CodeForces1006E- Military Problem
E. Military Problem
time limit per test
3 seconds
memory limit per test
256 megabytes
input
standard input
output
standard output
In this problem you will have to help Berland army with organizing their command delivery system.
There are nn officers in Berland army. The first officer is the commander of the army, and he does not have any superiors. Every other officer has exactly one direct superior. If officer aa is the direct superior of officer bb, then we also can say that officer bb is a direct subordinate of officer aa.
Officer xx is considered to be a subordinate (direct or indirect) of officer yy if one of the following conditions holds:
- officer yy is the direct superior of officer xx;
- the direct superior of officer xx is a subordinate of officer yy.
For example, on the picture below the subordinates of the officer 33 are: 5,6,7,8,95,6,7,8,9.
The structure of Berland army is organized in such a way that every officer, except for the commander, is a subordinate of the commander of the army.
Formally, let's represent Berland army as a tree consisting of nn vertices, in which vertex uu corresponds to officer uu. The parent of vertex uucorresponds to the direct superior of officer uu. The root (which has index 11) corresponds to the commander of the army.
Berland War Ministry has ordered you to give answers on qq queries, the ii-th query is given as (ui,ki)(ui,ki), where uiui is some officer, and kiki is a positive integer.
To process the ii-th query imagine how a command from uiui spreads to the subordinates of uiui. Typical DFS (depth first search) algorithm is used here.
Suppose the current officer is aa and he spreads a command. Officer aa chooses bb — one of his direct subordinates (i.e. a child in the tree) who has not received this command yet. If there are many such direct subordinates, then aa chooses the one having minimal index. Officer aa gives a command to officer bb. Afterwards, bb uses exactly the same algorithm to spread the command to its subtree. After bb finishes spreading the command, officer aa chooses the next direct subordinate again (using the same strategy). When officer aa cannot choose any direct subordinate who still hasn't received this command, officer aa finishes spreading the command.
Let's look at the following example:
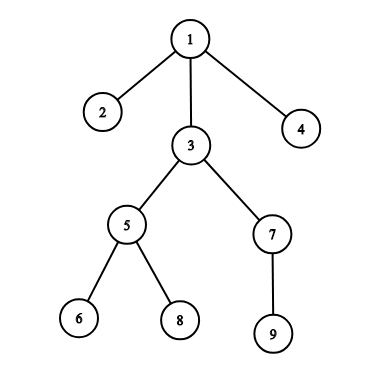
If officer 11 spreads a command, officers receive it in the following order: [1,2,3,5,6,8,7,9,4][1,2,3,5,6,8,7,9,4].
If officer 33 spreads a command, officers receive it in the following order: [3,5,6,8,7,9][3,5,6,8,7,9].
If officer 77 spreads a command, officers receive it in the following order: [7,9][7,9].
If officer 99 spreads a command, officers receive it in the following order: [9][9].
To answer the ii-th query (ui,ki)(ui,ki), construct a sequence which describes the order in which officers will receive the command if the uiui-th officer spreads it. Return the kiki-th element of the constructed list or -1 if there are fewer than kiki elements in it.
You should process queries independently. A query doesn't affect the following queries.
Input
The first line of the input contains two integers nn and qq (2≤n≤2⋅105,1≤q≤2⋅1052≤n≤2⋅105,1≤q≤2⋅105) — the number of officers in Berland army and the number of queries.
The second line of the input contains n−1n−1 integers p2,p3,…,pnp2,p3,…,pn (1≤pi<i1≤pi<i), where pipi is the index of the direct superior of the officer having the index ii. The commander has index 11 and doesn't have any superiors.
The next qq lines describe the queries. The ii-th query is given as a pair (ui,kiui,ki) (1≤ui,ki≤n1≤ui,ki≤n), where uiui is the index of the officer which starts spreading a command, and kiki is the index of the required officer in the command spreading sequence.
Output
Print qq numbers, where the ii-th number is the officer at the position kiki in the list which describes the order in which officers will receive the command if it starts spreading from officer uiui. Print "-1" if the number of officers which receive the command is less than kiki.
You should process queries independently. They do not affect each other.
Example
input
Copy
9 6
1 1 1 3 5 3 5 7
3 1
1 5
3 4
7 3
1 8
1 9
output
Copy
3
6
8
-1
9
4
题解:记录每个节点的时间戳和其有几个子节点即可;DFS
AC代码为:
#include<bits/stdc++.h>
using namespace std;
const int maxn = 2e5 + 10;
int n, m, a, b, c = 1, d;
bool vis[maxn] = { false };
vector<int> graph[maxn];
int level[maxn],pos[maxn],child[maxn];
int dfs(int src)
{
vis[src] = true;
pos[c] = src;
level[src] = c++;
int temp = 1;
for (int i = 0; i<graph[src].size(); i++)
{
if (!vis[graph[src][i]]) temp += dfs(graph[src][i]);
}
return child[src] = temp;
}
int main()
{
cin >> n >> m;
for (int i = 2; i <= n; i++)
{
cin >> a;
graph[a].push_back(i);
}
dfs(1);
while (m--)
{
cin >> a >> b;
if (child[a]<b) cout << -1 << endl;
else cout << pos[level[a] + b - 1] << endl;
}
return 0;
}
CodeForces1006E- Military Problem的更多相关文章
- Military Problem CodeForces 1006E (dfs序)
J - Military Problem CodeForces - 1006E 就是一道dfs序的问题 给定一个树, 然后有q次询问. 每次给出u,k, 求以u为根的子树经过深搜的第k个儿子,如果一个 ...
