不同机房vpc使用openswan打通内网
1、测试环境:
北京6云主机:120.92.51.75/10.0.3.13 VPC:10.0.0.0/16 Ren-test
上海2云主机:42.157.163.120/192.168.3.3 VPC:zxs_vpc
- 2、下载安装openwan:
- 1、安装依赖包:
- # yum -y install gmp-devel bison flex gcc
- 2、下载安装openswan
- https://download.openswan.org/openswan/
- # wget https://download.openswan.org/openswan/openswan-2.6.43.1.tar.gz
- # tar zxf openswan-2.6.43.1.tar.gz
- # cd openswan-2.6.43.1
- # make programs
- # sudo make install
- 3、启动openswan
- # /etc/init.d/ipsec start # 启动
- # netstat -lnput |grep pluto # 查看监听端口
- 4、基础环境,内核参数等配置修改
- # ipsec verify # 基础环境依赖、状态查看
- ① 解决,更新如下配置:
- echo 0 > /proc/sys/net/ipv4/conf/all/rp_filter;
- echo 0 > /proc/sys/net/ipv4/conf/default/rp_filter;
- echo 0 > /proc/sys/net/ipv4/conf/eth0/rp_filter;
- echo 0 > /proc/sys/net/ipv4/conf/eth1/rp_filter;
- echo 0 > /proc/sys/net/ipv4/conf/lo/rp_filter;
- ② 配置服务器路由转发功能等操作
- # vi /etc/sysctl.conf
- net.ipv4.ip_forward = 1 # 开启转发
- net.ipv4.conf.default.rp_filter = 0
- # 关闭icmp重定向
- # sysctl -a | egrep "ipv4.*(accept|send)_redirects" | awk -F "=" '{print$1"= 0"}' >> /etc/sysctl.conf
- # sysctl -p
- ③ 检查最终效果
- # ipsec verify
- #北京6云主机配置:
- [root@vm10-0-3-13 ]# cat /etc/issue
- CentOS release 6.9 (Final)
- [root@vm10-0-3-13 ~]# curl myip.ksyun.com
- {"eip":"120.92.51.75"}
- [root@vm10-0-3-13 ~]# cat /etc/sysctl.conf
- net.ipv4.ip_forward = 1
- net.ipv4.conf.default.rp_filter = 0
- net.ipv4.conf.default.accept_source_route = 0
- kernel.sysrq = 0
- kernel.core_uses_pid = 1
- net.ipv4.tcp_syncookies = 1
- net.bridge.bridge-nf-call-ip6tables = 0
- net.bridge.bridge-nf-call-iptables = 0
- net.bridge.bridge-nf-call-arptables = 0
- kernel.msgmnb = 65536
- kernel.msgmax = 65536
- kernel.shmmax = 68719476736
- kernel.shmall = 4294967296
- net.ipv4.tcp_keepalive_time = 1200
- net.ipv4.ip_local_port_range = 1024 65535
- net.ipv4.conf.all.rp_filter = 0
- net.ipv4.conf.default.rp_filter = 0
- net.ipv4.conf.eth0.rp_filter = 0
- net.ipv4.conf.eth1.rp_filter = 0
- net.ipv4.conf.all.arp_announce = 2
- net.ipv4.conf.default.arp_announce = 2
- net.ipv4.conf.eth0.arp_announce = 2
- net.ipv4.conf.eth1.arp_announce = 2
- net.ipv6.conf.all.disable_ipv6 = 0
- net.ipv6.conf.default.disable_ipv6 = 0
- net.ipv6.conf.lo.disable_ipv6 = 0
- net.ipv4.conf.all.accept_redirects = 0
- net.ipv4.conf.all.send_redirects = 0
- net.ipv4.conf.default.accept_redirects = 0
- net.ipv4.conf.default.send_redirects = 0
- net.ipv4.conf.lo.accept_redirects = 0
- net.ipv4.conf.lo.send_redirects = 0
- net.ipv4.conf.eth0.accept_redirects = 0
- net.ipv4.conf.eth0.send_redirects = 0
- net.ipv4.conf.eth1.accept_redirects = 0
- net.ipv4.conf.eth1.send_redirects = 0
- [root@vm10-0-3-13 ~]# cat /etc/ipsec.d/ksyun.conf
- conn BJ-to-SH
- ike=3des-sha1
- authby=secret
- phase2=esp
- phase2alg=3des-sha1
- compress=no
