Traefik-v2.x快速入门
一、概述
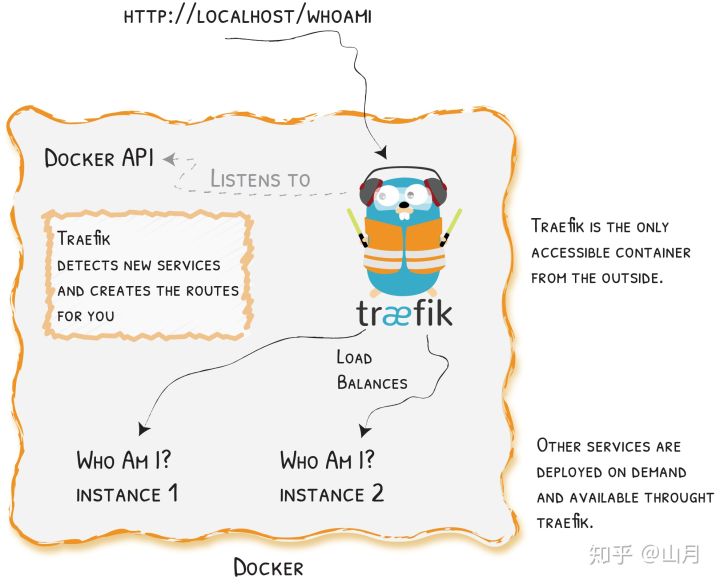
traefik 与 nginx 一样,是一款优秀的反向代理工具,或者叫 Edge Router。至于使用它的原因则基于以下几点
- 无须重启即可更新配置
- 自动的服务发现与负载均衡
- 与
docker的完美集成,基于container label的配置 - 漂亮的
dashboard界面 metrics的支持,对prometheus和k8s的集成
接下来讲一下它的安装,基本功能以及配置。traefik 在 v1 与 v2 版本间差异过大,本篇文章采用了 v2
traefik官方文档:https://docs.traefik.io/
注意:Traefikv2.0之后的版本在修改了很多bug之后也增加了新的特性,比如增加了TCP的支持,并且更换了新的WEB UI界面
二、快速开始
环境介绍
操作系统:centos7.6
数量:1台
docker版本:19.03.6
docker-compose版本:1.24.1
ip地址:192.168.28.218
docker-compose启动
新建yaml文件
vi traefik-v2.1.yaml
内容如下:
version: '3'
services:
reverse-proxy:
image: traefik:2.1.6
# Enables the web UI and tells Traefik to listen to docker
# 启用webUI 并告诉Traefile去监听docker的容器实例
command: --api.insecure=true --providers.docker
ports:
# traefik暴露的http端口
- "80:80"
# webUI暴露的端口(必须制定--api.insecure=true才可以访问)
- "8080:8080"
volumes:
# 指定docker的sock文件来让traefik获取docker的事件,从而实现动态负载均衡
- /var/run/docker.sock:/var/run/docker.sock
使用docker-compose创建集群
# docker-compose -f traefik-v2.1.yaml up -d reverse-proxy
Creating network "opt_default" with the default driver
Creating opt_reverse-proxy_1 ... done
查看使用docker-compose启动的应用
# docker-compose -f traefik-v2.1.yaml ps
Name Command State Ports
---------------------------------------------------------------------------------------------------------
opt_reverse-proxy_1 /entrypoint.sh --api.insec ... Up 0.0.0.0:80->80/tcp, 0.0.0.0:8080->8080/tcp
直接访问traefik对外暴露的http接口
curl -s "http://localhost:8080/api/rawdata" | python -m json.tool
输出如下:


{
"middlewares": {
"dashboard_redirect@internal": {
"redirectRegex": {
"permanent": true,
"regex": "^(http:\\/\\/[^:\\/]+(:\\d+)?)\\/$",
"replacement": "${1}/dashboard/"
},
"status": "enabled",
"usedBy": [
"dashboard@internal"
]
},
"dashboard_stripprefix@internal": {
"status": "enabled",
"stripPrefix": {
"prefixes": [
"/dashboard/",
"/dashboard"
]
