Lab 7-2
Analyze the malware found in the file Lab07-02.exe.
Questions and Short Answers
How does this program achieve persistence?
A: This program does not achieve persistence. It runs once and then exits.
What is the purpose of this program?
A: The program displays an advertisement web page to the user.
When will this program finish executing?
A: The program finishes executing after displaying the advertisement.
Detailed Analysis
We begin with some basic static analysis. While we don’t see any interesting ASCII strings, we do see one interesting Unicode string: http://www.malwareanalysisbook.com/ad.html. We check the imports and exports of the program, and see only a few imports in addition to the standard imports, as follows:
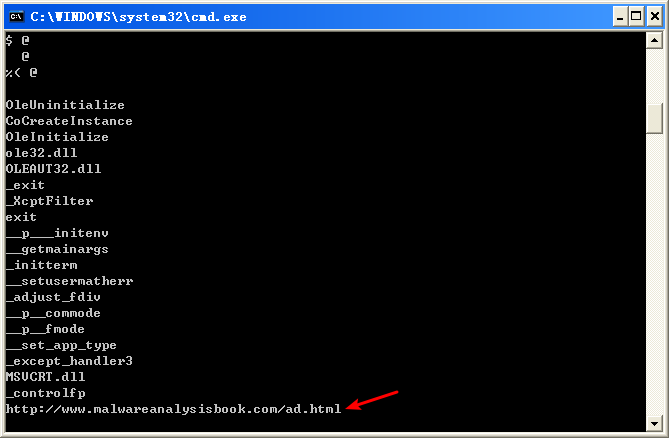

All of these functions are COM-related. The CoCreateInstance and OleInitialize functions in particular are required in order to use COM functionality.
Next, we try dynamic analysis. When we run this program, it opens Internet Explorer and displays an advertisement. There’s no evidence of the program modifying the system or installing itself to execute when the computer is restarted.
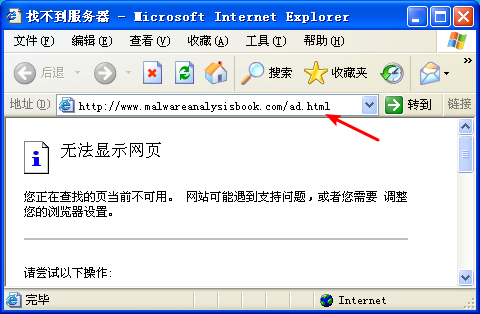
注:这是我掐断网络,运行 Lab07-02 的结果。
Now we can analyze the code in IDA Pro. We navigate to the *_main* method and see the code shown in the following listing.

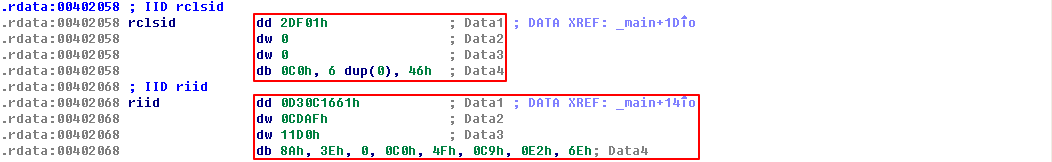
The first thing the malware does is initialize COM and obtain a pointer to a COM object with OleInitialize at \({\color{red} 1 }\) and CoCreateInstance at \({\color{red} 2 }\). The COM object returned will be stored on the stack in a variable that IDA Pro has labeled ppv, as shown at \({\color{red} 3}\). In order to determine what COM functionality is being used, we need to examine the interface identifier (IID) and class identifier (CLSID).
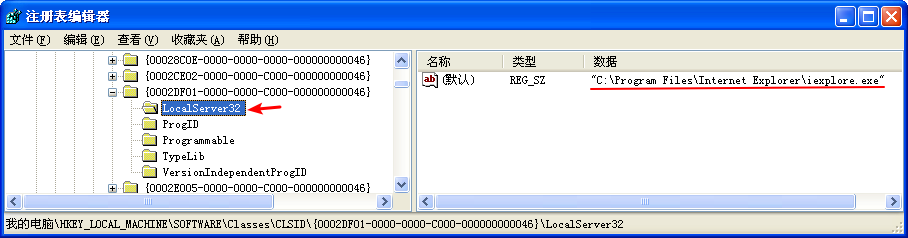
Clicking rclsid and riid shows that they are 0002DF01-0000-0000-C000-000000000046 and D30C1661-CDAF-11D0-8A3E-00C04FC9E26E, respectively. To determine which program will be called, check the registry for the CLSID, or search for the IID on the Internet for any documentation. In this case, these values are the same identifiers we used in “The Component Object Model” on page 154. The IID is for IWebBrowser2, and the CLSID is for Internet Explorer.