- type=tunnel
- pfs=yes
- leftid=42.157.163.120
- left=42.157.163.120
- leftsubnet=192.168.0.0/16
- leftnexthop=%defaultroute
- rightid=120.92.51.75
- right=10.0.3.13
- rightsubnet=10.0.0.0/16
- rightnexthop=%defaultroute
- auto=start
- [root@vm10-0-3-13 ~]# cat /etc/ipsec.secrets
- #include /etc/ipsec.d/*.secrets
- 0.0.0.0 0.0.0.0 : PSK "kingsoft"
- [root@vm10-0-3-13 ~]# ip addr show
- 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN
- link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
- inet 127.0.0.1/8 scope host lo
- 2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
- link/ether fa:16:3e:0c:35:df brd ff:ff:ff:ff:ff:ff
- inet 10.0.3.13/24 brd 10.0.3.255 scope global eth0
- 3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
- link/ether fa:16:3e:3e:72:2f brd ff:ff:ff:ff:ff:ff
- inet 10.0.2.208/24 brd 10.0.2.255 scope global eth1
- [root@vm10-0-3-13 ~]# ip route show
- 10.0.2.0/24 dev eth1 proto kernel scope link src 10.0.2.208
- 10.0.3.0/24 dev eth0 proto kernel scope link src 10.0.3.13
- 169.254.0.0/16 dev eth0 scope link metric 1002
- 169.254.0.0/16 dev eth1 scope link metric 1003
- default via 10.0.3.1 dev eth0
- [root@vm10-0-3-13 log]# tail -20 /var/log/pluto.log
- Jul 25 15:30:57: listening for IKE messages
- Jul 25 15:30:57: adding interface eth1/eth1 10.0.2.208:500
- Jul 25 15:30:57: adding interface eth1/eth1 10.0.2.208:4500
- Jul 25 15:30:57: adding interface eth0/eth0 10.0.3.13:500
- Jul 25 15:30:57: adding interface eth0/eth0 10.0.3.13:4500
- Jul 25 15:30:57: adding interface lo/lo 127.0.0.1:500
- Jul 25 15:30:57: adding interface lo/lo 127.0.0.1:4500
- Jul 25 15:30:57: | setup callback for interface lo:4500 fd 23
- Jul 25 15:30:57: | setup callback for interface lo:500 fd 22
- Jul 25 15:30:57: | setup callback for interface eth0:4500 fd 21
- Jul 25 15:30:57: | setup callback for interface eth0:500 fd 20
- Jul 25 15:30:57: | setup callback for interface eth1:4500 fd 19
- Jul 25 15:30:57: | setup callback for interface eth1:500 fd 18
- Jul 25 15:30:57: loading secrets from "/etc/ipsec.secrets"
- Jul 25 15:30:57: "BJ-to-SH" #1: initiating Main Mode
- Jul 25 15:30:57: "BJ-to-SH" #1: ignoring Vendor ID payload [Openswan(xeleranized)]
- Jul 25 15:30:57: "BJ-to-SH" #1: received Vendor ID payload [Dead Peer Detection]
- Jul 25 15:30:57: "BJ-to-SH" #1: received Vendor ID payload [RFC 3947]
- Jul 25 15:30:57: "BJ-to-SH" #1: enabling possible NAT-traversal with method RFC 3947 (NAT-Traversal)
- Jul 25 15:30:57: "BJ-to-SH" #1: transition from state STATE_MAIN_I1 to state STATE_MAIN_I2
- Jul 25 15:30:57: "BJ-to-SH" #1: STATE_MAIN_I2: sent MI2, expecting MR2
- Jul 25 15:30:57: "BJ-to-SH" #1: NAT-Traversal: Result using RFC 3947 (NAT-Traversal) sender port 500: I am behind NAT+peer behind NAT