},
"usedBy": [
"dashboard@internal"
]
}
},
"routers": {
"api@internal": {
"entryPoints": [
"traefik"
],
"priority": 2147483646,
"rule": "PathPrefix(`/api`)",
"service": "api@internal",
"status": "enabled",
"using": [
"traefik"
]
},
"dashboard@internal": {
"entryPoints": [
"traefik"
],
"middlewares": [
"dashboard_redirect@internal",
"dashboard_stripprefix@internal"
],
"priority": 2147483645,
"rule": "PathPrefix(`/`)",
"service": "dashboard@internal",
"status": "enabled",
"using": [
"traefik"
]
},
"reverse-proxy-opt@docker": {
"rule": "Host(`reverse-proxy-opt`)",
"service": "reverse-proxy-opt",
"status": "enabled",
"using": [
"http",
"traefik"
]
}
},
"services": {
"api@internal": {
"status": "enabled",
"usedBy": [
"api@internal"
]
},
"dashboard@internal": {
"status": "enabled",
"usedBy": [
"dashboard@internal"
]
},
"reverse-proxy-opt@docker": {
"loadBalancer": {
"passHostHeader": true,
"servers": [
{
"url": "http://172.18.0.2:80"
}
]
},
"serverStatus": {
"http://172.18.0.2:80": "UP"
},
"status": "enabled",
"usedBy": [
"reverse-proxy-opt@docker"
]
}
}
}
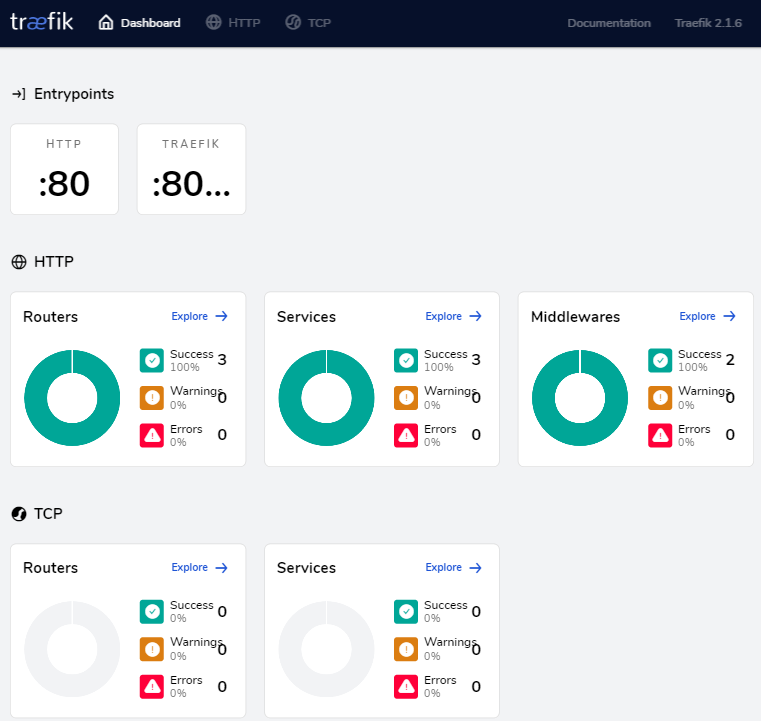
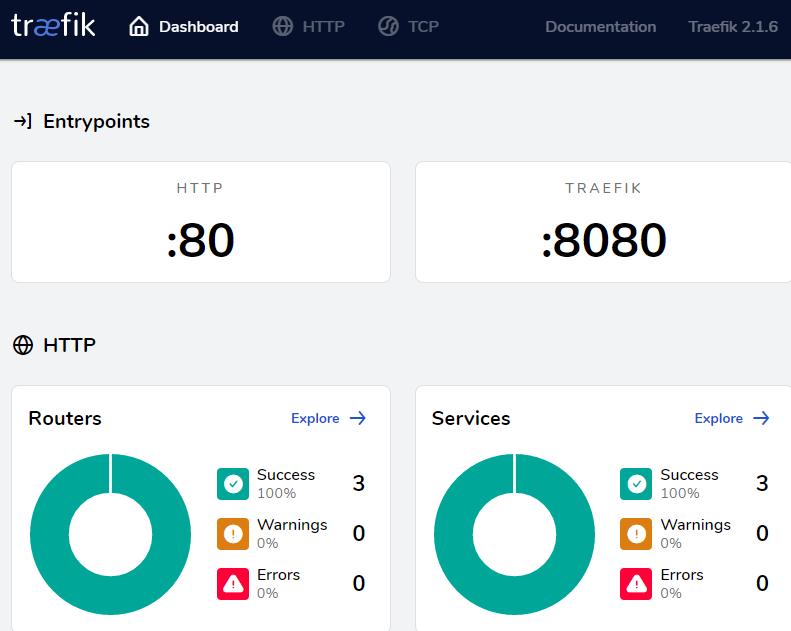
查看Traefik官方Dashboard
http://192.168.28.218:8080/
效果如下:
三、创建一个路由
Traefik来检测新服务并为你创建一个路由
创建一个新服务
vi test-service.yaml
内容如下:
version: '3'
services:
whoami:
image: containous/whoami
labels:
- "traefik.http.routers.whoami.rule=Host(`whoami.docker.localhost`)"
创建服务
# docker-compose -f test-service.yaml up -d whoami
WARNING: Found orphan containers (opt_reverse-proxy_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Creating opt_whoami_1 ... done
查看新创建的服务
# docker-compose -f test-service.yaml ps
Name Command State Ports
---------------------------------------
opt_whoami_1 /whoami Up 80/tcp
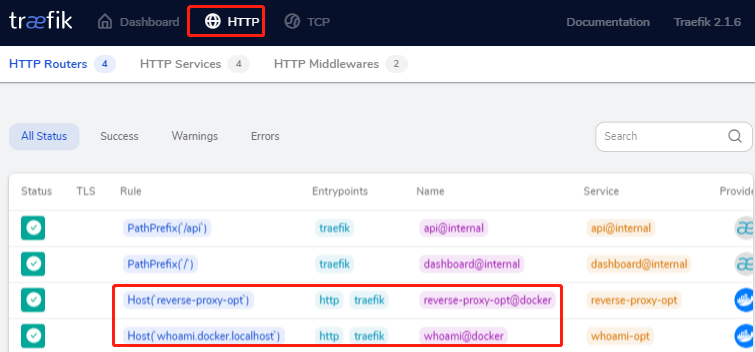
再次查看traefik中的路由信息(就会发现服务自动加载进去了)
其实有点儿类似kong 的路由,只是traefik会自动监听docker的事件
