Python Ethical Hacking - VULNERABILITY SCANNER(1)
HTTP REQUESTS
BASIC INFORMATION FLOW
- The user clicks on a link.
- HTML website generates a request(client-side)
- The request is sent to the server.
- The server performs the requests(server-side)
- Sends response back.
GET vs POST
Two main methods used to send data to the web application:
1. Through the URL(Usually using GET).
a. http://webisite.com/news.php?id=1
b. http://website.com/?id=1
2. Through input elements(Usually using POST).
a. Search boxes.
b. Login boxes.
c. ..etc.
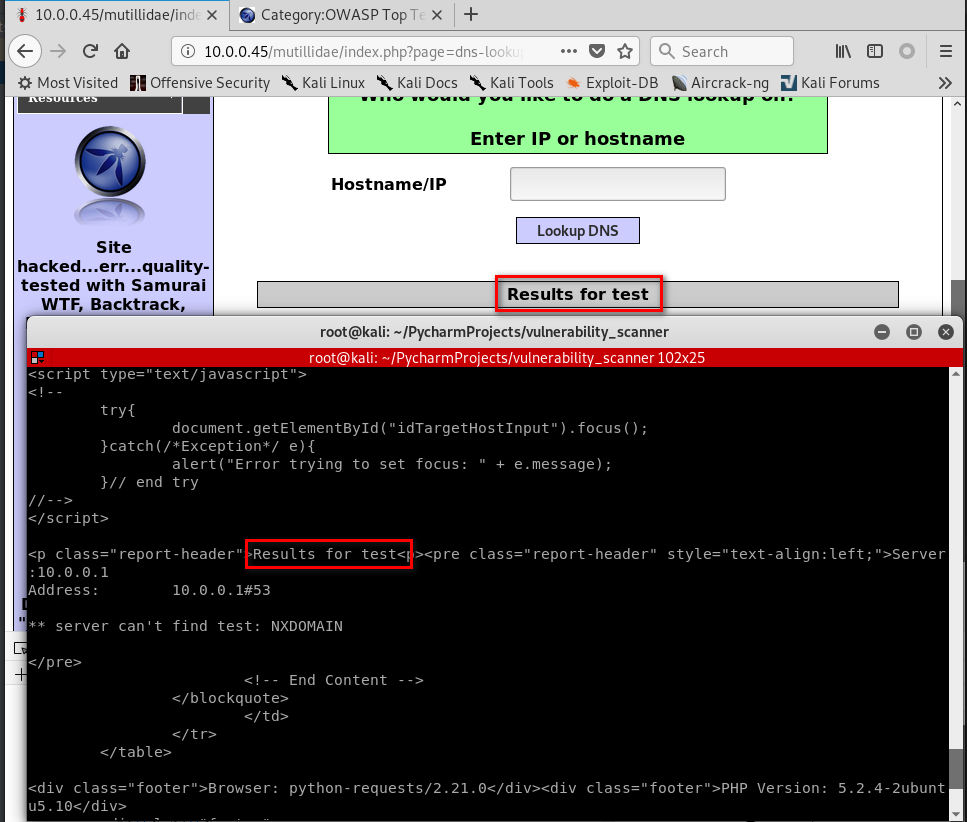
Target website:http://10.0.0.45/mutillidae/index.php?page=dns-lookup.php

#!/usr/bin/env python import requests
from bs4 import BeautifulSoup
from urllib.parse import urljoin def request(url):
try:
return requests.get(url)
except requests.exceptions.ConnectionError:
pass target_url = "http://10.0.0.45/mutillidae/index.php?page=dns-lookup.php"
response = request(target_url) parsed_html = BeautifulSoup(response.content.decode())
forms_list = parsed_html.findAll("form") for form in forms_list:
action = form.get("action")
post_url = urljoin(target_url, action)
method = form.get("method") inputs_list = form.findAll("input")
post_data = {}
for input in inputs_list:
input_name = input.get("name")
input_type = input.get("type")
input_value = input.get("value")
if input_type == "text":
input_value = "test" post_data[input_name] = input_value
result = requests.post(post_url, data=post_data)
print(result.content.decode())
Run the Python Code successfully.
Python Ethical Hacking - VULNERABILITY SCANNER(1)的更多相关文章
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
- Python Ethical Hacking - VULNERABILITY SCANNER(7)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(4)
Extracting & Submitting Forms Automatically Target website:http://10.0.0.45/dvwa/vulnerabilities ...
- Python Ethical Hacking - VULNERABILITY SCANNER(2)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(8)
Implementing Code To Discover XSS in Parameters 1. Watch the URL of the XSS reflected page carefully ...
- Python Ethical Hacking - VULNERABILITY SCANNER(3)
Polish the Python code using sending requests in a session Class Scanner. #!/usr/bin/env python impo ...
- Python Ethical Hacking - VULNERABILITY SCANNER(6)
EXPLOITATION - XSS VULNS EXPLOITING XSS Run any javascript code. Beef framework can be used to hook ...
- Python Ethical Hacking - VULNERABILITY SCANNER(5)
EXPLOITATION - XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript cod ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- 【Flutter实战】六大布局组件及半圆菜单案例
老孟导读:Flutter中布局组件有水平 / 垂直布局组件( Row 和 Column ).叠加布局组件( Stack 和 IndexedStack ).流式布局组件( Wrap )和 自定义布局组件 ...
- Linux下安装MongoDB 4.2数据库--使用tar包方式
(一)基础环境设置 操作系统版本 :centos-7.4 MongoDB版本:MongoDB 4.2 社区版 (1)关闭防火墙 # 关闭防火墙 [root@mongodbenterprise lib ...
- 基于MarkDown和Github图床以及SourceTree的一站式文章编辑和发布
标题: 基于MarkDown和Github图床以及SourceTree的一站式文章编辑和发布 作者: 梦幻之心星 sky-seeker@qq.com 标签: [MarkDown,Github,图床,S ...
- lsomap降维
# -*- coding: utf-8 -*- """ lsomap """ import numpy as np import matpl ...
- 在Github上建立自己的个人主页
目录 注册Github账号 登录Github账号 建立新仓库 选择个人主页的主题 注册Github账号 首先打开Github的主页(https://github.com/),点击右上角的sign up ...
- windows 下 node 安装 react
当前node.npm都已安装了. 可是在执行 安装 react的时候总是报错 最后会生成一个报错的txt文件( <npm-@googlegroups.com>npm-debug.log) ...
- Java基础之Synchronized原理
思维导图svg: https://note.youdao.com/ynoteshare1/index.html?id=eb05fdceddd07759b8b82c5b9094021a&type ...
- Jenkins 主题:jenkins-theme-v2
说明 本次样式是基于 Jenkins ver. 2.235.1 写的,所有对于之前的版本可能样式不兼容,好像变化挺大的.个人测试了在用的 Jenkins ver. 2.190.1,完全不行,所有建议想 ...
- [SCOI2016]背单词 题解
背单词 https://www.luogu.com.cn/problem/P3294 前言: Trie树的省选题(瑟瑟发抖QAQ) 问题汇总:(请忽略) (1)对Trie字典树的运用不熟练 (2)没想 ...
- 读取模式下cbc latch的事件模拟(热块竞争和热链竞争)-P62
文章目录 1. 背景 2. 过程 2.1 热块竞争 2.1.1 版本11.2.0.1.0 2.1.1.1 session 1(sid:34) 2.1.1.2 session 2(sid:35) 2.1 ...
