Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups
- Create Remote User Objects and LDAP Integration:
- samAccountName - eric.wei
- UserPrincipalName - eric.wei@pandabusiness.local
- Prerequisites:
- Microsoft Active Directory(LDAP)
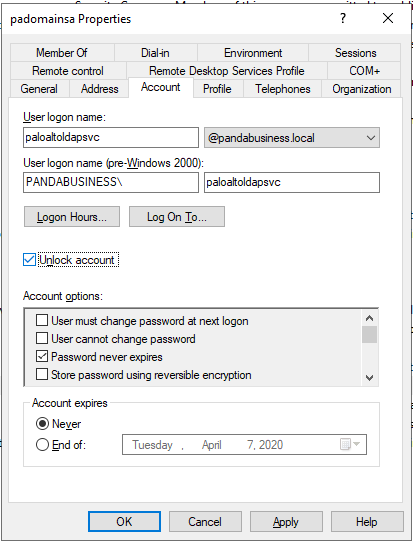
- AD service account for Palo Alto Firewall Integration
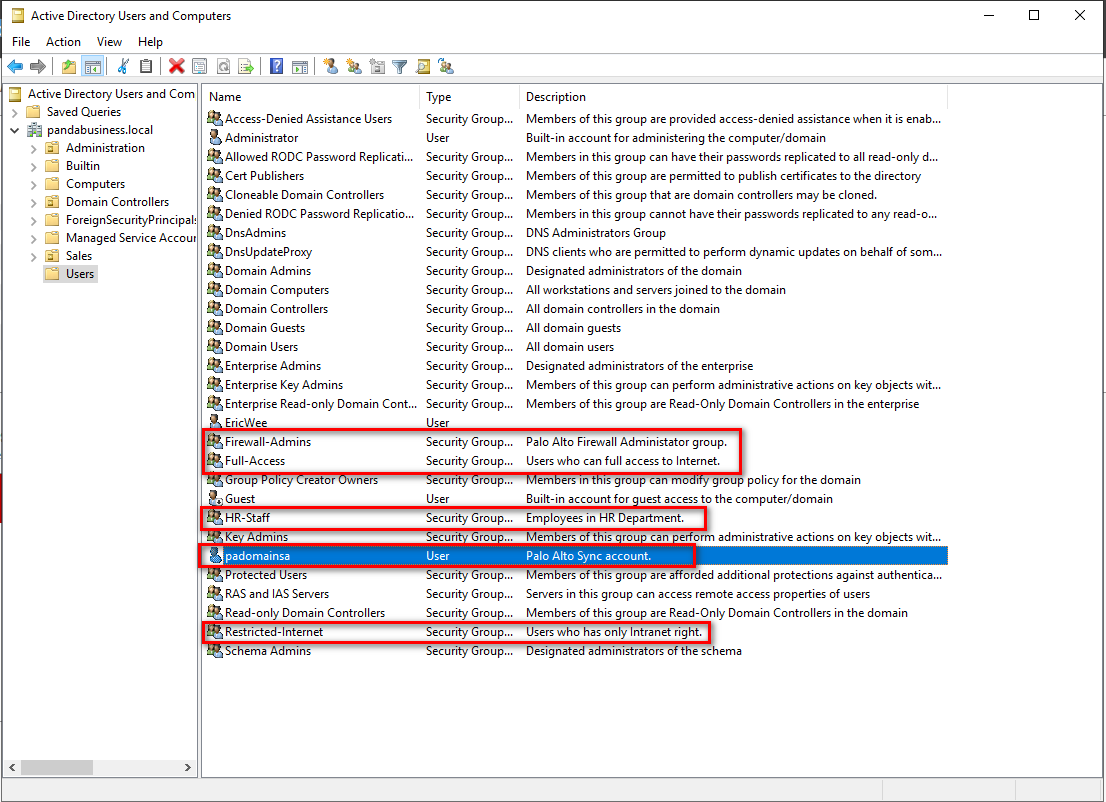
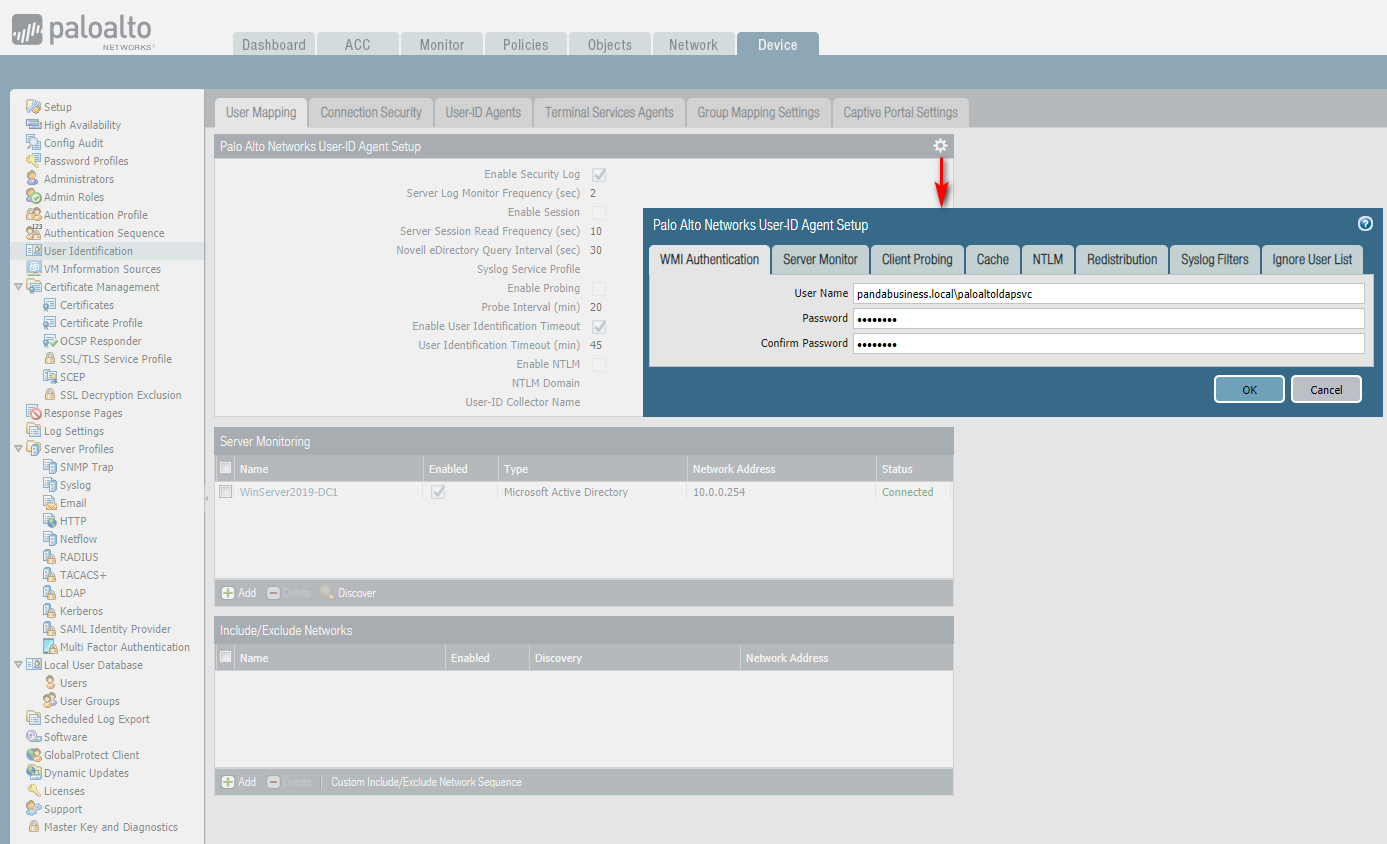
Create security groups and a function account in Users OU.