curl -s "http://localhost:8080/api/rawdata" | python -m json.tool
输出如下:


{
"middlewares": {
"dashboard_redirect@internal": {
"redirectRegex": {
"permanent": true,
"regex": "^(http:\\/\\/[^:\\/]+(:\\d+)?)\\/$",
"replacement": "${1}/dashboard/"
},
"status": "enabled",
"usedBy": [
"dashboard@internal"
]
},
"dashboard_stripprefix@internal": {
"status": "enabled",
"stripPrefix": {
"prefixes": [
"/dashboard/",
"/dashboard"
]
},
"usedBy": [
"dashboard@internal"
]
}
},
"routers": {
"api@internal": {
"entryPoints": [
"traefik"
],
"priority": 2147483646,
"rule": "PathPrefix(`/api`)",
"service": "api@internal",
"status": "enabled",
"using": [
"traefik"
]
},
"dashboard@internal": {
"entryPoints": [
"traefik"
],
"middlewares": [
"dashboard_redirect@internal",
"dashboard_stripprefix@internal"
],
"priority": 2147483645,
"rule": "PathPrefix(`/`)",
"service": "dashboard@internal",
"status": "enabled",
"using": [
"traefik"
]
},
"reverse-proxy-opt@docker": {
"rule": "Host(`reverse-proxy-opt`)",
"service": "reverse-proxy-opt",
"status": "enabled",
"using": [
"http",
"traefik"
]
},
"whoami@docker": {
"rule": "Host(`whoami.docker.localhost`)",
"service": "whoami-opt",
"status": "enabled",
"using": [
"http",
"traefik"
]
}
},
"services": {
"api@internal": {
"status": "enabled",
"usedBy": [
"api@internal"
]
},
"dashboard@internal": {
"status": "enabled",
"usedBy": [
"dashboard@internal"
]
},
"reverse-proxy-opt@docker": {
"loadBalancer": {
"passHostHeader": true,
"servers": [
{
"url": "http://172.19.0.2:80"
}
]
},
"serverStatus": {
"http://172.19.0.2:80": "UP"
},
"status": "enabled",
"usedBy": [
"reverse-proxy-opt@docker"
]
},
"whoami-opt@docker": {
"loadBalancer": {
"passHostHeader": true,
"servers": [
{
"url": "http://172.19.0.3:80"
}
]
},
"serverStatus": {
"http://172.19.0.3:80": "UP"
},
"status": "enabled",
"usedBy": [
"whoami@docker"
]
}
}
}
