[官网]How to configure the Microsoft Distributed Transaction Coordinator (MSDTC) on Linux
How to configure the Microsoft Distributed Transaction Coordinator (MSDTC) on Linux
APPLIES TO:  SQL Server (Linux only)
SQL Server (Linux only)  Azure SQL Database
Azure SQL Database  Azure SQL Data Warehouse
Azure SQL Data Warehouse  Parallel Data Warehouse
Parallel Data Warehouse
This article describes how to configure the Microsoft Distributed Transaction Coordinator (MSTDC) on Linux. MSDTC support on Linux was introduced in SQL Server 2019 preview.
Overview
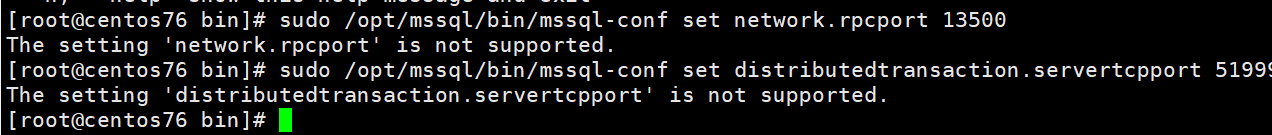
https://docs.microsoft.com/en-us/sql/linux/sql-server-linux-configure-msdtc?view=sqlallproducts-allversions sqlserver 不支持该命令 已经确认
Distributed transactions are enabled on SQL Server on Linux by introducing MSDTC and RPC endpoint mapper functionality within SQL Server. By default, an RPC endpoint-mapping process listens on port 135 for incoming RPC requests and routes that to appropriate components (such as the MSDTC service). A process requires super user privilege to bind to well-known ports (port numbers less than 1024) on Linux. To avoid starting SQL Server with root privileges for the RPC endpoint mapper process, system administrators must use iptables to create NAT translation to route traffic on port 135 to SQL Server's RPC endpoint-mapping process.
SQL Server 2019 introduces two configuration parameters for the mssql-conf utility.
| mssql-conf setting | Description |
|---|---|
| network.rpcport | The TCP port that the RPC endpoint mapper process binds to. |
| network.servertcpport | The port that the MSDTC server listens to. If not set, the MSDTC service uses a random ephemeral port on service restarts, and firewall exceptions will need to be re-configured to ensure that MSDTC service can continue communication. |
For more information about these settings and other related MSDTC settings, see Configure SQL Server on Linux with the mssql-conf tool.
Supported MSDTC configurations
The following MSDTC configurations are supported:
- OLE-TX Distributed transactions against SQL Server on Linux for JDBC and ODBC providers.
- XA Distributed transactions against SQL Server on Linux using JDBC providers.
- Distributed transactions on Linked server.
For limitations and known issues for MSDTC in preview, see Release notes for SQL Server 2019 preview on Linux.
MSDTC configuration steps
There are three steps to configure MSDTC communication and functionality. If the necessary configuration steps are not done, SQL Server will not enable MSDTC functionality.
- Configure network.rpcport and distributedtransaction.servertcpport using mssql-conf.
- Configure the firewall to allow communication on rpcport, servertcpport, and port 135.
- Configure Linux server routing so that RPC communication on port 135 is redirected to SQL Server's network.rpcport.
The following sections provide detailed instructions for each step.
Configure RPC and MSDTC ports
First, configure network.rpcport and distributedtransaction.servertcpport using mssql-conf.
Use mssql-conf to set the network.rpcport value. The following example sets it to 13500.
bashCopysudo /opt/mssql/bin/mssql-conf set network.rpcport 13500
Set the distributedtransaction.servertcpport value. The following example sets it to 51999.
bashCopysudo /opt/mssql/bin/mssql-conf set distributedtransaction.servertcpport 51999
Restart SQL Server.
bashCopysudo systemctl restart mssql-server
Configure the firewall
The final step is to configure the firewall to allow communication on rpcport, servertcpport, and port 135. This enables the RPC endpoint-mapping process and MSDTC process to communicate externally to other transaction managers and coordinators. The actual steps for this will vary depending on your Linux distribution and firewall.
The following example shows how to create these rules on Ubuntu.
sudo ufw allow from any to any port 51999 proto tcp
sudo ufw allow from any to any port 135 proto tcp
The following example shows how this could be done on Red Hat Enterprise Linux (RHEL):
sudo firewall-cmd --zone=public --add-port=51999/tcp --permanent
sudo firewall-cmd --zone=public --add-port=135/tcp --permanent
sudo firewall-cmd --reload
It is important to configure the firewall before configuring port routing in the next section. Refreshing the firewall can clear the port routing rules in some cases.