- CodeForces 1006E Military Problem(DFS,树的选择性遍历)
http://codeforces.com/contest/1006/problem/E 题意: 就是给出n,m,共n个点[1,n],m次询问.第二行给出n-1个数a[i],2<=i<=n ...
- Codeforces Round #498 (Div. 3)--E. Military Problem
题意问,这个点的然后求子树的第i个节点. 这道题是个非常明显的DFS序: 我们只需要记录DFS的入DFS的时间,以及出DFS的时间,也就是DFS序, 然后判断第i个子树是否在这个节点的时间段之间. 最 ...
- Military Problem CodeForces - 1006E(dfs搜一下 标记一下)
题意: 就是有一颗树 然后每次询问 父结点 的 第k个结点是不是他的子嗣...是的话就输出这个子嗣..不是 就输出-1 解析: 突然想到后缀数组的sa 和 x的用法..就是我们可以用一个id标记当前 ...
- Codeforces Round #498 (Div. 3) E. Military Problem (DFS)
题意:建一颗以\(1\)为根结点的树,询问\(q\)次,每次询问一个结点,问该结点的第\(k\)个子结点,如果不存在则输出\(-1\). 题解:该题数据范围较大,需要采用dfs预处理的方法,我们从结点 ...
- 树&图 记录
A - Lake Counting POJ - 2386 最最最最最基础的dfs 挂这道题为了提高AC率(糖水不等式 B - Paint it really, really dark gray Cod ...
- Codeforces Div3 #498 A-F
. A. Adjacent Replacement ...
- Codeforces Round #498 (Div. 3) 简要题解
[比赛链接] https://codeforces.com/contest/1006 [题解] Problem A. Adjacent Replacements [算法] 将序列中的所有 ...
- DFS序专题
牛客专题之DFS序 简介 dfs序: 每个节点在dfs深度优先遍历中的进出栈的时间序列,也就是tarjan算法中的dfn数组. 画个图理解一下: 这棵树的dfs序:1 3 2 4 2 5 6 7 6 ...
随机推荐
- T-SQL Part V: Locks
写SQL最常见的问题就是Dead Lock了.本篇简单介绍入门级别的Lock使用和排查. 首先来看MSDN上的官方文档(https://technet.microsoft.com/en-us/libr ...
- PHP 从另一个角度来分析 Laravel 框架的依赖注入功能
从根本上说,依赖注入不是让对象创建一个依赖关系,也不是让工厂对象去创建对象,而是将所需的依赖变成一个外部对象,使之成为一个"某些人的问题” 你为"某些人的问题”注入了类的依赖关系. ...
- PHP 当Swoole 遇上 ThinkPHP5
本文假设你已经有了 Linux 操作系统的 PHP 环境,强烈推荐使用 Vagrant 来搭建开发环境 安装 Swoole PECL 拓展可以通过 pecl 命令或者通过源码包编译安装,本文采用 pe ...
- java编程思想第四版第十章总结
1. 内部类的特性 他允许你把一些逻辑相关的类组织在一起. 2. 使用.this 如果你需要在内部类中堆外部类进行应用,可以使用外部类的名字后面加.this.下面展示了如何使用 .this packa ...
- requests模拟登陆的三种方式
###获取登录后的页面三种方式: 一.实例化seesion,使用seesion发送post请求,在使用他获取登陆后的页面 import requests session = requests.sess ...
- bind cname
$TTL 1D @ IN SOA @ rname.invalid. ( 0 ; serial 1D ; refresh 1H ; retry 1W ; expire 3H ) ; minimum NS ...
- iOS 抽奖轮盘效果实现思路
临近活动,相信不少app都会加一个新的需求——抽奖不多废话,先上GIF效果图 作为一个开发者,有一个学习的氛围跟一个交流圈子特别重要这是一个我的iOS交流群:937194184,不管你是小白还是大牛欢 ...
- 2019-11-26:密码学基础知识,csrf防御
信息安全的基础是数学--->密码算法--->安全协议(ssl VPN)-->应用(证书 PKI)密码学入门密码编码学:研究加解密算法的学科密码分析学:研究破译密码算法的学科 加解密分 ...
- 选择了uniapp开发app
7月份打算做一简单app,之前公司做app的时候简单用过Dcloud公司的mui,当时由于uniapp刚出来,最终选择了mui.对uniapp的 了解几乎没有. 做app对我来说几乎是零基础的,当然是 ...
- springboot+logback日志输出企业实践(上)
目录 1.引言 2.logback简介 3. springboot默认日志框架-logback 3.1 springboot示例工程搭建 3.2 日志输出与基本配置 3.2.1 日志默认输出 3.2. ...