查看http反向代理记录
查看Traefik中的http反向代理记录,点击HTTP
测试traefik相关功能
测试访问
# curl -H Host:whoami.docker.localhost http://localhost
Hostname: c334de4bc3c8
IP: 127.0.0.1
IP: 172.19.0.3
RemoteAddr: 172.19.0.2:57632
GET / HTTP/1.1
Host: whoami.docker.localhost
User-Agent: curl/7.29.0
Accept: */*
Accept-Encoding: gzip
X-Forwarded-For: 172.19.0.1
X-Forwarded-Host: whoami.docker.localhost
X-Forwarded-Port: 80
X-Forwarded-Proto: http
X-Forwarded-Server: 1ee8d25b3aac
X-Real-Ip: 172.19.0.1
单机扩容
# docker-compose -f test-service.yaml up -d --scale whoami=2
WARNING: Found orphan containers (opt_reverse-proxy_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Starting opt_whoami_1 ... done
Creating opt_whoami_2 ... done
再次访问(就会发现自动负载到两个不同的实例上去了)
# curl -H Host:whoami.docker.localhost http://localhost
Hostname: c334de4bc3c8
IP: 127.0.0.1
IP: 172.19.0.3
RemoteAddr: 172.19.0.2:57632
GET / HTTP/1.1
Host: whoami.docker.localhost
User-Agent: curl/7.29.0
Accept: */*
Accept-Encoding: gzip
X-Forwarded-For: 172.19.0.1
X-Forwarded-Host: whoami.docker.localhost
X-Forwarded-Port: 80
X-Forwarded-Proto: http
X-Forwarded-Server: 1ee8d25b3aac
X-Real-Ip: 172.19.0.1
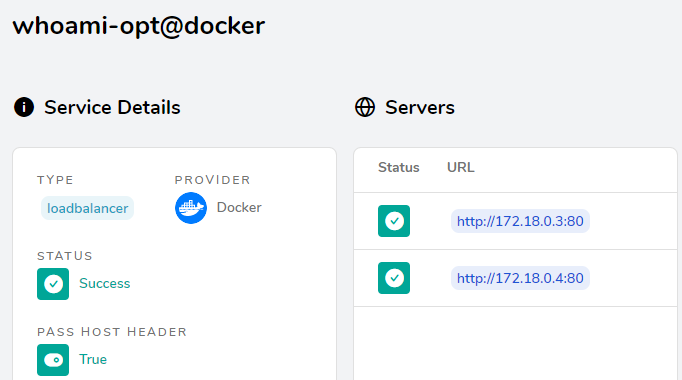
查看Traefike后端每个service的详情信息:
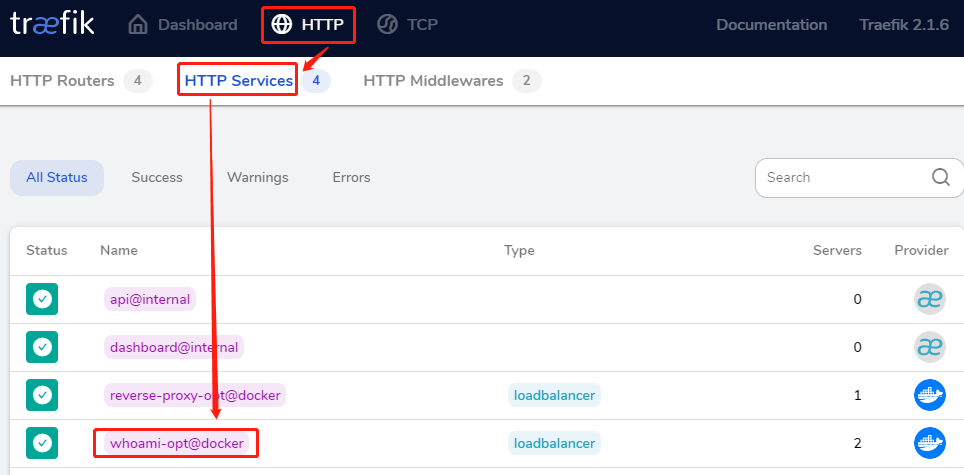
就会看到2个service
四、Traefik配置介绍
traefik配置结构图
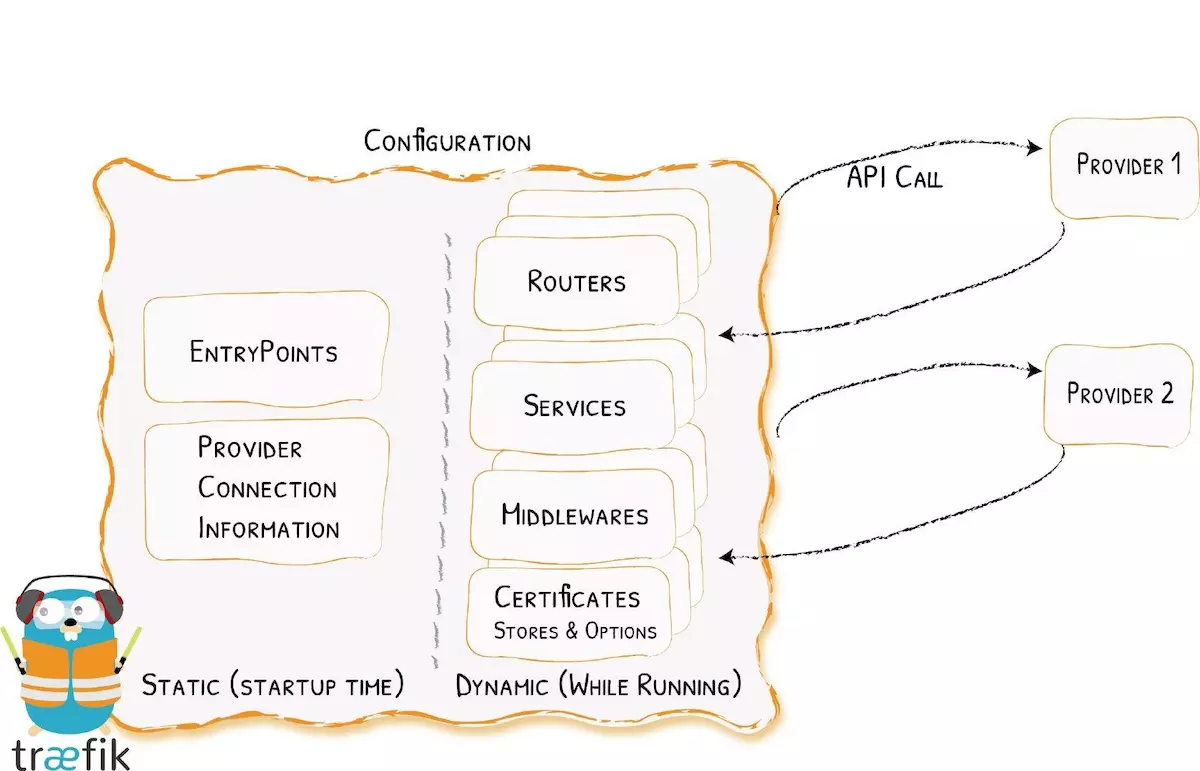
在traefik中的配置,会涉及到两方面内容:
- 动态的路由配置(即由k8s-api或docker相关api来自动发现服务的endpoint而进行路由的配置描述)
- 静态的启动配置(即traefik标准的启动配置参数)
注意:使用docker run traefik[:version] --help可查看traefik的配置参数
五、k8s部署Traefik
环境介绍
| 操作系统 | ip | 主机名 | 配置 | 备注 |
| centos 7.6 | 192.168.31.150 | k8s-master | 2核4G | Kubernetes1.16.3 |
| centos 7.6 | 192.168.31.178 | k8s-node01 | 2核8G | Kubernetes1.16.3 |
yaml文件介绍
mkdir /opt/traefik
目录结构如下:
./
├── traefik-config.yaml
├── traefik-ds-v2.1.6.yaml
├── traefik-rbac.yaml
└── ui.yaml
traefik-config.yaml


apiVersion: v1