- Jul 25 15:30:57: "BJ-to-SH" #1: transition from state STATE_MAIN_I2 to state STATE_MAIN_I3
- Jul 25 15:30:57: "BJ-to-SH" #1: STATE_MAIN_I3: sent MI3, expecting MR3
- Jul 25 15:30:57: "BJ-to-SH" #1: received Vendor ID payload [CAN-IKEv2]
- Jul 25 15:30:57: "BJ-to-SH" #1: Main mode peer ID is ID_IPV4_ADDR: '42.157.163.120'
- Jul 25 15:30:57: "BJ-to-SH" #1: transition from state STATE_MAIN_I3 to state STATE_MAIN_I4
- Jul 25 15:30:57: "BJ-to-SH" #1: STATE_MAIN_I4: ISAKMP SA established {auth=PRESHARED_KEY cipher=oakley_3des_cbc_192 integ=sha group=MODP2048}
- Jul 25 15:30:57: "BJ-to-SH" #2: initiating Quick Mode PSK+ENCRYPT+TUNNEL+PFS+UP+IKEV1_ALLOW+IKEV2_ALLOW+SAREF_TRACK+IKE_FRAG_ALLOW {using isakmp#1 msgid:8d92af45 proposal=3DES(3)_000-SHA1(2)_000 pfsgroup=OAKLEY_GROUP_MODP2048}
- Jul 25 15:30:57: "BJ-to-SH" #2: transition from state STATE_QUICK_I1 to state STATE_QUICK_I2
- Jul 25 15:30:57: "BJ-to-SH" #2: STATE_QUICK_I2: sent QI2, IPsec SA established tunnel mode {ESP/NAT=>0x32aaec51 <0x73d0c6c9 xfrm=3DES_0-HMAC_SHA1 NATOA=none NATD=42.157.163.120:4500 DPD=passive}
- 上海2云主机配置:
- [root@vm192-168-3-9 ~]# cat /etc/issue
- \S
- Kernel \r on an \m
- [root@vm192-168-3-9 ~]# curl myip.ksyun.com
- {"eip":"42.157.163.120"}
- [root@vm192-168-3-9 ~]# cat /etc/ipsec.d/ksyun.conf
- conn SH-to-BJ
- ike=3des-sha1
- authby=secret
- phase2=esp
- phase2alg=3des-sha1
- compress=no
- type=tunnel
- pfs=yes
- leftid=42.157.163.120
- left=192.168.3.9
- leftsubnet=192.168.0.0/16
- leftnexthop=%defaultroute
- rightid=120.92.51.75
- right=120.92.51.75
- rightsubnet=10.0.0.0/16
- rightnexthop=%defaultroute
- auto=start
- [root@vm192-168-3-9 ~]# cat /etc/ipsec.secrets
- 0.0.0.0 0.0.0.0 : PSK "kingsoft"
- [root@vm192-168-3-9 ~]# ip addr show
- 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
- link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
- inet 127.0.0.1/8 scope host lo
- valid_lft forever preferred_lft forever
- 2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
- link/ether fa:16:3e:7d:86:8f brd ff:ff:ff:ff:ff:ff
- inet 192.168.3.9/24 brd 192.168.3.255 scope global eth0
- valid_lft forever preferred_lft forever
- [root@vm192-168-3-9 ~]# ip route show
- default via 192.168.3.1 dev eth0
- 169.254.0.0/16 dev eth0 scope link metric 1002
- 192.168.3.0/24 dev eth0 proto kernel scope link src 192.168.3.9
- [root@vm192-168-3-9 ~]# tail -20 /var/log/messages
- Jul 25 15:07:32 vm192-168-3-9 ipsec_setup: Starting Openswan IPsec U2.6.43/K3.10.0-862.14.4.el7.x86_64...
- Jul 25 15:07:32 vm192-168-3-9 ipsec_setup: Using NETKEY(XFRM) stack
- Jul 25 15:07:32 vm192-168-3-9 kernel: IPv6: esp6_init: can't add xfrm type
- Jul 25 15:07:32 vm192-168-3-9 kernel: IPv6: ah6_init: can't add xfrm type
- Jul 25 15:07:32 vm192-168-3-9 kernel: AVX2 instructions are not detected.