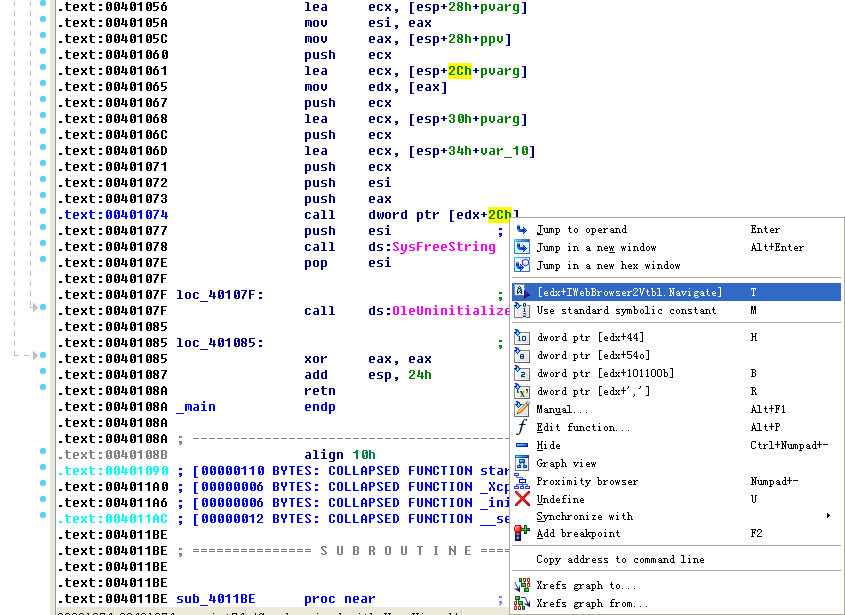
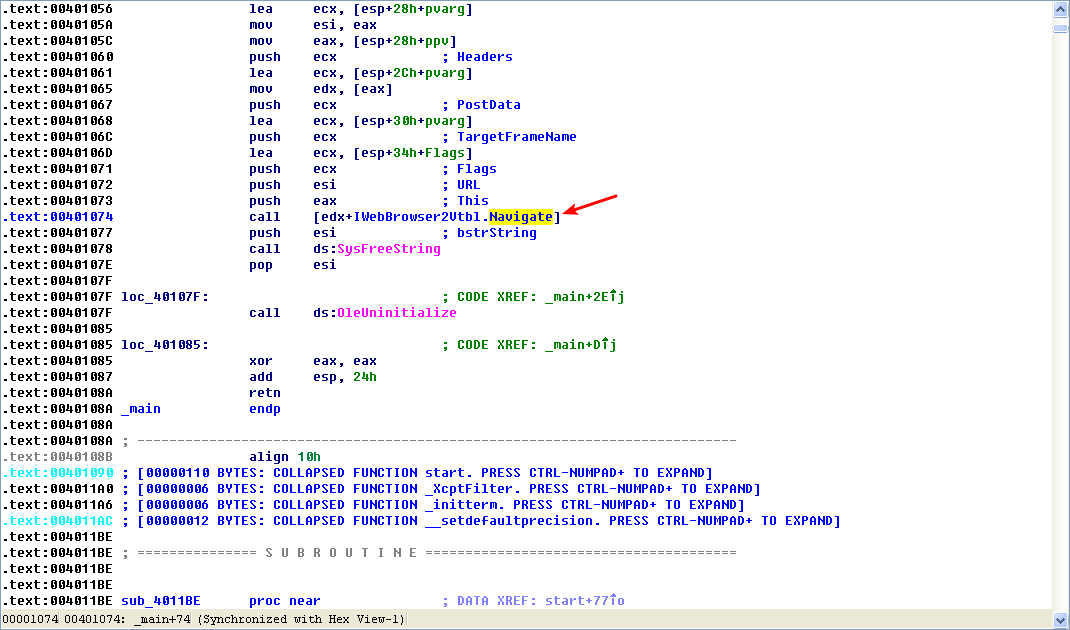
As shown in the following listing, the COM object returned by CoCreateInstance is accessed a few instructions later at \({\color{red} 1 }\).

Following this instruction, EAX points to the location of the COM object. At \({\color{red}2}\), EAX is dereferenced and EDX points to the beginning of the COM object itself. At \({\color{red} 3}\), the function at an offset of +0x2C from the object is called. As discussed in the chapter, the offset 0x2C for the IWebBrowser2 interface is the Navigate function, and we can use the Structures window in IDA Pro to create a structure and label the offset. When Navigate is called, Internet Explorer navigates to the web address http://www.malwareanalysisbook.com/ad.html.
