Practical Web Penettation Testing (the first one Mutillidae 大黄蜂)
1、now we looke at this book . I decide to make a brief review
the book covers as follows (I straight-forward copy here):
Chapter 1, Building a Vulnerable Web Application Lab, will help us to get and
install the vulnerable application Mutillidae using Windows and Linux. Also, we
will have a quick tour of how to use this vulnerable web application.
Chapter 2, Kali Linux Installation, will explain how to download, install, and
configure Kali Linux
Chapter 3, Delving Deep into the Usage of Kali Linux, will teach more about how
to deal with Kali Linux from the Terminal window, and will help you to become
a ninja in bash scripting as well.
Chapter 4, All About Using Burp Suite, covers what you need to know about
Metasploit to fulfil the role of a web application security expert.
Chapter 5, Understanding Web Application Vulnerabilities, explains the attacks
that can happen on a web application, and after finishing the chapter, you will be
able to use these skills to manipulate your findings during pentests.
Chapter 6, Application Security Pre-Engagement, will explain how to sign all the
necessary contracts before starting the tests. Also, you will learn how to
estimate, scope, and schedule your tests before they start.
Chapter 7, Application Threat Modeling, will explains that ATM is a security
architecture document that allows you to identify future threats and to pinpoint
the different pentest activities that need to be executed in the future deployment
of the web application project.