kind: ConfigMap
metadata:
name: traefik-config
namespace: kube-system
data:
traefik.toml: |
defaultEntryPoints = ["http","https"]
debug = false
logLevel = "INFO"
# Do not verify backend certificates (use https backends)
InsecureSkipVerify = true
[entryPoints]
[entryPoints.http]
address = ":80"
compress = true
[entryPoints.https]
address = ":443"
[entryPoints.https.tls]
#Config to redirect http to https
#[entryPoints]
# [entryPoints.http]
# address = ":80"
# compress = true
# [entryPoints.http.redirect]
# entryPoint = "https"
# [entryPoints.https]
# address = ":443"
# [entryPoints.https.tls]
[web]
address = ":8080"
[kubernetes]
[metrics]
[metrics.prometheus]
buckets=[0.1,0.3,1.2,5.0]
entryPoint = "traefik"
[ping]
entryPoint = "http"
traefik-ds-v2.1.6.yaml


---
apiVersion: v1
kind: ServiceAccount
metadata:
name: traefik-ingress-controller
namespace: kube-system
---
kind: DaemonSet
apiVersion: apps/v1
#apiVersion: extensions/v1beta1
metadata:
name: traefik-ingress-controller-v2
namespace: kube-system
labels:
k8s-app: traefik-ingress-lb
spec:
selector:
matchLabels:
name: traefik-ingress-lb-v2
template:
metadata:
labels:
k8s-app: traefik-ingress-lb
name: traefik-ingress-lb-v2
spec:
serviceAccountName: traefik-ingress-controller
terminationGracePeriodSeconds: 60
containers:
- image: traefik:2.1.6
name: traefik-ingress-lb-v2
ports:
- name: http
containerPort: 80
hostPort: 80
- name: admin
containerPort: 8080
hostPort: 8080
securityContext:
capabilities:
drop:
- ALL
add:
- NET_BIND_SERVICE
args:
- --api
- --api.insecure=true
- --providers.kubernetesingress=true
- --log.level=INFO
#- --configfile=/config/traefik.toml
#volumeMounts:
#- mountPath: /config
# name: config
volumes:
- configMap:
name: traefik-config
name: config
---
kind: Service
apiVersion: v1
metadata:
name: traefik-ingress-service-v2
namespace: kube-system
labels:
