Fibonacci Heaps
Mergeable heaps
A mergeable heap is any data structure that supports the following five operations,
in which each element has a key:
MAKE-HEAP./ creates and returns a new heap containing no elements.
INSERT.H; x/ inserts element x, whose key has already been filled in, into heap H.
MINIMUM.H/ returns a pointer to the element in heap H whose key is minimum.
EXTRACT-MIN.H/ deletes the element from heap H whose key is minimum, returning
a pointer to the element.
UNION.H1;H2/ creates and returns a new heap that contains all the elements of
heaps H1 and H2. Heaps H1 and H2 are “destroyed” by this operation.
In addition to the mergeable-heap operations above, Fibonacci heaps also support
the following two operations:
DECREASE-KEY.H; x; k/ assigns to element x within heap H the new key
value k, which we assume to be no greater than its current key value.1
DELETE.H; x/ deletes element x from heap H.


Each node has two other attributes. We store the number of children in the child
list of node x in x:degree. The boolean-valued attribute x:mark indicates whether
node x has lost a child since the last time x was made the child of another node.
Newly created nodes are unmarked, and a node x becomes unmarked whenever it
is made the child of another node. Until we look at the DECREASE-KEY operation
in Section 19.3, we will just set all mark attributes to FALSE.

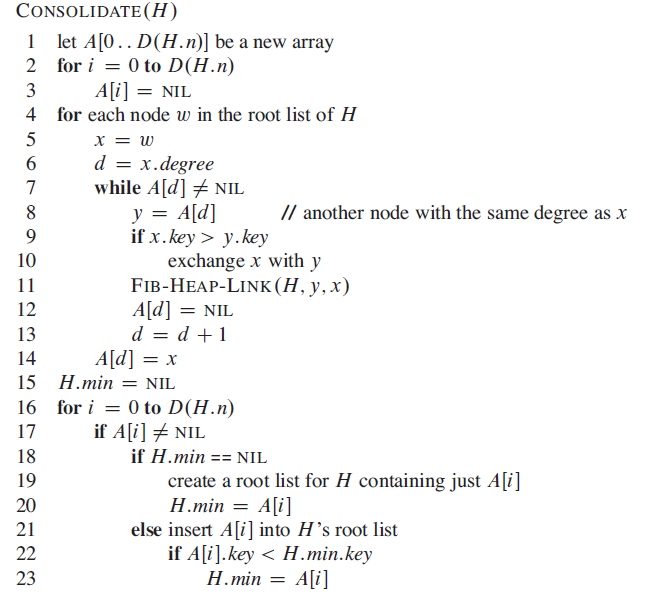
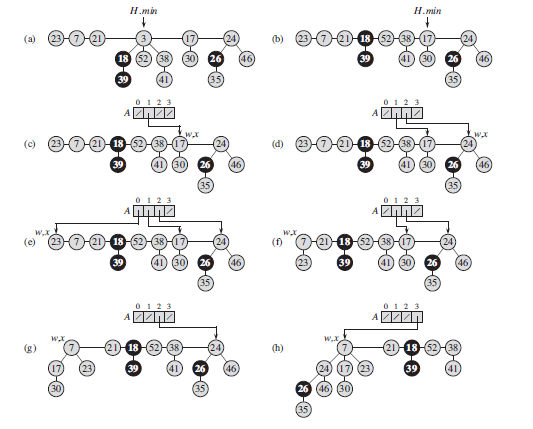
In detail, the CONSOLIDATE procedure works as follows. Lines 1–3 allocate
and initialize the array A by making each entry NIL. The for loop of lines 4–14
processes each root w in the root list. As we link roots together, w may be linked
to some other node and no longer be a root. Nevertheless, w is always in a tree
rooted at some node x, which may or may not be w itself. Because we want at
most one root with each degree, we look in the array A to see whether it contains
a root y with the same degree as x. If it does, then we link the roots x and y but
guaranteeing that x remains a root after linking. That is, we link y to x after first
exchanging the pointers to the two roots if y’s key is smaller than x’s key. After
we link y to x, the degree of x has increased by 1, and so we continue this process,
linking x and another root whose degree equalsx’s new degree, until no other root
that we have processed has the same degree as x. We then set the appropriate entry
of A to point to x, so that as we process roots later on, we have recorded that x is
the unique root of its degree that we have already processed. When this for loop
terminates, at most one root of each degree will remain, and the array A will point
to each remaining root.
The while loop of lines 7–13 repeatedly links the root x of the tree containing
node w to another tree whose root has the same degree as x, until no other root has
the same degree. This while loop maintains the following invariant:
At the start of each iteration of the while loop, d D x:degree.