Chapter 8, Source Code Review, covers how to deal with the source code review
process. The source code is the heart or engine of a web application, and it must
be properly constructed from a security perspective.
Chapter 9, Network Penetration Testing, explains how to use Metasploit, Nmap,
and OpenVAS together to conduct a network infrastructure vulnerability
assessment.
Chapter 10, Web Intrusion Tests, will show how to look for web application based
vulnerabilities (SQLi, XSS, and CSRF) using Burp. Also, the readers will learn
how to take advantage of, get a remote shell, and probably elevate their
privileges on the victim web server.
Chapter 11, Pentest Automation Using Python, explains how to automate
everything that we have learned using the Python language for a more
performant result.
Appendix A, Nmap Cheat Sheet, a list of the most common Nmap options.
Appendix B, Metasploit Cheat Sheet, provides a quick reference to the Metasploit
framework.
Appendix C, Netcat Cheat Sheet, provides Netcat commands and a few popular
practical examples.
Appendix D, Networking Reference Section, provides important information about
networking, such as network subnets, port number, and its services.
Appendix E, Python Quick Reference, provides a quick overview of the amazing
programming language—Python.
2、now we looke at the first paragraph
how install vulnerable web application on wondows or linux or Ubuntu the application nmae's is Mutillidae in chinese(大黄蜂)
at present how to download ,the address url : www.packtpub.com