- Jul 25 15:07:33 vm192-168-3-9 kernel: AVX2 or AES-NI instructions are not detected.
- Jul 25 15:07:33 vm192-168-3-9 ipsec_setup: ...Openswan IPsec started
- Jul 25 15:07:33 vm192-168-3-9 pluto: adjusting ipsec.d to /etc/ipsec.d
- Jul 25 15:07:33 vm192-168-3-9 ipsec__plutorun: 002 added connection description "SH-to-BJ"
- Jul 25 15:07:33 vm192-168-3-9 ipsec__plutorun: 002 listening for IKE messages
- Jul 25 15:07:33 vm192-168-3-9 ipsec__plutorun: 002 adding interface eth0/eth0 192.168.3.9:500
- Jul 25 15:07:33 vm192-168-3-9 ipsec__plutorun: 002 adding interface eth0/eth0 192.168.3.9:4500
- Jul 25 15:07:33 vm192-168-3-9 ipsec__plutorun: 002 adding interface lo/lo 127.0.0.1:500
- Jul 25 15:07:33 vm192-168-3-9 ipsec__plutorun: 002 adding interface lo/lo 127.0.0.1:4500
- Jul 25 15:07:33 vm192-168-3-9 ipsec__plutorun: 002 loading secrets from "/etc/ipsec.secrets"
- [root@vm192-168-3-9 ~]# 可以配置/etc/ipsec.conf中logfile=/var/log/pluto.log或plutostderrlog=/var/log/pluto.log开启openwan日志
- added connection description "SH-to-BJ"
- listening for IKE messages
- adding interface eth0/eth0 192.168.3.9:500
- adding interface eth0/eth0 192.168.3.9:4500
- adding interface lo/lo 127.0.0.1:500
- adding interface lo/lo 127.0.0.1:4500
- loading secrets from "/etc/ipsec.secrets"
- packet from 120.92.51.75:500: received Vendor ID payload [Dead Peer Detection]
- packet from 120.92.51.75:500: ignoring Vendor ID payload [FRAGMENTATION]
- packet from 120.92.51.75:500: received Vendor ID payload [RFC 3947] method set to=115
- packet from 120.92.51.75:500: received Vendor ID payload [draft-ietf-ipsec-nat-t-ike-03] meth=108, but already using method 115
- packet from 120.92.51.75:500: received Vendor ID payload [draft-ietf-ipsec-nat-t-ike-02_n] meth=106, but already using method 115
- packet from 120.92.51.75:500: received Vendor ID payload [draft-ietf-ipsec-nat-t-ike-02] meth=107, but already using method 115
- "SH-to-BJ" #1: responding to Main Mode
- "SH-to-BJ" #1: transition from state STATE_MAIN_R0 to state STATE_MAIN_R1