Test this account's WQL queries using WBEMTEST.
https://4sysops.com/archives/wbemtest-part-1-testing-wmi-connectivity/
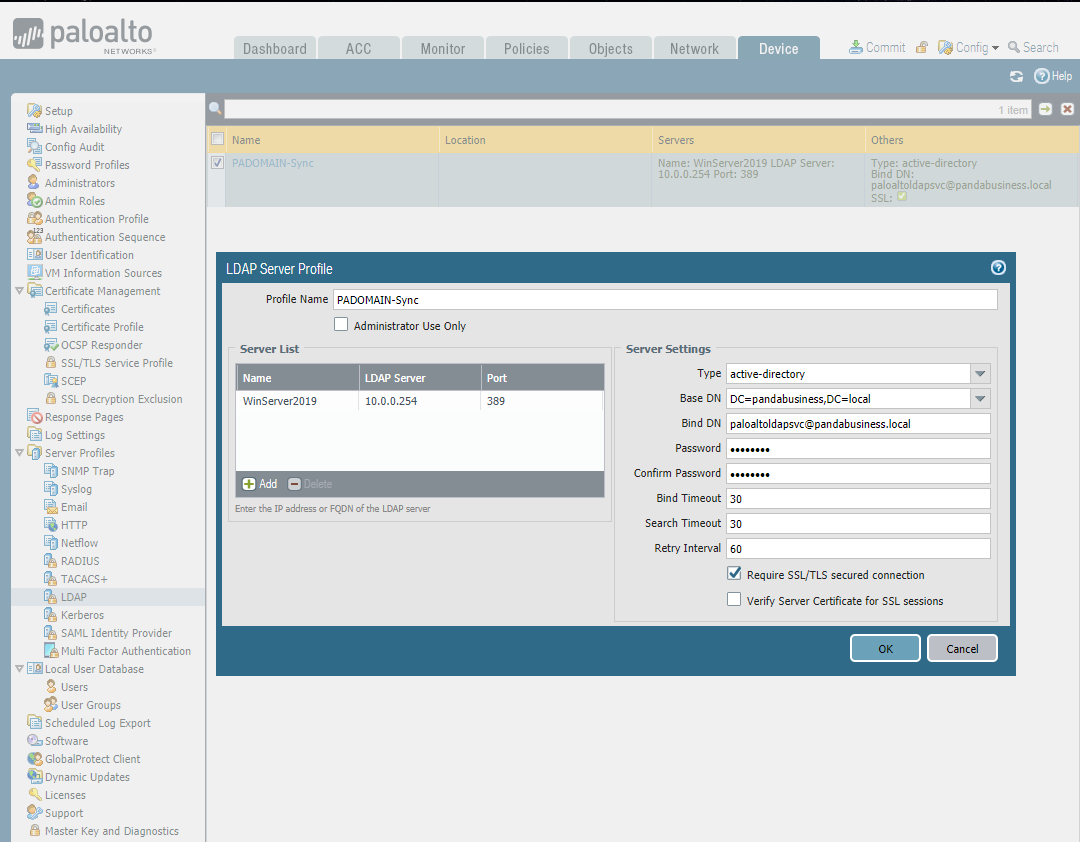
Set the LDAP Server Profile.