another resource in GitHub the address url: https://github.com/PacktPublishing/Practical-web-Penetration-Testing
how to building like this :
step1 download Mutiliidae url: https:/sourceforge.net
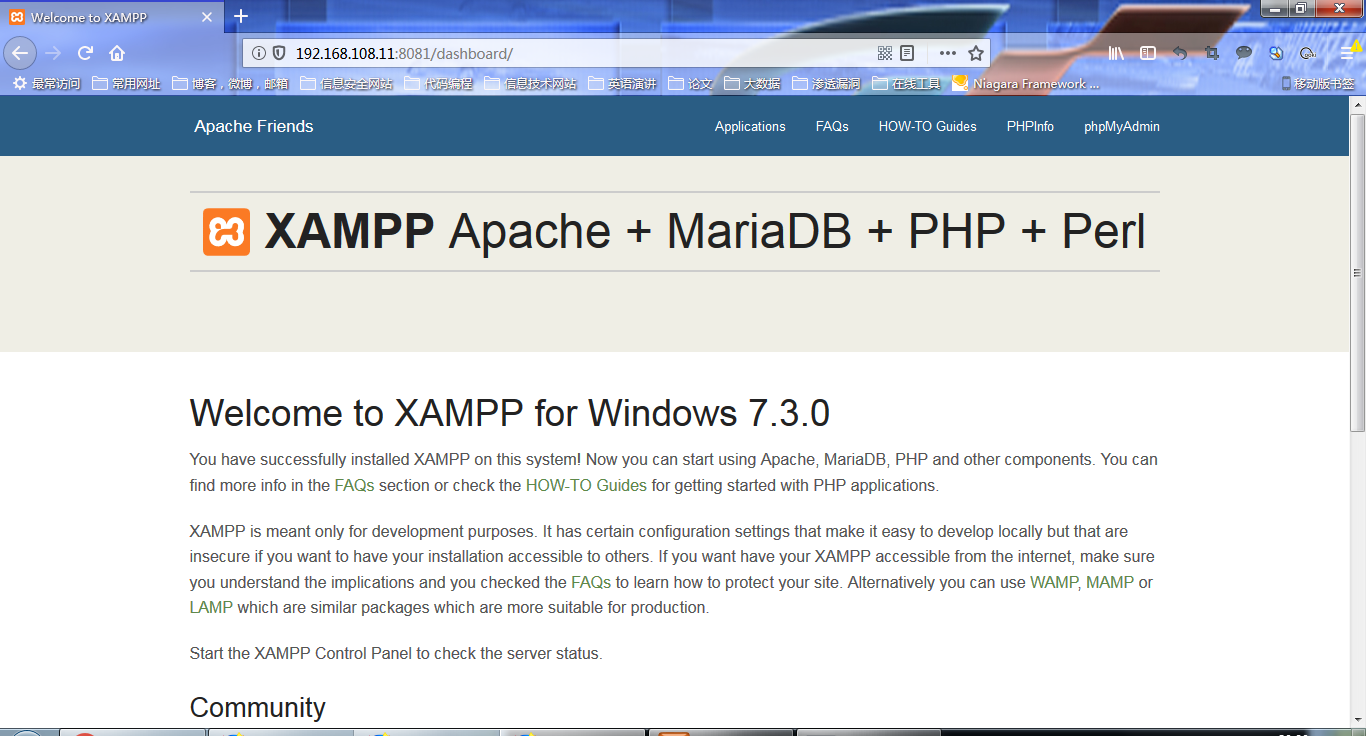
3、install the simulation application XAMPP
the XAMPP have Apache Mysql and php functions
the download url : https://www.apachefriends.org/download.html
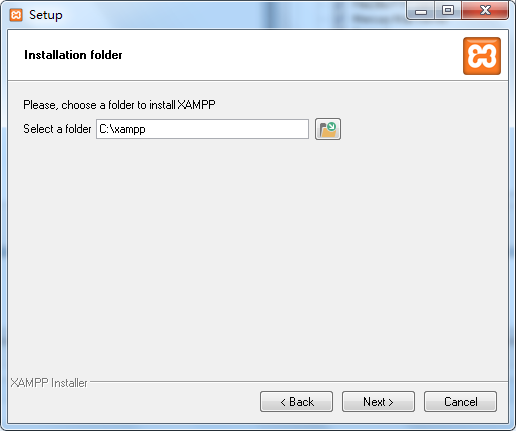
4、before install the XAMPP close allover antivirus,for me I have been installed another Trigger problems

install procedur as follows : in this here I use the default path C


我的电脑启动apacheL的时候 出现异常,因为之前安装过一个类似的application DVWA。也有可能是其他软件占用了固定的端口 ,修改配置文件如下
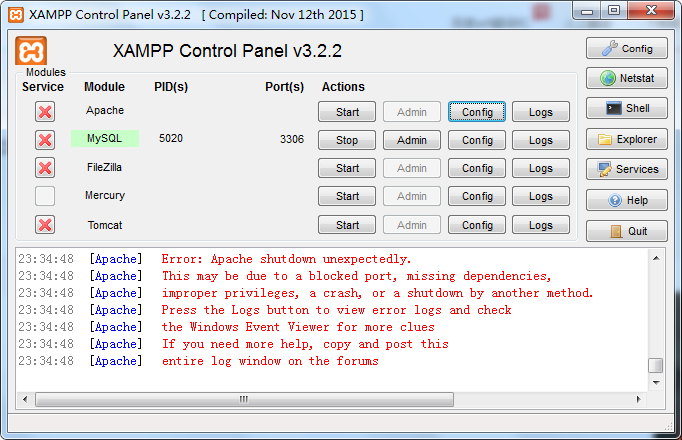
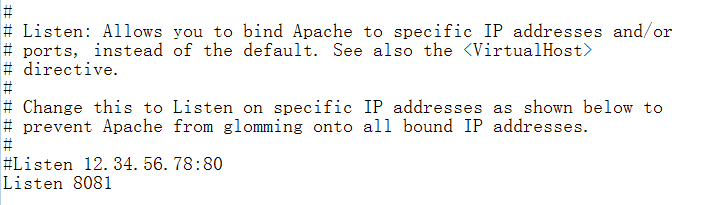
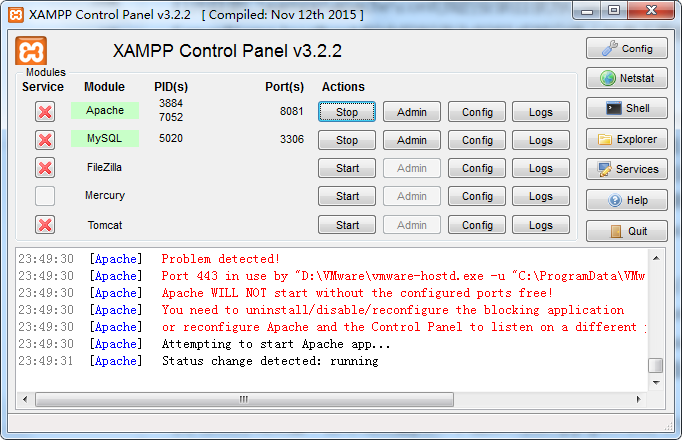
修改配置的端口后 启动成功。总结 修改一共两个端口 the one 服务端口 80 修改成8081 the second 监听端口 443 直接注释掉或者修改成1023以上的端口
5、how to install mutillidae
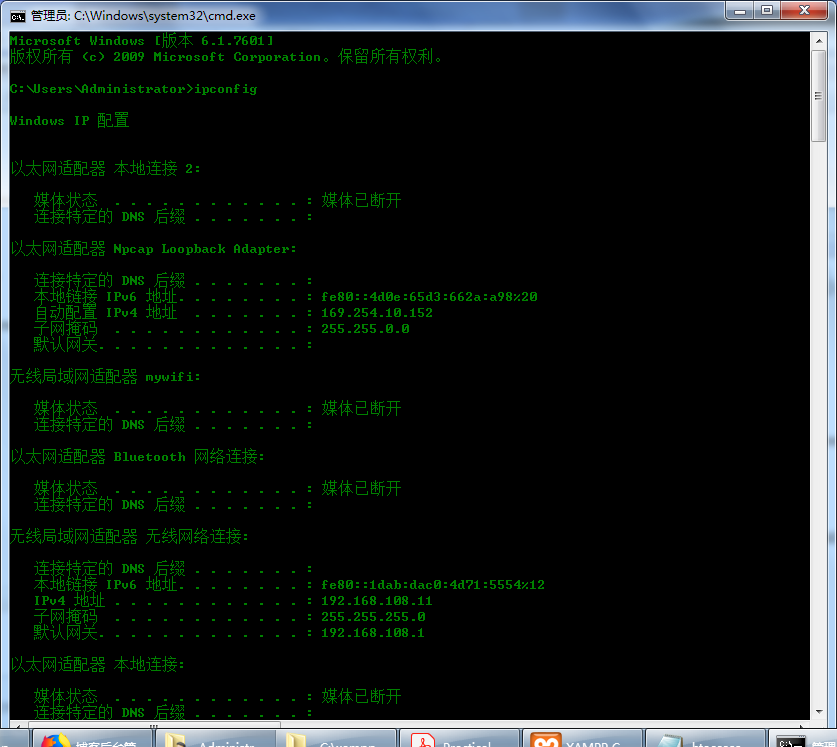
search your ip

成功启动Mutillidae之后 如下
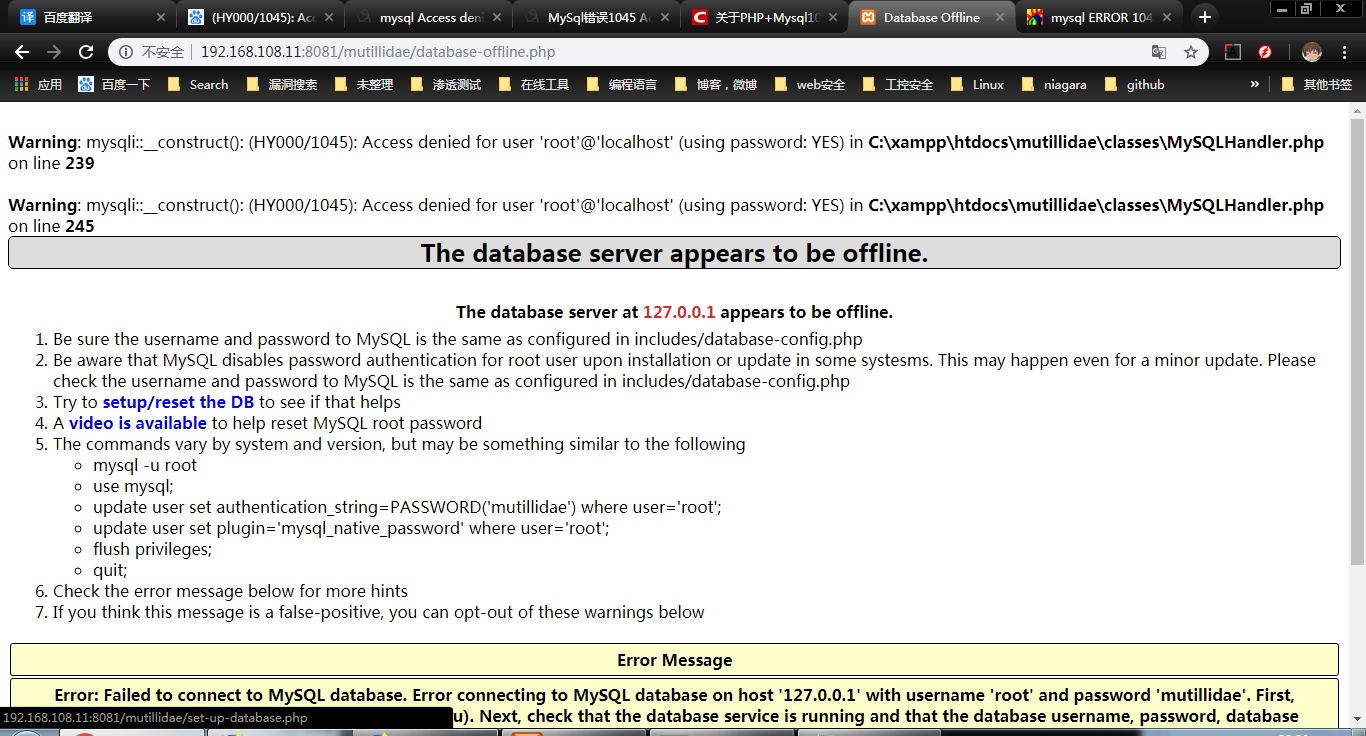
但是有时候提示出现 错误代码 1045
Access denied for user 'root'@'localhost' (using password:YES)

Practical Web Penettation Testing (the first one Mutillidae 大黄蜂)的更多相关文章
- Practical Web Penettation Testing (the first one Mutillidae 大黄蜂 之二)
1.how to use dpkg cmmand first it can be used for list all software , dpkg -l (由于kali linux 没有启动所以 ...
- 转:15 Best Responsive Web Design Testing Tools
Responsive Web Design is regarded as being the approach which suggests that web design and developme ...
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Web Penetration Testing