注:标识 edx + 2Ch(重命名偏移 2Ch):
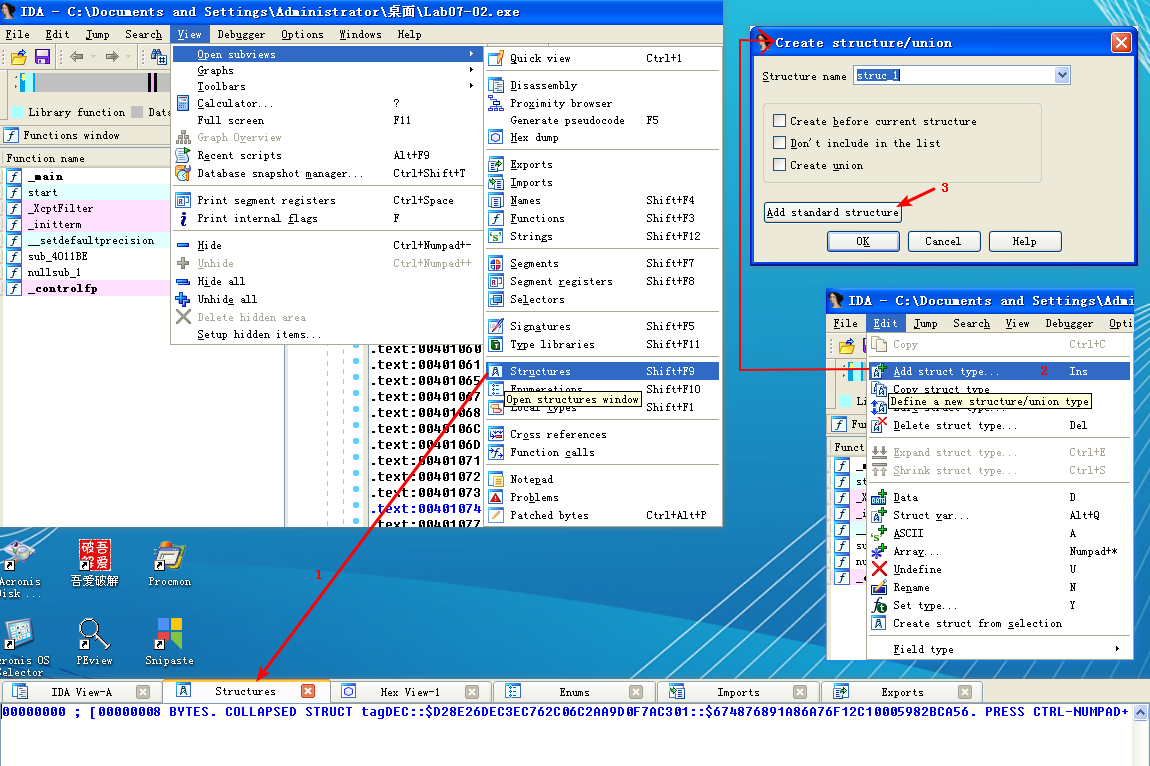


注结束。
After the call to Navigate, there are a few cleanup functions and then the program ends. The program doesn’t install itself persistently, and it doesn’t modify the system. It simply displays a one-time advertisement.
When you encounter a simple program like this one, you should consider it suspect. It may come packaged with additional malware, of which this is just one component.
Preference
Lab 7-2的更多相关文章
- MIT 6.828 JOS学习笔记18. Lab 3.2 Part B: Page Faults, Breakpoints Exceptions, and System Calls
现在你的操作系统内核已经具备一定的异常处理能力了,在这部分实验中,我们将会进一步完善它,使它能够处理不同类型的中断/异常. Handling Page Fault 缺页中断是一个非常重要的中断,因为我 ...
- MIT 6.828 JOS学习笔记17. Lab 3.1 Part A User Environments
Introduction 在这个实验中,我们将实现操作系统的一些基本功能,来实现用户环境下的进程的正常运行.你将会加强JOS内核的功能,为它增添一些重要的数据结构,用来记录用户进程环境的一些信息:创建 ...
- MIT 6.828 JOS学习笔记16. Lab 2.2
Part 3 Kernel Address Space JOS把32位线性地址虚拟空间划分成两个部分.其中用户环境(进程运行环境)通常占据低地址的那部分,叫用户地址空间.而操作系统内核总是占据高地址的 ...