k8s-app: traefik-ingress-lb-v2
spec:
selector:
k8s-app: traefik-ingress-lb-v2
ports:
- protocol: TCP
port: 80
name: web
- protocol: TCP
port: 8080
name: admin
traefik-rbac.yaml


---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: traefik-ingress-controller
rules:
- apiGroups:
- ""
resources:
- services
- endpoints
- secrets
verbs:
- get
- list
- watch
- apiGroups:
- extensions
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- extensions
resources:
- ingresses/status
verbs:
- update
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1beta1
metadata:
name: traefik-ingress-controller
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: traefik-ingress-controller
subjects:
- kind: ServiceAccount
name: traefik-ingress-controller
namespace: kube-system
ui.yaml


---
apiVersion: v1
kind: Service
metadata:
name: traefik-web-ui
namespace: kube-system
spec:
selector:
k8s-app: traefik-ingress-lb
ports:
- name: web
port: 80
targetPort: 8080
---
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: traefik-web-ui
namespace: kube-system
spec:
rules:
- host: prod-traefik-ui.bgbiao.cn
http:
paths:
- path: /
backend:
serviceName: traefik-web-ui
servicePort: web
部署
cd /opt/traefik
kubectl apply -f .
查看pod
# kubectl get pods -n kube-system | grep traefik
traefik-ingress-controller-v2-hz82b 1/1 Running 0 8m4s
查看svc
# kubectl get svc -n kube-system | grep traefik
traefik-ingress-service-v2 ClusterIP 10.1.188.71 <none> 80/TCP,8080/TCP 8m56s
traefik-web-ui ClusterIP 10.1.239.107 <none> 80/TCP 46m
查看ingresses
# kubectl get ingresses.extensions -n kube-system
NAME HOSTS ADDRESS PORTS AGE
traefik-web-ui prod-traefik-ui.bgbiao.cn 80 48m
查看traefik的dashboard
域名访问
由于没有dns服务器,这里直接修改hosts来测试。windows 10添加一条hosts记录
192.168.31.178 prod-traefik-ui.bgbiao.cn
注意:这里的192.168.31.178是node节点ip
效果如下:
ip方式
直接通过node ip+8080方式,比如:
http://192.168.31.178:8080
效果同上!