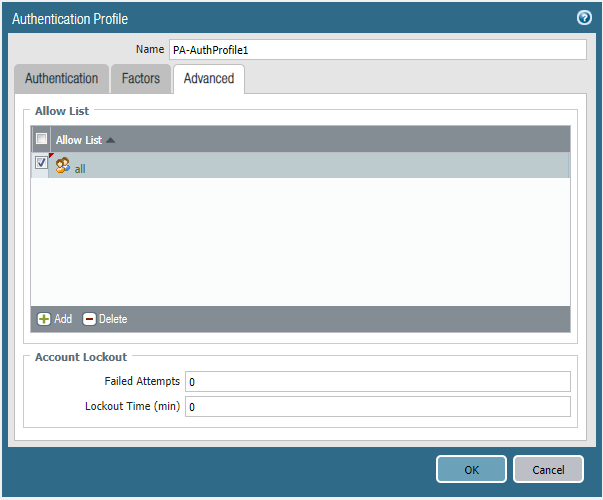
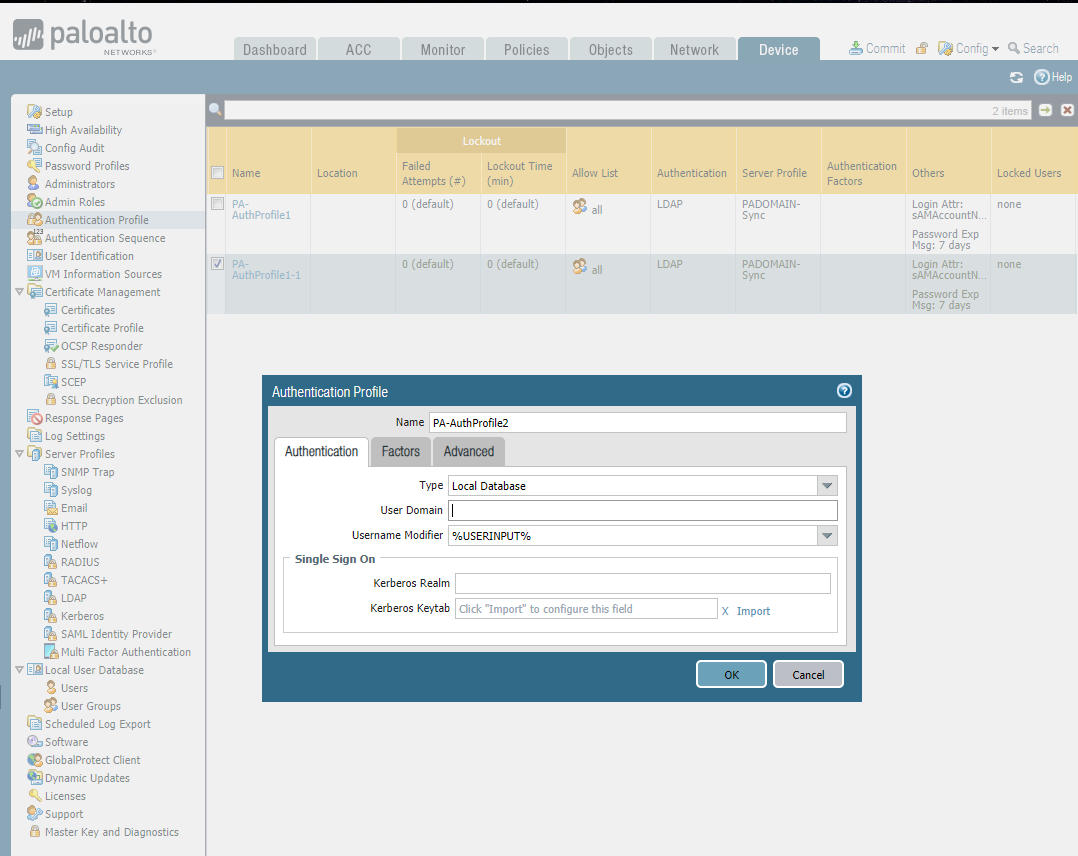
Create two Authentication Profiles.
LDAP Auth:

Local Database Auth:

Set Authentication Sequence.

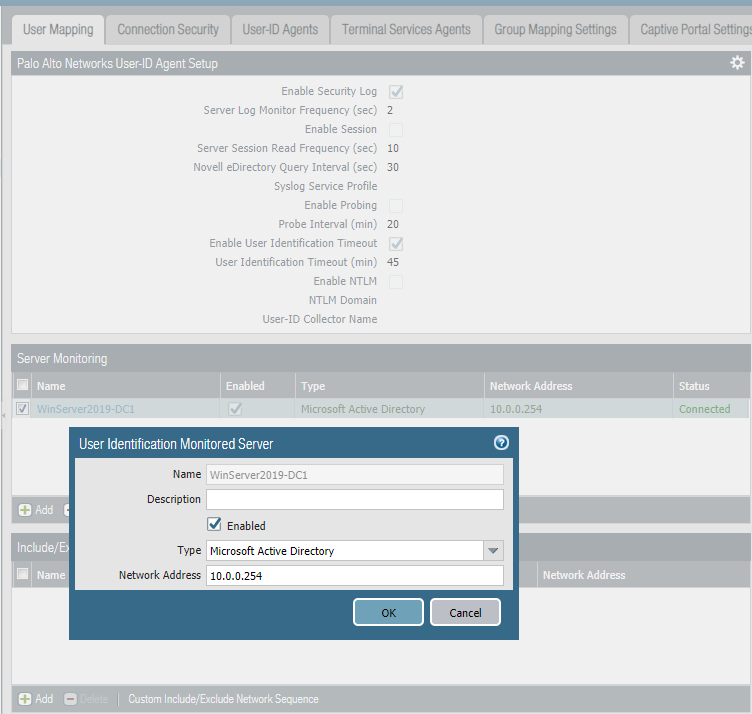
Set Server Monitoring in User Identification and commit the changes.
