Shiro官方快速入门10min例子源码解析框架3-Authentication(身份认证)
在作完预备的初始化和session测试后,到了作为一个权鉴别框架的核心功能部分,确认你是谁--身份认证(Authentication)。
通过提交给shiro身份信息来验证是否与储存的安全信息数据是否相符来判断用户身份的真实性
本文涉及到token的构建,框架结构下认证行为的调用,realm中授权数据的获取、登录信息比较,login过程中对已有有subject、session的处理
同样,本篇本文使用的是shiro 1.3.2版本,配合源码最佳~
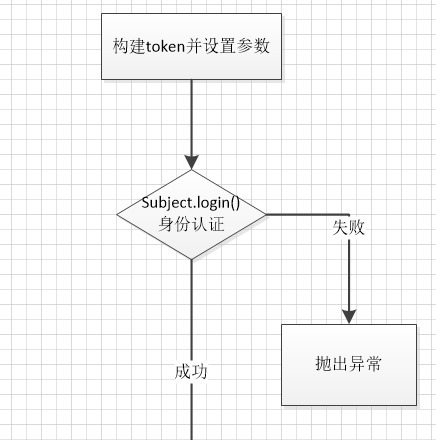
官方例子代码流程如下
if (!currentUser.isAuthenticated()) {
UsernamePasswordToken token = new UsernamePasswordToken("lonestarr", "vespa");
token.setRememberMe(true);
try {
currentUser.login(token);
} catch (UnknownAccountException uae) {
log.info("There is no user with username of " + token.getPrincipal());
} catch (IncorrectCredentialsException ice) {
log.info("Password for account " + token.getPrincipal() + " was incorrect!");
} catch (LockedAccountException lae) {
log.info("The account for username " + token.getPrincipal() + " is locked. " +
"Please contact your administrator to unlock it.");
}
// ... catch more exceptions here (maybe custom ones specific to your application?
catch (AuthenticationException ae) {
//unexpected condition? error?
}
}
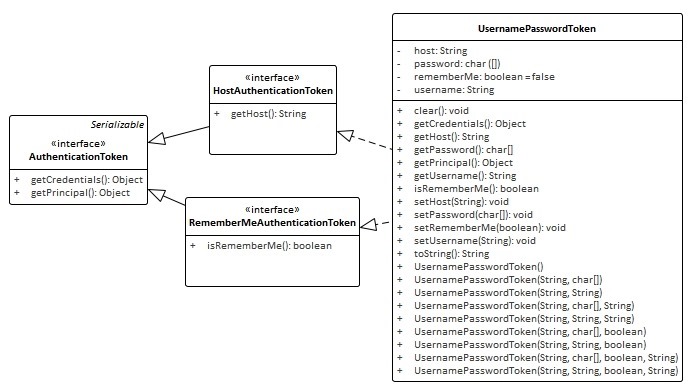
3.1首先构造token,其中 UsernamePasswordToken 实现了HostAuthenticationToken和RememberMeAuthenticationToken接口,他们都继承自AuthenticationToken接口
HostAuthenticationToken接口指定了token的域,RememberMeAuthenticationToken接口指定了token是否实现RememberMe(认证跨session)
ps:shiro 认证状态区分Authenticated和Remembered,Authenticated指当前session(或流程)下已经过认证,Remembered指曾经获得认证,如果是web状态下RememberMe相关信息保存在cookie中
二者可以调用 subject.isAuthenticated() 及subject.isRemembered()区分
其中UsernamePasswordToken 的Principal(身份)概念即Username,Credentials(凭证)概念即Password
在token 中设置用户名和密码
UsernamePasswordToken token = new UsernamePasswordToken("lonestarr", "vespa");
设置是否使用RememberMe(此案例中不具体起作用,只是作为示例在token中设置
token.setRememberMe(true);
案例中不对host进行设置
3.2完成对token的构建设置后,便进行认证(Authentication)操作
currentUser.login(token);
首先先借用官方的例图来了解一下整个的流程
1-调用subject的login入口传入token
2-subject实际调用SecurityManager的login
3-securityManager再调用authenticator实例的doAuthenticate方法,一般这个是ModularRealmAuthenticator的实例
4-判断realm的状况,如果是单realm则直接调用realm,如果是多realm则要判断认证策略(AuthenticationStrategy)
5-调用对应realm中的getAuthenticationInfo实现进行认证

DelegatingSubject.login代码如下,下面对认证流程进行详细的解读
public void login(AuthenticationToken token) throws AuthenticationException {
clearRunAsIdentitiesInternal();
Subject subject = securityManager.login(this, token);
PrincipalCollection principals;
String host = null;
if (subject instanceof DelegatingSubject) {
DelegatingSubject delegating = (DelegatingSubject) subject;
//we have to do this in case there are assumed identities - we don't want to lose the 'real' principals:
principals = delegating.principals;
host = delegating.host;
} else {
principals = subject.getPrincipals();
}
if (principals == null || principals.isEmpty()) {
String msg = "Principals returned from securityManager.login( token ) returned a null or " +
"empty value. This value must be non null and populated with one or more elements.";
throw new IllegalStateException(msg);
}
this.principals = principals;
this.authenticated = true;
if (token instanceof HostAuthenticationToken) {
host = ((HostAuthenticationToken) token).getHost();
}
if (host != null) {
this.host = host;
}
Session session = subject.getSession(false);