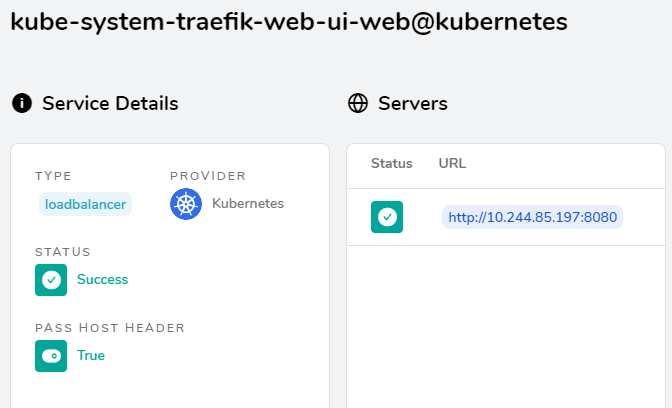
点击http
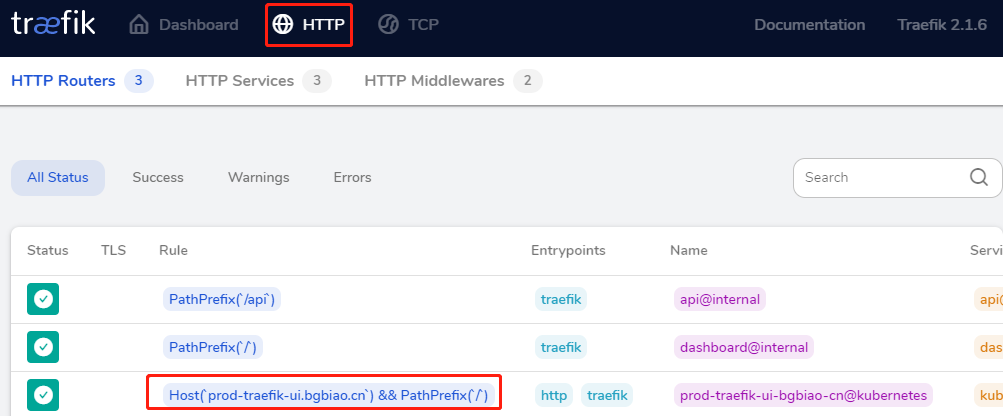
查看 http service
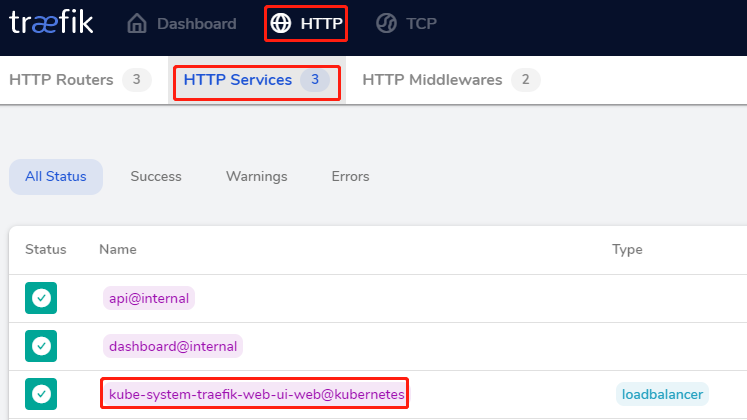
效果如下:
注意:虽然traefikv2.x改动了很多,但是还是向下兼容一些内容的,比如我重新创建traefik-v2.0.1之后,之前创建的ingress规则会自动导入
本文参考链接:
https://www.jianshu.com/p/0fc6df85d00d
https://zhuanlan.zhihu.com/p/97420459
Traefik-v2.x快速入门的更多相关文章
- Docker Compose + Traefik v2 快速安装, 自动申请SSL证书 http转https 初次尝试
前言 昨晚闲得无聊睡不着觉,拿起服务器尝试部署了一下Docker + Traefik v2.1.6 ,以下是一些配置的总结,初次接触,大佬勿喷. 我的系统环境是 Ubuntu 18.04.3 LTS ...
- Kubernetes快速入门
二.Kubernetes快速入门 (1)Kubernetes集群的部署方法及部署要点 (2)部署Kubernetes分布式集群 (3)kubectl使用基础 1.简介 kubectl就是API ser ...
- OpenStack云计算快速入门之二:OpenStack安装与配置
原文:http://blog.chinaunix.net/uid-22414998-id-3265685.html OpenStack云计算----快速入门(2) 该教程基于Ubuntu12.04版, ...
- Nginx快速入门菜鸟笔记
Nginx快速入门-菜鸟笔记 1.编译安装nginx 编译安装nginx 必须先安装pcre库. (1)uname -a 确定环境 Linux localhost.localdomain 2.6. ...
- [Asp.net 开发系列之SignalR篇]专题一:Asp.net SignalR快速入门
一.前言 之前半年时间感觉自己有点浮躁,导致停顿了半年多的时间没有更新博客,今天重新开始记录博文,希望自己可以找回初心,继续沉淀.由于最近做的项目中用到SignalR技术,所以打算总结下Asp.net ...
