进程环境的一些信息:创建 ...
- MIT 6.828 JOS学习笔记16. Lab 2.2
Part 3 Kernel Address Space JOS把32位线性地址虚拟空间划分成两个部分.其中用户环境(进程运行环境)通常占据低地址的那部分,叫用户地址空间.而操作系统内核总是占据高地址的 ...
- MIT 6.828 JOS学习笔记15. Lab 2.1
Lab 2: Memory Management lab2中多出来的几个文件: inc/memlayout.h kern/pmap.c kern/pmap.h kern/kclock.h kern/k ...
- MIT 6.828 JOS学习笔记10. Lab 1 Part 3: The kernel
Lab 1 Part 3: The kernel 现在我们将开始具体讨论一下JOS内核了.就像boot loader一样,内核开始的时候也是一些汇编语句,用于设置一些东西,来保证C语言的程序能够正确的 ...
- MIT 6.828 JOS学习笔记7. Lab 1 Part 2.2: The Boot Loader
Lab 1 Part 2 The Boot Loader Loading the Kernel 我们现在可以进一步的讨论一下boot loader中的C语言的部分,即boot/main.c.但是在我们 ...
- python opencv 利用Lab空间把春天的场景改为秋天
前一段时间实现了Reinhard颜色迁移算法,感觉挺有意思的,然后在代码上随意做了一些更改,有了一些发现,把Lab通道的a通道值改为127左右,可以将绿色改为黄色,而对其他颜色的改动非常小,因此可以将 ...
- Acadia Lab 228 + Lab 222
又是一对串烧实验,布好线后非常方便就可以一起完成. 连线方案一模一样: Lab 228 数码管骰子 核心代码如下: def loop() : global cnt global btn_read,se ...
- Acadia Lab 203 + Lab 231
在做完 Lab 6 之后,惊觉选做实验缺口很大,于是遍历了一遍夏任务,找到了一条最省力的路线. 做完 Lab 6 的连线不用拆,可以接下来做以下两个实验: Lab 203 网络时钟 核心代码如下: v ...
- GJM : 【技术干货】给The Lab Renderer for Unity中地形添加阴影
感谢您的阅读.喜欢的.有用的就请大哥大嫂们高抬贵手"推荐一下"吧!你的精神支持是博主强大的写作动力以及转载收藏动力.欢迎转载! 版权声明:本文原创发表于 [请点击连接前往] ,未经 ...
随机推荐
- QT5下的caffe项目属性
TEMPLATE = app CONFIG += console c++11 CONFIG -= app_bundle CONFIG -= qt SOURCES += /home/aimhabo/ca ...
- 【python011--数组2】
一.从列表中获取元素 *跟数组一样,我们可以通过元素的索引值(index)从列表获取单个元素,注意,列表索引值是从0开始的 >>> member= ['尘封','冰点','无名',' ...
- topcoder srm 680 div1
problem1 link 将限制按照$x$排序.那么$[upTo_{i}+1,upTo_{i+1}]$中数字个数为$quantity_{i+1}-quantity_{i}$.然后进行动态规划.$f[ ...
- Java TreeSet的定制排序
注:只贴出实现类 package Test3; import java.util.Comparator;import java.util.TreeSet; public class Test { pu ...
- RabbitMQ 入门指南——初步使用
MQ的消息持久化 https://www.rabbitmq.com/tutorials/tutorial-two-java.html When RabbitMQ quits or crashes it ...
- C# 给类做事件的一般做法
https://docs.microsoft.com/zh-cn/dotnet/standard/events/how-to-raise-and-consume-events 第一个示例演示如何引发和 ...
- LightOJ 1030 Discovering Gold(概率DP)题解
题意:1~n每格都有金子,每次掷骰子,掷到多少走几步,拿走那格的金子,问你金子的期望 思路:dp[i]表示从i走到n金子的期望,因为每次最多走1<=x<=6步,所以dp[i] = a[i] ...
- 【NOI 2009】诗人小G
Problem Description 小 \(G\) 是一个出色的诗人,经常作诗自娱自乐.但是,他一直被一件事情所困扰,那就是诗的排版问题. 一首诗包含了若干个句子,对于一些连续的短句,可以将它们用 ...
- linux golang
wget -c http://www.golangtc.com/static/go/go1.3.linux-386.tar.gz #下载32位Linux的够源码包 tar -zxvf go1.1.li ...
- 主键非自增列 EF 插入数据库引起的 ID 列不能为 NULL 的错误
protected override void OnModelCreating(DbModelBuilder modelBuilder) { modelBuilder.Entity<PostBo ...