Fibonacci Heaps的更多相关文章
- 一些鲜为人知却非常实用的数据结构 - Haippy
原文:http://www.udpwork.com/item/9932.html 作为程序猿(媛),你必须熟知一些常见的数据结构,比如栈.队列.字符串.链表.二叉树.哈希,但是除了这些常见的数据结构以 ...
- .NET中的泛型集合总结
最近对集合相关的命名空间比较感兴趣,以前也就用下List<T>, Dictionary<Tkey, TValue>之类,总之,比较小白.点开N多博客,MSDN,StackOve ...
- 【推荐】Data Structure Visualizations
University of San Francisco David Galles 功能:可视化数据结构&算法实现过程 网站地址 https://www.cs.usfca.edu/~ga ...
- [Algorithm] 如何正确撸<算法导论>CLRS
其实算法本身不难,第一遍可以只看伪代码和算法思路.如果想进一步理解的话,第三章那些标记法是非常重要的,就算要花费大量时间才能理解,也不要马马虎虎略过.因为以后的每一章,讲完算法就是这样的分析,精通的话 ...
- 某Facebook工程师写的攻略。
Chapter 1 Interesting read, but you can skip it. Chapter 2 2.1 Insertion Sort - To be honest you sho ...
- Programmer Competency Matrix--ref--http://sijinjoseph.com/programmer-competency-matrix/
Note that the knowledge for each level is cumulative; being atlevel n implies that you also know eve ...
- JAVA工程师技能要求
近期做了个JAVA工程师分类, JAVA工程师可能是市场上最多类的程序员: 初级JAVA工程师的基本要求 Good basic programming skills 良好基本编程技能 Founda ...
- 算法与数据结构(九) 查找表的顺序查找、折半查找、插值查找以及Fibonacci查找
今天这篇博客就聊聊几种常见的查找算法,当然本篇博客只是涉及了部分查找算法,接下来的几篇博客中都将会介绍关于查找的相关内容.本篇博客主要介绍查找表的顺序查找.折半查找.插值查找以及Fibonacci查找 ...
- #26 fibonacci seqs
Difficulty: Easy Topic: Fibonacci seqs Write a function which returns the first X fibonacci numbers. ...
随机推荐
- docker基本管理
一.docker基本命令 1.docker 获取镜像 将从 Docker Hub 仓库下载一个 Ubuntu 12.04 操作系统的镜像 docker pull ubuntu:12.04 Pullin ...
- No Directionality widget found
The problem is not that you have not wrapped your widgets into MaterialApp. As the documentation say ...
- Django-debug-toolbar的使用
Django项目的开发过程中,离不开各种调试,那么,我们今天介绍一个工具,django debug toolbar,该工具为我们提供了更加丰富的调试信息,如提供session信息,SQL查询信息等等. ...
- CSS 组合选择器
CSS 组合选择器 注:使用逗号分隔,同时应用. 多个id选择器拼接到一起 含有:i1 i2 i3的标签同时应用css样式. <html> <head> <!-- sty ...
- Docker Weave 介绍 or 工作原理
Docker Weave Network Weave Network:属于第三方网络项目. Weave在Docker主机之间实现Overlay网络,使用业界标准VXLAN封装,基于UDP传输,也可以加 ...
- Python Rabbit 广播模式
Exchange 在RabbitMQ下进行广播模式需要用到,exchange这个参数,它会把发送的消息推送到queues队列中,exchange必须要知道,它接下来收到的消息要分给谁,是要发给一个qu ...
- [C++ Primer Plus] 第5章、循环和关系表达式(一)程序清单——指针自加减优先级
程序5.4 #include<iostream> using namespace std; ; void main() { long long factorials[Size]; fact ...
- Oracle错误——user ** lacks CREATE SESSION privilege logon denied
错误 在删除一个用户TEST的情况下,再次新建用户TEST并赋予sysdba权限,使用plsqldev工具登录数据库TEST用户,报错user TEST lacks CREATE SESSION p ...
- 使用python内置库pytesseract实现图片验证码的识别
环境准备: 1.安装Tesseract模块 git文档地址:https://digi.bib.uni-mannheim.de/tesseract/ 下载后就是一个exe安装包,直接右击安装即可,安装完 ...
- (19)ThreadPoolExecutor线程池
# 线程池 # 实例化线程池 ThreadPoolExcutor (推荐cpu_count*(n+1)) # 异步提交任务 submit / map # 阻塞直到任务完成 shutdown # 获取子 ...
