Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER
- Discover all devices on the network.
- Display their IP address.
- Display their MAC address.
Write the Python code using the scapy.all module.
Refer to: https://scapy.readthedocs.io/en/latest/installation.html
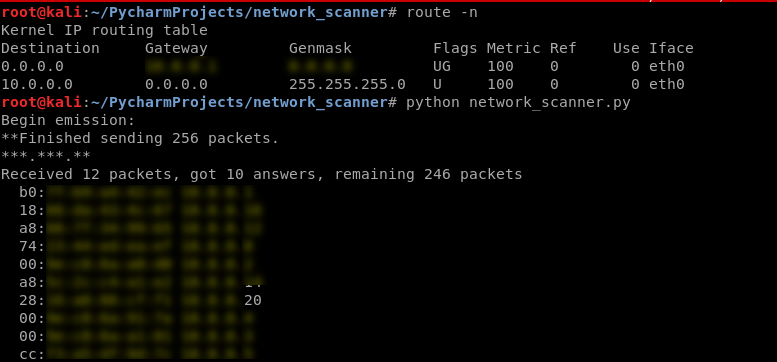
#!/usr/bin/env python import scapy.all as scapy def scan(ip):
scapy.arping(ip) scan("10.0.0.1/24")
ALGORITHM
Goal -> Discover clients on the network.
Steps:
1. Create arp request directed to broadcast MAC asking for IP.
Two main parts:
-> Use ARP to ask who has target IP.
-> Set destination MAC to broadcast MAC.
2. Send packet and receive a response.
3. Parse the response.
4. Print result.
Use the scapy module in this program.
https://scapy.readthedocs.io/en/latest/usage.html
EX: Python Script to discover the clients on the network.
#!/usr/bin/env python import scapy.all as scapy def scan(ip):
arp_request = scapy.ARP(pdst=ip)
broadcast = scapy.Ether(dst="ff:ff:ff:ff:ff:ff")
arp_request_broadcast = broadcast/arp_request
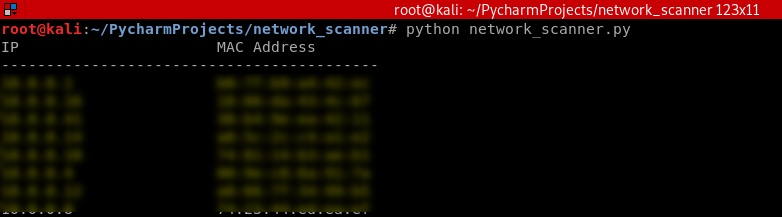
answered_list = scapy.srp(arp_request_broadcast, timeout=1, verbose=False)[0] print("IP\t\t\tMAC Address\n------------------------------------------")
for element in answered_list:
print(element[1].psrc + "\t\t" + element[1].hwsrc) scan("10.0.0.1/24")
Execute the script and show the result.
Python Ethical Hacking - NETWORK_SCANNER(1)的更多相关文章
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM Goal -> Check if MAC address was changed. Steps: 1. Execute and read ifconfig. ...
- Python Ethical Hacking - MAC Address & How to Change(2)
FUNCTIONS Set of instructions to carry out a task. Can take input, and return a result. Make the cod ...
- Python Ethical Hacking - MAC Address & How to Change(1)
MAC ADDRESS Media Access Control Permanent Physical Unique Assigned by manufacturer WHY CHANGE THE M ...
- Python Ethical Hacking - The Lab and Needed Software
The Lab and Needed Software Attacker Machine - Kali Linux https://www.kali.org/ 1. Install the softw ...
- Python Ethical Hacking - Basic Concetion
What is Hacking? Gaining unauthorized access. Hackers? 1.Black-hat Hackers 2.White-hat Hackers 3.Gre ...
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
随机推荐
- Java容器相关知识点整理
结合一些文章阅读源码后整理的Java容器常见知识点.对于一些代码细节,本文不展开来讲,有兴趣可以自行阅读参考文献. 1. 思维导图 各个容器的知识点比较分散,没有在思维导图上体现,因此看上去右半部分很 ...
- ca69a.cpp_c++_函数匹配(重载确定)
/*ca69a.cpp_c++_函数匹配(重载确定)#重载确定的三个步骤1.候选函数2.选择可行函数3.寻找最佳匹配(如果有的话)#含有多个形参的重载确定 void f1();void f1(int) ...
- LeetCode 题解目录
前言 本目录将不断更新记录leetcode的刷题日记. 二叉树 序号 标题 难度 标签 1 108 将有序数组转换为二叉搜索树 简单 树.深度优先搜索 2 538 把二叉搜索树转换为累加树 简单 树 ...
- Redis的常用配置
1. 配置守护线程方式运行,修改damonize,使用yes启用守护线程,这样就可以后台运行了 damonize no 修改为 damonize yes 2. 手动指定redis的pid,可以通过pi ...
- Redis Wendows安装步骤
1.打开cmd命令提示符2.打开cmd如下图,输入Redis下载磁盘名称+“:” ,然后回车 3.如下图:输入"cd" 然后空格,后面是Redis的路径 回车 4.设置服务命令 ...
- 谈谈我对 Flutter 未来发展 和 “嵌套地狱” 的浅显看法
Flutter 未来发展 提到 Flutter 就不得不提到 Fuchsia 系统,这是一个尚未正式发布的操作的系统,引用 Android 和 Chrome 的高级副总裁 Hiroshi Lockhe ...
- ceph bluestore与 filestore 数据存放的区别
一. filestore 对象所在的PG以文件方式放在xfs文件中 1 查看所有的osd硬盘,跟其他linux其他硬盘一样,被挂载一个目录中. [root@hz-storage1 ~]# df -h ...
- Dubbo想要个网关怎么办?试试整合Spring Cloud Gateway
一.背景 在微服务架构中 API网关 非常重要,网关作为全局流量入口并不单单是一个反向路由,更多的是把各个边缘服务(Web层)的各种共性需求抽取出来放在一个公共的"服务"(网关)中 ...
- 自定义Springboot全局异常类
一.简要说明 如何实现网上文章基本是随便一搜就可以很快找到, 这里不再赘述. 二.Spring-web和Spring-webmvc 通过idea查看到两个注解位于 spring-web-5.2.2.R ...
- Js数据类型、Json格式、Json对象、Json字符串
数据类型,从结构上看,所有的数据最终都可以分成三种类型: 第一种类型是scalar(标量),也就是一个单独的string(字符串)或数字(numbers),比如“北京”这个单独的词. 第二种类型是se ...