- quartz-2.2.x 快速入门 (1)
欢迎来到quartz快速入门教程.阅读本教程,你将会了解: quartz下载 quartz安装 根据你的需要,配置Quartz 开始一个示例应用 当熟悉了quratz调度的基本功能后,可以尝试一些 ...
- Toad快速入门
Toad快速入门 在实际中,Toad的用户很少用到其强大的新特性,同时新用户的摸索式熟悉Toad往往花费更多的时间.为此,铸锐数码为每个新购买Toad客户,提供两人次的在线培训服务,帮助客 ...
- JSP内置标签 JSP中JavaBean标签 JSP开发模式 EL和JSTL快速入门
2 JSP内置标签(美化+业务逻辑) 1)为了取代<%%>脚本形式,使用JSP标签/JSP动作,目的:与JSP页面的美化,即JSP面页都是由标签组成,不再有其它的内容 2)JSP内 ...
- Java程序员快速入门Go语言
这篇文章帮助Java程序员快速入门Go语言. 转载至 开源中国社区. http://www.oschina.net 本文将以一个有代表性的例子为开始,以此让Java程序员对Go语言有个初步认识,随后将 ...
- C++ STL快速入门
在数月之前的机试中第一次体验到STL的威力,因为自己本来一直在用C语言做开发,很多数据结构都是自己造的,比如链表.队列等,第一次接触C++ STL后发现这些数据结构都已经给我提供好了,我直接拿去调用就 ...
随机推荐
- [CERC2014]Virus synthesis【回文自动机+DP】
[CERC2014]Virus synthesis 初始有一个空串,利用下面的操作构造给定串 SS . 1.串开头或末尾加一个字符 2.串开头或末尾加一个该串的逆串 求最小化操作数, \(|S| \l ...
- 2020牛客暑期多校训练营(第二场) Boundary
传送门:Boundary 题意:给你n个点的坐标,问最多有多少个点可以在同一个圆上,(0,0)必须在这个圆上. 题解:三个点确定一个圆,所以暴力枚举两个点和(0,0)组成的圆,如果三个点不共线的话, ...
- Codeforces Round #529 (Div. 3) D. Circular Dance (思维)
题意:有\(n\)个熊小孩,绕着树转圈圈,编号\(i\)的小孩可以记住\(a_{i,1}\)和\(a_{i,2}\)两个小孩,这两个小孩是顺时针相邻的,但谁前谁后不一定.现在给你每个小孩的\(a_{i ...
- bfs输出路径 && 最短路(迪杰斯特拉)输出路径
问题描述 解决方法 1.像第一个问题那就是最短路问题(我代码采用迪杰斯特拉算法)实现 2.换乘次数最少,那就用bfs广搜来寻找答案.但是我的代码不能保证这个最少换乘是最短路程 代码 1 #includ ...
- python访问Oracle数据库相关操作
环境: Python版本:3.6.6 win系统:64位 Linux系统:64位 首先安装配置时,版本必须一致!包括:系统版本,python版本,oracle客户端的版本,cx_Oracle的版本! ...
- 流程的python PDF高清版
免费下载链接:https://pan.baidu.com/s/1qcPjLlFXhVXosIGBKHVVXQ 提取码:qfiz
- windows 系统下安装kibana和sense
目前最新版本已经不需要安装sense了,而是使用Dev Tools工具: 下面进行下载和安装kibana. 点击下载:https://artifacts.elastic.co/downloads/ki ...
- Kubernets二进制安装(8)之部署四层反向代理
四层反向代理集群规划 主机名 角色 IP地址 mfyxw10.mfyxw.com 4层负载均衡(主) 192.168.80.10 mfyxw20.mfyxw.com 4层负载均衡(从) 192.168 ...
- Leetcode(38)-报数
报数序列是指一个整数序列,按照其中的整数的顺序进行报数,得到下一个数.其前五项如下: 1. 1 2. 11 3. 21 4. 1211 5. 111221 1 被读作 "one 1&quo ...
- 多线程(二)多线程的基本原理+Synchronized
由一个问题引发的思考 线程的合理使用能够提升程序的处理性能,主要有两个方面, 第一个是能够利用多核 cpu 以及超线程技术来实现线程的并行执行: 第二个是线程的异步化执行相比于同步执行来说,异步执行能 ...