Configure port routing
Configure the Linux server routing table so that RPC communication on port 135 is redirected to SQL Server's network.rpcport. Configuration mechanism for port forwarding on different distribution may differ. On distributions which do not use firewalld service, iptable rules are an efficient mechanism to achieve this. Example of such distrubution are Ubuntu 16.04 and SUSE Enterprise Linux v12. The iptable rules may not persist during reboots, so the following commands also provide instructions for restoring the rules after a reboot.
Create routing rules for port 135. In the following example, port 135 is directed to the RPC port, 13500, defined in the previous section. Replace
<ipaddress>with the IP address of your server.bashCopyiptables -t nat -A PREROUTING -d <ip> -p tcp --dport 135 -m addrtype --dst-type LOCAL \
-j DNAT --to-destination <ip>:13500 -m comment --comment RpcEndPointMapper
iptables -t nat -A OUTPUT -d <ip> -p tcp --dport 135 -m addrtype --dst-type LOCAL \
-j DNAT --to-destination <ip>:13500 -m comment --comment RpcEndPointMapper
The
--comment RpcEndPointMapperparameter in the previous commands assists with managing these rules in later commands.View the routing rules you created with the following command:
bashCopyiptables -S -t nat | grep "RpcEndPointMapper"
Save the routing rules to a file on your machine.
bashCopyiptables-save > /etc/iptables.conf
To reload the rules after a reboot, add the following command to
/etc/rc.local(for Ubuntu or RHEL) or to/etc/init.d/after.local(for SLES):bashCopyiptables-restore < /etc/iptables.conf
The iptables-save and iptables-restore commands provide a basic mechanism to save and restore iptables entries. Depending on your Linux distribution, there might be more advanced or automated options available. For example, an Ubuntu alternative is the iptables-persistent package to make entries persistent.
On distributions which use firewalld service, the same service can be used for both opening the port on the server and internal port forwarding. For example, on Red Hat Enterprise Linux, you should use firewalld service (via firewall-cmd configuration utility with -add-forward-port or similar options) to create and manage persistent port forwarding rules instead of using iptables.
firewall-cmd --permanent --add-forward-port=port=135:proto=tcp:toport=13500
Important
The previous steps assume a fixed IP address. If the IP address for your SQL Server instance changes (due to manual intervention or DHCP), you must remove and recreate the routing rules if they were created with iptables. If you need to recreate or delete existing routing rules, you can use the following command to remove old RpcEndPointMapper rules:
iptables -S -t nat | grep "RpcEndPointMapper" | sed 's/^-A //' | while read rule; do iptables -t nat -D $rule; done
Verify
At this point, SQL Server should be able to participate in distributed transactions. To verify that SQL Server is listening, run the netstatcommand (if you are using RHEL, you might have to first install the net-tools package):
sudo netstat -tulpn | grep sqlservr
You should see output similar to the following:
tcp 0 0 0.0.0.0:1433 0.0.0.0:* LISTEN 13911/sqlservr
tcp 0 0 127.0.0.1:1434 0.0.0.0:* LISTEN 13911/sqlservr
tcp 0 0 0.0.0.0:13500 0.0.0.0:* LISTEN 13911/sqlservr
tcp 0 0 0.0.0.0:51999 0.0.0.0:* LISTEN 13911/sqlservr
tcp6 0 0 :::1433 :::* LISTEN 13911/sqlservr
tcp6 0 0 ::1:1434 :::* LISTEN 13911/sqlservr
tcp6 0 0 :::13500 :::* LISTEN 13911/sqlservr
tcp6 0 0 :::51999 :::* LISTEN 13911/sqlservr
However, after a restart, SQL Server does not start listening on the servertcpport until the first distributed transaction. In this case, you would not see SQL Server listening on port 51999 in this example until the first distributed transaction.
Next steps
For more information about SQL Server on Linux, see SQL Server on Linux.
[官网]How to configure the Microsoft Distributed Transaction Coordinator (MSDTC) on Linux的更多相关文章
- The Microsoft Distributed Transaction Coordinator (MS DTC) has cancelled the distributed transaction.
同事反馈一个系统在运行一个存储过程时遇到了下面错误: Msg 1206, Level 18, State 169, Procedure xxxxxx, Line 118The Microsoft Di ...
- 解决启动Distributed Transaction Coordinator服务出错的问题
解决启动Distributed Transaction Coordinator服务出错的问题 "Windows 不能在 本地计算机 启动 Distributed Transaction ...