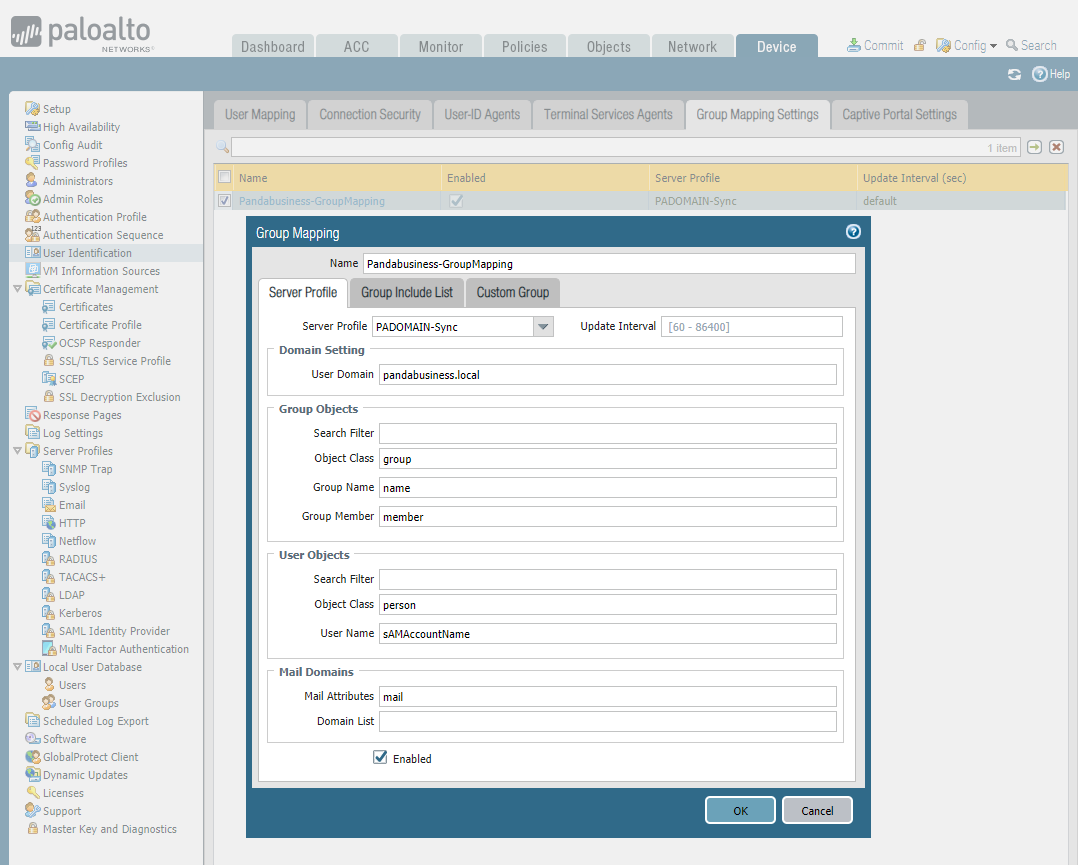
Set Group Mapping Settings.