if (session != null) {
this.session = decorate(session);
} else {
this.session = null;
}
}
3.2.1首先是初始化
clearRunAsIdentitiesInternal();
如果subject已含session则获取session并清除其中参数
3.2.2调用securityManager中的()login()开始认证
Subject subject = securityManager.login(this, token);
这里调用的是DefaultSecurityManager中的login
public Subject login(Subject subject, AuthenticationToken token) throws AuthenticationException {
AuthenticationInfo info;
try {
info = authenticate(token);//调用AbstractAuthenticator.authenticate,
} catch (AuthenticationException ae) {
try {
onFailedLogin(token, ae, subject);//认证失败,清除remenberMe的信息使之失效
} catch (Exception e) {
if (log.isInfoEnabled()) {
log.info("onFailedLogin method threw an " +
"exception. Logging and propagating original AuthenticationException.", e);
}
}
throw ae; //propagate
}
Subject loggedIn = createSubject(token, info, subject);
onSuccessfulLogin(token, info, loggedIn);
return loggedIn;
}
3.2.2.1
调用AbstractAuthenticator.authenticate(),其中调用ModularRealmAuthenticator.doAuthenticate
protected AuthenticationInfo doAuthenticate(AuthenticationToken authenticationToken) throws AuthenticationException {
assertRealmsConfigured();
Collection<Realm> realms = getRealms();
if (realms.size() == 1) {
return doSingleRealmAuthentication(realms.iterator().next(), authenticationToken);
} else {
return doMultiRealmAuthentication(realms, authenticationToken);
}
}
判断realms可用由于是配置的是单realm
则调用ModularRealmAuthenticator.doSingleRealmAuthentication(),其中调用realm实现判断token类型是否支持,然后执行realm实现中的getAuthenticationInfo方法
protected AuthenticationInfo doSingleRealmAuthentication(Realm realm, AuthenticationToken token) {
if (!realm.supports(token)) {
String msg = "Realm [" + realm + "] does not support authentication token [" +
token + "]. Please ensure that the appropriate Realm implementation is " +
"configured correctly or that the realm accepts AuthenticationTokens of this type.";
throw new UnsupportedTokenException(msg);
}
AuthenticationInfo info = realm.getAuthenticationInfo(token);
if (info == null) {
String msg = "Realm [" + realm + "] was unable to find account data for the " +
"submitted AuthenticationToken [" + token + "].";
throw new UnknownAccountException(msg);
}
return info;
}
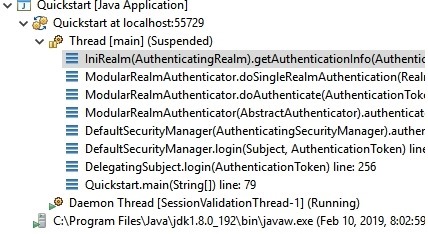
从下图中看出这里的realm是配置后的iniRealm实例,其方法在AuthenticatingRealm中实现,由于inirealm直接在初始化onInit()时就在内存加载了所有授权数据信息,例子并没有使用cache。
public final AuthenticationInfo getAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
AuthenticationInfo info = getCachedAuthenticationInfo(token);
if (info == null) {
//otherwise not cached, perform the lookup:
info = doGetAuthenticationInfo(token);
log.debug("Looked up AuthenticationInfo [{}] from doGetAuthenticationInfo", info);
if (token != null && info != null) {
cacheAuthenticationInfoIfPossible(token, info);
}
} else {
log.debug("Using cached authentication info [{}] to perform credentials matching.", info);
}
if (info != null) {
assertCredentialsMatch(token, info);
} else {
log.debug("No AuthenticationInfo found for submitted AuthenticationToken [{}]. Returning null.", token);
}
return info;
}
3.2.2.1.1调用SimpleAccountRealm.doGetAuthenticationInfo通过用户名从Map users 取出对应的SimpleAccount,并判断是否被锁,是否过期