- Distributed Transaction Coordinator(DTC)一些问题的解决方法
有时运行某个程序或者安装SQL Server时报错. 错误信息: 事务管理器不可用.(从 HRESULT 异常: 0x8004D01B) 启动服务Distributed Transaction Coo ...
- Distributed Transaction Coordinator 无法启动
有时候我们需要进行COM应用程序的权限设置,控制面板-->管理工具-->组件服务-->然后依此展开:组件服务-->计算机-->我的电脑-->DCOM 配置,接下来找 ...
- 无法启动DISTRIBUTED TRANSACTION COORDINATOR解决方法
有时候我们需要进行COM应用程序的权限设置,控制面板-->管理工具-->组件服务-->然后依此展开:组件服务-->计算机-->我的电脑-->DCOM 配置,接下来找 ...
- [官网]How to use distributed transactions with SQL Server on Docker
How to use distributed transactions with SQL Server on Docker https://docs.microsoft.com/en-us/sql/l ...
- MS SQL 错误:The operation could not be performed because OLE DB provider "SQLNCLI10" for linked server "test" was unable to begin a distributed transaction.
一同事在测试服务器(系统:Windows 2008 R2 Standard 数据库:SQL SERVER 2008 R2)通过链接服务器test使用分布式事务测试时出错,出错信息如下: set ...
- Nuget 自定义配置(官网)
<?xml version="1.0" encoding="utf-8"?> <configuration> <config> ...
- Visual C++ 2013 and Visual C++ Redistributable Package 更新版官网下载地址
Visual C++ 2013 and Visual C++ Redistributable Visual C++ 2013 and Visual C++ Redistributable Packag ...
随机推荐
- Win10 开始运行不保存历史记录原因和解决方法
Win10 开始运行命令以后,再次打开就没有任何历史记录了,常规方法是桌面-右键-个性化-开始-显示最常用的应用..可是打开是灰色的不可选. 每次打开开始都没有以前的记录..比如需要打开下regedi ...
- 08.Python网络爬虫之图片懒加载技术、selenium和PhantomJS
引入 今日概要 图片懒加载 selenium phantomJs 谷歌无头浏览器 知识点回顾 验证码处理流程 今日详情 动态数据加载处理 一.图片懒加载 什么是图片懒加载? 案例分析:抓取站长素材ht ...
- Leetcode:0002(两数之和)
LeetCode:0002(两数之和) 题目描述:给定两个非空链表来表示两个非负整数.位数按照逆序方式存储,它们的每个节点只存储单个数字.将两数相加返回一个新的链表.你可以假设除了数字 0 之外,这两 ...
- [TJOI2017]DNA
嘟嘟嘟 这题怎么想都想不出来,最后还是敲了暴力,喜提40分-- 正解竟然也是暴力-- 用\(s_0\)构造SAM,然后把\(s\)扔上去暴力dfs:记录一个修改次数tot,如果当前不匹配,就tot + ...
- 【转】MFC内嵌cef3浏览器内核
一.cef3内核的下载 可以从http://opensource.spotify.com/cefbuilds/index.html下载,注意:很多版本编译都可以通过 但是运行的时候会崩溃,以cef_b ...
- ActiveMQ后台使用
版权声明:本文为博主原创文章,未经博主允许不得转载. https://blog.csdn.net/nangeali/article/details/81514517默认地址 http://192.16 ...
- 一)surging 微服务框架使用系列之surging 的准备工作rabbitmq安装(转载 https://www.cnblogs.com/alangur/p/8339905.html)
(一)surging 微服务框架使用系列之surging 的准备工作rabbitmq安装 (1)下载erlang: http://www.erlang.org/download/otp_win64 ...
- git 忽略无效解决办法
有时候发现git提交了一些我们不需要提交的内容,这时候第一反应是加个忽略: https://github.com/github/gitignore 宇宙神器VS: https://github.com ...
- Linux、Windows如何进行性能监控与调优
1.Linux命令行工具 推荐:CentOS 7 1.1 top命令 top命令的输出如下: top命令的输出可以分为两部分:前半部分是系统统计信息,后半部分是进程信息.在统计信息中, 第1行是任务队 ...
- 【C#复习总结】细说委托
1 前言 本系列会将[委托] [匿名方法][Lambda表达式] [泛型委托] [表达式树] [事件]等基础知识总结一下.(本人小白一枚,有错误的地方希望大佬指正) 系类1:细说委托 系类2:细说匿名 ...