- "SH-to-BJ" #1: STATE_MAIN_R1: sent MR1, expecting MI2
- "SH-to-BJ" #1: NAT-Traversal: Result using draft-ietf-ipsec-nat-t-ike (MacOS X): both are NATed
- "SH-to-BJ" #1: transition from state STATE_MAIN_R1 to state STATE_MAIN_R2
- "SH-to-BJ" #1: STATE_MAIN_R2: sent MR2, expecting MI3
- "SH-to-BJ" #1: Main mode peer ID is ID_IPV4_ADDR: '120.92.51.75'
- "SH-to-BJ" #1: transition from state STATE_MAIN_R2 to state STATE_MAIN_R3
- "SH-to-BJ" #1: new NAT mapping for #1, was 120.92.51.75:500, now 120.92.51.75:4500
- "SH-to-BJ" #1: STATE_MAIN_R3: sent MR3, ISAKMP SA established {auth=OAKLEY_PRESHARED_KEY cipher=oakley_3des_cbc_192 prf=oakley_sha group=modp2048}
- "SH-to-BJ" #1: the peer proposed: 192.168.0.0/16:0/0 -> 10.0.0.0/16:0/0
- "SH-to-BJ" #2: responding to Quick Mode proposal {msgid:d6c02a77}
- "SH-to-BJ" #2: us: 192.168.0.0/16===192.168.3.9<192.168.3.9>[42.157.163.120]---192.168.3.1
- "SH-to-BJ" #2: them: 192.168.3.1---120.92.51.75<120.92.51.75>===10.0.0.0/16
- "SH-to-BJ" #2: transition from state STATE_QUICK_R0 to state STATE_QUICK_R1
- "SH-to-BJ" #2: STATE_QUICK_R1: sent QR1, inbound IPsec SA installed, expecting QI2
- "SH-to-BJ" #2: transition from state STATE_QUICK_R1 to state STATE_QUICK_R2
- "SH-to-BJ" #2: STATE_QUICK_R2: IPsec SA established tunnel mode {ESP=>0xd85f23ba <0x232e6a69 xfrm=3DES_0-HMAC_SHA1 NATOA=none NATD=120.92.51.75:45
- 00 DPD=none}
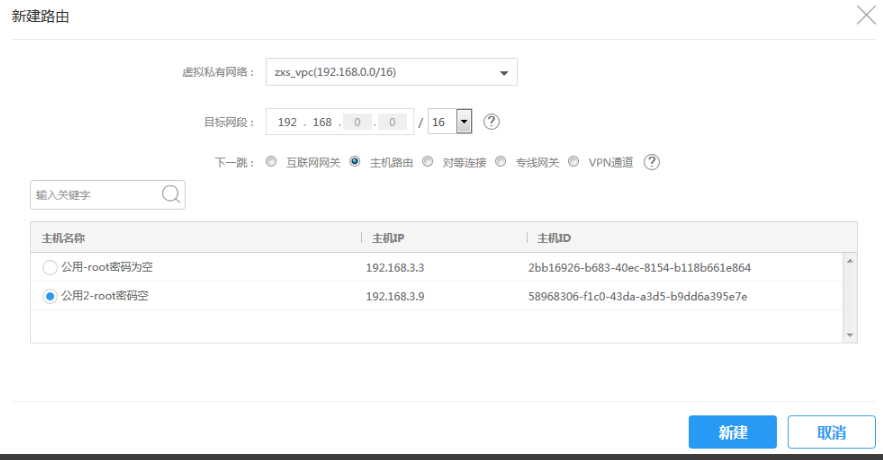
3、VPC控制台路由配置:
北京6 VPC:

上海2 VPC:
参考文档:https://www.172173.com/openswan.html#2-5-%E9%AA%8C%E8%AF%81%E7%8E%AF%E5%A2%83
不同机房vpc使用openswan打通内网的更多相关文章
- 阿里云vpc网络SNAT实现内网实例通外网
需求场景: 因费用和安全考虑,内网部分机器没有分配公网IP,没绑定弹性公网IP,没有购买NAT服务,但是内网机器需要访问外网部分资源,如发送邮件. 操作步骤如下: 1.查看外网上的转发功能的开启没开启 ...
- 典型案例收集-使用OpenVPN连通多个机房内网(转)(静态路由)
说明: 1.这篇文章主要是使用静态路由表实现的多个机房通过VPN连接后的子网机房互通. 2.OpenVPN使用的是桥接模式(server-bridge和dev tap),这个是关键点,只有这样设置才可 ...
- ngrok反向隧道--获取内网IP
ngrok反向隧道 前情提要:小明与小白各有一台主机,两台主机在同一内网,小明想直接通过内网ssh到小白的主机上.但是小白的ip地址会不断的变化,而小明不想每次都要麻烦小白查看ip.于是小明催生了一个 ...
- 内网gitlab访问外网
外网要访问内网,内网出口必须有公网ip,且外网访问内部网络可以用花生壳,可以用主机端口映射 写ansible调api,打通内网到阿里云的master节点 如何将公司内网与云服务器内网打通 参照 ...