- MIT 6.828 JOS学习笔记15. Lab 2.1
Lab 2: Memory Management lab2中多出来的几个文件: inc/memlayout.h kern/pmap.c kern/pmap.h kern/kclock.h kern/k ...
- MIT 6.828 JOS学习笔记10. Lab 1 Part 3: The kernel
Lab 1 Part 3: The kernel 现在我们将开始具体讨论一下JOS内核了.就像boot loader一样,内核开始的时候也是一些汇编语句,用于设置一些东西,来保证C语言的程序能够正确的 ...
- MIT 6.828 JOS学习笔记7. Lab 1 Part 2.2: The Boot Loader
Lab 1 Part 2 The Boot Loader Loading the Kernel 我们现在可以进一步的讨论一下boot loader中的C语言的部分,即boot/main.c.但是在我们 ...
- python opencv 利用Lab空间把春天的场景改为秋天
前一段时间实现了Reinhard颜色迁移算法,感觉挺有意思的,然后在代码上随意做了一些更改,有了一些发现,把Lab通道的a通道值改为127左右,可以将绿色改为黄色,而对其他颜色的改动非常小,因此可以将 ...
- Acadia Lab 228 + Lab 222
又是一对串烧实验,布好线后非常方便就可以一起完成. 连线方案一模一样: Lab 228 数码管骰子 核心代码如下: def loop() : global cnt global btn_read,se ...
- Acadia Lab 203 + Lab 231
在做完 Lab 6 之后,惊觉选做实验缺口很大,于是遍历了一遍夏任务,找到了一条最省力的路线. 做完 Lab 6 的连线不用拆,可以接下来做以下两个实验: Lab 203 网络时钟 核心代码如下: v ...
- GJM : 【技术干货】给The Lab Renderer for Unity中地形添加阴影
感谢您的阅读.喜欢的.有用的就请大哥大嫂们高抬贵手"推荐一下"吧!你的精神支持是博主强大的写作动力以及转载收藏动力.欢迎转载! 版权声明:本文原创发表于 [请点击连接前往] ,未经 ...
随机推荐
- HashMap出现Hash DOS攻击的问题
随着RESTful风格的接口普及,程序员默认都会使用json作为数据传递的方式.json格式的数据冗余少,兼容性高,从提出到现在已被广泛的使用,可以说成为了Web的一种标准.无论我们服务端使用什么语言 ...
- Oracle对于敏感数据的处理,可以采用策略(dbms_rls.add_policy)
Oracle Policy的简单说明: Policy应用于数据行访问权限控制时,其作用简而言之,就是在查询数据表时,自动在查询结果上加上一个Where子句.假如该查询已有where子句,则在该Wher ...
- java之项目构建工具Gradle
介绍 Java 作为一门世界级主流编程语言,有一款高效易用的项目管理工具是 java 开发者共同追求的心愿和目标.显示 2000 年的 Ant,后有 2004 年的 Maven 两个工具的诞生,都在 ...
- node os模块
const os = require('os'); console.log(os.homedir()); console.log(os.hostname()); console.log(os.plat ...
- 去掉Tomcat的管理页面
一.去掉Tomcat的管理页面 一.方法一:如果要去掉默认该界面,可以重命名tomcat目录下的ROOT,并新建空文件夹命名为ROOT 1.刚打开tomcat,默认访问的是tomcat管理页面,比如X ...
- 基于usb4java的usb通讯
下载java API及lib库地址:http://usb4java.org/index.html 1.导入所需要的库: 2.添加配置文件:文件名:javax.usb.properties:内容:jav ...
- 20175211 2018-2019-2 《Java程序设计》第二周学习总结
目录 教材学习内容总结 第二章 第三章 教材学习中的问题和解决过程 代码调试中的问题和解决过程 代码托管 上周考试错题总结 其他(感悟.思考等,可选) 学习进度条 参考资料 教材学习内容总结 第二章 ...
- mint-ui Toast icon 图标
Toast({ message: '修改成功', iconClass: 'fa fa-check fa-5x' }); Toast({ message: '修改失败', iconClass: 'fa ...
- CentOS 7 之 Systemd 入门教程:实战篇
开机启动对于那些支持 Systemd 的软件,安装的时候,会自动在/usr/lib/systemd/system目录添加一个配置文件. 如果你想让该软件开机启动,就执行下面的命令(以httpd.ser ...
- sitecore开发入门教程如何获取Sitecore项目的域名
我假设您在<sites>web.config文件的部分中设置了多个站点,并且每个站点都hostName定义了一个属性,例如 <site name="website1&quo ...