1.国外使用的一款在线工具,对web的信息收集很有帮助 地址http://archive.org , WayBack Machine 主界面如下:对百度存档的历史信息进行查询. 2.IP地址归属信息 ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(2)
INFORMATION GATHERING IP address. Domain name Info. Technologies used. Other websites on the same se ...
随机推荐
- java解压缩zip
依赖的包: <!-- https://mvnrepository.com/artifact/org.apache.ant/ant --> <dependency> <gr ...
- 微信支付-H5网页支付开通流程
简介 H5 支付是指商户在微信客户端外的移动端网页展示商品或服务,用户在前述页面确认使用微信支付时,商户发起本服务呼起微信客户端进行支付.主要用于触屏版的手机浏览器请求微信支付的场景.可以方便的从外 ...
- python模块-----time
说明 time模块提供各种时间相关的功能 与时间相关的模块有:time,datetime,calendar 这个模块的功能不是适用于所有的平台 这个模块中定义的大部分函数是调用C平台上的同名函数实现 ...
- ECharts.js学习(一) 简单入门
EChart.js 简单入门 最近有一个统计的项目要做,在前端的数据需要用图表的形式展示.网上搜索了一下,发现有几种统计图库. MSChart 这个是Visual Studio里的自带控件,使用比 ...
- 生产环境使用 pt-table-checksum 检查MySQL数据一致性【转】
公司数据中心从托管机房迁移到阿里云,需要对mysql迁移(Replication)后的数据一致性进行校验,但又不能对生产环境使用造成影响,pt-table-checksum 成为了绝佳也是唯一的检查工 ...
- 使用 Charles 抓取 App 网络请求
最近开发App的时候需要用到大量其他应用的数据,但接口不公开,所以想到了抓取.差不多要读到5W的用户数据,采用的是找到数据接口,然后不停发请求的方式.用到的抓取工具是Charles,本文讲解的应用是W ...
- Git学习笔记02-创建版本库
版本库就是一个目录,这个目录里面的所有文件都会被Git管理,每个文件的修改,删除都能追踪.以便在某个时刻追踪历史记录,或者还原 路径切换,查看文件命令和linux差不多,cd 文件路径 ls查看路径 ...
- Python Web开发框架Django
花了两周时间,利用工作间隙时间,开发了一个基于Django的项目任务管理Web应用.项目计划的实时动态,可以方便地被项目成员查看(^_^又重复发明轮子了).从前台到后台,好好折腾了一把,用到:HTML ...
- 题解-AtCoder Code-Festival2017qualA-E Modern Painting
Problem CODE-FESTIVAL 2017 qual A 洛谷账户的提交通道 题意:有一个\(n\)行\(m\)列的方格,在边界外有可能有机器人(坐标为\((0,x),(n+1,x),(x, ...
- 在 C# 中,(int) ,Int32.Parse() 和 Convert.toInt32() 三种方法的区别
在 C# 中,(int),Int32.Parse() 和 Convert.toInt32() 三种方法有何区别? int 关键字表示一种整型,是32位的,它的 .NET Framework 类型为 S ...
