Ethical Hacking - NETWORK PENETRATION TESTING(16)
ARP Poisoning - MITMf
MITMf is a framework that allows us to launch a number of MITM attacks. MITMf also starts SSLstrip automatically to bypass HTTPS/SSL.
Download and Install the MITMf tool from the following website: https://github.com/byt3bl33d3r/MITMf

Installed successfully.
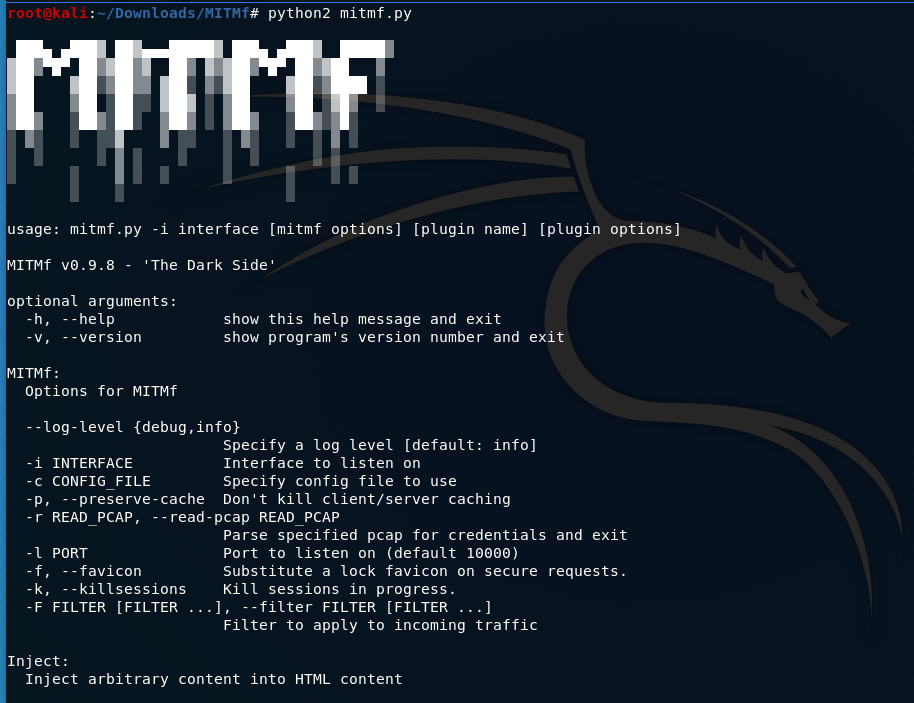
Usage:
mitmf --arp --spoof --gateway [GATEWAY IP] --targets [TARGET IPs] -i [interface]
e.g. python2 mitmf.py --arp --spoof --gateway 10.0.0.1 --target 10.0.0.210 -i eth0
echo >/proc/sys/net/ipv4/ip_forward

The MITMf is working now.

>>>My pip2 is broken. The following is the steps to fix this problem.
$ wget https://bootstrap.pypa.io/get-pip.py
$ sudo python2. get-pip.py
Ethical Hacking - NETWORK PENETRATION TESTING(16)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- Docker数据管理与挂载管理
介绍如何在 Docker 内部以及容器之间管理数据:在容器中管理数据主要有两种方式:数据卷(Volumes).挂载主机目录 (Bind mounts) 镜像来源 [root@docker01 ~]# ...
- linux下操作memcache的操作命令
1.连接memcache linux下一般使用telnet连接memcache服务 [root@localhost ~]# telnet 127.0.0.1 11266 Trying 127.0.0. ...
- 3分钟理解NMS非极大值抑制
1. NMS被广泛用到目标检测技术中,正如字面意思,抑制那些分数低的目标,使最终框的位置更准: 2. 假如图片上实际有10张人脸,但目标检测过程中,检测到有30个框的位置,并且模型都认为它们是人脸,造 ...
- fatal error C1189: #error : This file requires _WIN32_WINNT to be #defined at least to 0x0403. Value 0x0501 or higher is recommended.
说了原因,下面是修改方法,就是在stdafx.h文件中修改相关的定义,修改完后的效果应该如下: ? 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 #ifndef WINVER ...
- 廖雪峰Python教学课后作业---datetime
# -*- coding: utf-8 -*- import re from datetime import datetime, timezone, timedelta def to_timestam ...
- 写出Python中列表、元祖、字典、字符串的至少5种以上的方法
1.列表 常用方法 作用 参数 append(data) 在尾部添加数据 data-加入到列表中的数据 insert(idx,data) 在指定位置添加数据 idx-索引 data-数据 ext ...
- 让网页变灰的实现_网站蒙灰CSS样式总汇
每次全国哀悼日,各大网站首页都变成了灰色,添加以下全局CSS样式,可以实现此效果: 方法一 html { -webkit-filter: grayscale(100%);filter:progid:D ...
- 文件读取一些payload
Windows: C:boot.ini //查看系统版本 C:WindowsSystem32inetsrvMetaBase.xml //IIS配置文件 C:Windowsrepairsam //存储系 ...
- Windows下生成IOS证书并发布APP安装到IPhone
目录: 一:生成证书 二:安装到IPhone 准备环境: 1.Appuploader(需要安装Java环境) 2.爱思助手 一.生成证书 1.1.打开appuploader后登陆开发者账号 1.2.点 ...
- day22 常用模块(上)
一.时间模块 1 time模块 获取时间的三种格式: 第一种:time.time() 时间戳(timestamp):从1970年到现在的秒数 #应用场景:计算时间差 可以对时间加减,返回值为浮点型 p ...