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
UsernamePasswordToken upToken = (UsernamePasswordToken) token;
SimpleAccount account = getUser(upToken.getUsername());
if (account != null) {
if (account.isLocked()) {
throw new LockedAccountException("Account [" + account + "] is locked.");
}
if (account.isCredentialsExpired()) {
String msg = "The credentials for account [" + account + "] are expired";
throw new ExpiredCredentialsException(msg);
}
}
return account;
}
对应getUser方法使用了读锁保证了map读操作的原子性
protected SimpleAccount getUser(String username) {
USERS_LOCK.readLock().lock();
try {
return this.users.get(username);
} finally {
USERS_LOCK.readLock().unlock();
}
}
3.2.2.1.2调用AuthenticatingRealm.assertCredentialsMatch,获取密码比较器(CredentialsMatcher),其中调用doCredentialsMatch获取对比token和info(上面从realm通过用户名获取的AuthenticationInfo实例)中的密码(核心的一步),并返回结果
public boolean doCredentialsMatch(AuthenticationToken token, AuthenticationInfo info) {
Object tokenCredentials = getCredentials(token);
Object accountCredentials = getCredentials(info);
return equals(tokenCredentials, accountCredentials);
}
3.2.2.2随后通知认证监听器AuthenticationListener(本例未设置)层层返回info至DefaultSecurityManager创建新的有登录信息的subject
Subject loggedIn = createSubject(token, info, subject);
并将现有subject中的信息赋予新的subject
protected Subject createSubject(AuthenticationToken token, AuthenticationInfo info, Subject existing) {
SubjectContext context = createSubjectContext();
context.setAuthenticated(true);
context.setAuthenticationToken(token);
context.setAuthenticationInfo(info);
if (existing != null) {
context.setSubject(existing);
}
return createSubject(context);
}
3.2.2.3设置rememberMe(本例未实现
onSuccessfulLogin(token, info, loggedIn);
3.2.3 继续获取信息principals,host(本例无),设置session到subject,
if (subject instanceof DelegatingSubject) {
DelegatingSubject delegating = (DelegatingSubject) subject;
//we have to do this in case there are assumed identities - we don't want to lose the 'real' principals:
principals = delegating.principals;
host = delegating.host;
} else {
principals = subject.getPrincipals();
}
if (principals == null || principals.isEmpty()) {
String msg = "Principals returned from securityManager.login( token ) returned a null or " +
"empty value. This value must be non null and populated with one or more elements.";
throw new IllegalStateException(msg);
}
this.principals = principals;
this.authenticated = true;
if (token instanceof HostAuthenticationToken) {
host = ((HostAuthenticationToken) token).getHost();
}
if (host != null) {
this.host = host;
}
Session session = subject.getSession(false);
if (session != null) {
this.session = decorate(session);
} else {
this.session = null;
}
3.3完成认证后测试一下Principal(用户名)是否正确
log.info("User [" + currentUser.getPrincipal() + "] logged in successfully.");
可见用户信息正确
至此完成了一个简单的Authentication过程
参考:
http://shiro.apache.org/10-minute-tutorial.html
http://shiro.apache.org/authentication.html
http://www.apache.org/dyn/closer.cgi/shiro/1.3.2/shiro-root-1.3.2-source-release.zip
转载请注明作者及来源:https://www.cnblogs.com/codflow/
Shiro官方快速入门10min例子源码解析框架3-Authentication(身份认证)的更多相关文章
- Shiro官方快速入门10min例子源码解析框架2-Session
Shiro自身维护了一套session管理组件,它可以独立使用,并不单纯依赖WEB/Servlet/EJB容器等环境,使得它的session可以任何应用中使用. 2-Session)主要介绍在quic ...