- service几种访问类型(集群外负载均衡访问LoadBalancer , 集群内访问ClusterIP,VPC内网负载均衡LoadBalancer ,集群外访问NodePort)
一.集群外访问(负载均衡) kind: ServiceapiVersion: v1spec: ports: - protocol: TCP port: 4341 targetPort: 8080 no ...
- IPsecVPN:阿里云VPN网关和深信服防火墙打通公有云和公司内网
简介 目前许多公司网络环境为混合云(私有云,IDC,公司内网融合)的状态,通过内网ip的访问使得工作更加方便,需求也更为迫切,而本文介绍的即是实现私有云和公司内网互通的一种方法,希望对有此需求的小伙伴 ...
- QQ通信原理及QQ是怎么穿透内网进行通信的? (转)
原:http://f543711700.iteye.com/blog/978044#bc2344608 QQ是一个基于TCP/UDP协议的通讯软件 发送消息的时候是UDP打洞,登陆的时候使用HTTP~ ...
- 烂泥:openvpn双网卡客户端与内网机器通信
本文由ilanniweb提供友情赞助,首发于烂泥行天下 想要获得更多的文章,可以关注我的微信ilanniweb. 前段时间写了一篇有关openvpn搭建与内网机器通信的文章,那篇文章是基于服务器单网卡 ...
- [转载]QQ通讯原理及QQ是怎么穿透内网的
QQ是一个基于TCP/UDP协议的通讯软件 发送消息的时候是UDP打洞,登陆的时候使用HTTP~因为登陆服务器其实就是一个HTTP服务器,只不过不是常用的那些,那个服务器是腾讯自行开发的!!! 一.登 ...
随机推荐
- 城市防汛应急管理智慧 Web GIS 可视化平台
前言 今年第 17 号台风"狮子山"(热带风暴级)登陆海南岛,受"狮子山"影响,海南岛北半部地区出现暴雨到大暴雨.局地特大暴雨.台风带来的强风雨导致海南岛多地树 ...
- SpringSecurity 小demo
SpringSecurity 首先搭建好springboot工程,然后引入springsecurity依赖. <dependency> <groupId>org.springf ...
- JavaWeb Cookie,Session
Cookie 1.Cookie翻译过来是饼干的意思.Cookie是服务器通知客户端保存键值对的一种技术.客户端有了Cookie 后,每次请求都发送给服务器.每个Cookie的大小不能超过4kb. 2. ...
- CF1208H Red Blue Tree
CF1208H Red Blue Tree 原本应该放在这里但是这题过于毒瘤..单独开了篇blog 首先考虑如果 $ k $ 无限小,那么显然整个树都是蓝色的.随着 $ k $ 逐渐增大,每个点都会有 ...
- PicGo + Gitee +Typora实现markdown图床
目录 1. PicGo安装 2.Gitee配置 3.配置PicGo 3.Typora的设置 网上有一些很详细的教程,我这里只记录要点,其余部分按以下教程步骤来就行. 1. PicGo安装 国内下载可能 ...
- [Linux] 非root安装GCC9.1.0
说明 一般Linux系统自带或公共的GCC版本都很低,如目前我们的服务器版本的GCC还停留在gcc-4.9.3,而官网已到达9.2版本(下载http://ftp.gnu.org/gnu/gcc/) , ...
- CentOS6安装Zabbix(RPM包)
1. 系统环境状态 2. 安装zabbix4.0 3. 安装mysql+apache+php环境 4.配置mysql 5.配置zabbix-server 6. 配置apache 7. web安装 1 ...
- Azure Key Vault(二)- 入门简介
一,引言 在介绍 Azure Key Vault 之前,先简单介绍一下 HSM(硬件安全模块). -------------------- 我是分割线 -------------------- 1,什 ...
- absurd, abundant
absurd How: absolutely, completely, clearly, faintly, manifestly, obviously, patently, quite, rather ...
- 【Linux】【Basis】【网络】网络相关的内核参数
Linux系统内核设置优化tcp网络,# vi /etc/sysctl.conf,添加以下内容 net.ipv4.tcp_syncookies = 1 表示开启SYN Cookies.当出现SYN等待 ...