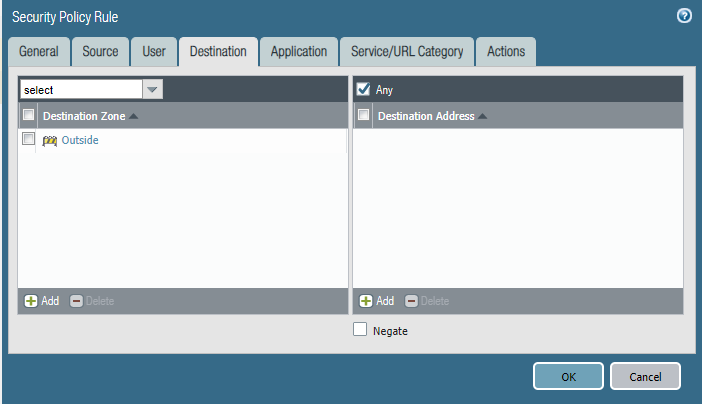
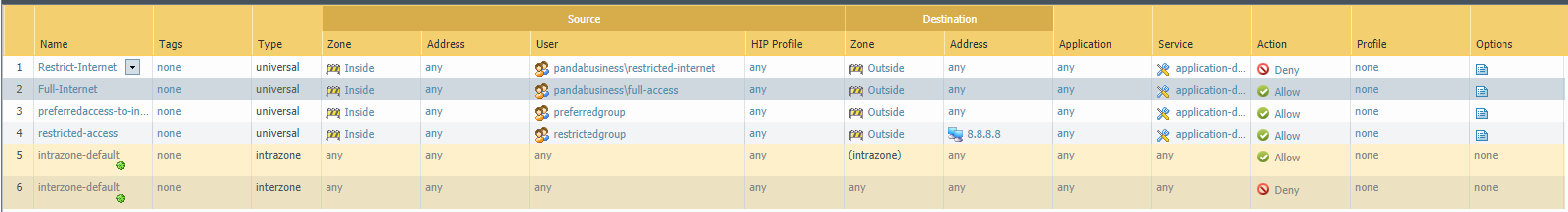
Finally set the security policies.
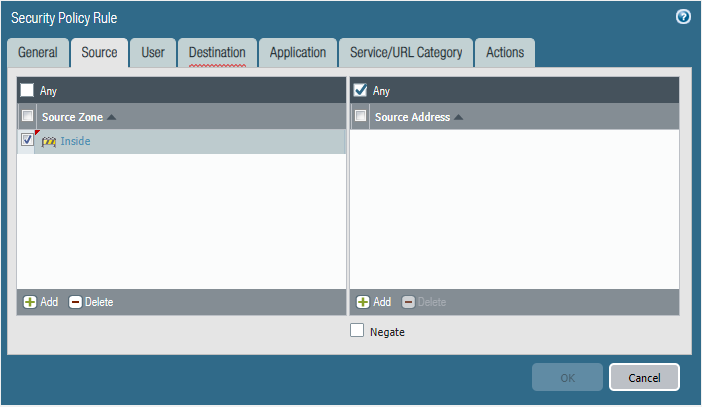
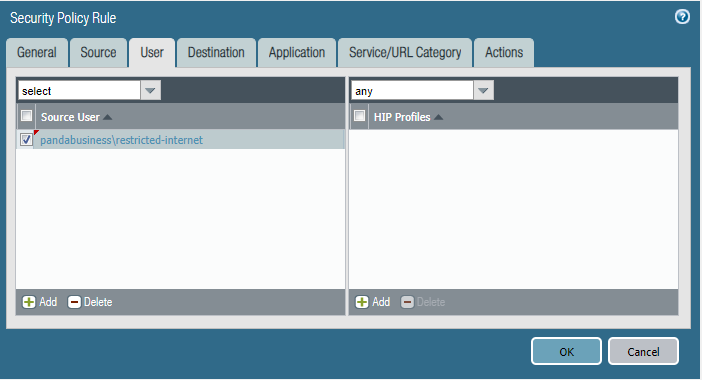
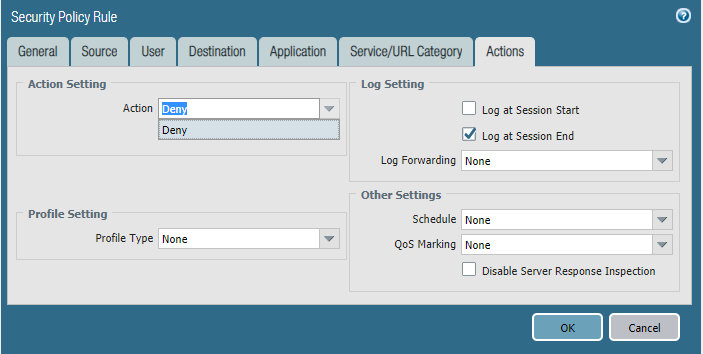
Policy 1 - Restrict-Internet


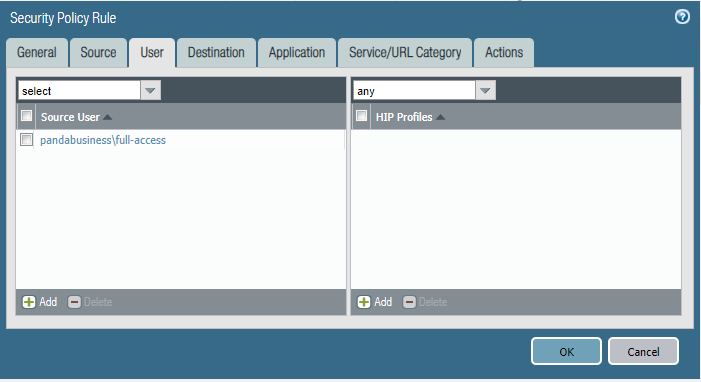
Policy 2 - Full Internet



Commit the change to take effective finally.
Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)的更多相关文章
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups Creating address objects. Organizing address objects with address groups ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your: Network Layer 2 interfaces and VLAN ...
- Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires Bridge two physical connections and apply security Policies without influencing a ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment: Download and Install Pan-OS from the following website https://d ...
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Cyber Security - Palo Alto Security Policies(2)
Task 3 The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- vc6.0打开类向导时报错-Parsing error: Expected ";".Input Line: "解决方法