- Shiro官方快速入门10min例子源码解析框架1-初始化
Shiro,一个易用的Java安全框架,主要集合身份认证.授权.加密和session管理的功能. 这系文章主要简介Shiro架构,并通过官方的quickstart例程分析最简实现下Shiro的工作流程 ...
- Orleans例子源码
这是Orleans系列文章中的一篇.首篇文章在此 我共享以下我现在写教程的简单的Orleans例子源码. 这个代码已经是我为了写word改动过了的.不过大体内容是通用的. 我写博客总体想法是:去除所有 ...
- 【Activiti工作流引擎】官方快速入门demo
Activiti官方快速入门demo 地址: https://www.activiti.org/quick-start 0. 版本 activiti 5.22.0 JDK 1.8 1. 介绍 这个快速 ...
- 分布式 PostgreSQL 集群(Citus),官方快速入门教程
多租户应用程序 在本教程中,我们将使用示例广告分析数据集来演示如何使用 Citus 来支持您的多租户应用程序. 注意 本教程假设您已经安装并运行了 Citus. 如果您没有运行 Citus,则可以使用 ...
- 使用C#类向数据库添加数据的例子源码
在上一篇中,增加了sql server数据库操作类SqlOperator,用于操作sql server数据库.还有一个SqlStringHelper类,用于处理sql语句的单引号.那么这两个类怎么使用 ...
- jackson官方快速入门文档
官方地址: http://jackson.codehaus.org/ http://wiki.fasterxml.com/JacksonInFiveMinutes http://wiki.faster ...
- TodoMVC中的Backbone+MarionetteJS+RequireJS例子源码分析之一
Marionette牵线木偶,Backbone是脊骨的意思,Marionette是基于Backbone做扩展库,可以理解为把脊骨骨架绑线扯着变成牵线木偶动起来哈哈,使backbone更易使用呵呵! 构 ...
- Android例子源码非第三方实现根据字母排序的城市列表
values 下dimens.xml <resources> <!-- Default screen margins, per the Android Design guidelin ...
随机推荐
- html中设置data-*属性值 并在js中进行获取属性值
<!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8&quo ...
- mxonline实战13,授课讲师列表页,详情页,index页面全局导航
对应github地址:第13天 把teacher-list.html和teacher-detail.html拷贝过来 一. 授课讲师列表页 1. 修改html文件 把org-list.ht ...
- 孩子们各显神通对付 iOS 12「屏幕使用时间」的限制
简评:2018 年秋季,苹果公司推出了 iOS 12,其中备受好评的一项改变是:增加了屏幕使用时间限制,以减轻沉迷手机的状况.三个月过去后,这项功能似乎并没有对孩子造成太多困扰,道高一尺魔高一丈,孩子 ...
- 手动抠下的wordpress登录页面样式
CSS文件 login.css body, html { height: 100%; margin: 0; padding: 0; } html[Attributes Style] { -webkit ...
- 腾讯云服务器安装宝塔面板快速配置LNMP/LAMP网站系统
我们在选择购买腾讯云服务器之后,有部分用户肯定是用来建站用途的.毕竟云服务器的性能和功能比虚拟主机优秀很多.腾讯云服务器拥有香港.北京.广州.上海.美国等多个机房,可以安装Linux和Windows系 ...
- Carte上面的作业1、2天就会丢失的问题
发现Carte上面的作业莫名其妙就会没有,问了客户的维护人员说也没删除. 对象时间也是No Limit,但还是隔1.2天就不见了. 那说明之前配置这里还是无效 <slave_config> ...
- dubbo学习笔记:快速搭建
搭建一个简单的dubbo服务 参考地址: dubbo官网:http://dubbo.apache.org/zh-cn/docs/user/references/registry/zookeeper.h ...
- HTML5创业的另一种可能
当一种新的颠覆式技术出现,是投靠大平台还是坚持走独立的道路? HTML5(下称H5)火了.在多数人还没完全弄清楚什么是H5时,它已悄无声息地潜入移动端,并渐呈燎原之势火速席卷云寻觅云寻觅. 以前,H5 ...
- 阿里云CentOS7.4上搭建FTP服务器
1 安装过程 第一步:首先判断是否安装了vsftpd # rpm -qa | grep vsftpd 第二步:如果没有安装则安装vsftpd # yum -y install vsftpd 从第三步开 ...
- css3基础下
box-shadow:0 5px 5px rgba(0,0,0,0.5) 文本 text-shadow:5px 5px 4px green; word-wrap: 背景: background:#ff ...
