Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX
- For best results package the program from the same OS as the target.
- EG if the target is Windows then package the program from a Windows computer with a python interpreter.
- Install Windows python interpreter on Linux.
- Use it to convert python programs to Windows executables.
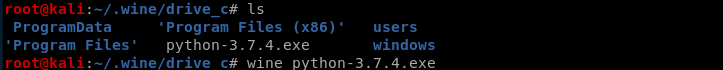
Install wine tool on Kali Linux:
dpkg --add-architecture i386 && apt-get update &&
apt-get install wine32
Install Python 3.7.4 using wine.
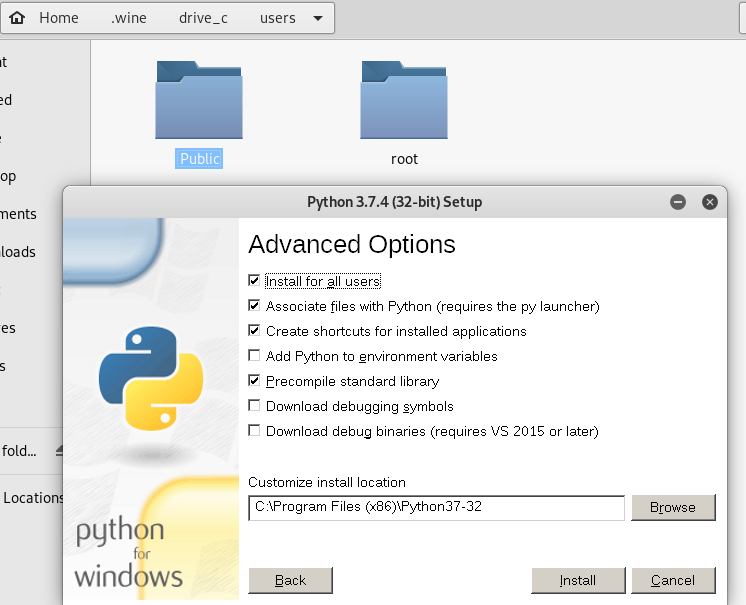
Install PyInstaller on Kali Linux.
wine python.exe -m pip install /root/Downloads/PyInstaller-3.5.tar.gz

To package the keylogger program, we need to install the pynput module first.
wine python.exe -m pip --default-time= install pynput
Convert the python program to windows executable.
wine ~/.wine/drive_c/'Program Files (x86)'/Python37-/Scripts/pyinstaller.exe zkeylogger.py --onefile --noconsole


Test the zkeylogger.exe file on the Windows 10 PC. It works perfectly.

Python Ethical Hacking - Malware Packaging(2)的更多相关文章
- Python Ethical Hacking - Malware Packaging(1)
PACKAGING Convert python program into an executable that: Packages all program files into a single e ...
- Python Ethical Hacking - Malware Packaging(4)
Converting Python Programs to Linux Executables Note: You can not execute the program on Linux by do ...
- Python Ethical Hacking - Malware Packaging(3)
Convert Python Programs to OS X Executables https://files.pythonhosted.org/packages/4a/08/6ca123073a ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE Download files on a system. Once packaged properly will work on all operating systems. ...
- Python Ethical Hacking - Malware Analysis(3)
Stealing WiFi Password Saved on a Computer #!/usr/bin/env python import smtplib import subprocess im ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- Mac App破解之路九 vscode插件破解
破解对象: luaide 破解目的:学习如何破解vscode插件 破解背景: vsscode用了这么多年,安装了很多插件,其中luaide插件是收费的. 说实话,100块并不贵, 我本来准备买的. ...
- 布局之: flex(CSS3新增)
flex 基本概念 flex布局(flex是flexible box的缩写), 也称为弹性盒模型 .将属性和属性值(display:flex; )写在哪个标签样式中,谁就是 容器:它的所有子元素自动成 ...
- vue-drag-resize 可拖拽可缩放的标签,如何管理多个拖拽元素之间的zIndex?操作上需要保持当前激活的组件是最上层,但是在总体上,又要确保其图层管理的顺序。
麻烦总是不断出现,还好办法总比困难多, 1.公司开发一款可视化编辑html网页的多媒体编辑平台,牵扯到标签元素的拖拽,缩放,我找了找方法发现原生技术实现起来代码太多,麻烦,还好找到了一个vue组件,可 ...
- Beta冲刺测试随笔
测试工作安排 人员安排: 余文锦,孙劼成,陈富杰,明锐,王彦杰,陈康杰:测试 杨铭海,张鑫宇测试用例的编写 测试工具选择和运用 本来计划Beta冲刺挑选人员进行测试相关的接触和学习并胜任测试工作,但是 ...
- 代码规范与计划(Beta阶段)
这个作业属于哪个课程 软件工程 (福州大学至诚学院 - 计算机工程系) 团队名称 WeChair 这个作业要求在哪里 Beta冲刺 这个作业的目标 代码规范与计划 作业正文 如下 其他参考文献 代码规 ...
- Hystrix总结
Hystrix 能使你的系统在出现依赖服务失效的时候,通过隔离系统所依赖的服务,防止服务级联失败,同时提供失败回退机制,更优雅地应对失效,并使你的系统能更快地从异常中恢复. Hystrix能做什么? ...
- sklearn机器学习算法--K近邻
K近邻 构建模型只需要保存训练数据集即可.想要对新数据点做出预测,算法会在训练数据集中找到最近的数据点,也就是它的“最近邻”. 1.K近邻分类 #第三步导入K近邻模型并实例化KN对象 from skl ...
- Linux 查看日志的时候常用命令总结
Linux ~ 查看日志的常用命令总结 1.tail -n <行数>,显示文件的尾部n行内容. -f 循环读取,常用于查阅正在改变的日志文件. ① tail -f test.log ...
- Python3-configparser模块-配置文件解析器
Python3中的configparser模块主要用于处理类似于windows ini 文件结构的配置文件 1.configparser模块提供实现基本配置语言的ConfigParser类 2.配置文 ...
- 关于for循环和Iterator遍历ArrayList的性能问题
今日看到@DriveMan的一篇博客,题为<ArrayList集合实现RandomAccess接口有何作用?为何LinkedList集合却没实现这接口?>,文中提到对于实现了RandomA ...