--------------------------- Microsoft Visual C++ --------------------------- Parsing error: Expecte ...
- Lucene5多条件查询
lucene是一个很强大的搜索工具,最近公司项目上用到,结合JAVA1234所讲,对多条件查询做出总结 先描述一下我的多条件需求,如果和您的类似,继续往下看. 1.我的Lucene搜索会在很多地方使用 ...
- springcloud2.0 添加配置中心遇到的坑
新手入门,在springcloud 配置config的时候遇到了几个比较烦的坑 先说1.5x版本的一些配置吧 首先是端点暴露的方式 management: security: enabled: fal ...
- java关于传值与传引用
关于java传值还是传引用的问题经常出现在一些烦人的面试题中,主要考察个人对java基础的掌握情况. 首先明确一下:本地方法中,java的参数传递都是传值.但是如果是远程调用方法时,会将对象本身传递过 ...
- Spring Boot Admin 2.1.4最新实战教程
环境的搭建 首先搭建eruka的注册中心 pom.xml <?xml version="1.0" encoding="UTF-8"?> <pr ...
- Python3-datetime模块-日期与时间
官方文档 http://python.usyiyi.cn/translate/python_352/library/datetime.html 代码示例 from datetime import da ...
- 入门大数据---Storm搭建与应用
1.Storm在Linux环境配置 主机名 tuge1 tuge2 tuge3 部署环境 Zookeeper/Nimbus Zookeeper/Supervisor Zookeeper/Supervi ...
- JavaScript中__proto__与prototype的关系(转)
一.所有构造器/函数的__proto__都指向Function.prototype,它是一个空函数(Empty function) 1 2 3 4 5 6 7 8 9 Number.__proto__ ...
- 洛谷 P1215 【[USACO1.4]母亲的牛奶 Mother's Milk】
这道题\(DFS\)就好了,六种情况,\(ab,ac,ba,bc,ca,cb\),我们直接枚举就可.什么?这样不会结束?用一个\(vis\)数组判断走过没有就可以了.最后排序输出即可. \(code: ...
- python案例远程执行命令
------类似于cmd的功能,client执行命令,server发命令结果发送到client -----------server.py------------------- import subpr ...
